This description is based on the status of the Microsoft 365 Portal in June 2023. Changes to the user interface on the part of Microsoft are possible at any time and must be taken into account accordingly in the implementation.
All information without warranty.
Configuration for phishing simulations: Bypass junk filter
New article: 06.2023
notempty
This article refers to a Resellerpreview
Whitelisting
To ensure that the simulated phishing emails of the Awareness PLUS training are not blocked by the Microsoft mail server or Microsoft Defender, whitelisting must be configured at various points.
Bypass junk filter
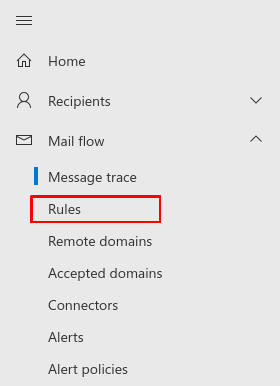
Another rule is needed to bypass the junk filter
Fig.1
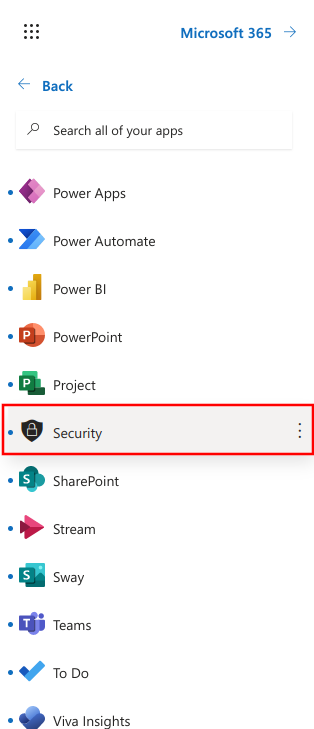
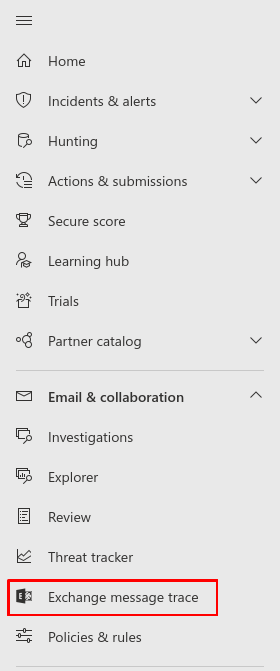
Log in to the MS365 portal at https://login.microsoftonline.com
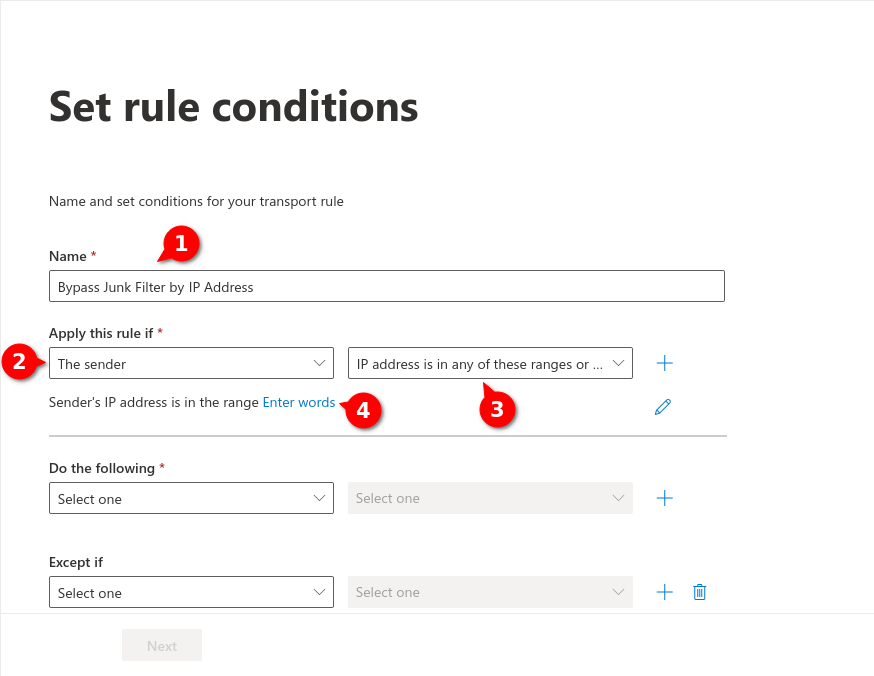
Fig.6
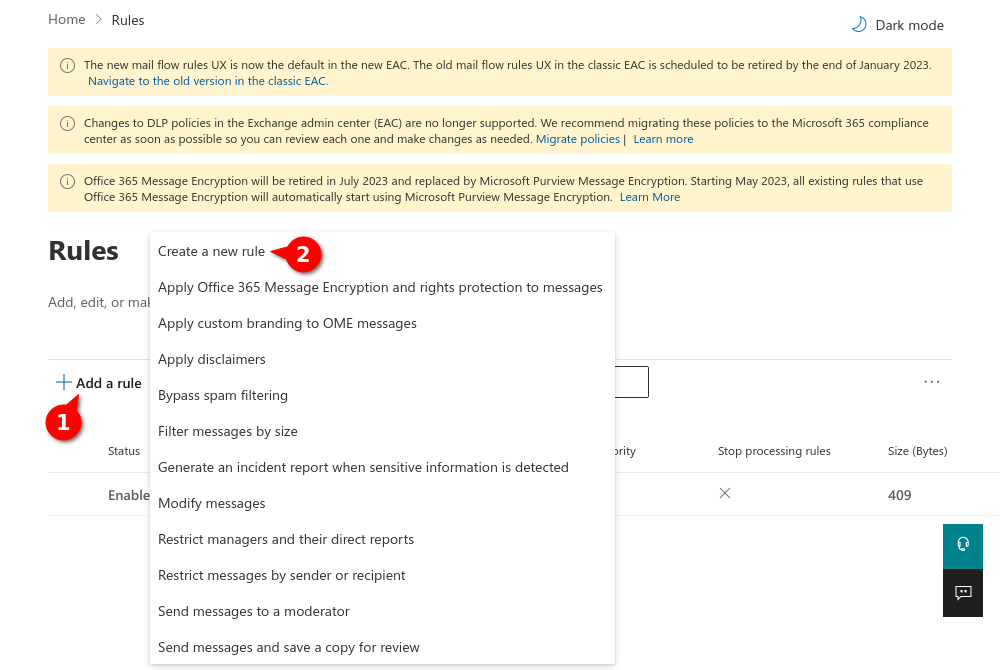
- Assign a unique name for the rule (here i.g.: Bypass Junk Filter by IP Address )
- Select for Apply this rule if
- Select
- Click on Enter words. For that see next figure
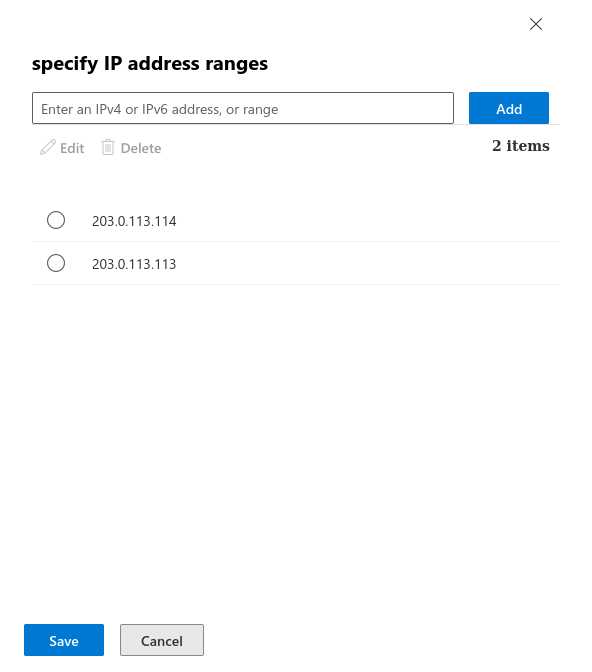
Fig.7
Enter the IP adress(es) from the section Whitelisting phishing simulation and confirm with . In the figure are example IPs that are not used!
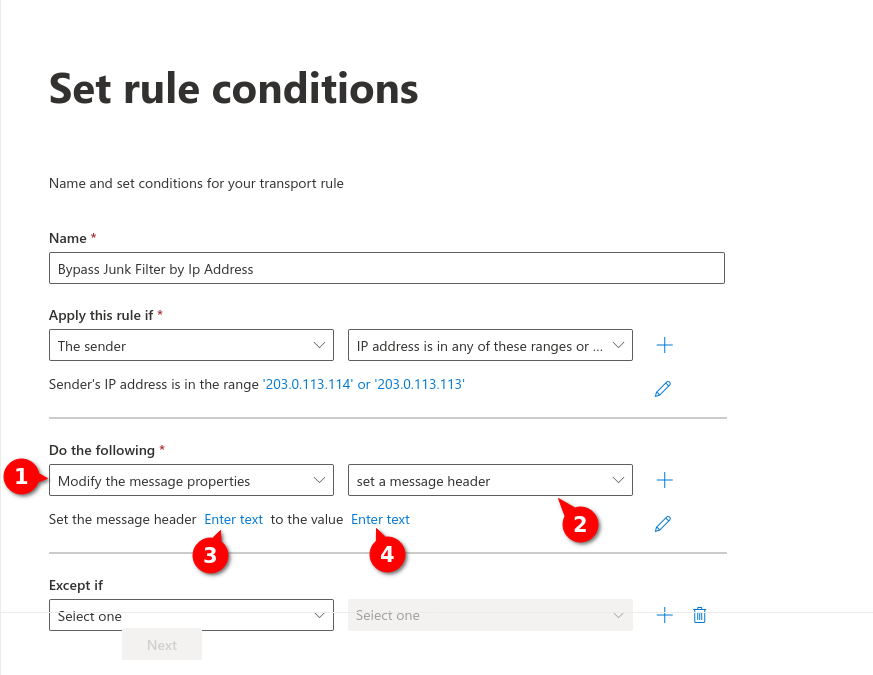
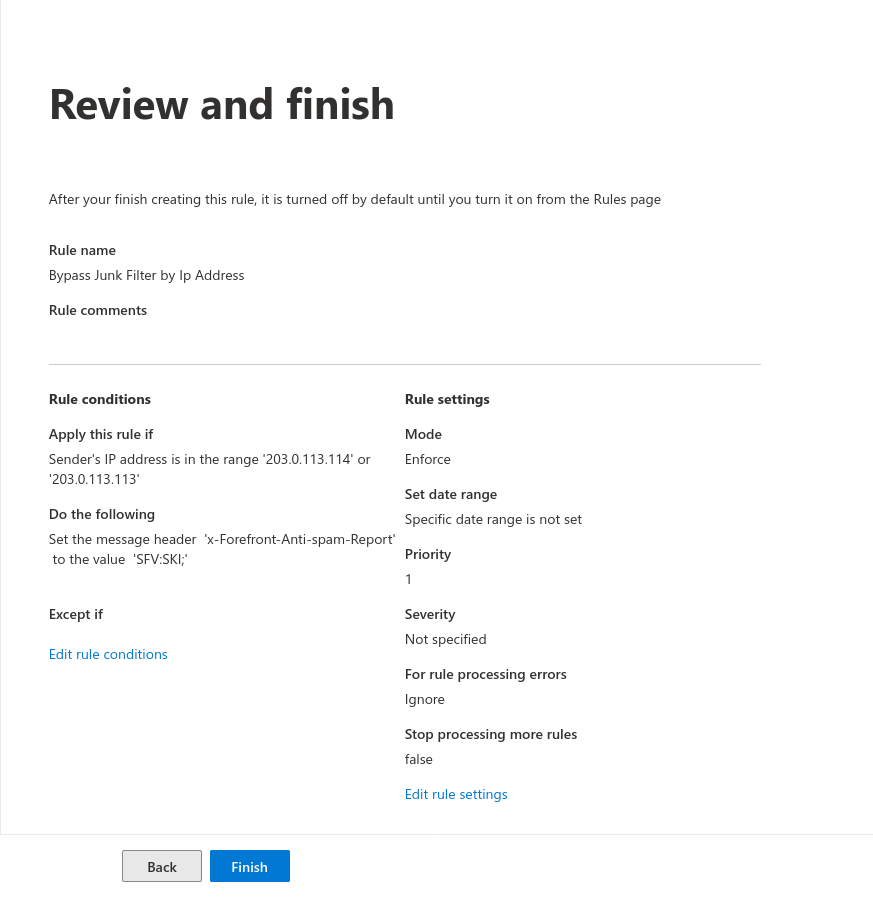
Fig.8
- Select in Do the following
- Select
- Enter the header message (3) and the value (4) by clicking on Enter text
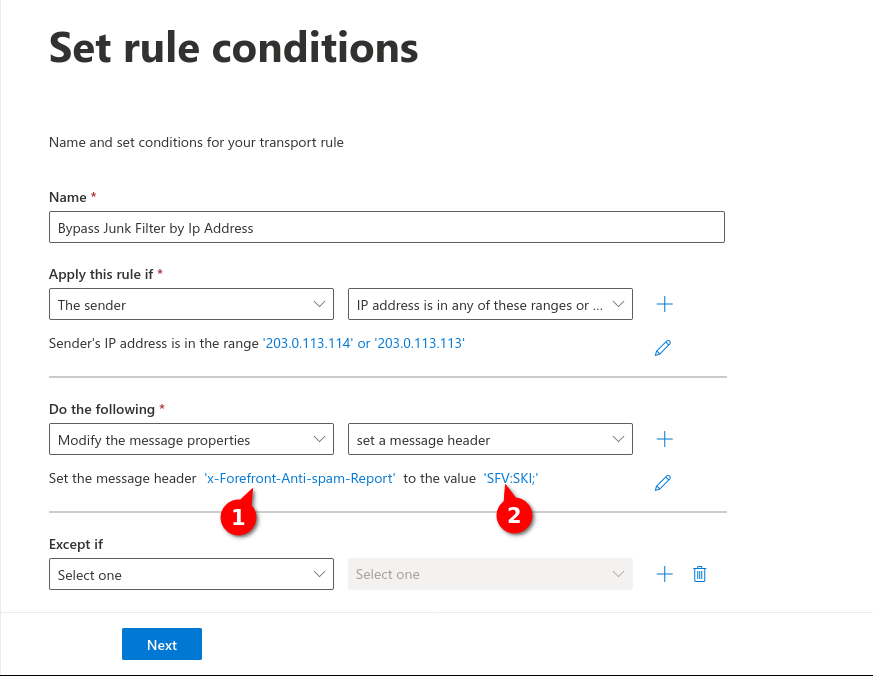
Fig.9
Enter the following values:
- For message header (1): x-Forefront-Antispam-Report
- For Value (2): SFV:SKI;
- Then click on
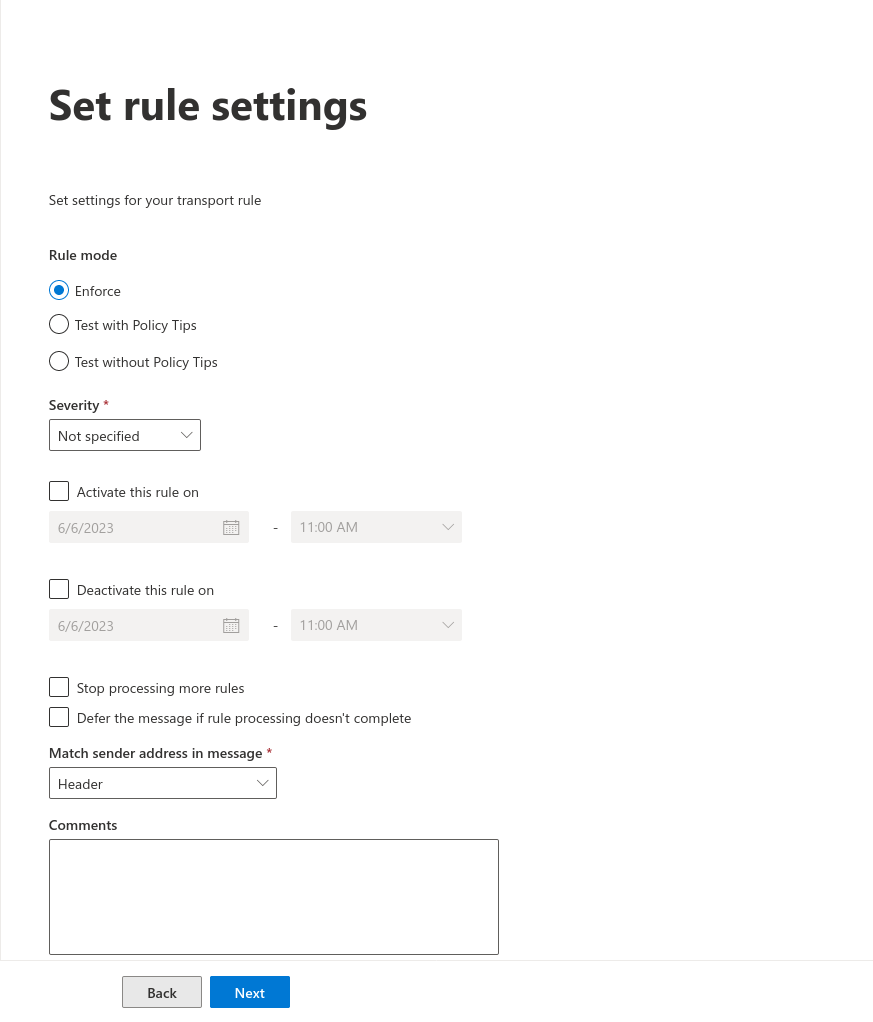
Fig.10
- For Rule mode Enforce is selected
- At Severity is sufficient
- At will can be set between which times this rule should be active