Last adaptation to the version: 12.6.1
New:
- Updated to Redesign of the webinterface
General Settings | |||
| General settings are made under Area General. | |||
| Caption | Value | Description | UTMuser@firewall.name.fqdnAnwendungen 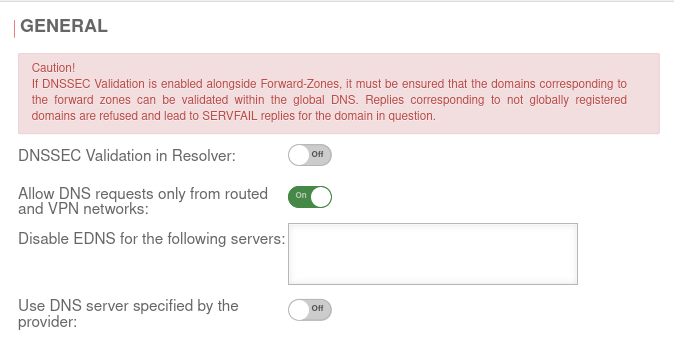 Tab General Tab General
|
|---|---|---|---|
| DNSSEC validation in resolver: | Off | notempty Caution! If DNSSEC Validation is enabled alongside Forward-Zones, it must be ensured that the domains corresponding to the forward zones can be validated within the global DNS. Replies corresponding to not globally registered domains are refused and lead to SERVFAIL replies for the domain in question. When this function is activated, all DNS entries are resolved with DNSSEC without exception. This would also attempt a validation in the DNS hierarchy for only local addresses. However, due to the lack of uniqueness of the local address, it cannot be registered with higher-level DNS servers. An error message appears, the address is not resolved and the zone is therefore not accessible (using DNS). This applies, for example, to .local domains! Further information on the implementation of DNSSEC can be found here. | |
| Allow DNS queries only from routed and VPN networks: | On Default |
By default, only DNS queries from the following sources are answered:
| |
| Off | If DNS queries are to be answered from other external networks as well, this option must be disabled | ||
| Disable EDNS for the following servers: | EDNS can be disabled for servers that do not comply with RFC 6891. Old or misconfigured name servers sometimes do not use or do not correctly use Extended DNS and as a result do not accept DNS queries that use these protocol extensions. The DO flag (DNSSEC OK) can no longer be placed in the standard header. | ||
| notempty New as of v12.6.0 Use DNS server specified by the provider: |
Off | When activated, the DNS server of the Internet provider is used. | |