- Updated to Redesign of the webinterface
Introduction
A Roadwarrior connection connects individual hosts to the local network. This allows, for example, a field service employee to connect to the network of the headquarters.
This step-by-step guide shows how to configure an end-to-site connection. The selected connection type is native IPSec with IKEv1.
For native IPSec connections with IKEv1 the client needs a separate program.
Configuration of a native IPSec connection
New connections can be added in the menu Area Connections Button
Wizard
Connection Type Step 1 - Connection Type
| |||
| Caption | Value | Description | UTMuser@firewall.name.fqdnVPNIPSec 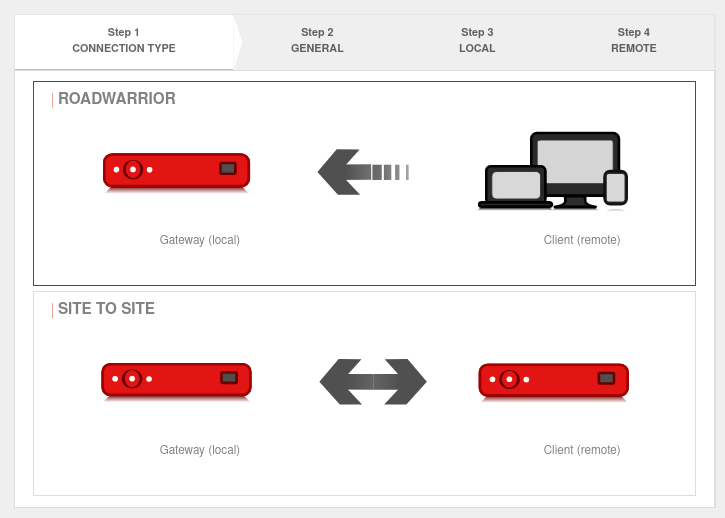 Wizard step 1 Wizard step 1
|
|---|---|---|---|
| Selection of the connection type | The following connections are available:
|
For the configuration of an E2S / End-to-Site-connection Roadwarrior is to be selected. | |
General Step 2 - General
| |||
| Name: | IPSec Roadwarrior | Chose unique name | 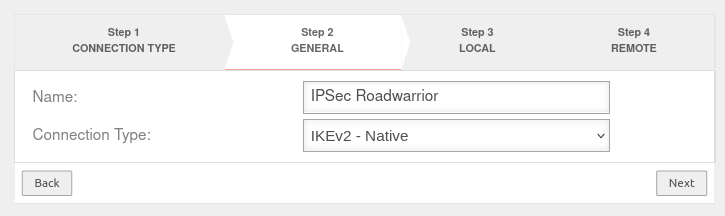 |
| Connection Type: | Possible connection types: The connection type IKEv1 - L2TP can only be selected if L2TP is set to Autostart or explicitly enabled in the admin interface. Enable L2TP under: Area Hidden functions Enable L2TP: Yes Activate hidden menu buttons: Ctrl + Alt + A Please note which type is supported by the operating system | ||
| notempty In setup step 2, two fundamentally different connection types are available for selection. Depending on whether a connection type of IKEv1, or IKEv2 is selected, the upcoming setup steps 3 and 4 differ:
| |||
Local – IKEv1 Step 3 - Local - IKEv1
| |||
| Local Gateway ID: | The gateway ID is included in the authentication. This can be an IP address, a host name or an interface. Automatically filled in when an X.509 certificate is selected. |
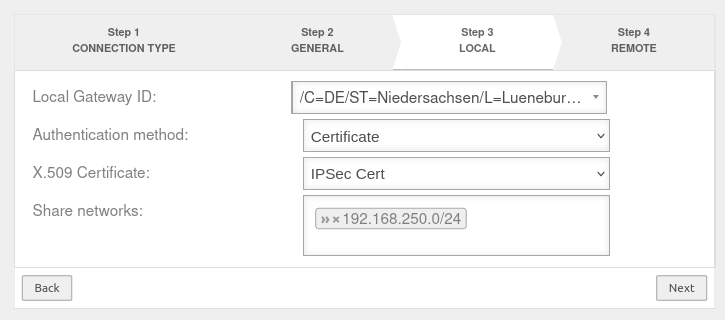 | |
| Authentication method: | A pre-shared key is in use | ||
| An existing certificate is being used | |||
| An existing private RSA key is in use | |||
| X.509 Certificate: Only for authentication method
|
Selection of a certificate | ||
| Privater RSA-Schlüssel: | Selecting an RSA key | ||
| Share networks: Only for IKEv1 - Native |
» ✕192.168.250.0/24 | Enable networks for the IPSec connection | |
Local – IKEv2 Step 3 - Local - IKEv2
| |||
| Local Gateway ID: | The gateway ID is included in the authentication. This can be an IP address, a host name or an interface. Automatically filled in when an X.509 certificate is selected. |
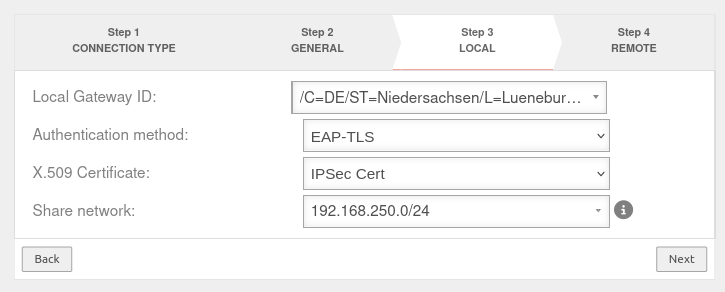 | |
| Authentication method | A pre-shared key is in use | ||
| An existing certificate is being used | |||
| An existing private RSA key is in use | |||
| Only with IKEv2 | EAP-TLS is used. Required for MSCHAPv2. | ||
| X.509 Certificate: Only for authentication method
|
Selection of a certificate | ||
| Private RSA key: | Selecting an RSA key | ||
| Share networks: | 192.168.250.0/24 | Enable networks for the IPSec connection | |
Remote terminal – IKEv1 Step 4 - Remote terminal - IKEv1
| |||
| Public RSA key: Only for authentication method RSA |
The required public RSA key of the remote terminal | 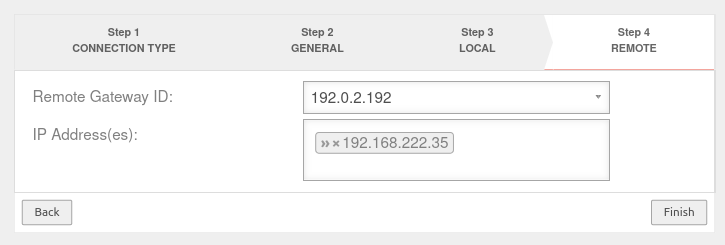 | |
| Remote Gateway ID: Only for IKEv1 - Native |
192.0.2.192 or My_Roadwarrior |
If more than one IPSec connection is established, a unique ID should be entered here. The password of incoming connections is validated against the ID of the IPSec connection. If no IP address is specified as ID, further settings must be made for site-to-site connections. | |
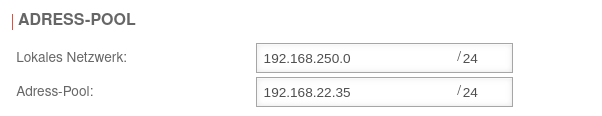
| IP address / pool: Only for IKEv1 - XAuth |
» ✕192.168.22.35/24 | IP address, or pool for establishing the IPSec connections | |
| Open user dialog after completion: Only with
|
Yes | Opens the user dialog of the UTM after the wizard is done. For the establishment of this connection the input of user data is necessary. The user needs the necessary rights. | |
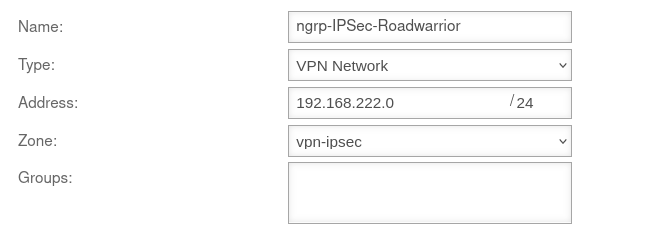
| IP Address(es): Only for IKEv1 - Native |
192.168.222.35 | Additional IP address for the Roadwarrior with which the IPSec connection is established.
| |
Remote terminal – IKEv2 Step 4 - Remote terminal - IKEv2
| |||
| Public RSA key: Only for authentication method RSA |
The required public RSA key of the remote terminal | 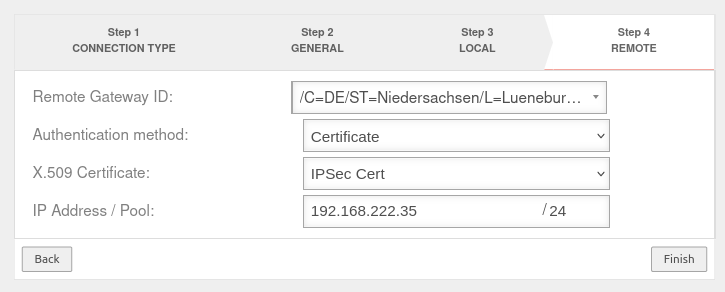 | |
| IP address / pool: | 192.168.22.35/24 | IP address, or pool for establishing the IPSec connections | |
| Authentication method Only for authentication method
|
An existing certificate is being used | ||
| EAP-MSCHAPV2 is in use | |||
| EAP-TLS is used. Required for MSCHAPv2. | |||
| X.509 Certificate: Only for authentication method
|
The certificate for the remote terminal. Two different certificates must be selected for the local and remote side. | ||
| User groups: Only for EAP-MSCHAPv2 |
Selection of the authorized user group. This must be created beforehand. | ||
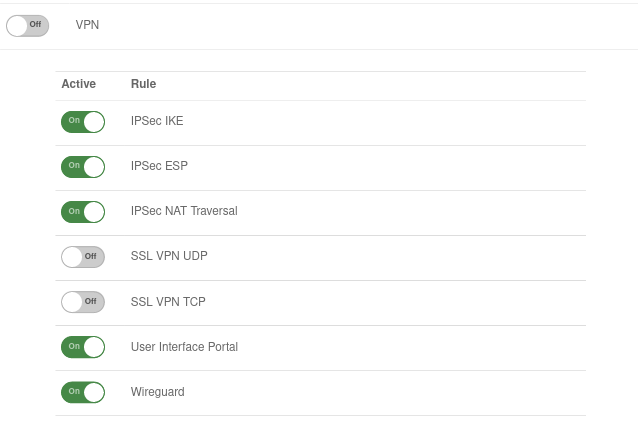
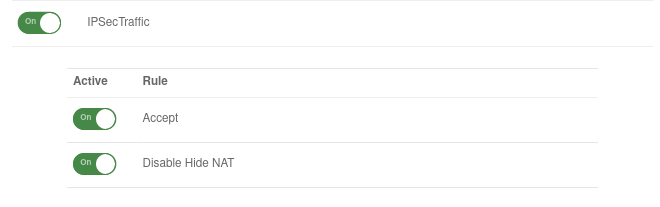
Set of rules
To grant access to the internal network, the connection must be allowed.
Packetfilter rules
Add portfilter rule at Button .
The first rule allows the IPSec tunnel to be built at all.
A second rule allows the Roadwarrior to access the desired network, host or network group.
| # | Source | Destination | Service | NAT | Action | Active | |||
| 4 | Accept | On | |||||||
| 5 | Accept | On |
Now a connection with a Roadwarrior can be established.
A client may have to be used for this. It must be ensured that the parameters on both sides are identical in all phases of the connection.
Necessary changes, when using an NCP client:
- UTM
- Diffie-Hellman Group (Phase 1)
- DH-Group (PFS) (Phase 2)
or
- NCP- or Greenbow-Client:
- IKE-DH-Group
Additionally when using IKEv1:
- NCP- or Greenbow-Client:
- Exchange mode: Main Mode (IKEv1)
- Activate Config_mode
Additional settings
In addition to the settings that have already been set in the wizard, further parameters can be configured:
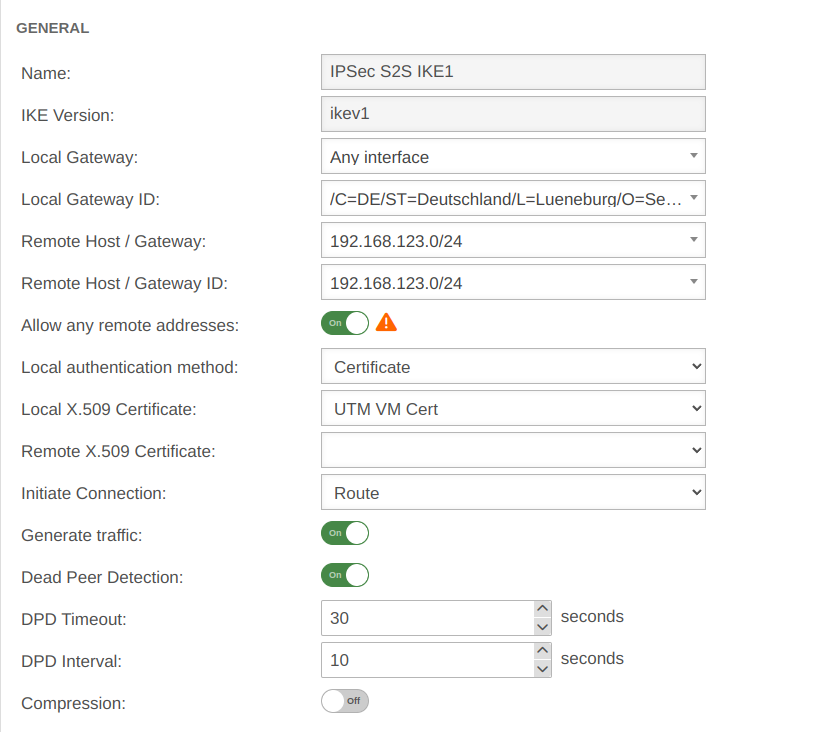
IKEv1
Phase 1 | ||||||
Area Connections Button GeneralGeneral | ||||||
| Caption | Value | Description | UTMuser@firewall.name.fqdnVPNIPSec 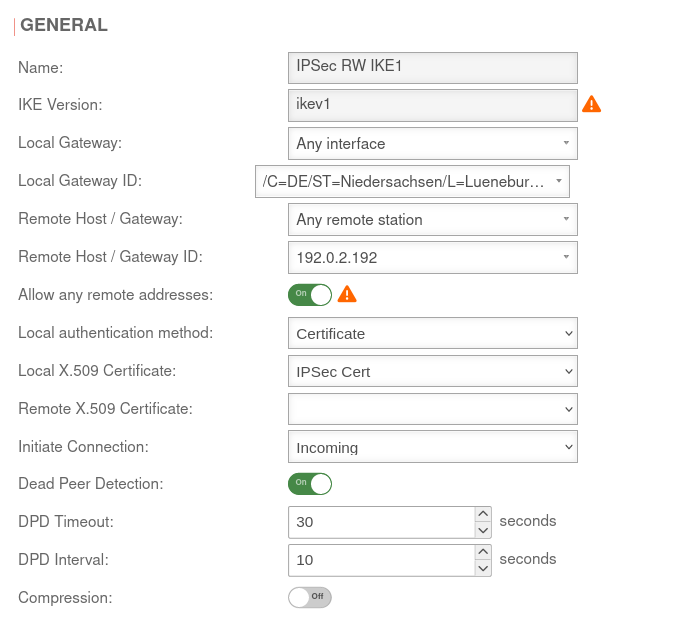 Phase 1 Genereal Phase 1 Genereal
|
|||
|---|---|---|---|---|---|---|
| Allow any remote addresses: | On Default |
Disable this option for site-to-site connections with DynDNS hosts if multiple IPsec connections with a priori unknown addresses (DynDNS S2S, Roadwarrior) are configured. | ||||
| Startup behavior: | The tunnel is initiated by the UTM even if no packets are sent. Incoming requests are accepted. | |||||
| Default if Remote Host is any | The UTM accepts incoming tunnel requests. No outgoing connection is created. | |||||
| Default if Remote Host known | The tunnel is initiated by the UTM only when packets are to be sent.notempty Only set as default value if Any remote station is not selected as Remote Host / Gateway.
| |||||
| Deactivates the tunnel | ||||||
| Dead Peer Detection: | On | Checks at a set interval whether the tunnel still exists. If the tunnel was terminated unexpectedly, the SAs are dismantled. (Only then it is also possible to reestablish a new tunnel). | ||||
| DPD Timeout: | 30 seconds | Period before the state under Startup behavior is restored. The same values are used here as for regular packets. | ||||
| DPD Interval: | 10 seconds | Testing interval | ||||
| Compression: | Off | Compression is not supported by all remote stations | ||||
| Enable MOBIKE: | Yes | Used to deactivate the MOBIKE option Deactivation prevents encrypted data from a remote station from being additionally encapsulated in 4500udp, which leads to problems in communication. | ||||
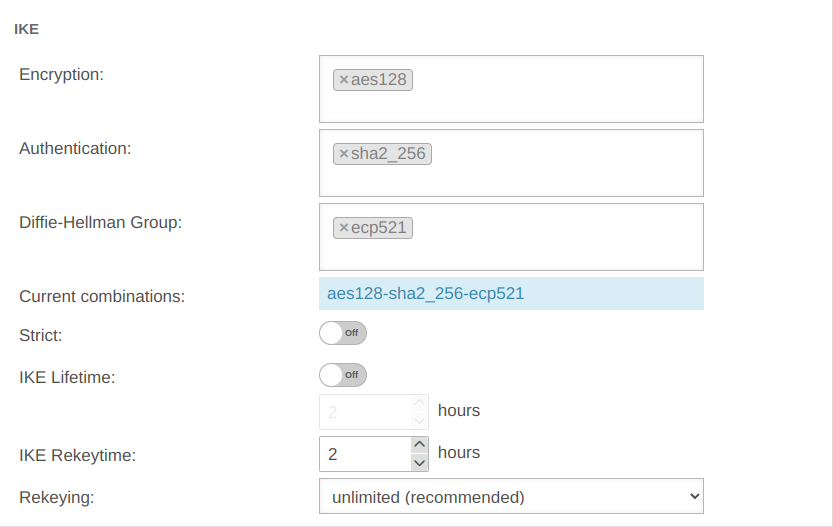
Section IKE Settings that must be identical in the UTM and in the client: IKE | ||||||
| Caption | Default UTM | Default NCP Client | 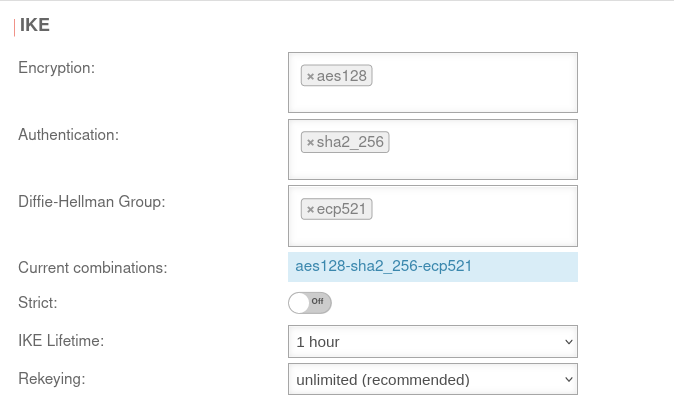 |
 | ||
| Encryption: | » ✕aes128 | AES 128 Bit | ||||
| Authentication: | » ✕sha2_256 | Hash: SHA2 256 Bit | ||||
| Diffie-Hellman Group: | » ✕ecp521 | IKE DH-Gruppe: DH2 (modp1024) | ||||
| Aktuelle Kombinationen: | aes128-sha2_256-ecp521 | |||||
| Section IKE More settings: | ||||||
| Caption | Value | Description | ||||
| Strict: | Off | The configured parameters (authentication and encryption algorithms) are preferred for connections | ||||
| On | No further proposals are accepted. A connection is only possible with the configured parameters. | |||||
| IKE Life time: | Out 3 hours | Validity period of the Security Association: Agreement between two communicating entities in computer networks. It describes how the two parties apply security services to communicate securely with each other. When using multiple services, multiple security connections must also be established. (Source: Wikipedia 2022) in phase 1 Can be activated On in addition to IKE Rekeytime. If the Lifetime is set, the value must be greater than the Rekeytime. | ||||
| IKE Life time: | Validity period of the Security Association: Agreement between two communicating entities in computer networks. It describes how the two parties apply security services to communicate securely with each other. When using multiple services, multiple security connections must also be established. (Source: Wikipedia 2022) in phase 1 | |||||
| IKE Rekeytime: | 2 hours | The validity period in which the connection is established (initial or after termination) | ||||
| notempty Starting with version 12.5.0, for already existing' connections that have no rekeytime' set, the value of the lifetime is entered at this point and the value of the lifetime is set to 0.
This significantly increases the stability of the connection and should not bring any disadvantages. If a value has already been set for the rekeytime (possible from v12.4) no change is made. Example: Current version: ike_lifetime = 2 ike_rekeytime = 0 After update: ike_lifetime = 0 ike_rekeytime = 2 ---- Current version: ike_lifetime = 2 ike_rekeytime = 1 After update: (without change) ike_lifetime =2 ike_rekeytime = 1 | ||||||
| Rekeying: | Number of attempts to establish the connection (initial or after abort). For E2S connections (Roadwarrior), the setting 3 times can avoid endless attempts to connect to devices that are not correctly logged out. | |||||
Phase 2 | ||||||
Area Connections Button GeneralSection General Settings that must be identical in the UTM and in the client: | ||||||
| Caption | Default UTM | Default NCP Client | UTMuser@firewall.name.fqdnVPNIPSec 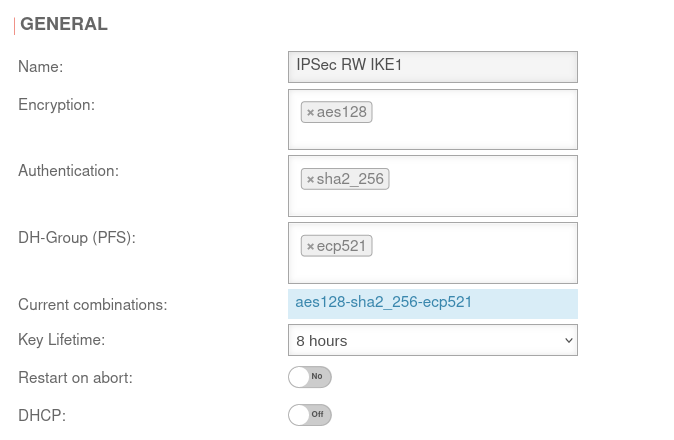 Phase 2 / Section General with / IKEv1 / Roadwarrior Phase 2 / Section General with / IKEv1 / Roadwarrior
|
UTMuser@firewall.name.fqdnVPNIPSec 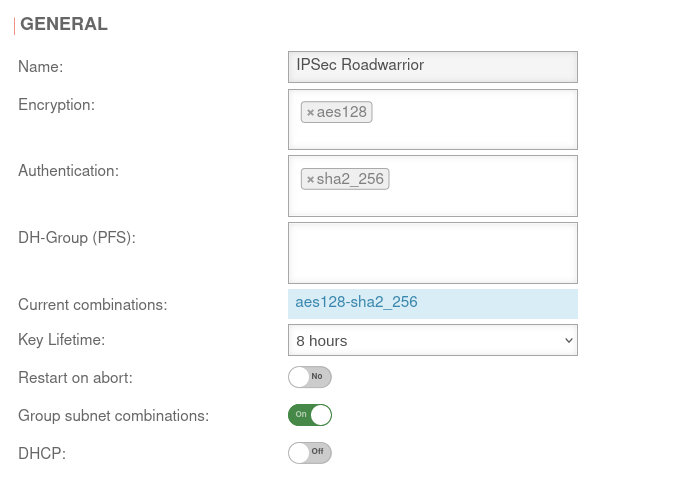 Phase 2 / Section General with / IKEv2 / Roadwarrior Phase 2 / Section General with / IKEv2 / Roadwarrior
|
UTMuser@firewall.name.fqdnVPNIPSec 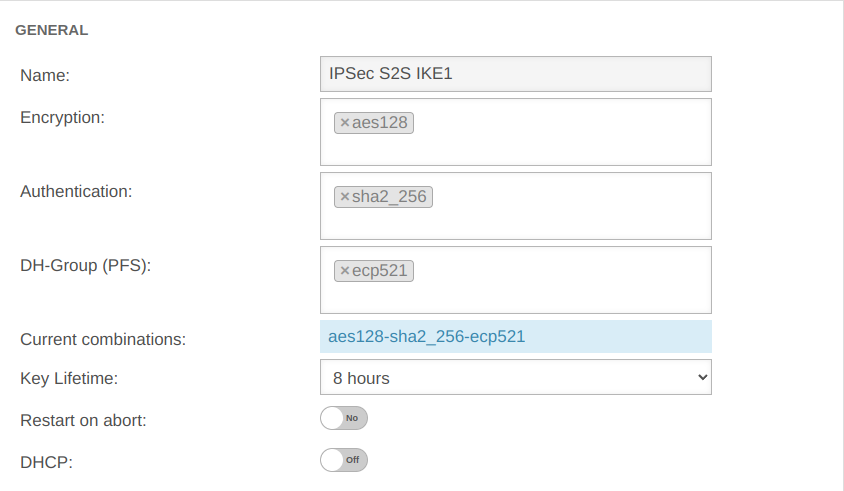 Phase 2 / Section General with / IKEv1 / S2S Phase 2 / Section General with / IKEv1 / S2S
|
UTMuser@firewall.name.fqdnVPNIPSec 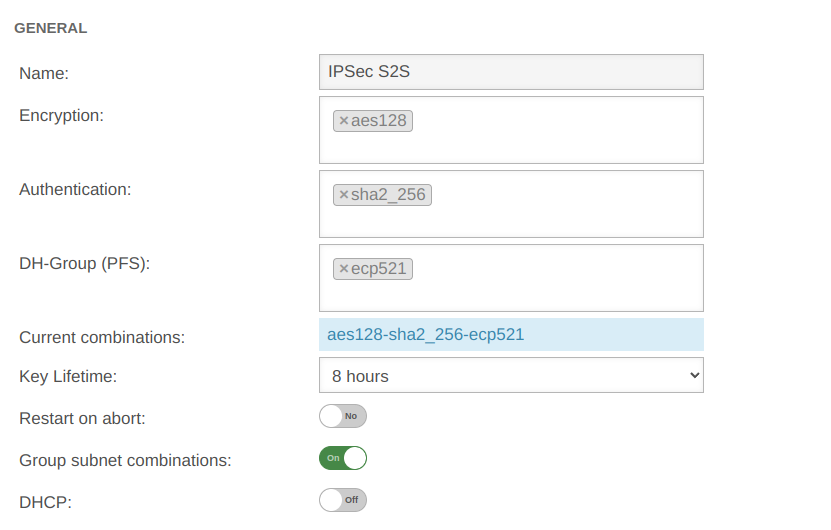 Phase 2 / Section General with / IKEv2 / S2S Phase 2 / Section General with / IKEv2 / S2S
|
| Encryption: | » ✕aes128 | AES 128 Bit | ||||
| Authentication: | » ✕sha2_256 | SHA2 256 Bit | ||||
| Diffie-Hellman Group: | » ✕ecp521 | IKE DH-Gruppe: DH2 (modp1024) | ||||
| Diffie-Hellman Group: | » ✕ecp521 | IKE DH-Gruppe: DH2 (modp1024) | ||||
| Aktuelle Kombinationen: | aes128-sha2_256-ecp521 | |||||
| Schlüssel-Lebensdauer: | Validity period of the key in phase 2 | |||||
| Austausch-Modus: | Main Mode (nicht konfigurierbar) | Aggressive Mode (IKEv1) The UTM does not support Aggressive Mode for security reasons. | ||||
| Restart on abort: | No | If the connection was terminated unexpectedly, activating will restore the state configured under Startup behavior in phase 1. The Dead Peer Detection is automatically activated in phase 1.
| ||||
| DHCP: | Out | When enabled clients receive IP addresses from a local network. This requires further configurations, see wiki article on DHCP for IPSec.
| ||||
SubnetsSection Subnets | |||
| Scenario: All subnets have access to each other
With an SSH login as root, the behavior can be understood particularly well.
|
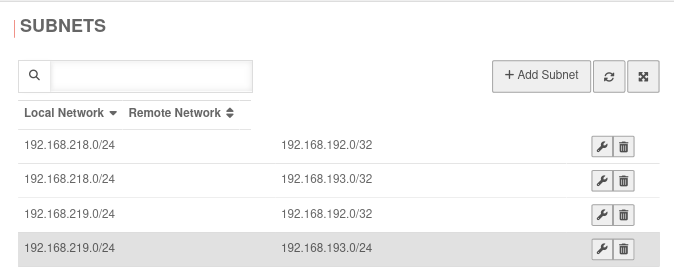 | ||
| Scenario: Not all subnets may access every network of the remote gateway
If in phase two a local network is not connected to all remote networks (or a remote network is not connected to all local ones), this will not be taken into account if the option Group subnet combinations is active! notempty The Group subnet combinations option will connect all local networks to all remote networks!
notempty Port filter rules make it possible to control access.
With an SSH login as root, the behavior can be understood particularly well.
|
Datei:UTM v12.6.2 VPN Ipsec RW IKEv1 Phase 2 reduzierte Subnetze-enpng | ||
Troubleshooting
Detailed Troubleshooting instructions can be found in the Troubleshooting Guide.
If an email address should be used as gateway ID, it is necessary to insert a double @@ in front of the ID (mail@... becomes @@mail@...). Otherwise the ID will be treated as FQDN.
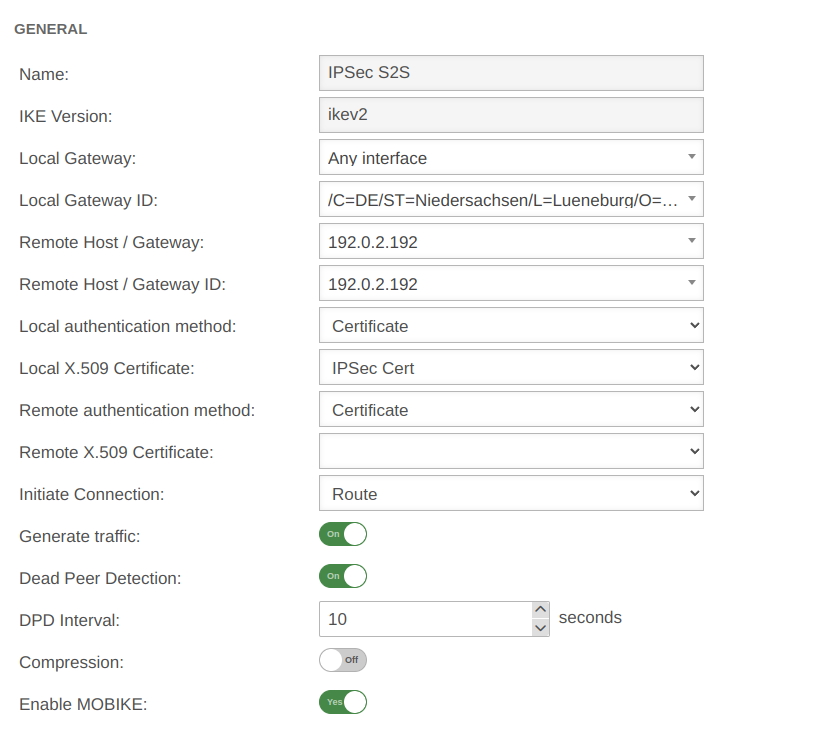
IKEv2
Phase 1 | ||||||
Area Connections Button GeneralGeneral | ||||||
| Caption | Value | Description | UTMuser@firewall.name.fqdnVPNIPSec 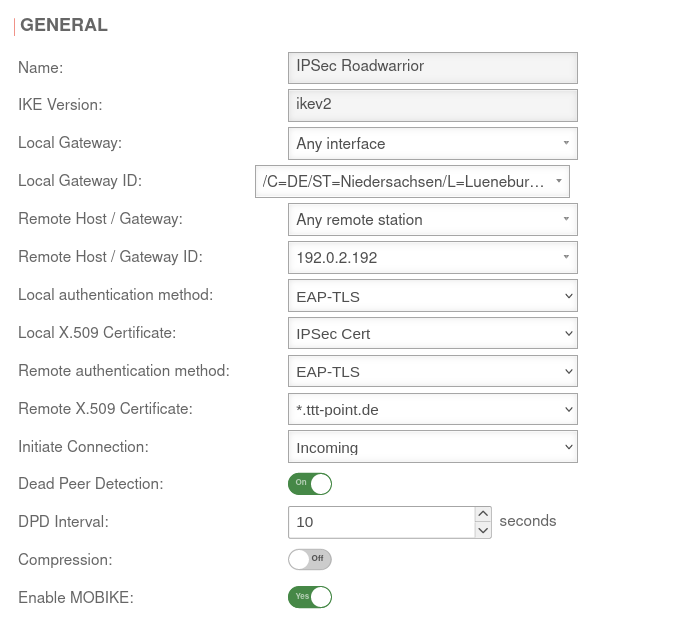 Phase 1 Genereal Phase 1 Genereal
|
|||
|---|---|---|---|---|---|---|
| Startup behavior: | The tunnel is initiated by the UTM even if no packets are sent. Incoming requests are accepted. | |||||
| Default if Remote Host is any | The UTM accepts incoming tunnel requests. No outgoing connection is created. | |||||
| Default if Remote Host known | The tunnel is initiated by the UTM only when packets are to be sent.notempty Only set as default value if Any remote station is not selected as Remote Host / Gateway.
| |||||
| Deactivates the tunnel | ||||||
| Dead Peer Detection: | On | Checks at a set interval whether the tunnel still exists. If the tunnel was terminated unexpectedly, the SAs are dismantled. (Only then it is also possible to reestablish a new tunnel). | ||||
| DPD Timeout: | 30 seconds | Period before the state under Startup behavior is restored. The same values are used here as for regular packets. | ||||
| DPD Interval: | 10 seconds | Testing interval | ||||
| Compression: | Off | Compression is not supported by all remote stations | ||||
| Enable MOBIKE: | Yes | Used to deactivate the MOBIKE option Deactivation prevents encrypted data from a remote station from being additionally encapsulated in 4500udp, which leads to problems in communication. | ||||
Section IKE Settings that must be identical in the UTM and in the client: IKE | ||||||
| Caption | Default UTM | Default NCP Client | 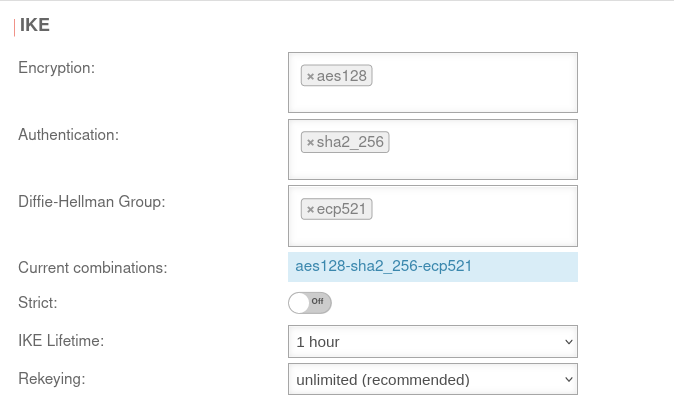 |
 | ||
| Encryption: | » ✕aes128 | AES 128 Bit | ||||
| Authentication: | » ✕sha2_256 | Hash: SHA2 256 Bit | ||||
| Diffie-Hellman Group: | » ✕ecp521 | IKE DH-Gruppe: DH2 (modp1024) | ||||
| Aktuelle Kombinationen: | aes128-sha2_256-ecp521 | |||||
| Section IKE More settings: | ||||||
| Caption | Value | Description | ||||
| Strict: | Off | The configured parameters (authentication and encryption algorithms) are preferred for connections | ||||
| On | No further proposals are accepted. A connection is only possible with the configured parameters. | |||||
| IKE Life time: | Out 3 hours | Validity period of the Security Association: Agreement between two communicating entities in computer networks. It describes how the two parties apply security services to communicate securely with each other. When using multiple services, multiple security connections must also be established. (Source: Wikipedia 2022) in phase 1 Can be activated On in addition to IKE Rekeytime. If the Lifetime is set, the value must be greater than the Rekeytime. | ||||
| IKE Life time: | Validity period of the Security Association: Agreement between two communicating entities in computer networks. It describes how the two parties apply security services to communicate securely with each other. When using multiple services, multiple security connections must also be established. (Source: Wikipedia 2022) in phase 1 | |||||
| IKE Rekeytime: | 2 hours | The validity period in which the connection is established (initial or after termination) | ||||
| notempty Starting with version 12.5.0, for already existing' connections that have no rekeytime' set, the value of the lifetime is entered at this point and the value of the lifetime is set to 0.
This significantly increases the stability of the connection and should not bring any disadvantages. If a value has already been set for the rekeytime (possible from v12.4) no change is made. Example: Current version: ike_lifetime = 2 ike_rekeytime = 0 After update: ike_lifetime = 0 ike_rekeytime = 2 ---- Current version: ike_lifetime = 2 ike_rekeytime = 1 After update: (without change) ike_lifetime =2 ike_rekeytime = 1 | ||||||
| Rekeying: | Number of attempts to establish the connection (initial or after abort). For E2S connections (Roadwarrior), the setting 3 times can avoid endless attempts to connect to devices that are not correctly logged out. | |||||
Phase 2 | ||||||
Area Connections Button GeneralSection General Settings that must be identical in the UTM and in the client: | ||||||
| Caption | Default UTM | Default NCP Client | UTMuser@firewall.name.fqdnVPNIPSec 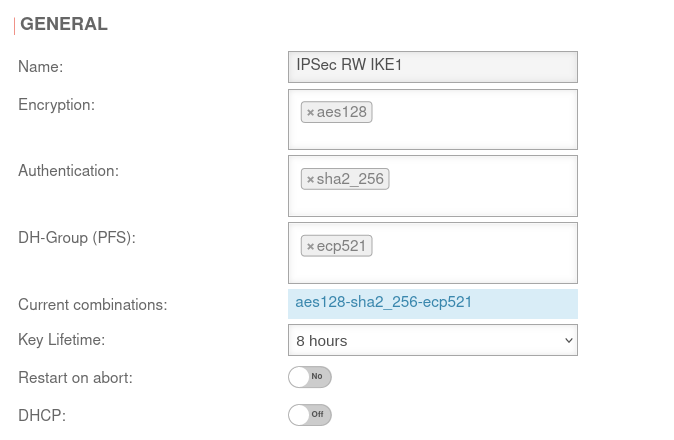 Phase 2 / Section General with / IKEv1 / Roadwarrior Phase 2 / Section General with / IKEv1 / Roadwarrior
|
UTMuser@firewall.name.fqdnVPNIPSec 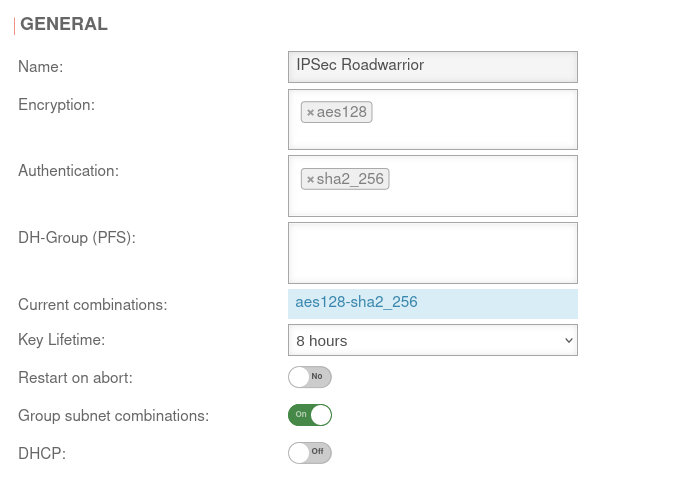 Phase 2 / Section General with / IKEv2 / Roadwarrior Phase 2 / Section General with / IKEv2 / Roadwarrior
|
UTMuser@firewall.name.fqdnVPNIPSec 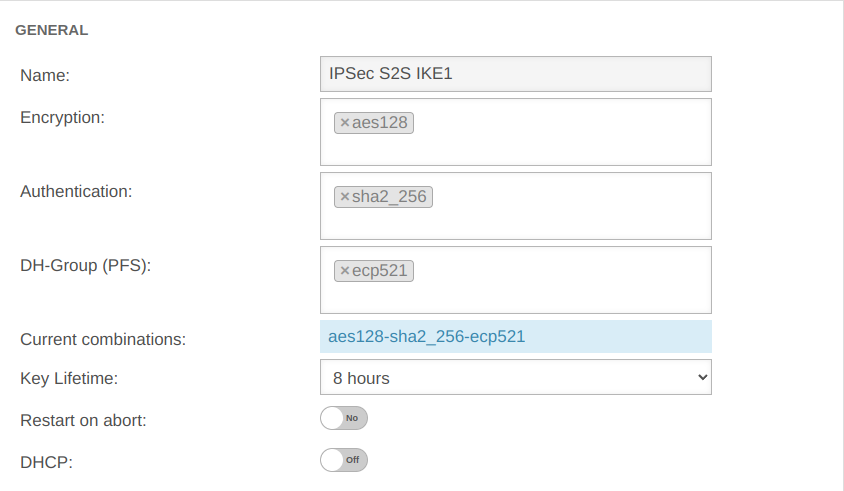 Phase 2 / Section General with / IKEv1 / S2S Phase 2 / Section General with / IKEv1 / S2S
|
UTMuser@firewall.name.fqdnVPNIPSec 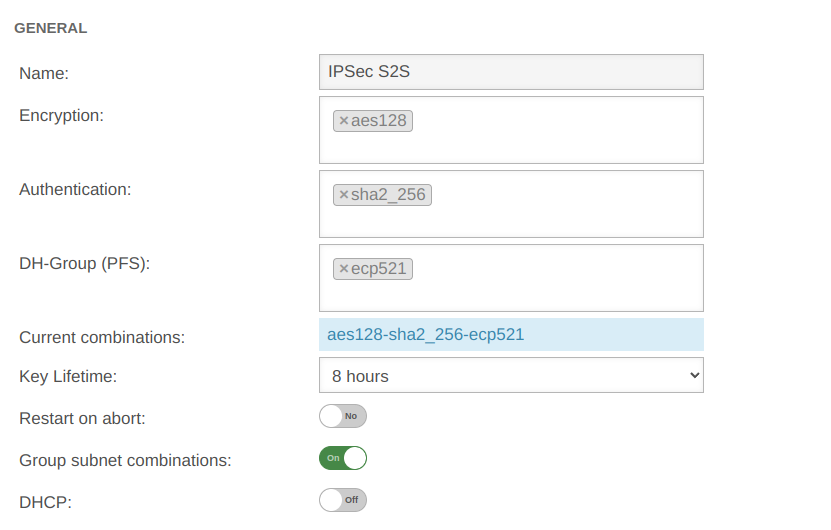 Phase 2 / Section General with / IKEv2 / S2S Phase 2 / Section General with / IKEv2 / S2S
|
| Encryption: | » ✕aes128 | AES 128 Bit | ||||
| Authentication: | » ✕sha2_256 | SHA2 256 Bit | ||||
| Diffie-Hellman Group: | » ✕ecp521 | IKE DH-Gruppe: DH2 (modp1024) | ||||
| Diffie-Hellman Group: | » ✕ecp521 | IKE DH-Gruppe: DH2 (modp1024) | ||||
| Aktuelle Kombinationen: | aes128-sha2_256-ecp521 | |||||
| Schlüssel-Lebensdauer: | Validity period of the key in phase 2 | |||||
| Austausch-Modus: | Main Mode (nicht konfigurierbar) | Aggressive Mode (IKEv1) The UTM does not support Aggressive Mode for security reasons. | ||||
| Restart on abort: | No | If the connection was terminated unexpectedly, activating will restore the state configured under Startup behavior in phase 1. The Dead Peer Detection is automatically activated in phase 1.
| ||||
| Group subnet combinations: | Yes |
If more than one network is configured on the local side or at the remote gateway, a separate SA is negotiated for each subnet combination when it is deactivated. This results in numerous subnet combinations and thus many SAs, especially with multiple subnets, and leads to limitations and losses in the stability of the connections due to the design of the IPSec protocol. | ||||
| DHCP: | Out | When enabled clients receive IP addresses from a local network. This requires further configurations, see wiki article on DHCP for IPSec.
| ||||
Troubleshooting
Detailed Troubleshooting instructions can be found in the Troubleshooting Guide.
If an email address should be used as gateway ID, it is necessary to insert a double @@ in front of the ID (mail@... becomes @@mail@...). Otherwise the ID will be treated as FQDN.
Connection Rate Limit
Throttling of access from certain source IPs to recurring ports
notempty
If the rate limit is set too low, unexpected effects may occur, e.g. services may be restricted.
notempty
The function can initially only be configured via the CLI
SSL-VPN accesses can be protected against aggressive scans or login attempts, for example.
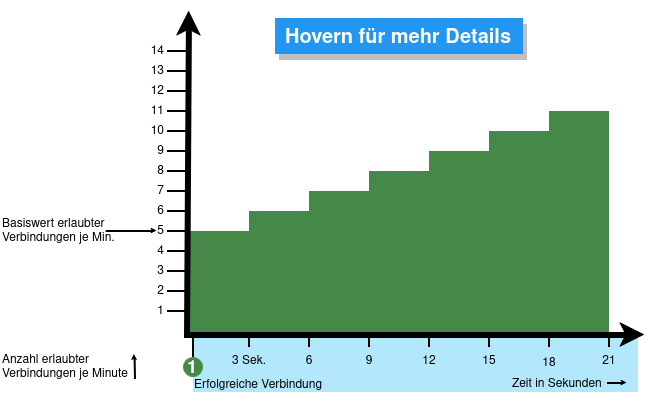
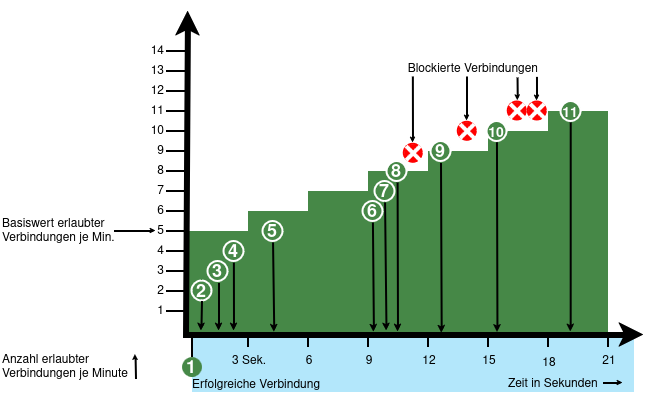
From v12.6.2, the UTM can limit the number of TCP and/or UDP connections from an external IP address to one port.
The following conditions apply:
- Only incoming connections for which a default route exists are monitored
- The connections from an IP address to a port of the UTM are counted within one minute
- When activated, 5 connections / connection attempts per minute are permitted.
The connections are then limited:- The additionally permitted connections are distributed evenly within 60 seconds of the first connection.
- With a CONNECTION_RATE_LIMIT value of 20, an additional connection is added every 3 seconds.
- 10 seconds after the first login, 3 further connections could be established (each from the same IP address to the same destination port)
- Blocking an IP address only affects access to the port that has been used too often.
Other ports can still be accessed.
- The function is activated by default for new installations on 20 UDP connections / minute on all ports
- For Updates the function must be manually activated
| extc-Variable | Default-Value | Description |
|---|---|---|
| CONNECTION_RATE_LIMIT_TCP | 0 | Number of permitted TCP connections of an IP address per port 0 = Function deactivated, no blocking is performed |
| CONNECTION_RATE_LIMIT_TCP_PORTS | Ports to be monitored. Empty by default=all ports would be monitored (if activated). Individual ports are separated by spaces: [ 1194 1195 ] | |
| CONNECTION_RATE_LIMIT_UDP | 20 / 0 Default setting for new installations from v12.6.2: 20 For update installations the value is 0, so the function is deactivated. |
Number of permitted UDP connections of an IP address per port |
| CONNECTION_RATE_LIMIT_UDP_PORTS | Ports to be monitored. Empty by default=all ports are monitored (only for new installations!). Individual ports are separated by spaces: [ 1194 1195 ] |
Configuration with CLI commands
| CLI command | Function |
|---|---|
| extc value get application securepoint_firewall Alternatively as root user: spcli extc value get application securepoint_firewall | grep RATE |
Lists all variables of the securepoint_firewall application. The variables beginning with CONNECTION_RATE_LIMIT_ are responsible for the connection limit. application |variable |value --------------------+-------------------------------+----- securepoint_firewall |… |… |CONNECTION_RATE_LIMIT_TCP |0 |CONNECTION_RATE_LIMIT_TCP_PORTS| |CONNECTION_RATE_LIMIT_UDP |20 |CONNECTION_RATE_LIMIT_UDP_PORTS| |
| extc value set application securepoint_firewall variable CONNECTION_RATE_LIMIT_TCP value 20 system update rule |
Limits the allowed number of TCP connections from a single IP address to a specific port to 20 per minute |
| extc value set application securepoint_firewall variable CONNECTION_RATE_LIMIT_TCP value 0 system update rule |
Deactivates the monitoring of TCP connections |
| extc value set application securepoint_firewall variable CONNECTION_RATE_LIMIT_TCP_PORTS value [ 443 11115 ] system update rule |
Restricts the monitoring of TCP connections to ports 443 and 11115 There must be spaces before and after the square brackets [ ]! |
| extc value set application securepoint_firewall variable CONNECTION_RATE_LIMIT_TCP_PORTS value [ ] system update rule |
A NULL value removes the restriction to certain ports There must be spaces before and after the square brackets [ ]! |
| extc value set application securepoint_firewall variable CONNECTION_RATE_LIMIT_UDP value 20 system update rule |
Limits the allowed number of UDP connections from a single IP address to a specific port to 20 per minute Default setting for new installations from v12.6.2: 20 For update installations the value is 0, so the function is deactivated. |
| extc value set application securepoint_firewall variable CONNECTION_RATE_LIMIT_UDP value 0 system update rule |
Deactivates the monitoring of UDP connections |
| extc value set application securepoint_firewall variable CONNECTION_RATE_LIMIT_UDP_PORTS value [ 1194 1195 ] system update rule |
Restricts the monitoring of UDP connections to ports 1194 and 1195. (Example for 2 created SSL-VPN tunnels). There must be spaces before and after the square brackets [ ]! |
| extc value set application securepoint_firewall variable CONNECTION_RATE_LIMIT_UDP_PORTS value [ ] system update rule |
A NULL value removes the restriction to certain ports There must be spaces before and after the square brackets [ ]! |
extc value set application securepoint_firewall variable CONNECTION_RATE_LIMIT_TCP value 20 notempty Finally, the CLI command system update rule must be entered so that the values in the rules are applied.
|
For example, to allow a maximum of 20 connections per minute per IP address and port. For TCP, monitoring is restricted to ports 443 and 11115. All ports are monitored for UDP connections. |