Configure Azure Apps with OAuth for the UTM Mail Connector
Last adaptation to the version: 12.6.0
New:
- Updated to Redesign of the webinterface
notempty
This article refers to a Resellerpreview
- Preliminary note
This article includes descriptions of third-party software and is based on the status at the time this page was created.
Changes to the user interface on the part of the manufacturer are possible at any time and must be taken into account accordingly in the implementation.
All information without warranty.
- Application ID
- Client ID
- Secret client key
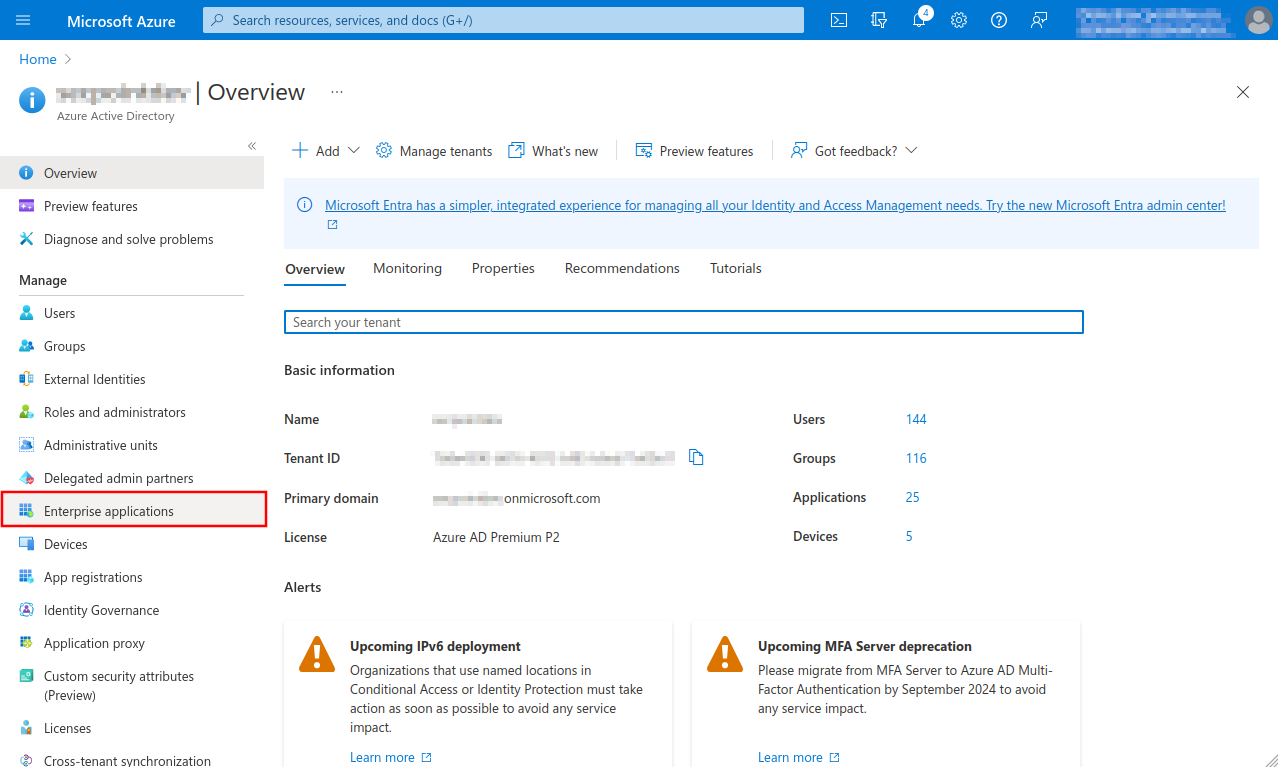
- Launch Azure Active Directory admin center
- Note down/Copy Tenant ID from the Azure Active Directory menu
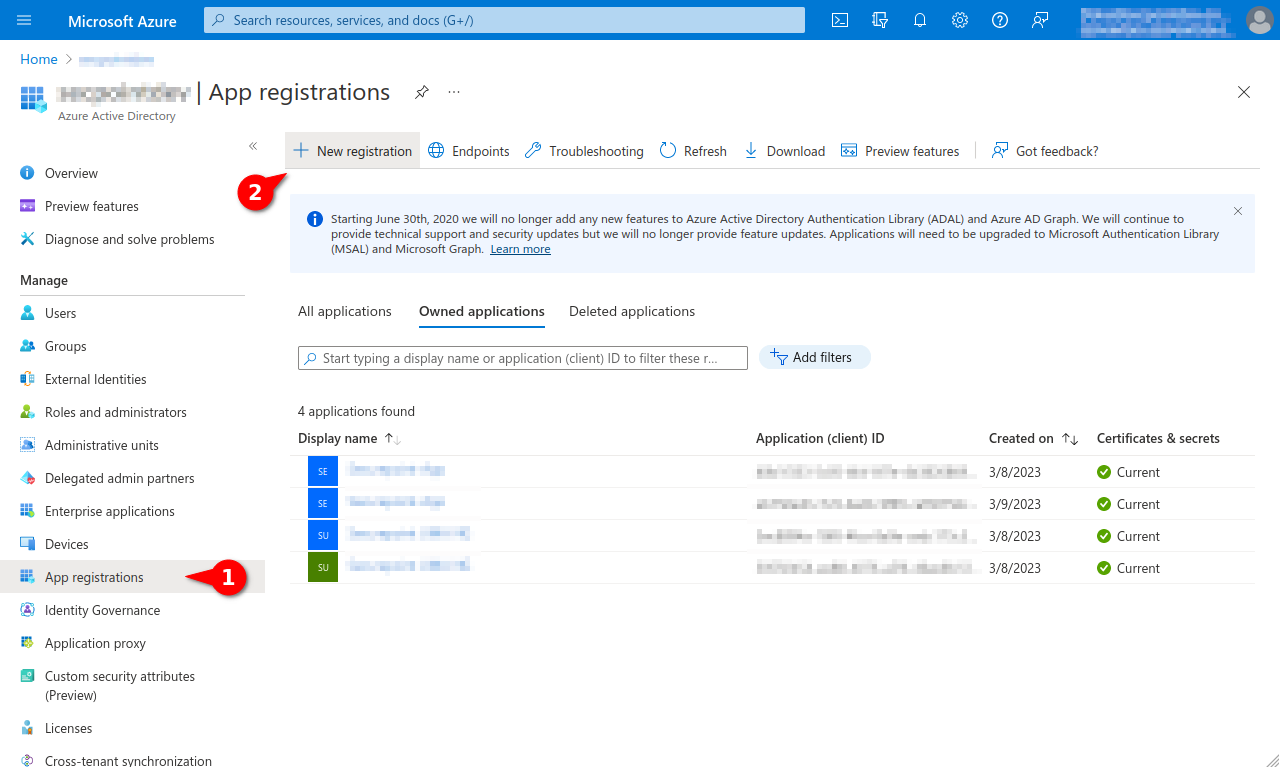
- Register new app under theApp registration menu under the New registration button
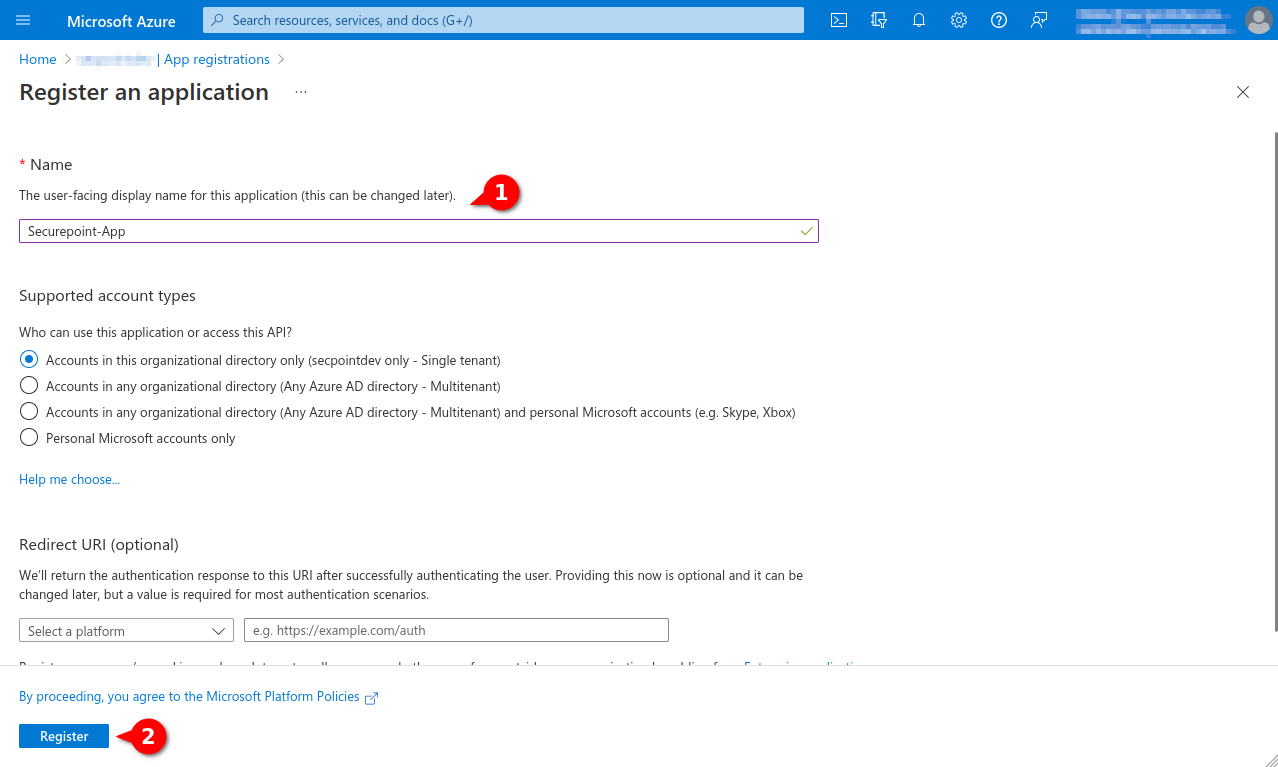
- Assign a unique name and click the register button
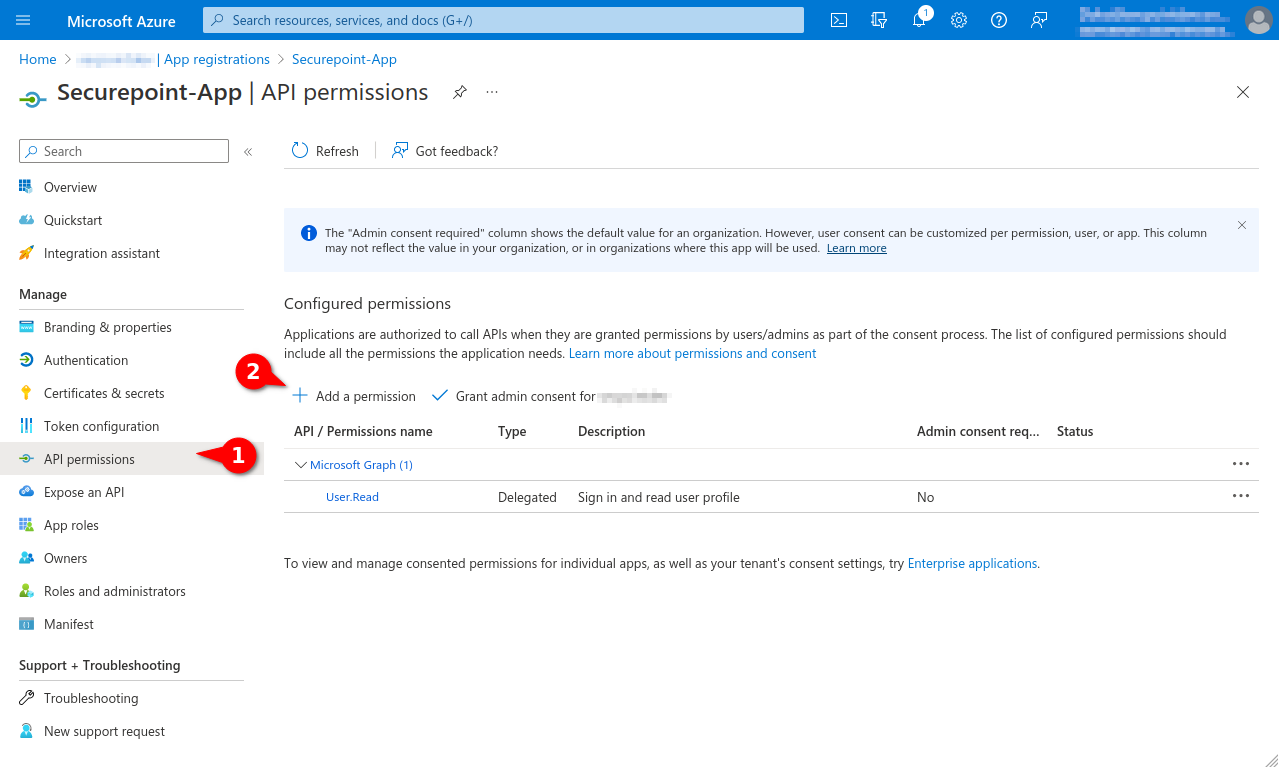
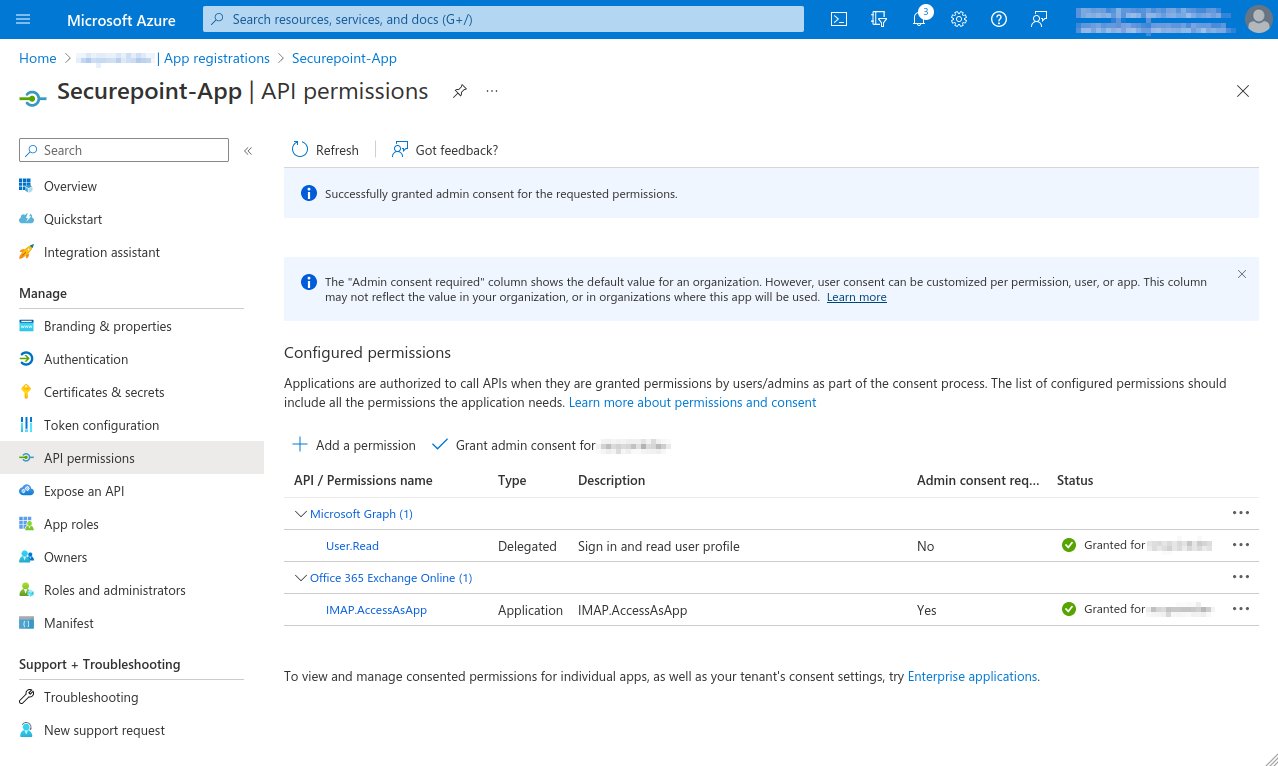
- In the API permissions menu, click the Add a permission button.
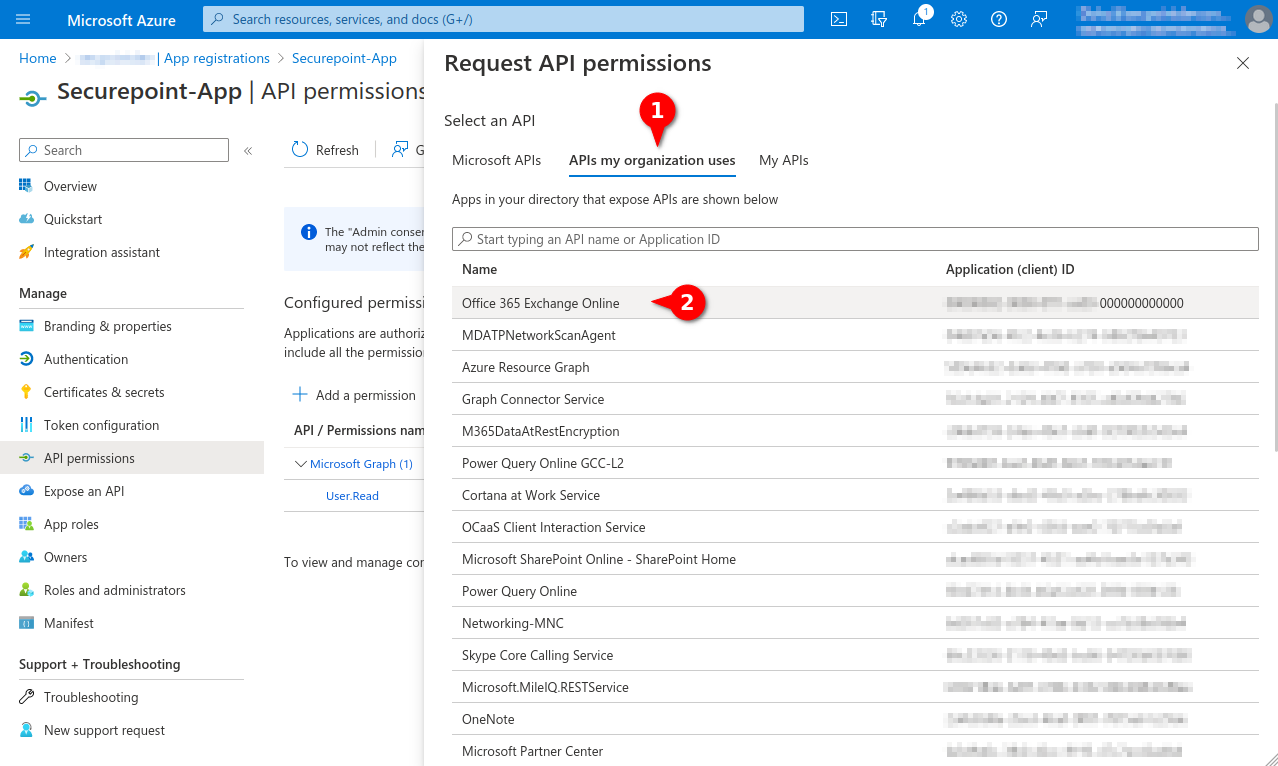
- Select permission for Office 365 Exchange Online in the APIs my organization uses tab
- Add IMAP.AccessAsApp permission for Office 365 Exchange Online
- In the menu API permissions activate the entry Grant admin consent for [...].
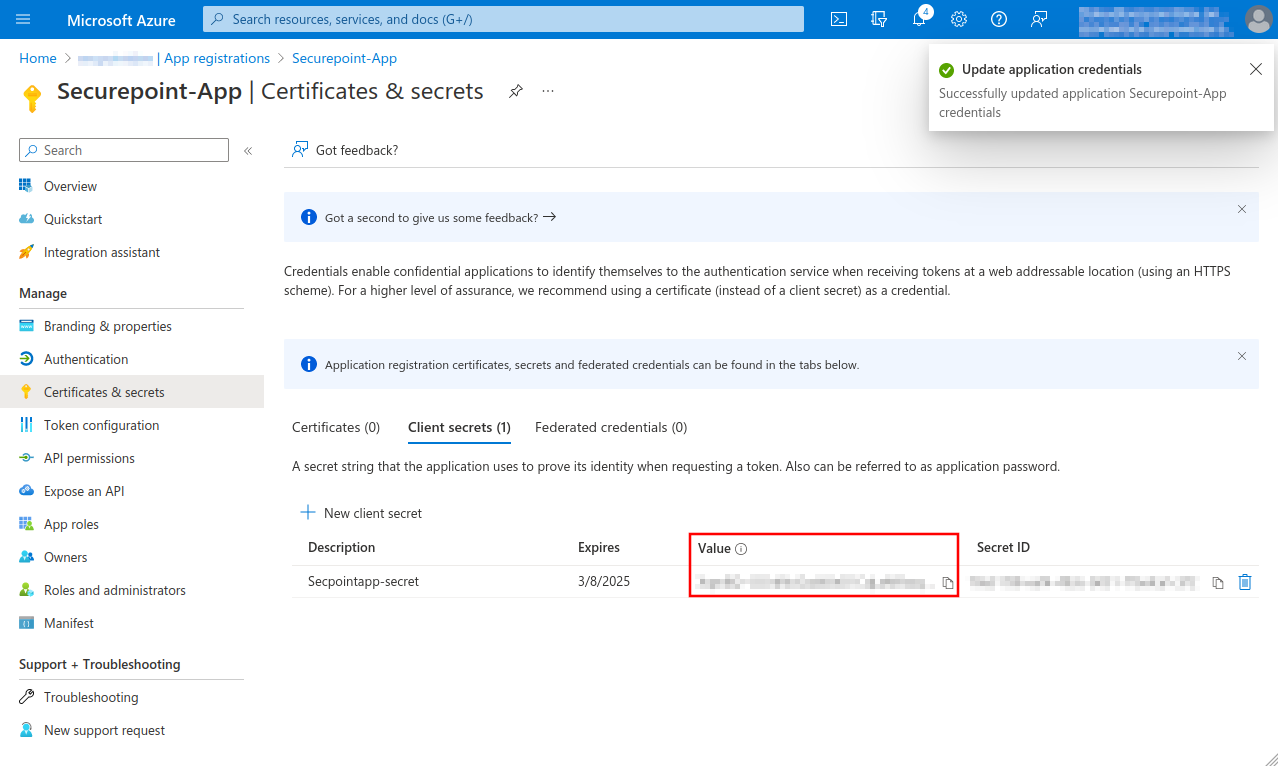
- Create a Client secret in the Certificates & secrets menu
- Note down Value, will be entered as Secret Client Key when adding an OAuth 2 connection
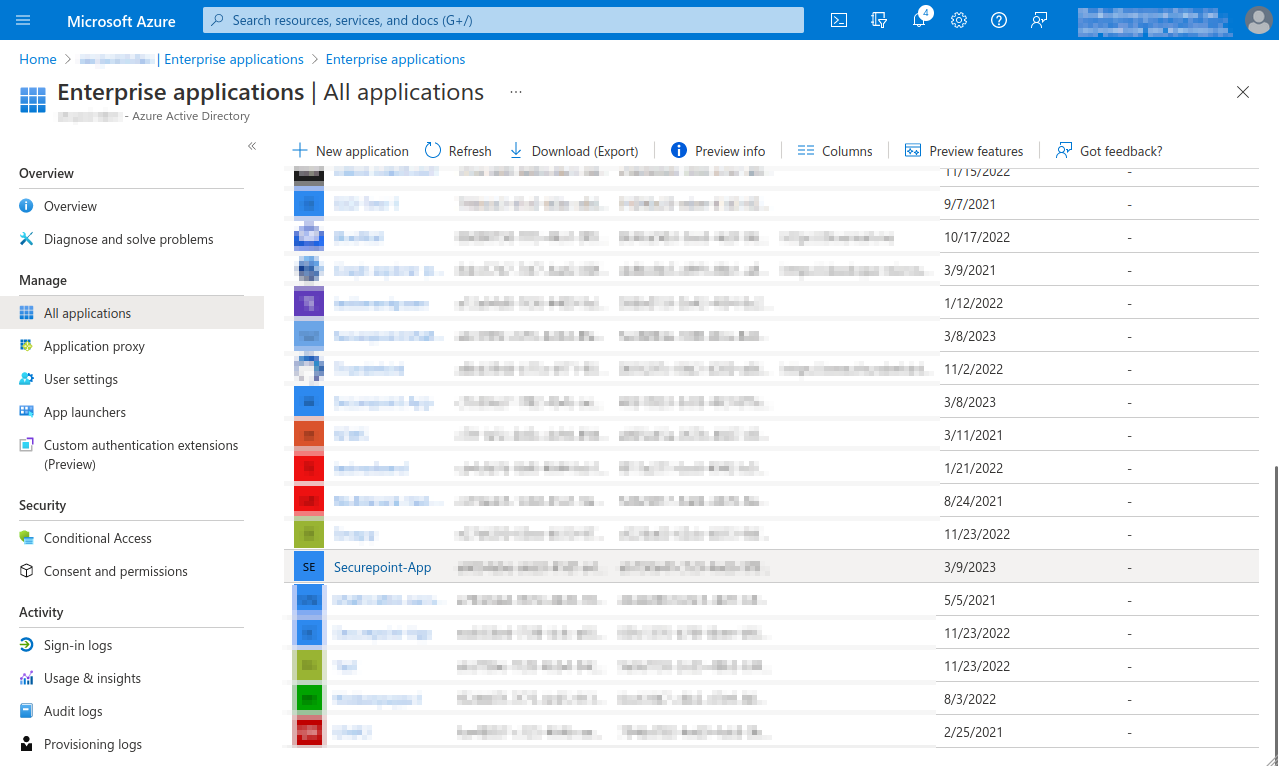
- Open menu Enterprise Applications and select app
- Note down from the app properties Application ID and Object ID.
- Open Powershell on Windows Client Administrator, import ExchangeOnlineManagement and connect to tenant
- Select the recipient mailbox in the Exchange admin center and choose Read and manage (Full Access) as delegation.
- Add member for Mailbox Delegation
- This completes the configuration in Microsoft Azure.
The further configuration is done in the UTM in the menu
Area Services Button
anf in the tab
OAuth2 with the button.
- notemptyThe Microsoft servers may take up to 30 minutes before access works
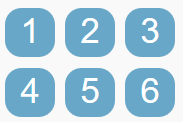
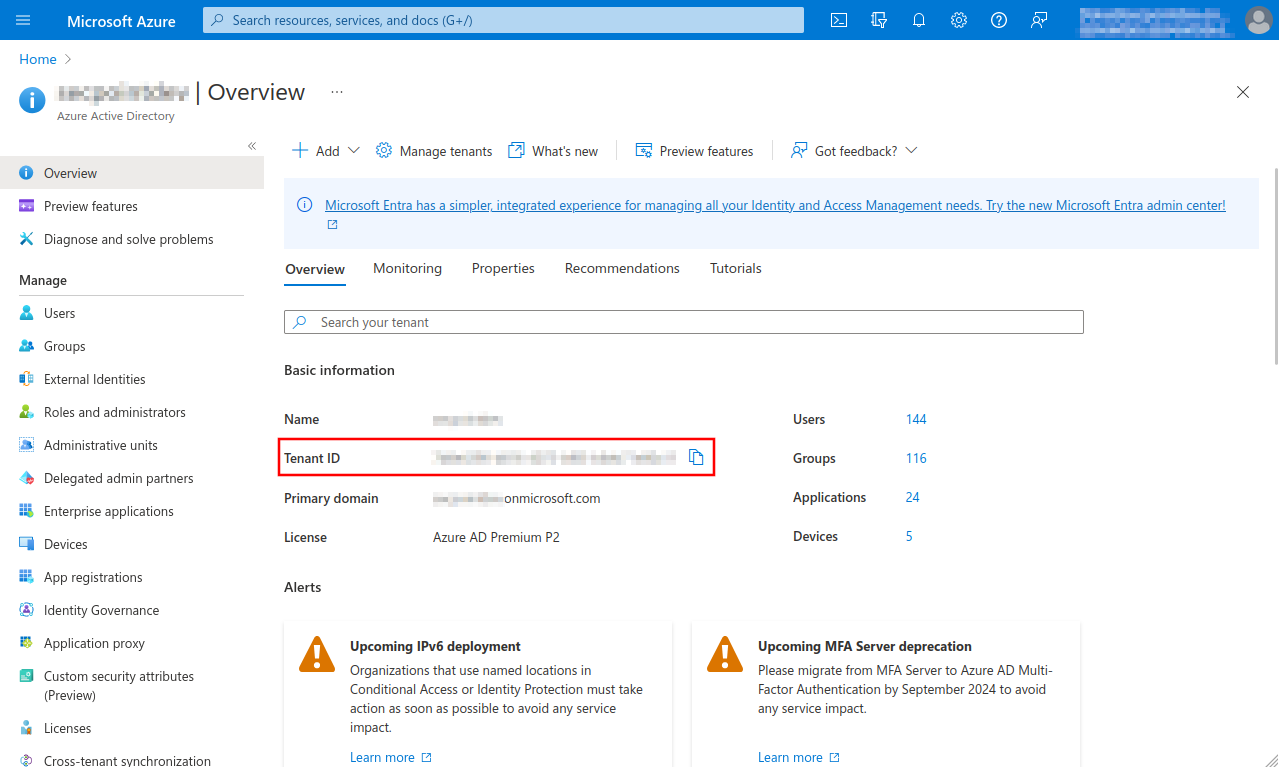
Fig.1
- Select Azure Active Directory menu
- Note down or copy Tenant ID, is entered when adding an OAuth 2 connection
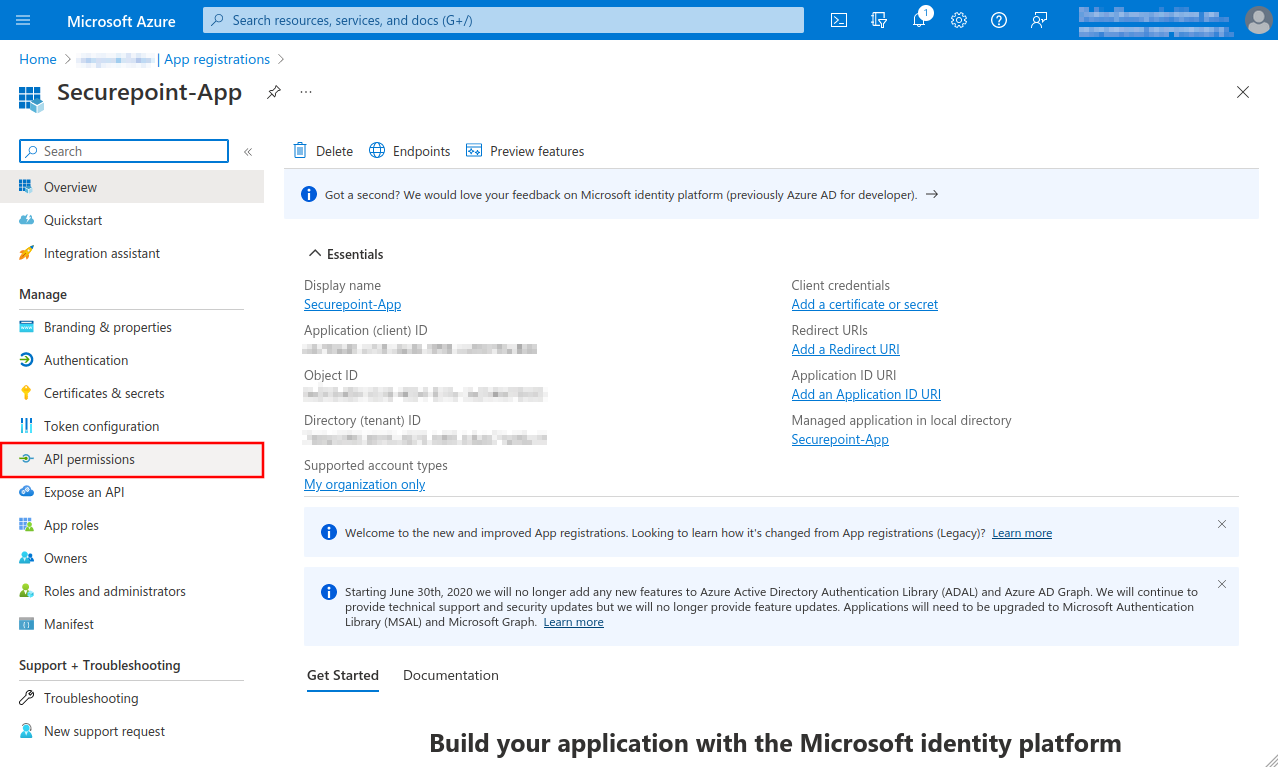
Fig.4
A summary of the newly registered app is displayed
- The Object ID displayed here does not belong to the app and is not needed!
- Select API permissions menu
Fig.7
- Click Application permissions button
- Search for imap
- Checkmark IMAP.AccessAsApp
- Click the Add permissions button
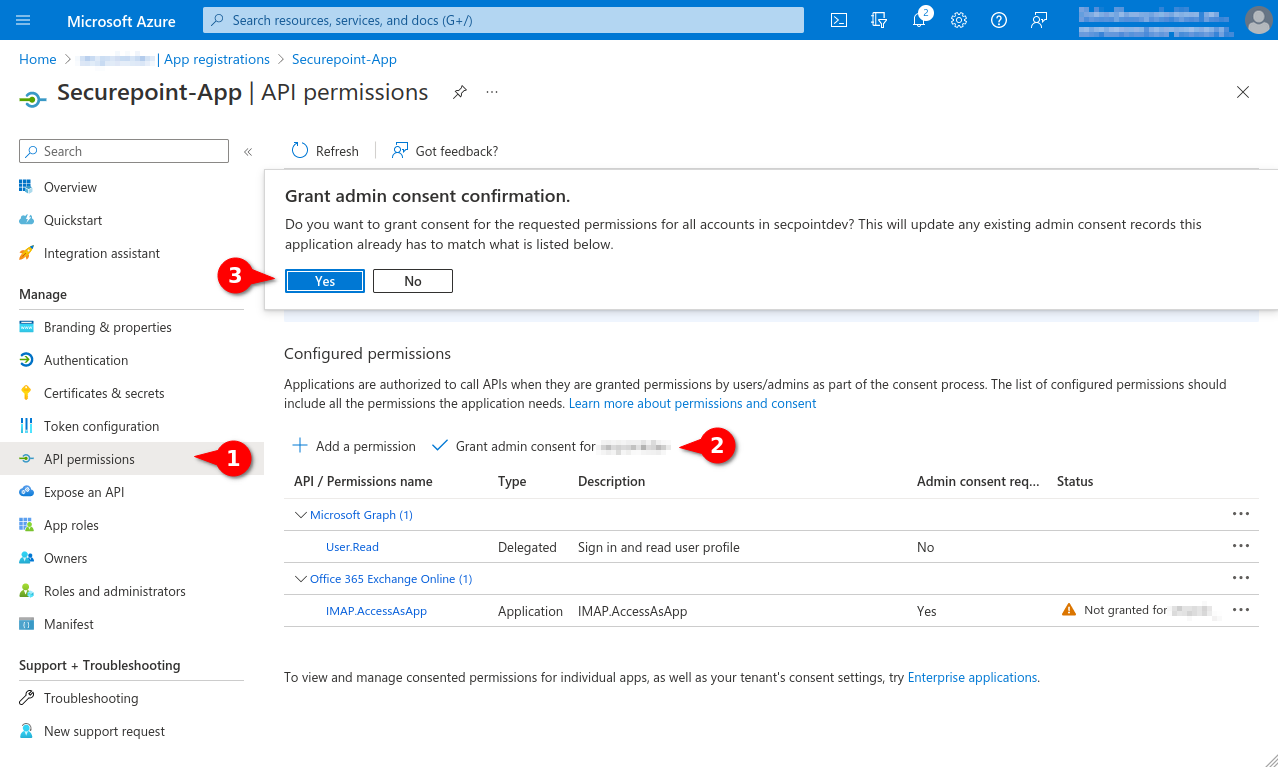
Fig.8
- Select menu API permissions again.
- Select entry Grant admin consent for [...]
- Click the Yes button
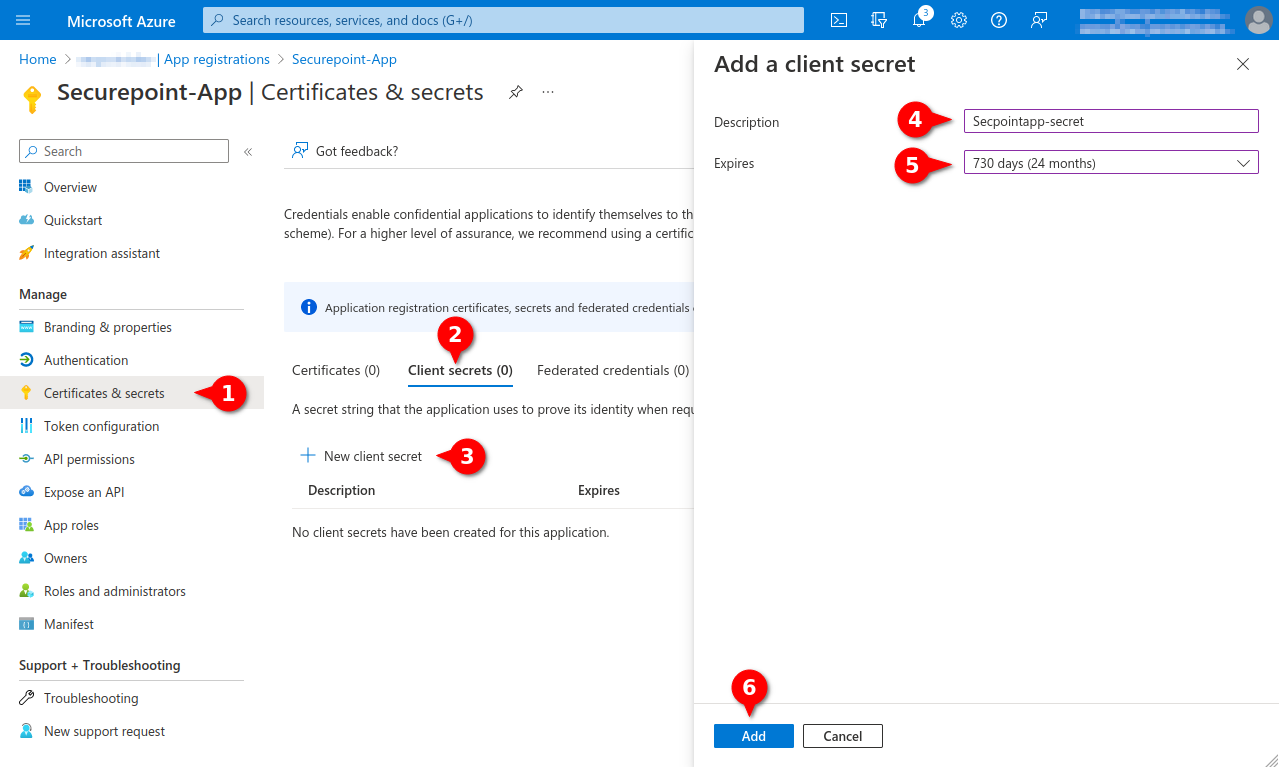
Fig.10
- Menu Certificates & secrets
- Tab Client secrets
- Entry New Client secret
- Enter unique description
- Select desired duration (max. 24 months)
- Click Add button
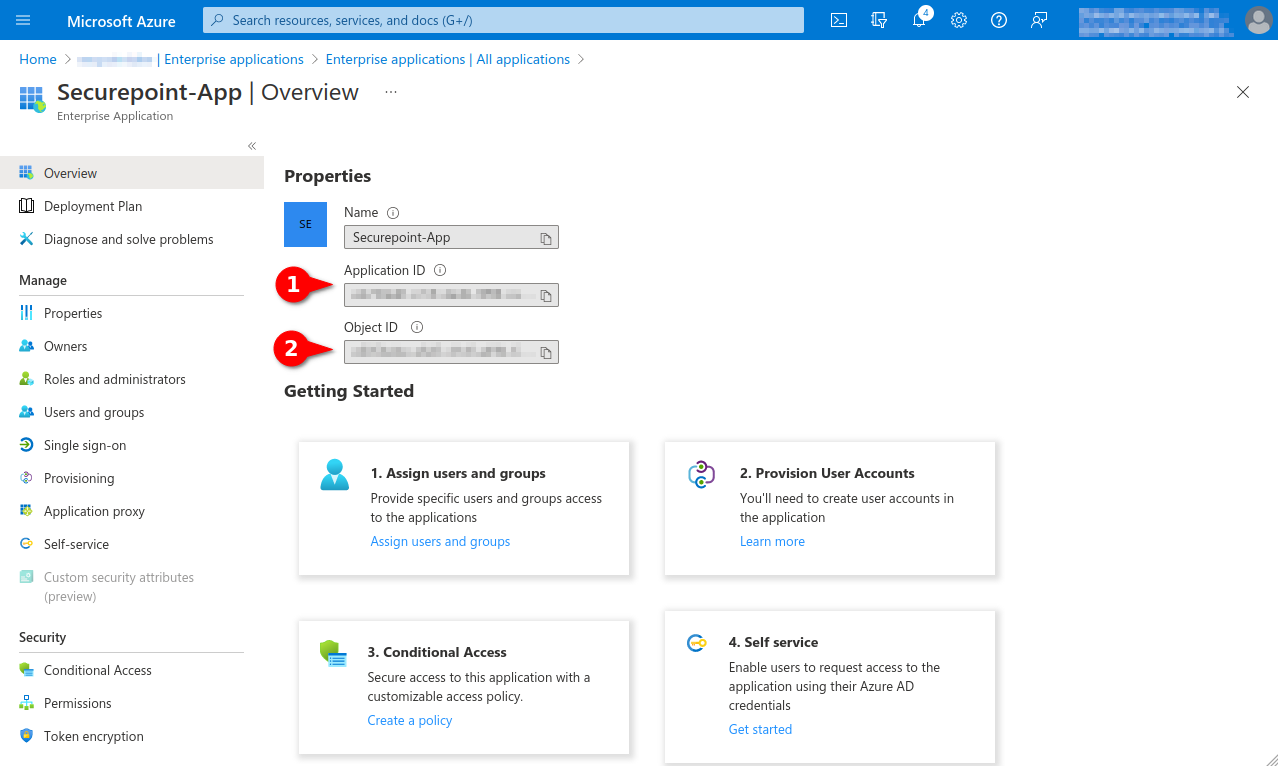
Fig.14
Note down from the app properties:
- Application ID, is entered as Application ID when adding an OAuth 2 connection
- Object ID, is required for the granting of the authorisation via Powershell
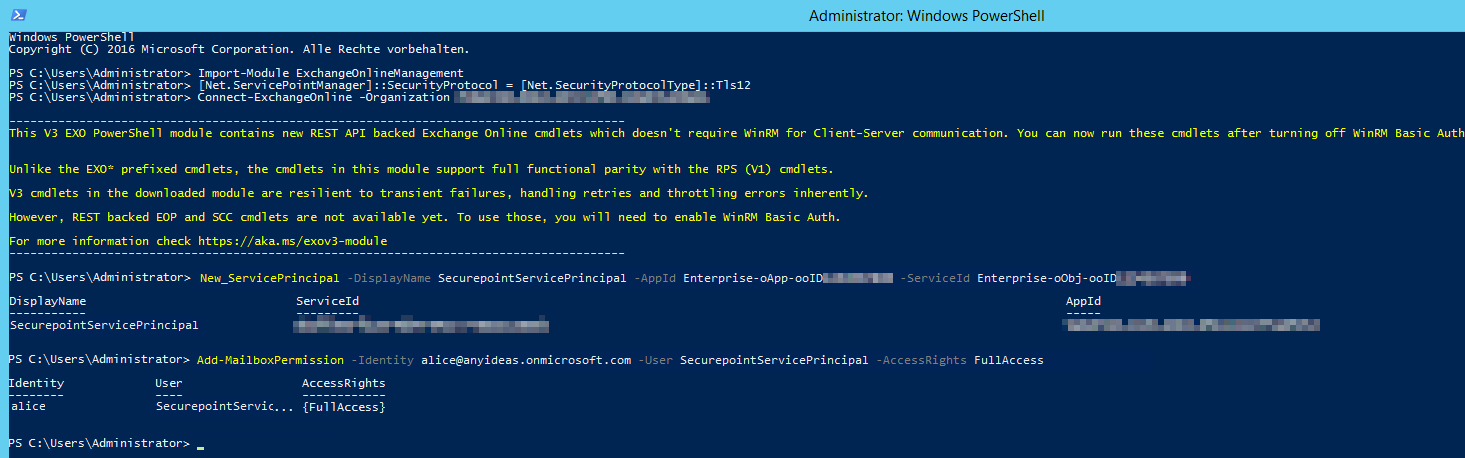
Fig.15
- Open Powershell on a Windows client administrator
- Install ExchangeOnlineManagement module If there are problems installing the module or connecting, you may need to configure Powershell to TLS 1.2:
>[Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12- > Install-Module -Name ExchangeOnlineManagement -allowprerelease
- Import ExchangeOnlineManagement and connect to Tenant:
- > Import-module ExchangeOnlineManagement
- > Connect-ExchangeOnline -Organization Tenant ID (See Fig.1)
- Create a new service principal and assign a unique name:
- > New-ServicePrincipal -DisplayName SecurepointServicePrincipal -AppId Enterprise-oApp-ooID-oooo-oooooooo -ServiceId Enterprise-oObj-ooID-oooo-oooooooo
- For Enterprise-oApp-ooID-oooo-oooooooo enter the Application ID and for Enterprise-oObj-ooID-oooo-oooooooo enter the Object ID (see Fig. 14)
- Then assign mailbox permissions:
- > Add-MailboxPermission -Identity alice@anyideas.onmicrosoft.com -User SecurepointServicePrincipal -AccessRights FullAccess