- New section: Resource utilisation
Scope of services
- Award-winning IKARUS t3 scan.engine for reliable detection
- Real-time updates for virus patterns
- Extensive virus scans
- Available languages: German and English
- Scheduled on-demand scan profiles
- Fast on-access scan
- Sending suspicious files to the Ikarus lab for further analysis
- Quarantine feature with various cleanup functions
- „Guard“ - Option für proaktiven Virenschutz
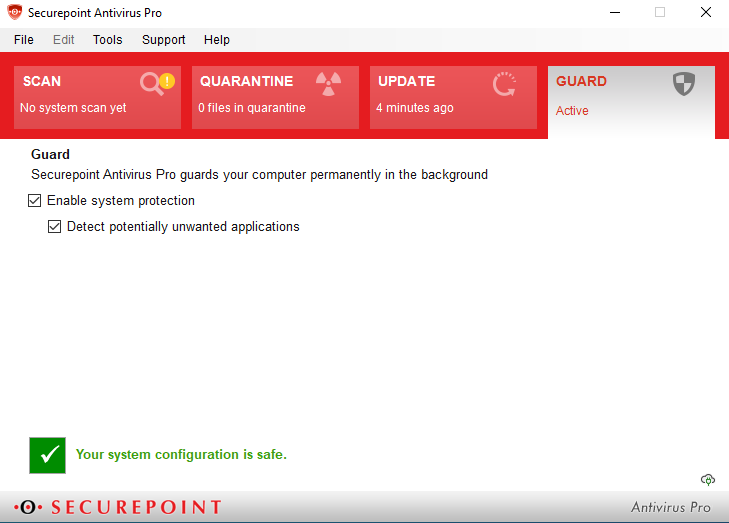
- Guard - option for proactive virus protection
- Resource-friendly operation
The virus scanner
Securepoint Antivirus Pro is a real-time scanner (on-access scan) that performs a complex malware analysis of all files in the background, ensuring that already known viruses and malware are detected directly.
Unknown malware that is not yet included in the virus databases is detected using advanced and complex analyses. Behavior-based heuristics and algorithms are used in a secured virtual environment (sandbox), in which the most common systems, devices, functions and programming and machine languages are displayed.
Archives are unpacked, decrypted and executed, files and functions are analyzed, changed memory areas and unpacked codes are observed and evaluated.
The behavior immediately after the download often also provides indications of malware. Targeted actions indicate a virus, immediately after the behavior detection it is checked whether it is in a simulated environment - and thus exposes itself.
The also integrated recognition based on static characteristics ensures that known malicious code is also recognized.
All findings on found malicious codes, viruses and pests are entered into the IKARUS virus database and can be detected and isolated in the first scan procedure in the future. The virus database is checked for updates by Securepoint Antivirus Pro every 20 minutes. The machine analyses are supplemented and expanded by the IKARUS analysis and research team.
In addition, new approaches to malware detection are constantly being researched. Depending on the location and purpose of security software, necessary and useful methods and features differ.
If the suspicious file is found, access to it is blocked and a quarantine entry is made by the client. The quarantine can be used to decide what to do with the found file (e.g. delete the file).
The on-demand scan is responsible for the defined and manual scans for individual files, folders or even drives. Four scan profiles are available by default, which can be started automatically at freely definable times.
Protection from potentially undesirable applications and programs (PUA and PUP) protects the device from adware and unwanted add-ins.
Resource utilisation
- On Access Scan utilises maximum resources, as time is critical: high priority process
- On Demand Scan: Started manually: Maximum resources: high priority process
- On Demand Scan: Planned start: Maximum resources: low priority process
- The faster the system's hard drive runs, the faster the system itself works. Replacing an HDD with an SSD generally results in a significant increase in performance.