Konfiguration of the Captive-Portals
Last adaptation to the version: 11.8.7
- New:
- Article updated
- English translation
- Added rule for HTTPS with SLL interception
Previous versions: -
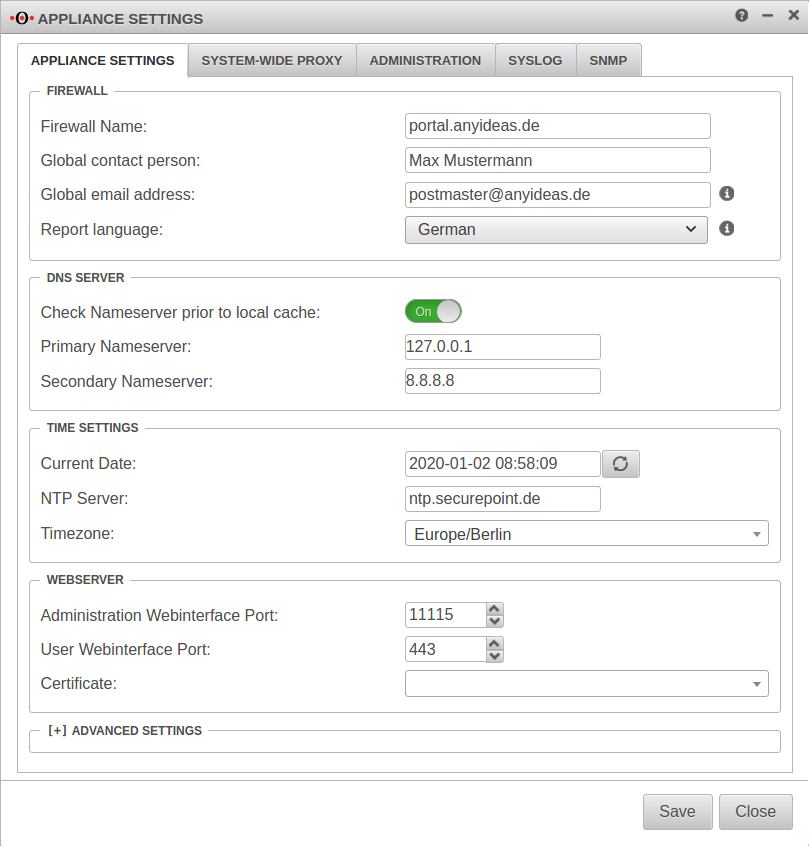
Server settings
Menü Reiter Server settings
Customize Firewall Name
The firewall name should be defined as FQDN. (In the example portal.anyideas.de)
This is necessary so that later the resolution of the landing page of the captive portal is compatible with the certificate.
Firewall
| ||
| Firewallname | portal.anyideas.de | FQDN compliant firewall name |
Entering the DNS serverThe localhost (here 127.0.0.1) is entered as the primary name server. In the past, 'google-public-dns-a.google.com' has proven itself as a secondary name server with its fast response time and high availability. DNS server | ||
| Primary name server | 127.0.0.1 | Localhost |
| Secondary name server | 8.8.8.8 | Possible name server: google-public-dns-a.google.com |
Importing certificates
Since the landing page of the captive portal is a HTTPS website, the next step is to provide the required certificate. We strongly recommend to buy a certificate from an official CA (or to use an existing wildcard certificate) to avoid later irritations because of browser warnings.
Basically there are two options:
- A Certificate for a FQDN
- in this case the common name of the certificate would be portal.anyideas.de
- A wildcard certificate
- in which case the common name of the certificate would be *.anyideas.de
In the first step, the CA provided together with the certificate must be imported into the UTM.
Menu Tab CA ButtonIn the first step, the CA provided together with the certificate must be imported into the UTM.
Menu Tab CA Button
The CA and the certificate must be in .pem format !
Certificates can be converted with the tool openssl - available for all common platforms (part of Linux, call via console) - and the following commands:
| Certificate | Command |
|---|---|
| X509 to PEM | openssl x509 -in certificatename.cer -outform PEM -out certificatename.pem |
| DER to PEM | openssl x509 -inform der -in certificate.cer -out certificate.pem |
| P7B to PEM | openssl pkcs7 -print_certs -in certificate.p7b -out certificate.pem |
| PFX to PEM | openssl pkcs12 -in certificate.pfx -out certificate.pem -nodes |