Set up Internet access of a UTM and import cloud backup
Last adaptation to the version: 12.5.1
New:
- PPPoE and VDSL are united
Prefaces
- Usually, the installation wizard appears during the initial setup of the UTM.
This checks whether a configuration already exists that is marked as the start configuration.
(Status )
If this is not the case, the wizard opens automatically.
- It is not advisable to start the installation wizard later, as other settings made in the meantime may be overwritten.
Installation wizard
Step 1 - General
| Caption | Value | Description | 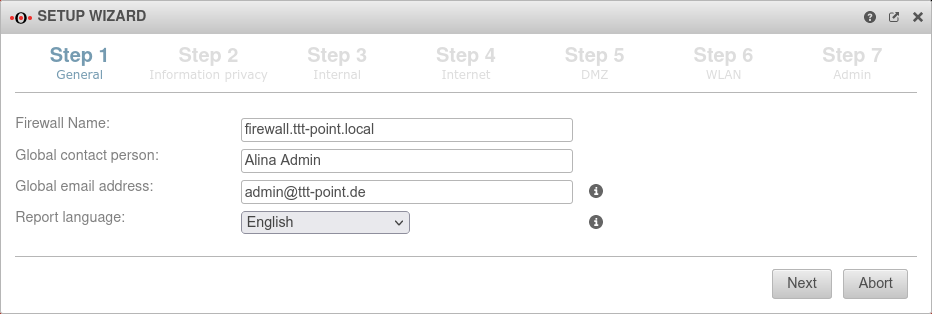 |
|---|---|---|---|
| Firewall Name: | firewall.ttt-point.local | Any value Any value can be entered here for a restore. As soon as a configuration from the cloud backup has been activated, those settings will be applied. | |
| Global contact person: | Alina Admin | Any value Any value can be entered here for a restore. As soon as a configuration from the cloud backup has been activated, those settings will be applied. | |
| Global email address: | admin@ttt-point.de | Any value Any value can be entered here for a restore. As soon as a configuration from the cloud backup has been activated, those settings will be applied. | |
| Language of reports: | Leave default setting For a restore the default setting can be left. As soon as a configuration from the cloud backup has been activated, those settings will be applied. | ||
Step 2 - Privacy | |||
| Anonymize all applications | Yes | Leave default setting For a restore the default setting can be left. As soon as a configuration from the cloud backup has been activated, those settings will be applied. |
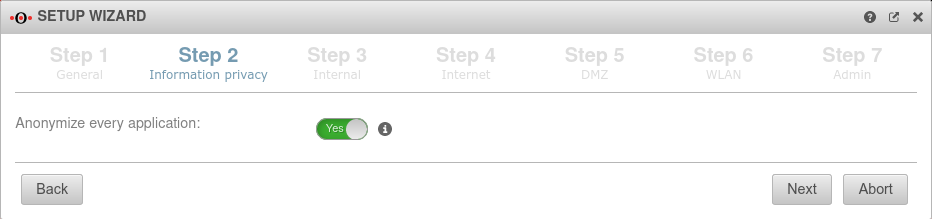 |
Step 3 - Internal | |||
| Internal firewall IP address: | 192.168.175.1/24 | This means that after setting up Internet access and the necessary reboot, the firewall is still accessible to the device from which the current configuration is being carried out in order to subsequently activate the cloud configuration. |
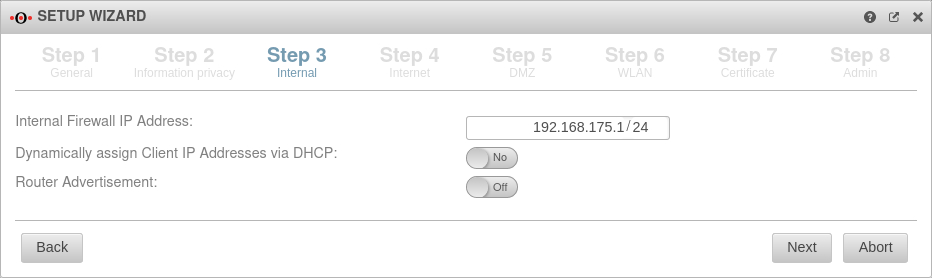 |
| Dynamically assign Client IP Addresses via DHCP: | No | Leave default setting For a restore the default setting can be left. As soon as a configuration from the cloud backup has been activated, those settings will be applied. | |
| Router Advertisement: | Off | If the UTM has received an IPv6 prefix, it can advertise the subnet via router advertisement in the network segment behind the interface. (See article IPv6 Prefix Delegation) | |
| Internal firewall IP address: | 192.168.175.1/24 | This means that after setting up Internet access and the necessary reboot, the firewall is still accessible to the device from which the current configuration is being carried out in order to subsequently activate the cloud configuration. |
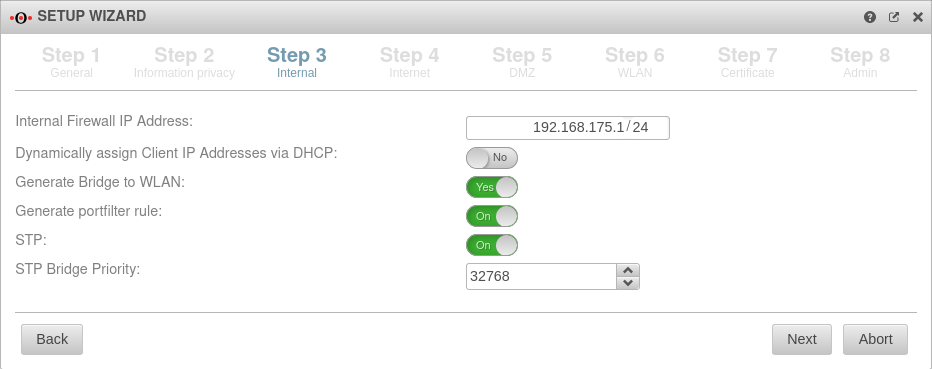 |
| Dynamically assign Client IP Addresses via DHCP: | No | Leave default setting For a restore the default setting can be left. As soon as a configuration from the cloud backup has been activated, those settings will be applied. | |
| Generate WLAN Bridge: | No Default |
Any value Any value can be entered here for a restore. As soon as a configuration from the cloud backup has been activated, those settings will be applied. | |
| Generate portfilter rule: Shown when Generate WLAN Bridge is enabled |
No | When activated, a port filter rule is automatically generated | |
| STP: Shown when Generate WLAN Bridge is enabled |
Off | When activated, STP (Spanning Tree Protocol) is used | |
| STP Bridge Priority: Shown when Generate WLAN Bridge is enabled |
32768 Default |
The priority of the STP Bridge is set | |
Step 4 - InternetThis is where the Internet connection is configured on the external interface (A0). | |||
Connection type PPPoE / VDSL Connection type:
| |||
| With this type, an ADSL or SDSL modem is connected to the external interface (A0). The connection is initiated by the UTM. | |||
| Username: | (Shares ISP) | The login information is provided by the ISP (Internet Service Provider) | 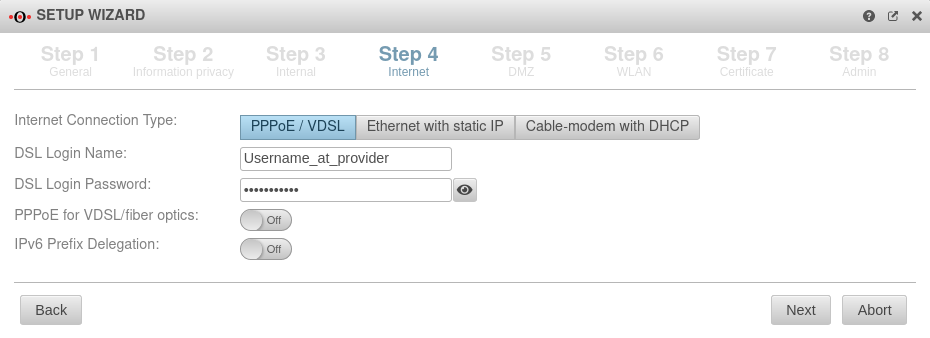 |
| Password: | (Shares ISP) | ||
| PPPoE for VDSL/fiber optics: | Off | Check the box if PPPoE is connected via a VDSL modem or via fibre. | |
| IPv6 Prefix Delegation: | Off | Allows an IPv6 network assigned by the Internet Service Provider to be split into /64 networks and assigned to individual interfaces via Router Advertisement. Example: Network assigned by ISP: 2001:0db8:aaaa:bb::/56 Networks distributed at internal interfaces via router adviertisement: 2001:0db8:aaaa:bb00::/64 2001:0db8:aaaa:bb01::/64 | |
Connection type Ethernet with static IP Connection type:
| |||
| With this connection type, a router is connected to the external interface (A0), which itself initiates the connection to the Internet. The login information of the provider is stored in the preceding router and not on the UTM. | |||
| External IP address: | 192.168.178.101/24 | The IP address of the external interface (A0) and the IP address range for the external network (subnet mask in CIDR notation). The default is an already existing IP address, if applicable. The external interface receives an IP address via DHCP by default, provided a DHCP server is available in the external network. |
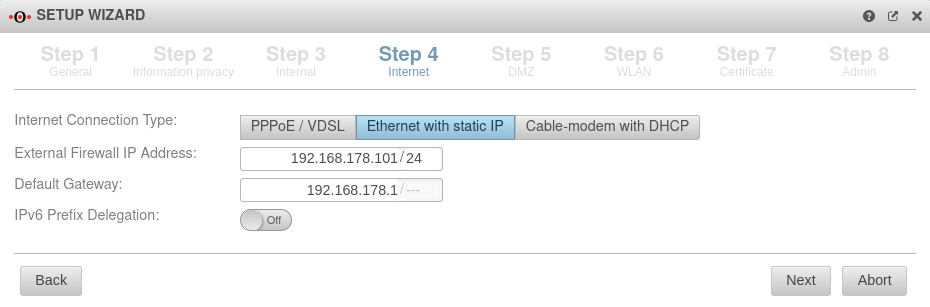 |
| Default Gateway: | IP address of the default gateway for the UTM so that it knows which is the closest router for all networks that are not on an internal interface: As a rule: the Internet. | ||
| IPv6 Prefix Delegation: | Off | Allows an IPv6 network assigned by the Internet Service Provider to be split into /64 networks and assigned to individual interfaces via Router Advertisement. Example: Network assigned by ISP: 2001:0db8:aaaa:bb::/56 Networks distributed at internal interfaces via router adviertisement: 2001:0db8:aaaa:bb00::/64 2001:0db8:aaaa:bb01::/64 | |
Connection type Cable modem with DHCP Connection type:
Originally mostly devices that cable providers provided to their customers. | |||
| Also with this connection type, a router is connected to the external interface (A0), which itself initiates the connection to the Internet. The login information of the provider is stored in the preceding router and not on the UTM. |
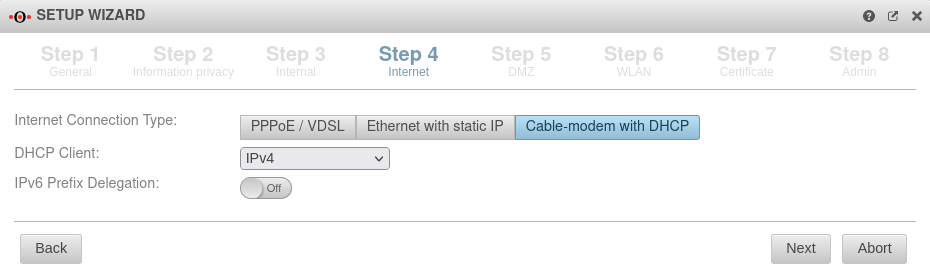 | ||
| DHCP Client: | Selection with which protocol the interface receives IP addresses from the preceding router with DHCP server. | ||
| Off | Allows an IPv6 network assigned by the Internet Service Provider to be split into /64 networks and assigned to individual interfaces via Router Advertisement. Example: Network assigned by ISP: 2001:0db8:aaaa:bb::/56 Networks distributed at internal interfaces via router adviertisement: 2001:0db8:aaaa:bb00::/64 2001:0db8:aaaa:bb01::/64 | ||
Connection type LTE / others Connection type:
| |||
Step 5 - DMZConfiguration of a second internal network, often referred as Demilitarized Zone: Usually a network that is separate from the internal network. | |||
| DMZ IP address: | 192.168.176.1/24 | Any value Any value can be entered here for a restore. As soon as a configuration from the cloud backup has been activated, those settings will be applied. |
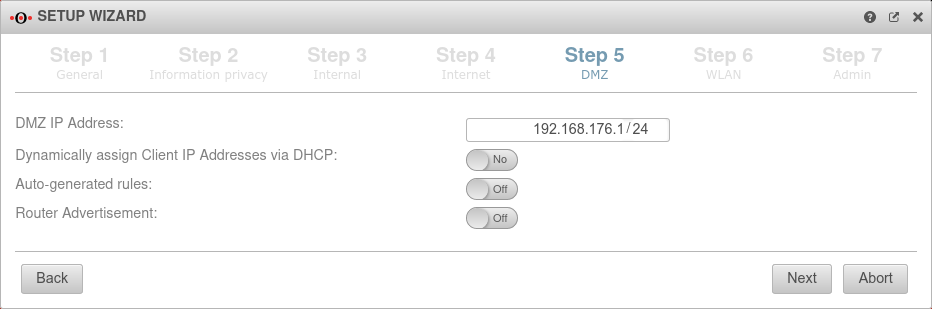 |
| Assign the IP addresses to the clients in this network via DHCP: | No | Leave default setting For a restore the default setting can be left. As soon as a configuration from the cloud backup has been activated, those settings will be applied. | |
| Autogenerated rules: | No | Leave default setting For a restore the default setting can be left. As soon as a configuration from the cloud backup has been activated, those settings will be applied. | |
| Generate WLAN Bridge: Only if a WLAN module is present |
No | Any value Any value can be entered here for a restore. As soon as a configuration from the cloud backup has been activated, those settings will be applied. | |
| Router Advertisement: | No | If the UTM has received an IPv6 prefix, it can advertise the subnet via router advertisement in the network segment behind the interface. (See article IPv6 Prefix Delegation) | |
Step 6 - WLANThe RC1000R (G5) model has no WLAN option. | |||
| WLAN IP address: Not in bridge mode |
192.168.177.1/24 | The IP address of the WLAN interface (wlan0) and the subnet mask (as CIDR notation) for the WLAN network. In bridge mode, the setting from the internal network in which bridge mode was activated is used here. |
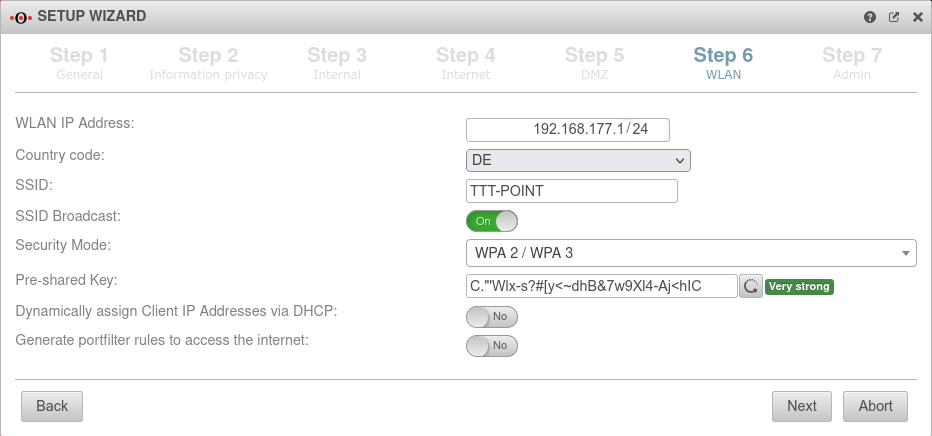 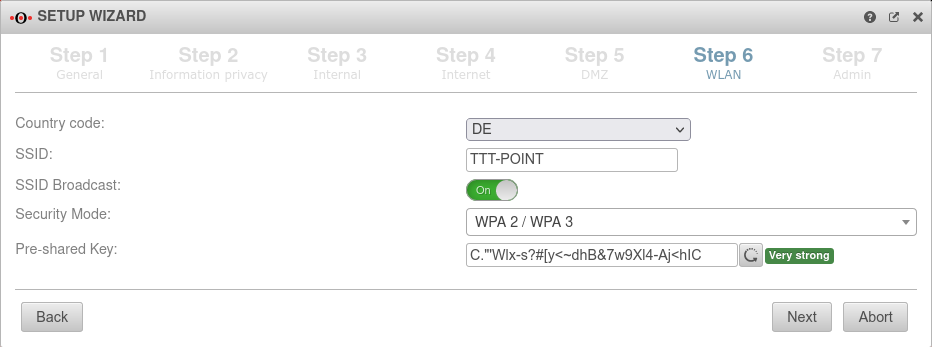 |
| Country code: | The country code is used to determine which frequencies and which signal strengths may be used. The frequencies used and the transmission power can be found in a Wikipedia article. | ||
| SSID: | TTT-POINT | The Service Set Identifier (SSID) is the name under which the WLAN network is presented to the clients. This must be entered in any case. | |
| SSID Broadcast: | On | This option can be used to define whether the WLAN network can be seen by every client or whether the transmission of the SSID should be suppressed. (Off) | |
| Security Mode | Is considered unsafe and only exists for backwards compatibility. (TKIP is used as encryption method) | ||
| Standard with enhanced security AES128 is used as encryption method: https://en.wikipedia.org/wiki/WPA2 | |||
| Standard with highest available level of security AES256 and SAE are used as encryption methodes: https://en.wikipedia.org/wiki/WPA3 | |||
| Assign the IP addresses to the clients in this network via DHCP: Not in bridge mode |
Off | When enabled Yes, the UTM works as a DHCP server: All clients in the WLAN network receive an IP address via DHCP. This sets the UTM as the default gateway and DNS server for the clients. In bridge mode, the setting from the internal network in which bridge mode was activated is used here. | |
| Pre-Shared Key: | Don'tcopythis:Ei)#W~X$… | The base station and mobile device must have the same PSK (≙password). The security of the encryption depends directly on the length and complexity of the PSK! | |
| Automatically generates a very strong PSK | |||
| Generate rules for Internet access: Not in bridge mode |
Off | Port filtering rules can be automatically created for this network, allowing traffic to the Internet on the interface to the external interface (A0). Likewise, rules are created that also allow data traffic from the internal network into the WLAN network. notempty These any rules are intended for testing purposes and should be disabled and replaced with well-defined rules in production mode. In bridge mode, the setting from the internal network in which bridge mode was activated is used here. | |
Step 7 - Certificate | |||
| Generate CA and server certificate: | Yes Default |
If Yes is enabled, a CA and server certificate will be generated. |
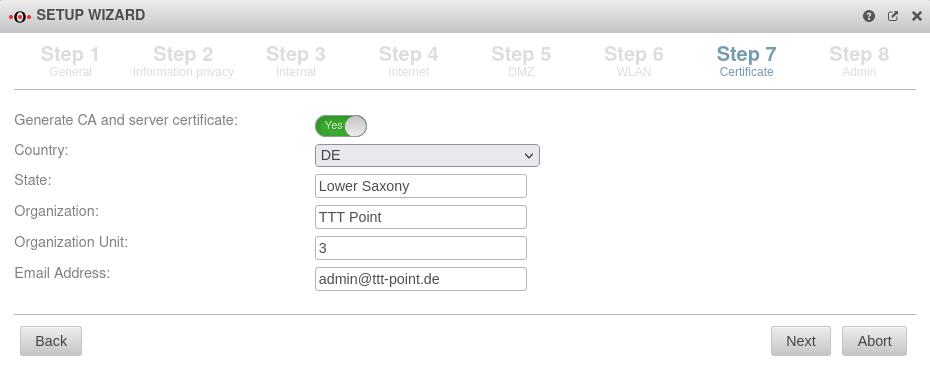 |
| Country: | Detailed information is used to identify who issued the certificate | ||
| State: | Lower Saxony | ||
| Organization: | TTT Point | ||
| Department: | Support | ||
| Email address: | admin@ttt-point.de | ||
Step 8 - Administrator | |||
| User | admin | The username admin cannot be changed at this point | 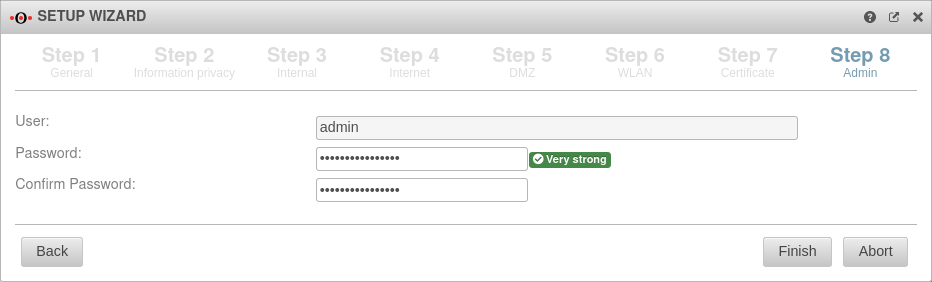 |
| Password: | ••••••• |
Passwords must meet the following criteria:
| |
| Confirm password: | ••••••• | ||
| |||
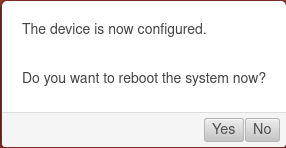
Reboot
| |||
| Do you want to reboot the system now? | In order for the configuration changes to be applied, the respective services must be restarted in the correct order. This is achieved by a reboot of the device. |
 | |
Import Cloud Backup
Import cloud backup under
As soon as the UTM has access to the Internet, those cloud backups that were created with this licence are displayed here.
As soon as the UTM has access to the Internet, those cloud backups that were created with this licence are displayed here.
The UTM now boots with the cloud backup settings