notempty
- Erklärung des Verhaltens bei einer Aktion E-Mail im Betreff markieren mit
- Criteria for links whose text and destination differ v12.6
- New function: Tags
- New actions related to tag
- List of possible Mail-Header for X-Securepoint
- TNEF decoding by default On
- New URL Filter Category Unknown v12.5.0
Introduction
In order to determine whether an incoming email is spam, the POP3 proxy, mail relay and mail connector can pass incoming emails to the Mailfilter. The Mailfilter consists of the:
- Cyren scan daemon,
- the ClamAntivirus ,Only for systems that meet the requirements
- the Securepoint content filter and
- a URL filter.
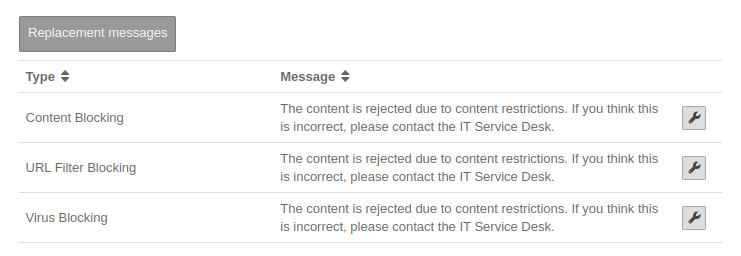
If a web link is found within the email which matches the URL filter or which is recognized by the content filter, a freely editable replacement message appears instead of the content section of the email.
By using the Mail Connector, it is possible to check not only POP3 but also emails fetched with IMAP as well as the two encrypted variants through the Mailfilter.
The UTM mail archive stores mails that have been quarantined using the filter rule.
Emails forwarded and delivered by the UTM (HAM) are no longer found in the mail archive unless this option is explicitly activated.
Requirement
Filter rules
Overview | |||||||||||||
| The filter rules are used to decide how to proceed with emails for which defined properties have been detected. A distinction is made between the SMTP and POP3 protocols as well as the mail connector. Via the Mail Connector, the UTM is able to read emails from a mail server using the POP3 and IMAP protocols and their encrypted variants POP3S and IMAPS. It also inspects them for spam and malware by using the Mailfilter. Furthermore, a distinction is made between the protocols POP3 and SMTP. If the mail relay is used, the protocol is SMTP. If the POP3 proxy is used, the POP3 protocol is selected. |
UTMuser@firewall.name.fqdnApplications 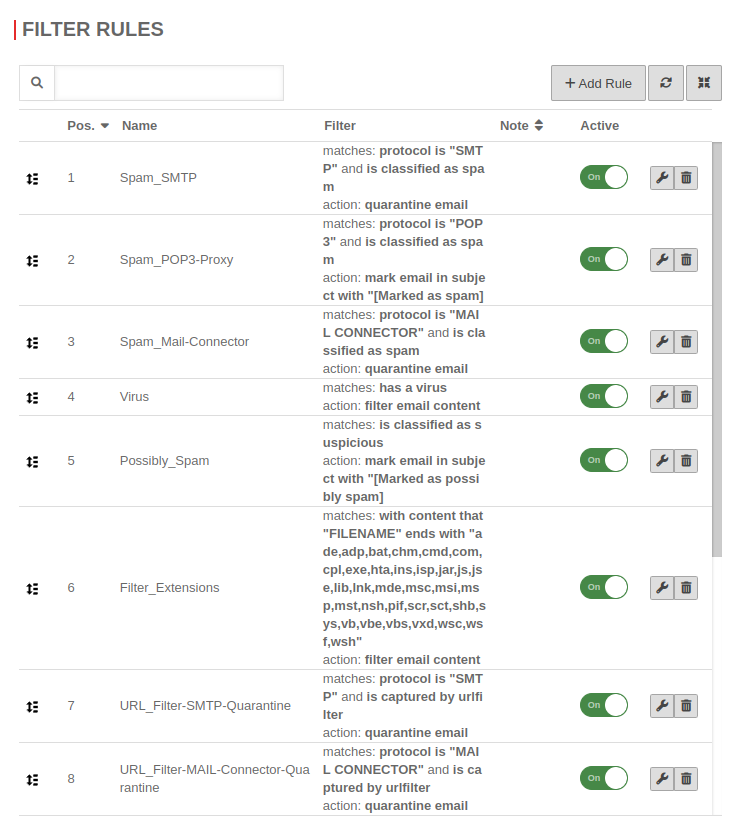 Mailfilter Mailfilter
| ||||||||||||
Add filter rule | |||||||||||||
| With a new filter rule is created. A unique Rule name must be assigned. The Conditions with Vorlage:MenuD and-Operator determines,
|
UTMuser@firewall.name.fqdnMailfilterApplications 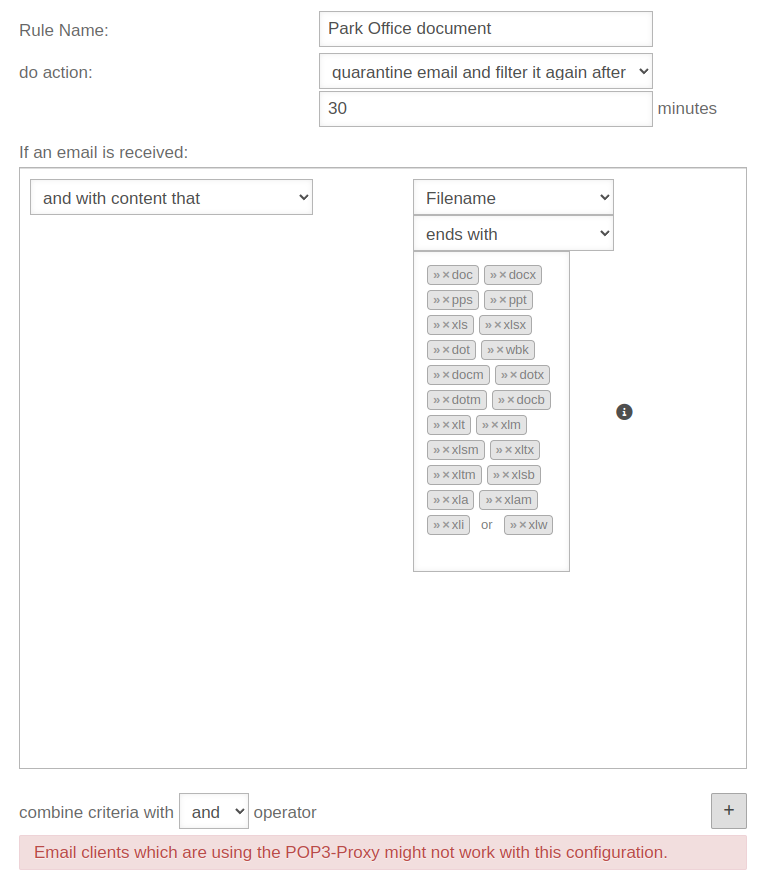 Creation of a filter rule using an example Creation of a filter rule using an example
| ||||||||||||
Criteria | |||||||||||||
| Filtering according to the following is possible: If an email is received... | |||||||||||||
| Condition | Operator | Value | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| | |||||||||||||
See Wiki article about Regex. |
» ✕any values | ||||||||||||
| see source host | |||||||||||||
| see source host | |||||||||||||
| see source host | |||||||||||||
| additionally: Specification of the header field |
see source host The header field »from« indicates a sending mail server (Received: from) - not the »Sender« field. | ||||||||||||
| The spam filtering engine expects that the category of this email may change in the next 15 minutes. | |||||||||||||
| notempty New as of v12.6.0 |
Used to detect fake URLs. Normal text that is not structured like a URL is not taken into account. | ||||||||||||
oder |
see source host | ||||||||||||
| Enter the domain |
» ✕fail » ✕pass » ✕temperror | ||||||||||||
Prerequisite for the use is in the menu Area General activation of the option SPF/DKIM/DMARC checks: On
| |||||||||||||
Enter the domain |
» ✕fail » ✕neutral » ✕pass » ✕permerror » ✕softfail » ✕temperror | ||||||||||||
Prerequisite for the use is in the menu Area General activation of the option SPF/DKIM/DMARC checks: On
| |||||||||||||
Prerequisite for the use is in the menu Area General activation of the option SPF/DKIM/DMARC checks: On | |||||||||||||
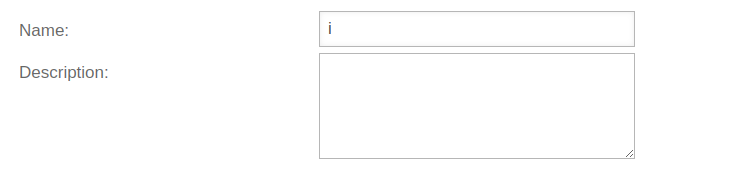
| notempty New as of: 12.6.0 |
An existing tag is selected. A new tag can be added using the button. | ||||||||||||
| notempty New as of: 12.6.0 |
An existing tag is selected. A new tag can be added using the button. | ||||||||||||
| The button can by used to apply additional critaria for this filter. | |||||||||||||
Aktionen | |||||||||||||
The following options are available for Do action:
Further filter rules can be applied to these emails. | |||||||||||||
| Action | Description | ||||||||||||
| Accepts the email. The test for the rule set is completed. | |||||||||||||
| The sender receives a notification that their email has been rejected. notempty When using the Mail-Connector, this function is strongly discouraged.
Neither the sender nor the recipient will be notified that the email has been rejected! | |||||||||||||
| Additional input of quarantine duration in minutes. Example: 30 minutes | |||||||||||||
| (and hold a predefined time (see Settings) for viewing) | |||||||||||||
| The email is disposed off without the sender being notified. | |||||||||||||
| A Replacement Message is displayed for the relevant section (plain text, html text, attachment, etc.). | |||||||||||||
| Text, which is added to the subject header to mark an email so that it can, for example, be relocated from the mail server to a corresponding folder. | |||||||||||||
Verhalten bei Aktion E-Mail im Betreff markieren mit
| |||||||||||||
Das Verhalten einer Mailfilterregel mit der Aktion ist abhängig davon, ob die E-Mail sich in Quarantäne befindet, oder nicht.
| |||||||||||||
Whitelist exception rule | |||||||||||||
| In a whitelist rule, the acceptance of a mail is defined under certain conditions. In order for a rule to work as a whitelist rule, the order must be defined so that this rule takes precedence over the general spam quarantine rule. By clicking and holding the left mouse button on the whitelist rule (pos. 7) in the "Pos." column, this rule is moved upwards above the general Spam_SMTP filter rule. Once the rule has reached the desired position, the mouse button is released and the whitelist rule is assigned a new position number according to its ranking. | UTMuser@firewall.name.fqdnApplications 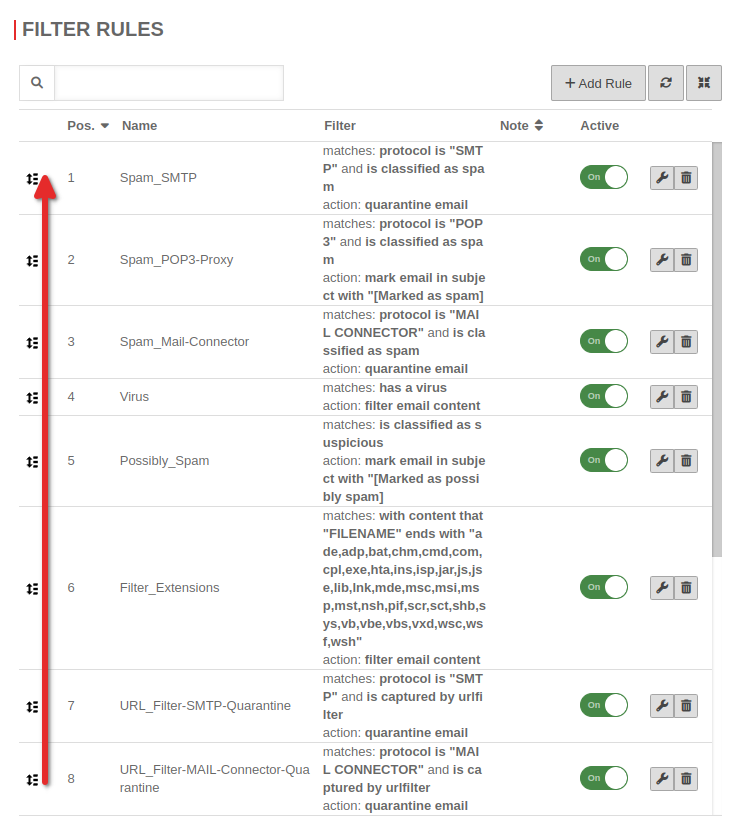 Move filter rule Move filter rule
| ||||||||||||
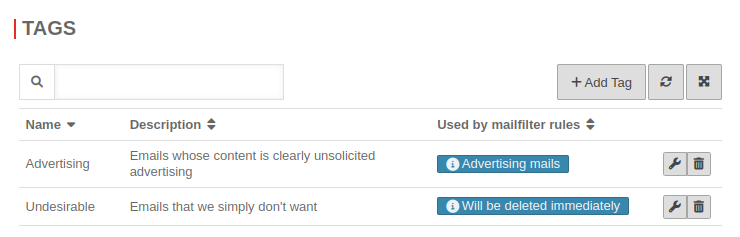
Tags
notempty
URL-Filter
| Text for emails that have been filtered because of the URLs they contain. | UTMuser@firewall.name.fqdnApplications 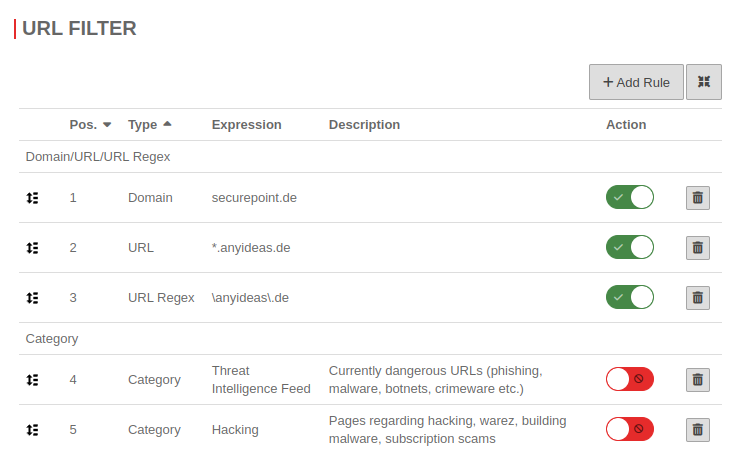 URL filter with some filters URL filter with some filters
| ||
Add Rule | |||
| Type | anyideas.com | Domain in plain text notation. All subdomains and subpages are filtered. | UTMuser@firewall.name.fqdnApplications 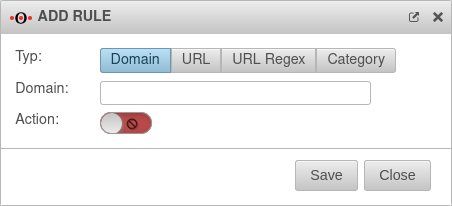 Filter rules Filter rules
|
| Type | *.anyideas.com/pages/* | Only the exact URL is filtered (wildcard * is possible). | |
| Type | .*\.anyideas\.com | URL in regex format, which allows numerous placeholders Syntax of regular expressions - Regex | |
| Type | Unknown |
This allows you to block access to all websites that have not yet been classified by Securepoint.
| |
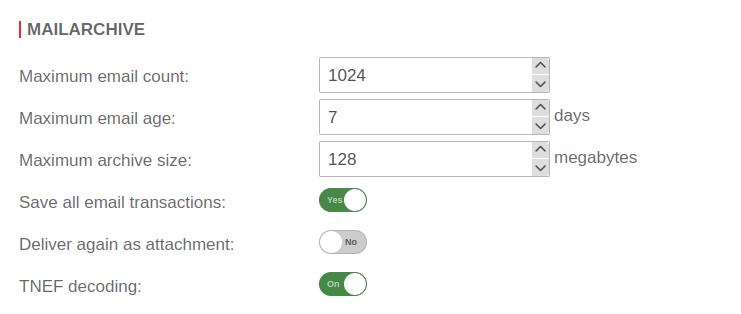
Settings
In this section, you can create a spam report, modify the blocking messages, and define the criteria according to which the emails are stored in the UTM mail archive.
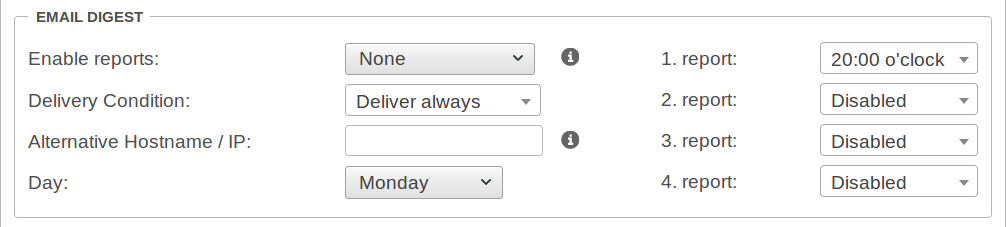
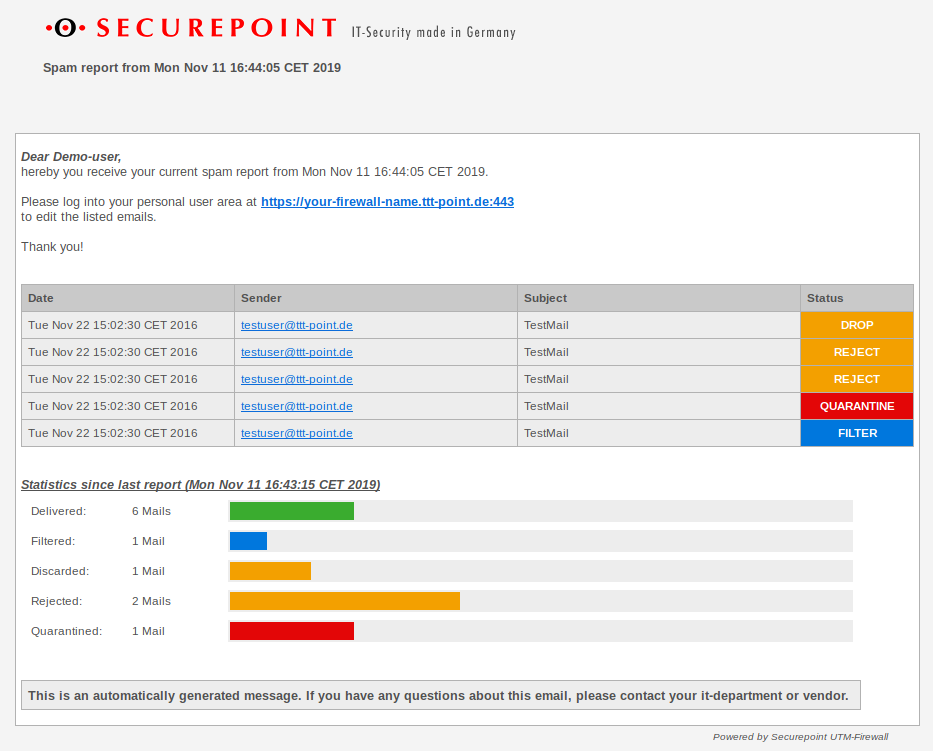
Spam report
The spam report can inform email users at certain intervals about emails filtered, blocked or quarantined by the UTM. This report can be sent either on a specific day of the week or daily, at a specific time.
| Action | Value | Description |
|---|---|---|
| Enable reports: | (Default) | No spam reports will be sent. |
| Reports are sent to the users. | ||
| Reports are sent to the users and an overview is sent to the administrator. | ||
| Delivery Condition: | Deliver always (Default) | In any case, a spam report will be sent. |
| Not accepted | Quarantined or filtered | |
| Quarantined or filtered | A spam report will only be delivered if at least one email has been quarantined or filtered. | |
| Alternative Hostname / IP: | If the web interface with the mail server is to be accessed via an external IP or another host name. | |
| Day: | (Default) | This report can be sent either on a specific or . |
| 1. Report | 20:00 o'clock | Specifies the time for sending the report. |
| 2.Report 3.Report 4.Report |
Disabled | With every day reports, a total of four reports can be sent at specified times. |
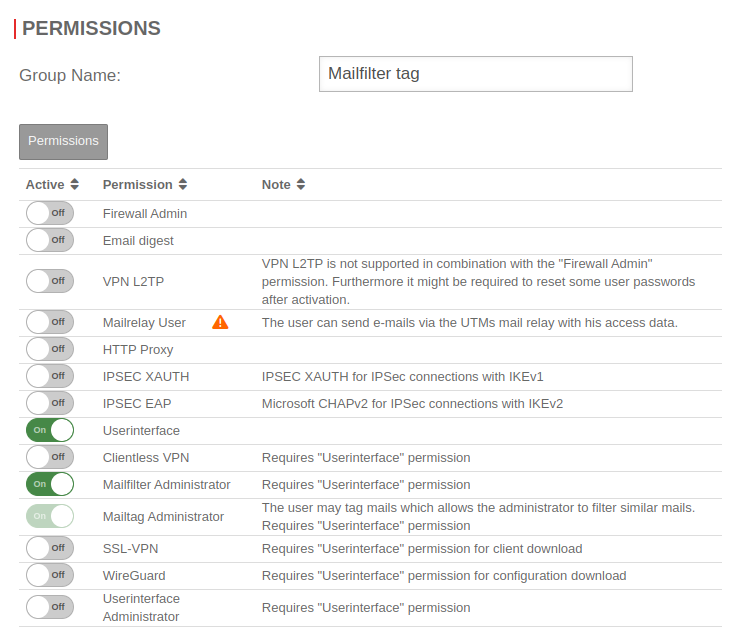
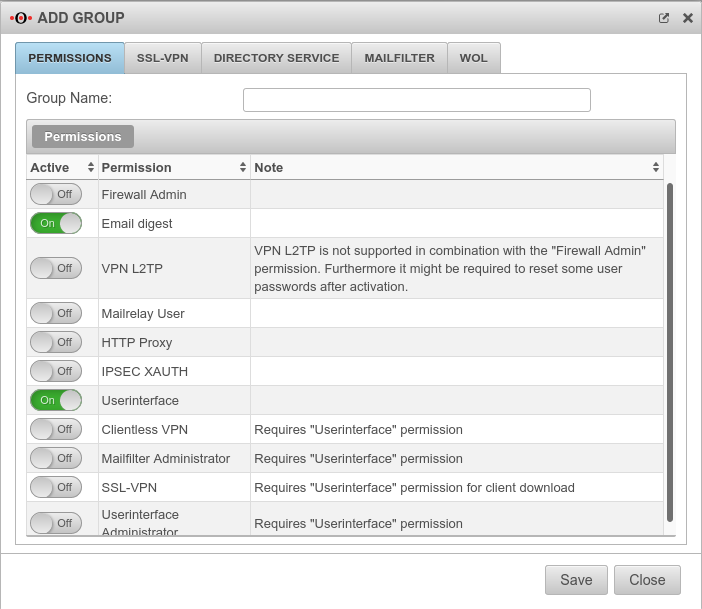
In order for the report to reach the e-mail user, it is necessary for the e-mail user to be in a group with the 'Spamreport permission.
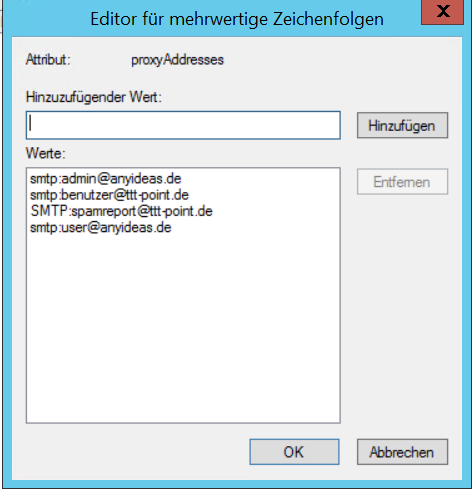
If several mail addresses for a user are stored in an AD, the entry configured there as Primary SMTP address is used as the default address.
The setting for this is made in the menu
Groups or Edit under Permissions:
The following sections must be activated here:
- Email digest
- On activates the creation of the spam report
- Userinterface
- On The email address can be taken from a directory server such as ActiveDirectory or LDAP if the UTM is connected to it. Otherwise, the user must be created with his email address on the UTM.
The email address can be taken from a directory server such as ActiveDirectory or LDAP if the UTM is connected to it. Otherwise, the user must be created with his email address on the UTM.
In the Mailfilter tab, further settings must be made, including the e-mail address to which reports are sent:
| Email address | ||
| Caption | Default | Description |
|---|---|---|
| support@ttt-point.de | Email accounts that can be viewed by members of this group to control the mail filter. Delete with | |
| Email address | Adding a mail address to the list | |
| Allow downloads of following attachments: | (Default) | Members of this group can download attachments from mails in the user interface that meet certain criteria. |
| Allow forwarding of following emails: | (Default) | Members of this group can forward emails in the user interface that meet certain criteria |
| Report email address: | Email address to which a spam report is sent. If no entry is made here, the spam report is sent to the first email address in the list. If several mail addresses for a user are stored in an AD, the entry configured there as Primary SMTP address is used as the default address..
| |
| Report language: | Default under → Firewall → language of reportsIt can be specifically selected: or |
Spam report to the user.
Replacement messages
Mail archive
Conclusion
Finish the configuration with Save.
Mail-Header
The following values can be set under the X-Securepoint header field by the mail filter:
- X-Securepoint: Virusscan Failure
- X-Securepoint: Spamcheck Failure
- X-Securepoint: Virus found (virus_name)
- X-Securepoint: Content Changed
- X-Securepoint: Spam
- X-Securepoint: Probably Spam
- X-Securepoint: UrlFilterSpam
- X-Securepoint: Bulk