notempty
- Indication of rejection of too large mails in mail filter view in the user interface
- Präferiertes Protokoll
- Note on the use of Authentication with TLS/SSL encryption
- Adding headers for greylisting can be disabled
- Übersetzung
Configuration of the Mailrelay
Preconditions
Settings on the provider side
In order to ensure a smooth participation in the mail traffic, some conditions must be fulfilled:
- A fixed IP address.
- An A record on the DNS server of the provider that resolves to this IP (e.g. mail.ttt-point.de).
- An MX record that determines the address at which the mail server of a domain can be reached (e.g. mail.ttt-point.de).
- A PTR record that resolves the fixed IP back to the MX record (reverse DNS).
These are all settings that have to be made by the provider and NOT on the Securepoint Appliance!
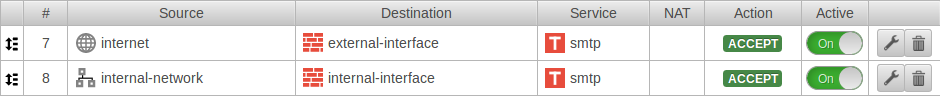
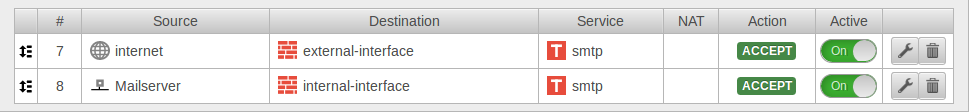
Set of rules
To enable other mail servers to deliver mails to the mail relay, access to the external interface with the SMTP protocol must be allowed in the port filter:
Email address
Under Global email address: a postmaster address should be configured. Otherwise undeliverable mails will remain on the disk space. This can cause the available memory to become insufficient at some point and mails to no longer be accepted.
Basic configuration of the mailrelay for receiving mails
The configuration of the mailrelay takes place under .
General
| Function | Value | Description | 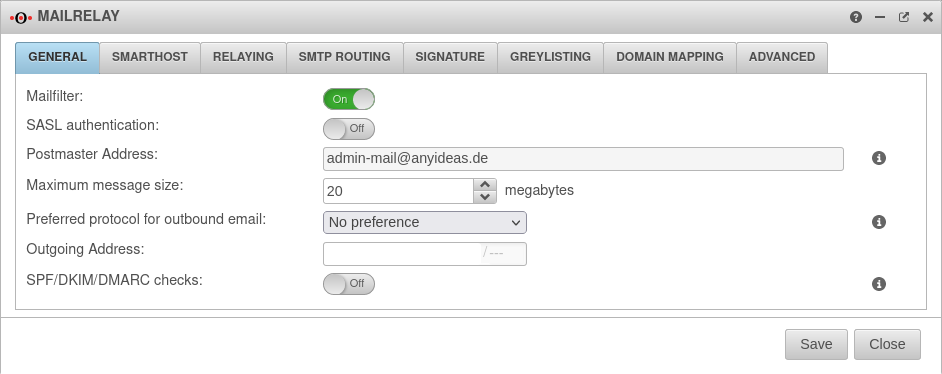 |
|---|---|---|---|
| Activate mail filter: | On | Activate | |
| SASL authentication: | Off | Enables SASL authentication, if activated | |
| Postmaster Address: | admin-mail@anyideas.de | A correct email address must be stored here. This email address is specified in the dialog in the Global email address field. Changes are only possible there. | |
| Maximum message size: | 20 Megabytes | Maximum size of the mails in megabytes accepted by the mail relay.
New as of v.12.2.3 A message appears in the mail filter view in the user interface about the rejection.
| |
| Preferred protocol for outbound email: New as of v.12.2.3 |
Specifies whether the mail relay should preferentially establish outgoing connections with a certain protocol. This setting should only changed from its default in special cases (e.g., IPv4 behind NAT) and if problems to deliver mail arise. | ||
| IPv4 is preferred as protocol (e.g. IPv4 behind NAT) | |||
| IPv6 is preferred as protocol | |||
| Outgoing Address: | With multipath routing, an outgoing interface can be specified here by the IP address. Communication from the internal network then also runs via this IP address. Further settings must be made on the mail server and its firewall in order to accept mails from this IP address.
| ||
| SPF/DKIM/DMARC checks: in 11.8.7 |
Off | Enables filtering for corresponding DKIM/DMARC/SPF-results in Mailfilter rules when enabled On. Adds RFC 8601 Authentication-Results Header to email. Not performed for mails sent by SASL-authenticated users or mails coming from "trusted hosts", i.e. hosts that have an entry in the relaying list with action RELAY and option "Connect" or no option. Further information in the article about Mailfilter
|
Smarthost
Settings for a Smarthost are only required if such a setting is required for outgoing mails. This is the case, for example, if no own mail server is operated or no fixed public IP address is available.
| Caption | Value | Description | |
|---|---|---|---|
| Enable Smarthost: | On | activates the Smarthost function. | 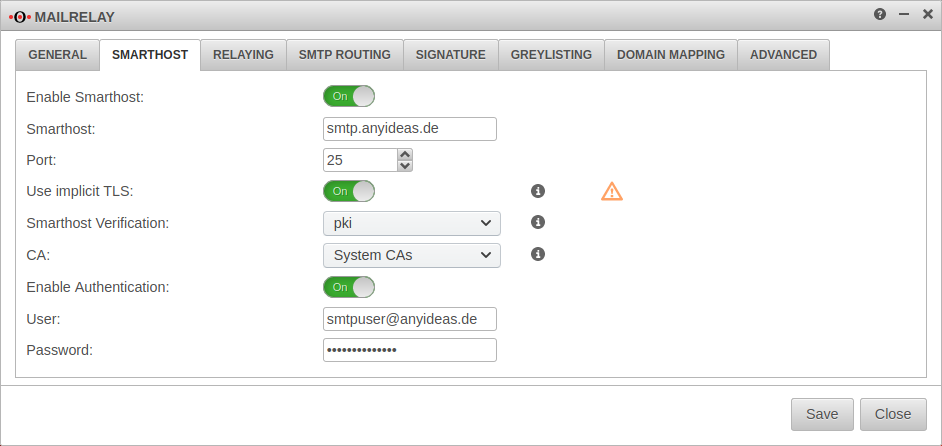 |
| Smarthost: | Mail server that is to receive and send outgoing mails.(sample address) | ||
| Port: | 465 | Mail port for external mail server 25: Default port for smtp (default) 465: default port for implicit TLS 587: default port for STARTTLS | |
| Use implicit TLS: New from 11.8.4 |
Off | By default (deactivated), a connection is first established via smtp and then attempts to initiate TLS encryption with the remote terminal. | |
| On | When activated, the connection is first encrypted with TLS before smtp communication is established. If the remote terminal does not control TLS, no connection is established. The TLS version is configured under . | ||
| Smarthost Verification: | There is no verification of the smarthost. | ||
| The smarthost is verified by default installed root CAs or a self-signed CA. CA: (Default) Alternatively, a CA (previously created or imported under ) can be selected for authentication. | |||
| The Smarthost is only verified using the DANE protocol (RFC 6698) and must support this protocol.. The DANE protocol requires the mandatory activation of DNSSEC
| |||
| Enable Authentication: | On | Enables authentication on the smarthost mail server. | |
| User: | Credentials | ||
| Password: | Credentials |
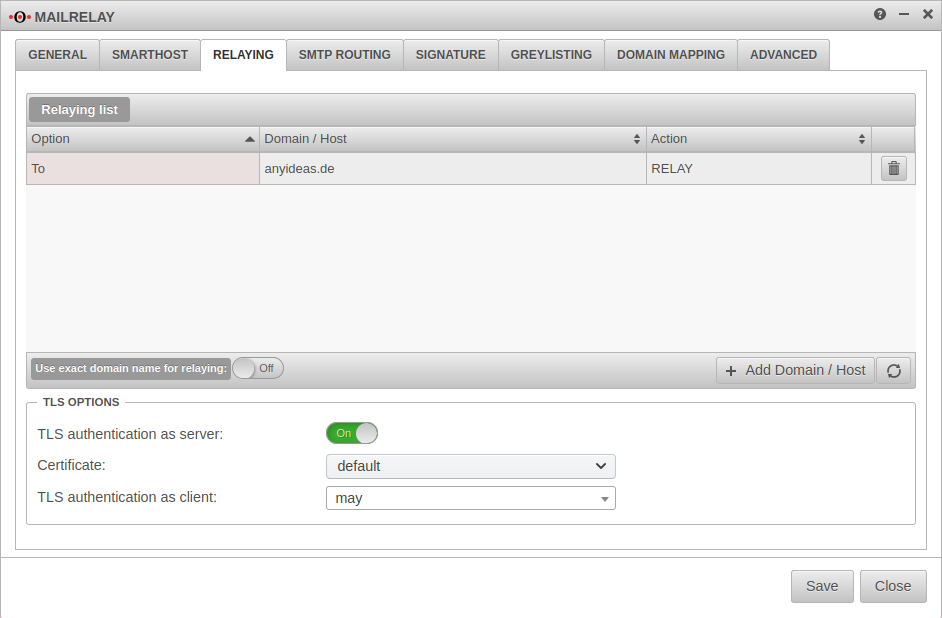
Relaying
Relaying list
Here it is configured which mails are accepted by the Securepoint appliance and forwarded to the internal mail server. Relaying can be allowed for certain hosts or certain domains.
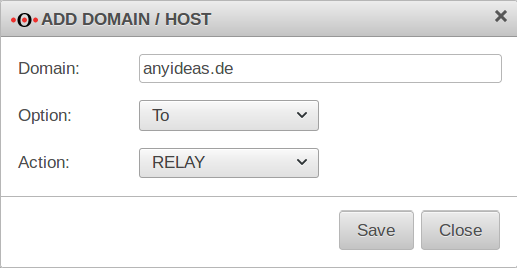
Add an entry with the button
In order to relay all mails intended for recipients of your own domain, the following entry must be configured:
| Domain / Host hizufügen | |
|---|---|
| Domain | anyideas.de
|
| Option | |
| Aktion | |
Use exact domain name for relaying:
On The relay reacts only to the domain name entered in the list and not to unregistered subdomains or extensions.
Example: Domain entered in the relay list: anyideas.de
TLS Settings
| Caption | Default | Description |
|---|---|---|
| TLS encryption as server: | On | If TLS is deactivated, mails are sent over unencrypted connections! |
| Certificate: | The mailrelay uses a self-signed certificate for transport encryption. Optionally, a certificate whose CN corresponds to the UTM host name can be imported under . | |
| TLS authentication as client: | Uses TLS if it is offered. | |
| Always uses TLS. Connection with servers that do not offer TLS will be cancelled. | ||
| Authenticates and uses TLS to DANE-compliant servers, if offered. |
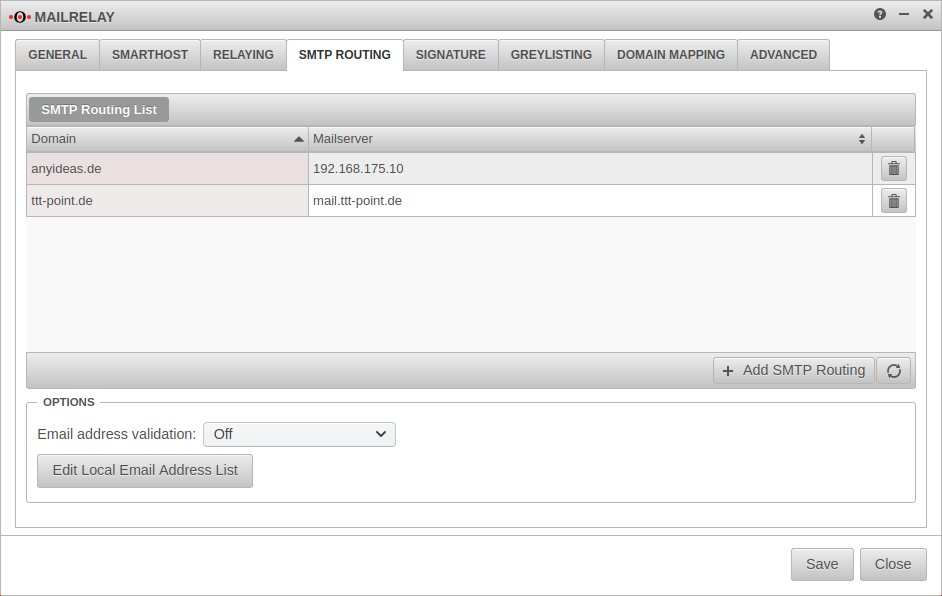
SMTP Routen
SMTP Routing List
With the button further routes are created.
| Required information: | |
|---|---|
| Domain: | anyideas.de (or the corresponding mail domain)
|
| Mailserver: | either as FQDN or the IP address
|
Options
In this section you can configure the verification of the destination email address. It causes mails to unknown recipients to be rejected. On the one hand the attempt to deliver spam to "invented" recipients is effectively prevented, on the other hand legitimate senders receive feedback that their mail could not be delivered, for example because they have committed themselves to the recipient address.
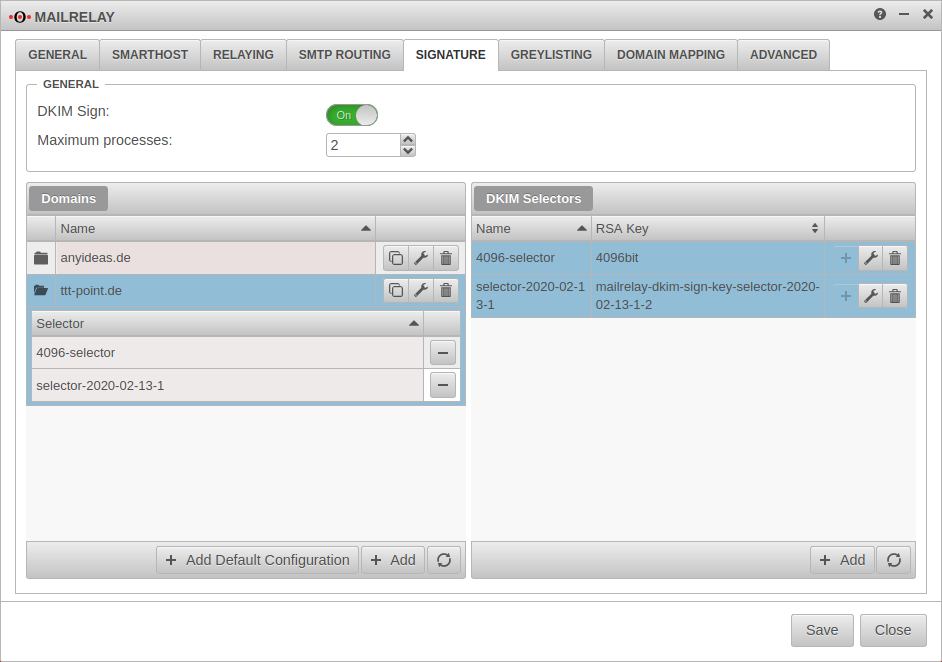
Signing
Optional Settings
Further settings are recommended, but not mandatory for operative use:
Greylisting
A regular mail server, on the other hand, will make another successful delivery attempt after a certain period of time.
The following configurations are possible:
Allowlist Allowlist | |||
| Caption | Default | Description | |
|---|---|---|---|
| IP / Networks | » ✕10.0.0.0/8 » ✕172.16.0.0/12 » ✕192.168.0.0/16 » ✕127.0.0.0/8 | The default are the private IP address ranges and the loopback address. With a click into the clickobx you can add further networks and single hosts (e.g.:» ✕203.0.113.113/32) | 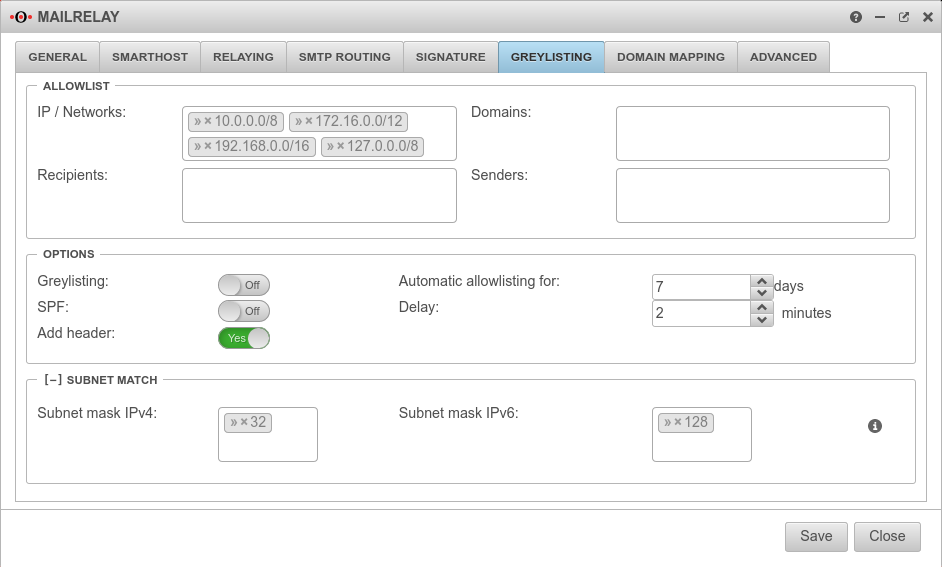 |
| Domains | Here single Mailserver domains can be added e.g.: smtp.anyideas.de The domain of the mail server does not have to be identical with the e-mail domain of the sender. Example: Sender user@ttt-point.de sends via the mail server » ✕smtp.anyideas.de | ||
| Recipient | Individual recipients can be added here, e.g: » ✕MailUser@ttt-point.de | ||
| Sender | Individual senders can be added here e.g.:{cb | ||
Settings Settings | |||
| Greylisting: | Aus | An activates the function Delivery attempts from unknown mail servers are initially rejected. | |
| SPF: | Aus | If the Sender Policy Framework of the sender domain is correctly entered in the DNS, the mail will be delivered without delay if On is activated. | |
| Add header: New as of v12.2.2 | Yes | By default, an additional greylisting entry is added for each recipient listed in the mail header. This can cause problems in case of many recipients. When disabled no, no greylisting headers are inserted. | |
| Automatic allowlisting for: | 7 Days(Default) | days(Default) : For this period, after a successful delivery mails will be accepted immediately. | |
| Delay: | 2 Minutes (Default) | minutes(Default): The period of time that the sending mail server is given to make another delivery attempt. | |
Subnet MatchSubnet Match | |||
| Subnet mask IPv4: | » ✕32 | Instead of the sending server having to have the exact IP address as before, this can be changed so that, for example, only the first 2 or 3 octets have to match. This enables whitelisting even if the sender has several mail servers. Possible values: (Only one value can be entered.) » ✕32 (Single Host) » ✕24 Subnet, with match of first three octets » ✕29 Any value via keyboard input. | |
| Subnet mask IPv6: | » ✕128 | ||
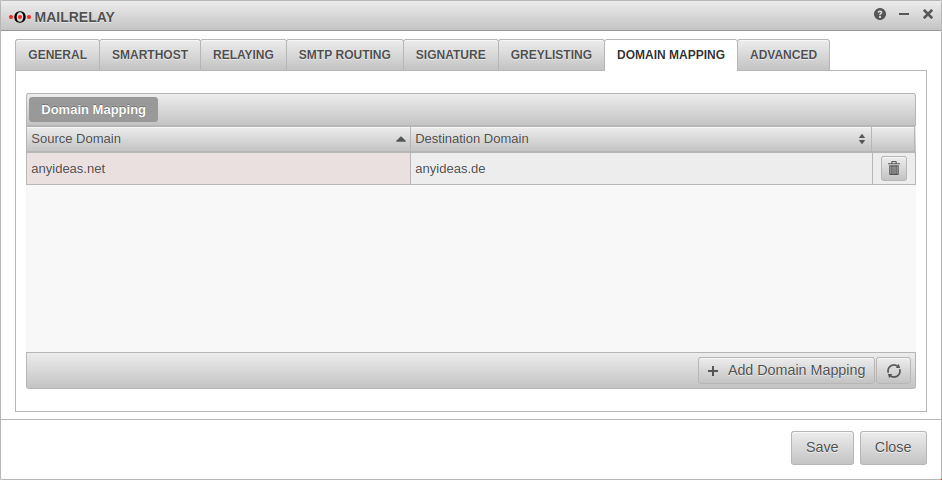
Domain Mapping
Domains can be mapped to receive incoming mails to e.g. user@anyideas.net also under user@anyideas.de.
With the mapping between two domains can be activated.
To do this, a Source-Domain: and a Destination Domain: must be specified.
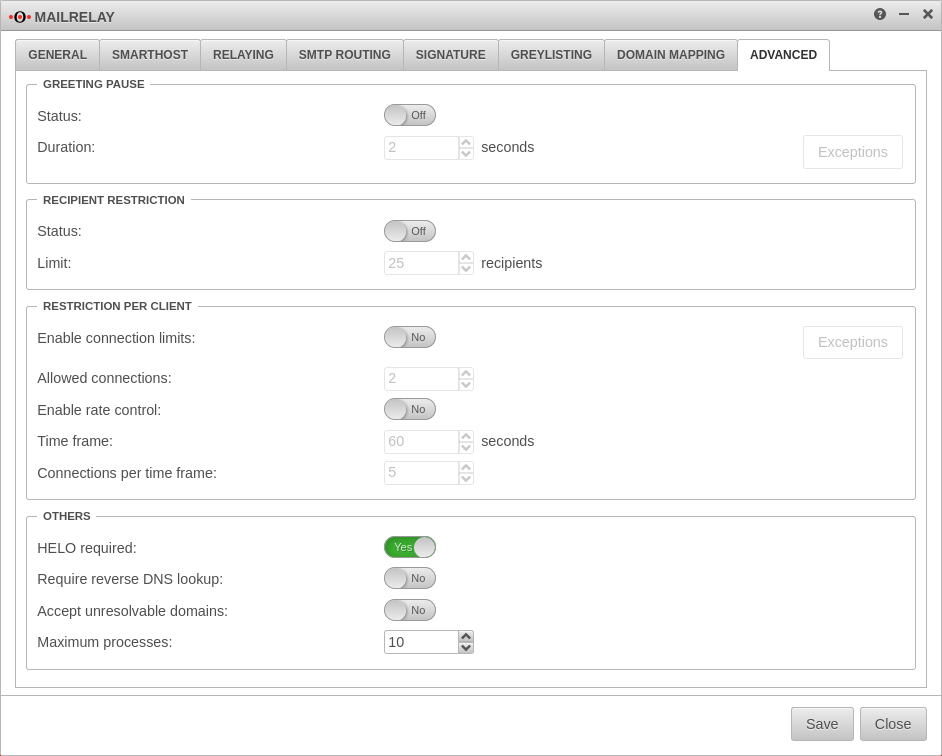
Advanced Settings
Here some further options to avoid spam can be found, each of which can be activated individually:
Configuration of the mailrelay for outgoing mails
To make sure that no spam or malware can be sent from your own network, the mail relay can also be used for outgoing mails.
Set of rules
To allow access to the mail relay, the hosts authorized to send mail must be allowed access to the corresponding interface of the Securepoint appliance (depending on the zone in which the hosts are located) via the SMTP protocol. Depending on the requirements, this can be a single host (e.g. the mail server), a group of hosts or the entire network. It is important that all applications that are to send mails via the mail relay have entered the corresponding firewall interface as SMTP server or smarthost.
For example, to allow the internal network access to the mail relay, the set of rules can be created with the predefined network groups:
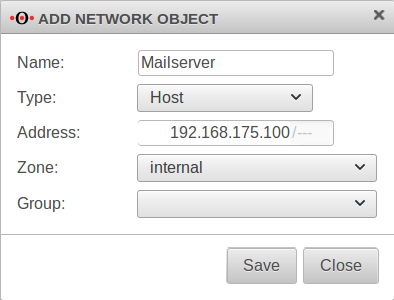
If only the mail server is to be able to send mails, it must first be created as a network object:
This object can then be used in the firewall rule:
If a certain group of computers in the internal network is to be allowed to use the mail relay, these computers must be created as network objects. These can then be combined in a group (e.g. "SMTP Authorized").
Configuration Relaying
In order for the mailrelay to accept mails from the internal network or from the mail server, the settings in the Relaying} tab must be supplemented by a corresponding entry. The network address of the corresponding subnet or the IP address of the relevant computer serves as criterion:
| Domain | 192.0.2.0/30 or 192.0.2.192 These are sample IPs for the internal mail servers. These have to be replaced by individual addresses! |
| Option | |
| Action |
Conclusion
The UTM can now check incoming and outgoing mails for spam and viruses.