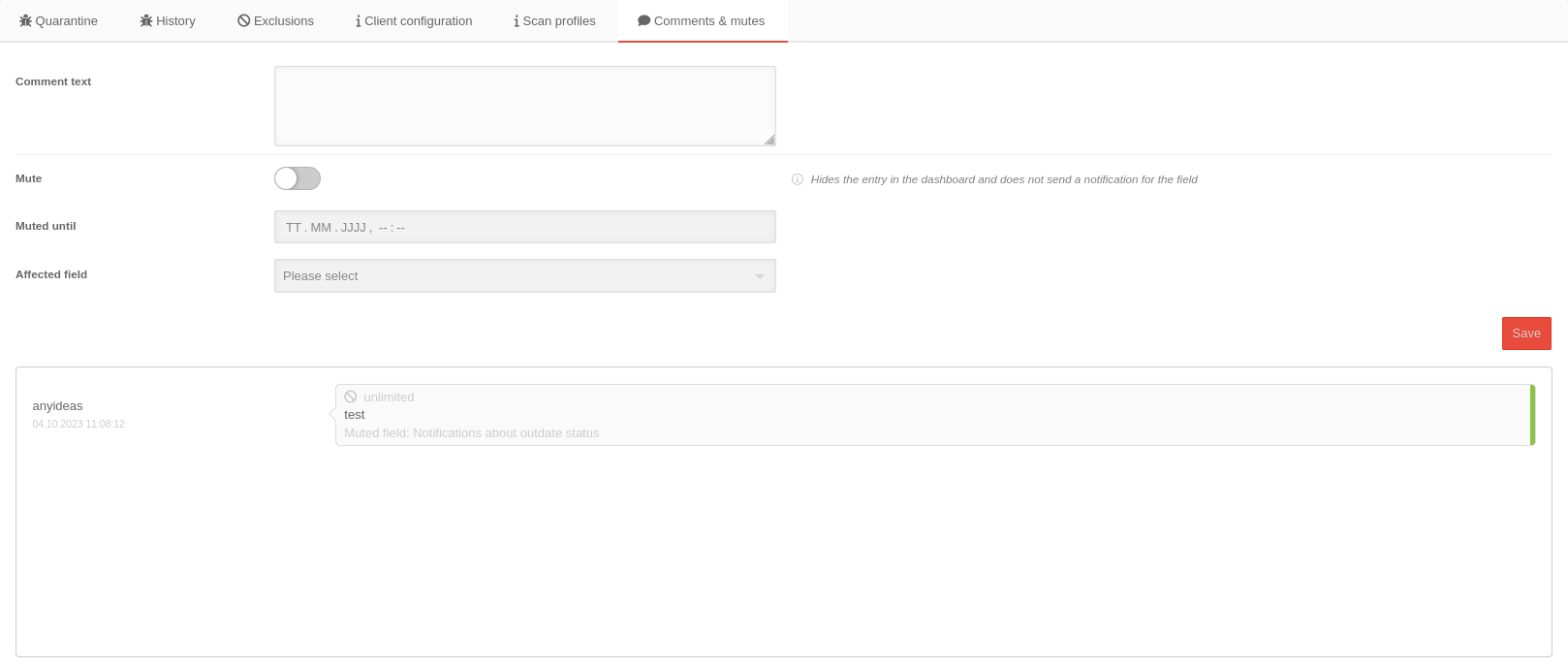
- Layout adjustments
- Note on de- / activating the muting
- New filter: 32-bit-systems only
Introduction
Device Information presents information about current threats as well as information about the device.
Device overview
In the device overview all devices can be managed which are installed and assigned to the own or the customer license. Several devices can be moved at the same time and the most important device information is displayed.
The list can be sorted by clicking on the according column name.
| Restrict the selection: | ||
|---|---|---|
| Displays only devices that match the search text. Not applied to: Operating system and status. | ||
| Export table | Exports the table with the device overview into a xlsx file which can be downloaded afterwards via a . | |
| Table settings | Leads to the tab Table Settings in the User Preferences. Here you can select the columns to be displayed for the tables Devices and Licenses. | |
| Opens a box with filter settings: | ||
| Filter | ||
| Display Entries | 25 Number of entries per page (10, 25, 50, 100) | |
| Status filter: | Displays only entries with the selected status (see below). | |
| Allows different actions with the selected devices | ||
| Move | Moves devices to a new group. If the group is no longer part of the installed license, the license affiliation is also changed. | |
| Activate | Enables Securepoint Antivirus Pro on the device | |
| Deactivating | Disables Securepoint Antivirus Pro on the device | |
| Delete | Deletes the device from the device management. Only possible if the device has been deactivated before! | |
| Caption | Description | |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Hostname | As stored in the operating system of the device. Links directly to Device Information. | |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
| Own description | As stored in the Device Information (freely definable). | |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
| Group | Group to which the device belongs. Links directly to Group Settings. | |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
| IP address | IP address of the device. | |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
| Domain | Domain name, if device is a member. | |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
| Operating System | Operating system of the device. | |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
| Infections | Number of reported (and untreated) infections since last contact. | |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
| Status |
| |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
Device Information
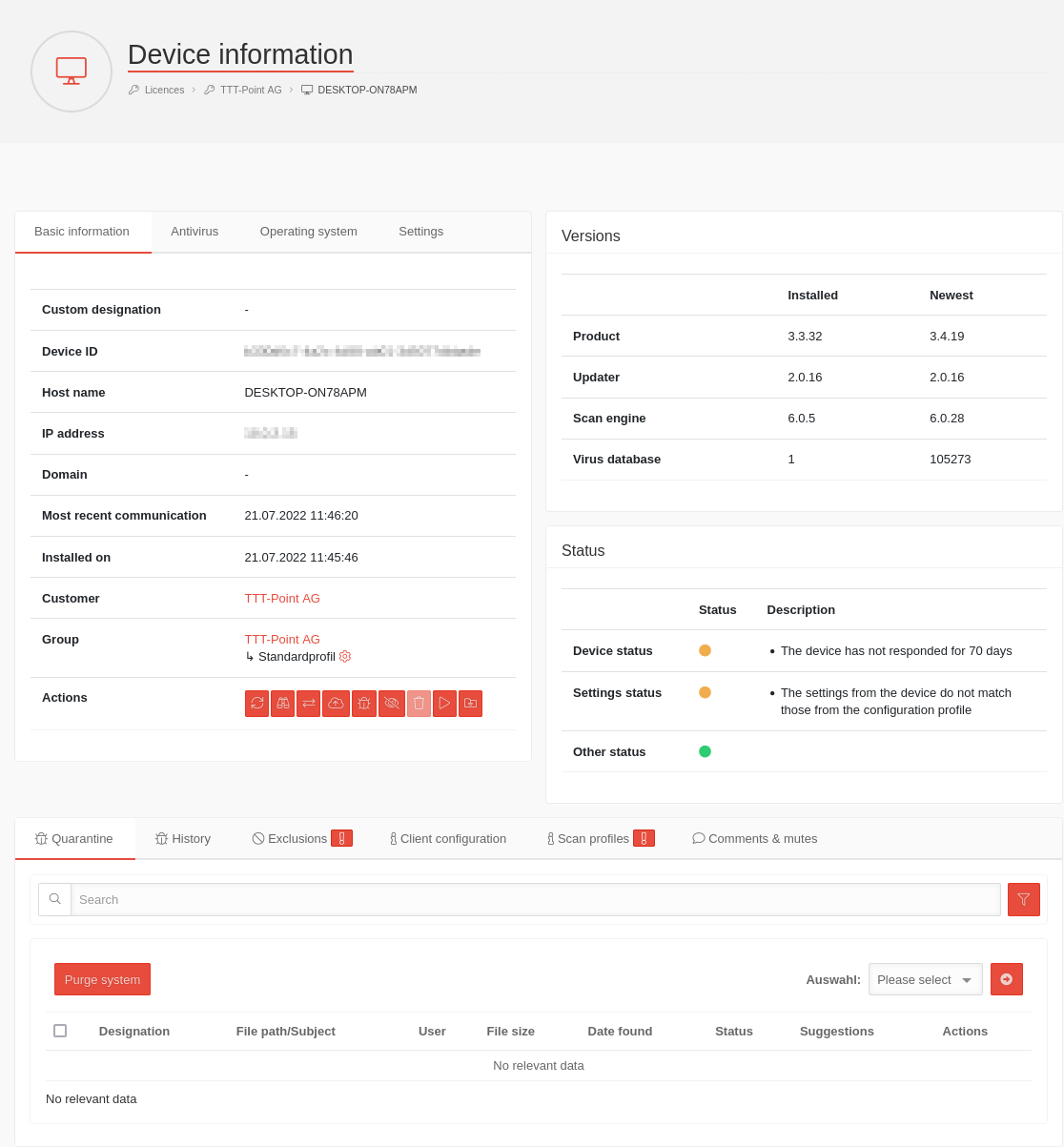
Further device information can be displayed by clicking on the device name. These are divided into different sections. By clicking on the Basic Information, Antivirus or Operating System tabs you will get the corresponding information. The version information is compared with the data from the update servers and indicates which modules are on which update status.
In the viruses Quarantine area, current threats are displayed. Threats with which an action has been performed (e.g. Delete and Save) will be displayed at viruses History.
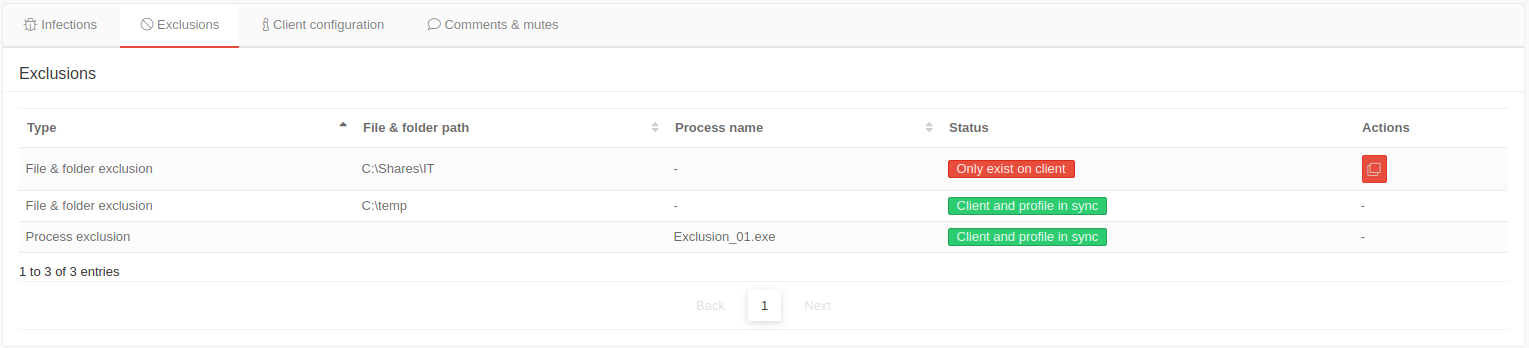
In the Exclusions tab, files, folders or processes can be excluded from the scan.
Versions
The Versions section displays the installed and the latest versions of various components of Antivirus Pro:
- Product
- Updater
- Scan Engine
- Virus database
If the installed version does not match the latest version, an update should be carried out on the client. If necessary, a problem in the update process can be detected here.
Basic Information
The basic informations display important informations about the device and settings for notifications.
| Caption | Description | ||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Custom designation | The name that appears in the basic information can be assigned here. | ||||||||||||||||||||
| Device ID | 1234abcd-12ab-12ab-12ab-123456abcdef | ||||||||||||||||||||
| Hostname | As stored in the operating system of the host | ||||||||||||||||||||
| IP address | IP address in the local network of the host | ||||||||||||||||||||
| Domain | If applicable, display of the domain in which the device is a member | ||||||||||||||||||||
| Client Password | Shows whether the client is protected with a password against modification / uninstallation. | ||||||||||||||||||||
| Last communication | Date and time of communication between client and portal | ||||||||||||||||||||
| Installed at | Date and time of installation | ||||||||||||||||||||
| Customer | Linked to the associated customer administration in the reseller portal | ||||||||||||||||||||
| Groups | Links to the corresponding group in the group management in the AV portal and displays all devices belonging to this group. Also shows the ↳ configuration profile associated with this group, which is linked to edit with | ||||||||||||||||||||
| Action |
|
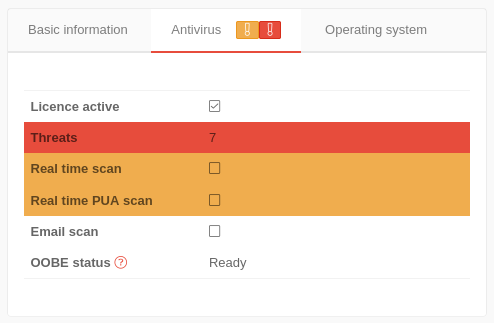
Antivirus
The tab Antivirus contains the information about the Securepoint Antivirus Client.
The information whether the license is active, the client is currently running or a threat has been found is highlighted in color.
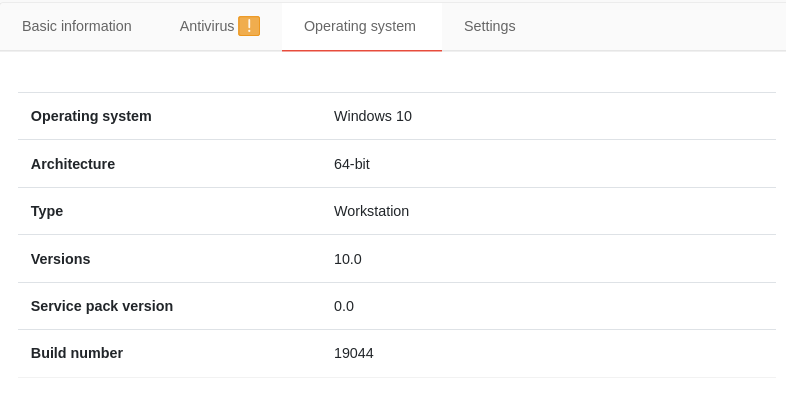
Operating System
The operating system information contains information about the operating system on which the Securepoint Antivirus Pro Client is installed.
Settings
| Caption | Description |  |
|---|---|---|
| Custom designation | The name that appears in the basic information can be assigned here. | |
| Save | Saves the settings | |
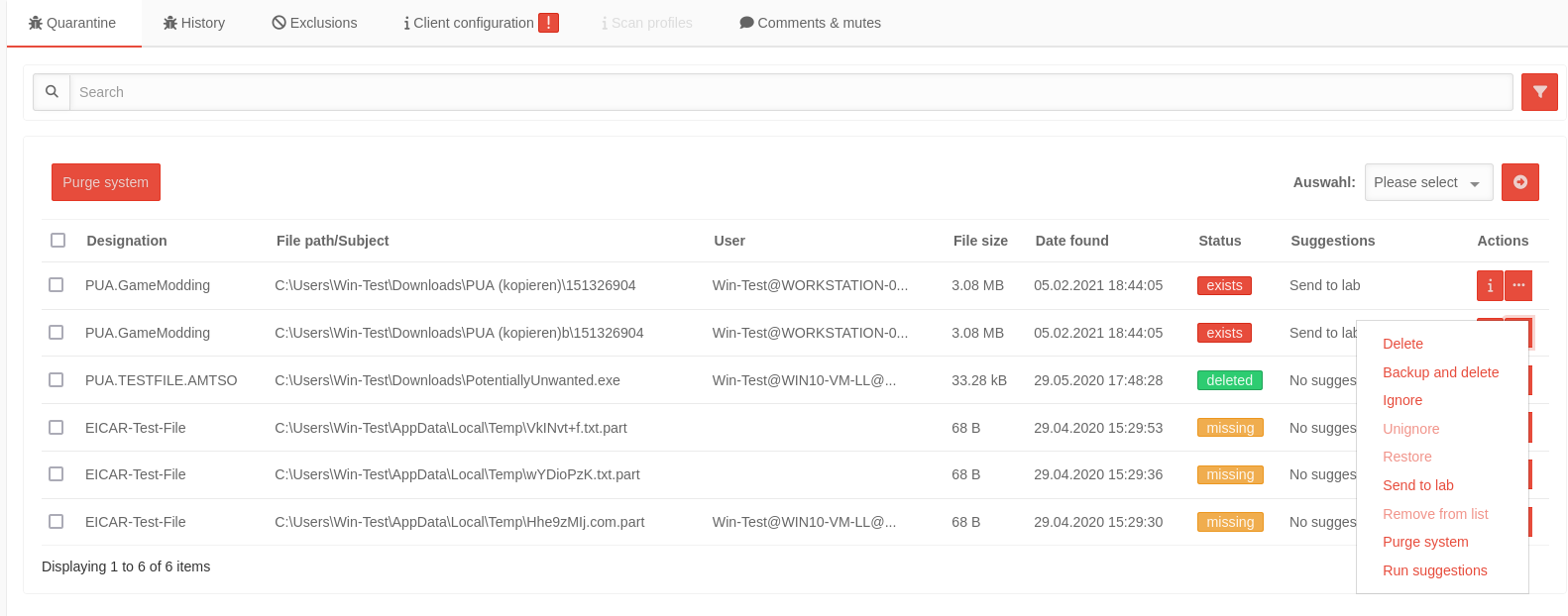
Quarantine
Shows various information about found viruses.
The listing can be sorted by column headings.
With the button various actions can be triggered on the host for those entries marked with .
| Caption | Value | Description | |
|---|---|---|---|
| Designation | EICAR-Test-File | Name of the file by the Ikarus engine. Please note: The names of viruses and PUAs can differ between different antivirus programs. | |
| File path / subject | C:\... | Local file path on the device with AV Client | |
| user | |||
| File size | 68 B | Size of the infected file | |
| Date found | 14.04.2020 12:26:19 | ||
| Status | exists | Access to the object is blocked. No actions have been performed so far | |
| ignored | Object was found, but the access was temporarily (until the next restart of the Antivirus Pro service) released again. | ||
| deleted | The object was deleted. | ||
| copy exists | A backup copy has been made and access to it has been blocked. The original object was deleted. | ||
| file is missing | The file was removed on the host system (without executing it). | ||
| Suggestions | Suggested action | ||
| Actions | Displays the details of the scan profile and whether the individual settings are synchronized between the portal and the client. | ||
| Performs one of the following actions | |||
| Delete | Deletes the object definitely from the system. | ||
| Backup and delete | Files: Creates a backup copy, blocks access to it and deletes the original object. This allows the file to be restored to its original location if necessary. | ||
| Ignore | Temporarily releases the selected files (until the next restart of the Antivirus Pro service) | ||
| Unignore | Cancels the previously selected share of a file already before a reboot. | ||
| Restore | Restores the file to its original location. The status changes to exists} | ||
| Send to lab | The suspicious file is sent to the analysis laboratory. An email address for feedback can be provided upon request. The status does not change. | ||
| Remove from List | Removes entries from the quarantine list. These entries are then only in the
| ||
| Purge system | Is like "Backup and Delete": It creates a backup copy of the file, and then deletes the original. Additional removes virus entries from the registry. The process can take much longer. | ||
| Run suggestions | Carry out the recommendation. Especially advantageous in case of several marked threats via the button on the left at the beginning of the table!
| ||
Exclusions
client configuration
The current settings on the client are displayed here.
| synchronous | The settings in the machine and in the profile are identical. |
| asynchronous | The settings in the device and in the profile are not identical. |
| Caption | Default | Description |
|---|---|---|
| Monitoring the system | Can be disabled in the Guard section. | |
| PUA and PUP detection | Can be disabled in the Guard section. | |
| System monitoring after reboot | Can be deactivated in the Tools menu → Settings / tab Extras . | |
| Use default settings | Can be deactivated in the Tools menu → Settings / tab Exclusions . | |
| Maximum file size (In MB) | - | Size in MB up to which files are scanned. |
| Participate in signature quality assurance | Can be deactivated in the Tools menu → Settings / tab Extras . |
| Caption | Default | Description |
|---|---|---|
| Log system supervision in the main log | Can be activated in the Tools menu → Settings / tab Logging . | |
| Record logs for scans | Can be activated in the Tools menu → Settings / tab Logging . | |
| Record all data when scanning | Can be activated in the Tools menu → Settings / tab Logging . | |
| Overwrite logs | Can be activated in the Tools menu → Settings / tab Logging . |
| Caption | Default | Description |
|---|---|---|
| Use Proxy-Server | Can be activated in the Tools menu → Settings / tab Update . | |
| Use System Proxy | Can be activated in the Tools menu → Settings / tab Update . | |
| Proxyserver Address | - | Can be activated in the Tools menu → Settings / tab Update . |
| Proxyserver port | - | Can be activated in the Tools menu → Settings / tab Update . |
| Proxyserver login | Can be activated in the Tools menu → Settings / tab Update . | |
| Password protection | Can be activated in the Tools menu → Settings / tab Extras at Password protection. |
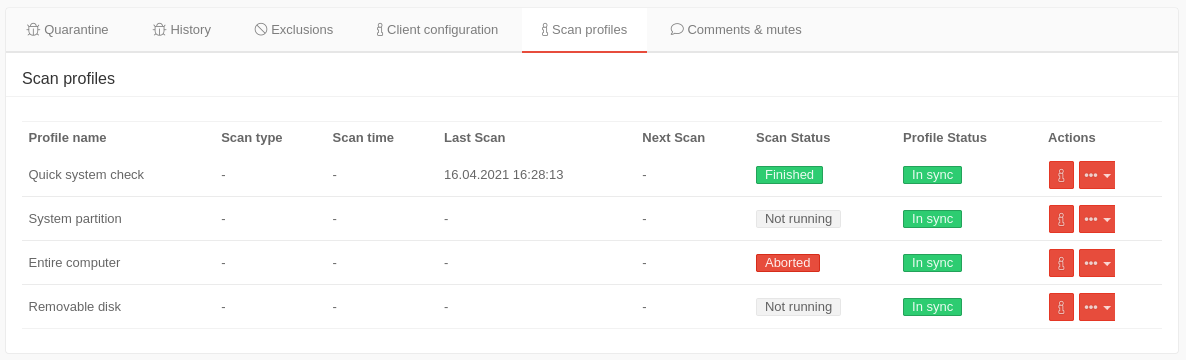
Scan profile