notempty
- Note on ESP and UDP 500/4500
- IKEv2 Lifetime and Rekeying are automatically swapped if necessary
- Weak algorithms are displayed in the selection dialogs only after explicit activation (IKEv1 and IKEv2)
- Hide IKEv1 L2TP. Display only with special activation (v12.4)
- Copy psk to clippboard (v12.4)
- Note on Config_mode for NCP or Greenbow clients (v12.4)
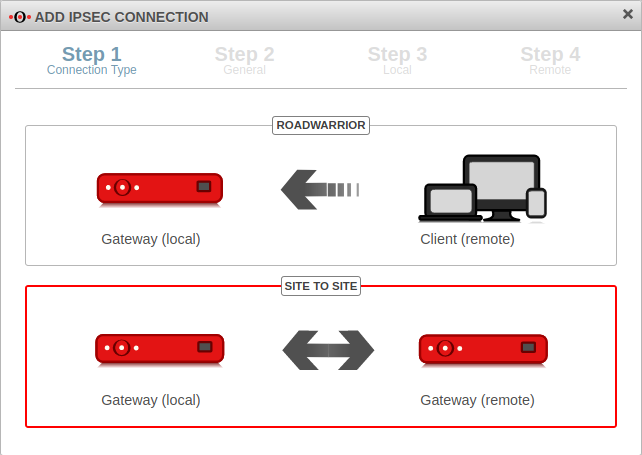
Introduction
A Site-to-Site connection links two networks together.
For example, the local network of a main office with the local network of a branch office / secondary office.
Public IP addresses, as well as dynamic DNS entries, can be used to connect the two remote gateways.
Preparation
Configuration of an IPSec Site-to-Site connection
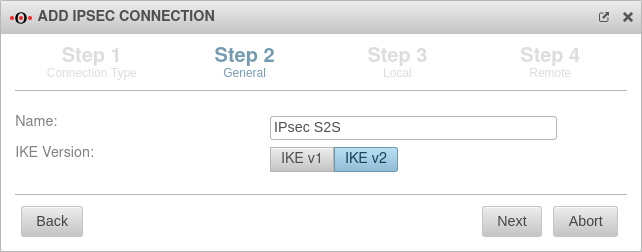
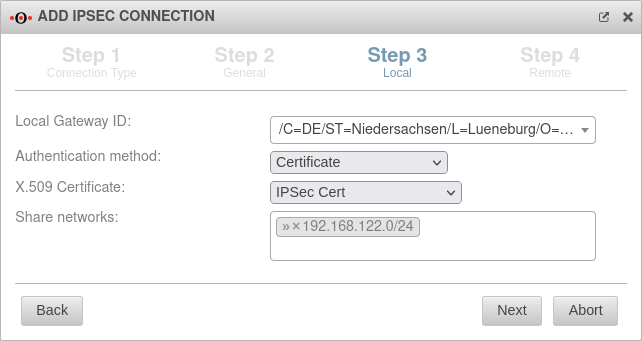
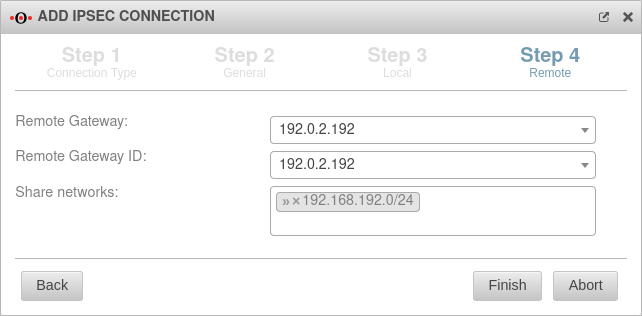
Setup Wizard
More settings
IKEv1
notempty
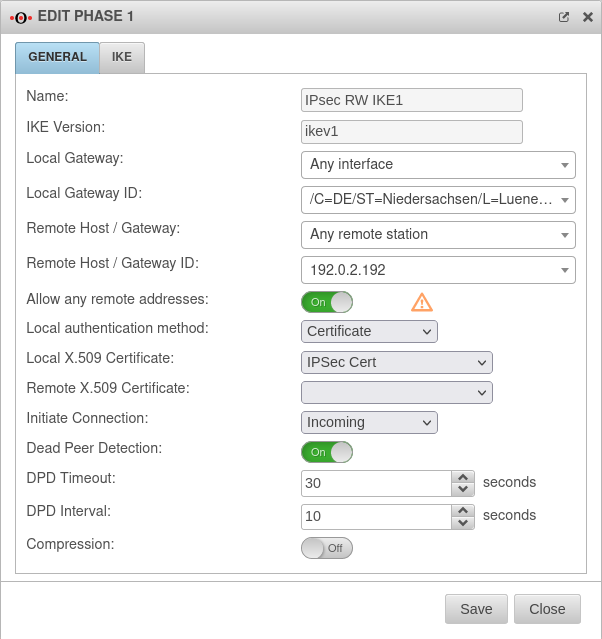
Phase 1 | ||||||
Tab Connections Button GeneralTab General | ||||||
| Caption | Value | Description | 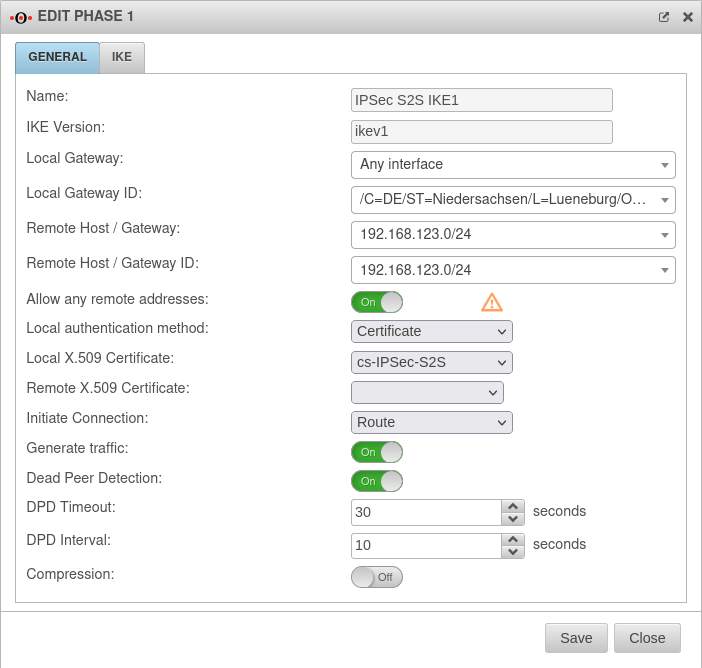 |
|||
|---|---|---|---|---|---|---|
| Allow any remote addresses: | On Default |
Disable this option for site-to-site connections with DynDNS hosts if multiple IPsec connections with a priori unknown addresses (DynDNS S2S, Roadwarrior) are configured. | ||||
| Startup behavior: |
The tunnel is initiated by the UTM even if no packets are sent. Incoming requests are accepted. | |||||
| Default if Remote Host is any | The UTM accepts incoming tunnel requests. No outgoing connection is created. | |||||
| Default if Remote Host known | The tunnel is initiated by the UTM only when packets are to be sent.notempty Only set as default value if Any remote station is not selected as Remote Host / Gateway.
| |||||
| Deactivates the tunnel | ||||||
| Generate traffic: notempty New as of v12.4 For Initiate Connection Route |
On | Prevents unwanted disconnections when no data traffic is taking place | ||||
| Dead Peer Detection: | On | Checks at a set interval whether the tunnel still exists. If the tunnel was terminated unexpectedly, the SAs are dismantled. (Only then it is also possible to reestablish a new tunnel). | ||||
| DPD Timeout: | 30 seconds | Period before the state under Startup behavior is restored. The same values are used here as for regular packets. | ||||
| DPD Interval: | 10 seconds | Testing interval | ||||
| Compression: | Off | Compression is not supported by all remote stations | ||||
| Enable MOBIKE: | Yes Default |
Used to deactivate the MOBIKE option Deactivation prevents encrypted data from a remote station from being additionally encapsulated in 4500udp, which leads to problems in communication. | ||||
Tab IKE Settings that must be identical in the UTM and in the client: IKE | ||||||
| Caption | Default-Werte UTM | Default-Werte NCP-Client | 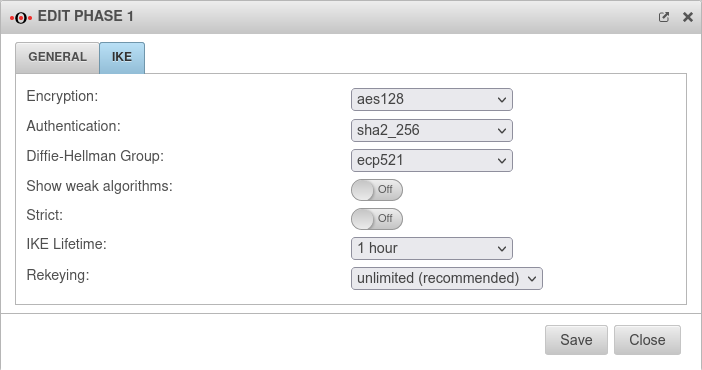 |
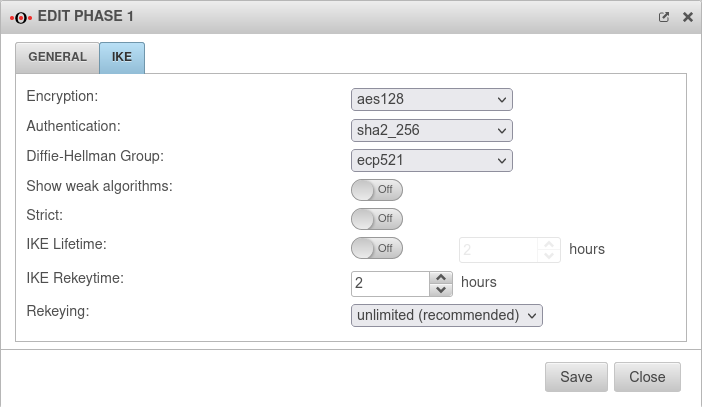 | ||
| Encryption: | AES 128 Bit | |||||
| Authentication: | Hash: SHA2 256 Bit | |||||
| Diffie-Hellman Group: | IKE DH-Gruppe: DH2 (modp1024) | |||||
New default value as of v12.5.1
| ||||||
| Tab IKE More settings: | ||||||
| Caption | Value | Description | ||||
| Show weak algorithms: notempty New as of v12.5 |
Off | Also shows algorithms in the selection dialogs that are considered weak and should not be used. | ||||
| Strict: | Off | The configured parameters (authentication and encryption algorithms) are preferred for connections | ||||
| On | No further proposals are accepted. A connection is only possible with the configured parameters. | |||||
| IKE Life time: notempty Change as of v12.5 |
Out 3 hours | Validity period of the Security Association: Agreement between two communicating entities in computer networks. It describes how the two parties apply security services to communicate securely with each other. When using multiple services, multiple security connections must also be established. (Source: Wikipedia 2022) in phase 1 Can be activated Vorlage:ButtonOn in addition to IKE Rekeytime. If the Lifetime is set, the value must be greater than the Rekeytime. | ||||
| IKE Life time: | Validity period of the Security Association: Agreement between two communicating entities in computer networks. It describes how the two parties apply security services to communicate securely with each other. When using multiple services, multiple security connections must also be established. (Source: Wikipedia 2022) in phase 1 | |||||
| IKE Rekeytime: notempty New as of: v12.4 notemptyChange as of v12.5 |
2 hours | The validity period in which the connection is established (initial or after termination) | ||||
| notempty Starting with version 12.5.0, for already existing' connections that have no rekeytime' set, the value of the lifetime is entered at this point and the value of the lifetime is set to 0.
This significantly increases the stability of the connection and should not bring any disadvantages. If a value has already been set for the rekeytime (possible from v12.4) no change is made. Example: Current version: ike_lifetime = 2 ike_rekeytime = 0 After update: ike_lifetime = 0 ike_rekeytime = 2 ---- Current version: ike_lifetime = 2 ike_rekeytime = 1 After update: (without change) ike_lifetime =2 ike_rekeytime = 1 | ||||||
| Rekeying: | Number of attempts to establish the connection (initial or after abort). For E2S connections (Roadwarrior), the setting 3 times can avoid endless attempts to connect to devices that are not correctly logged out. | |||||
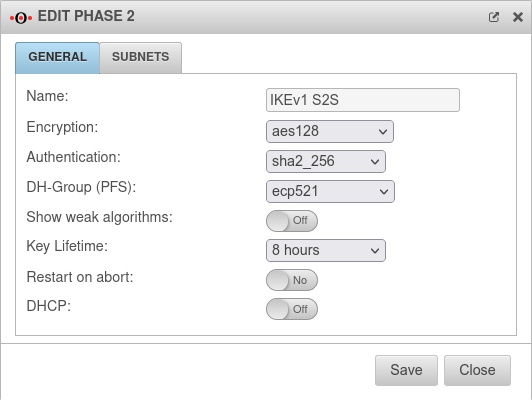
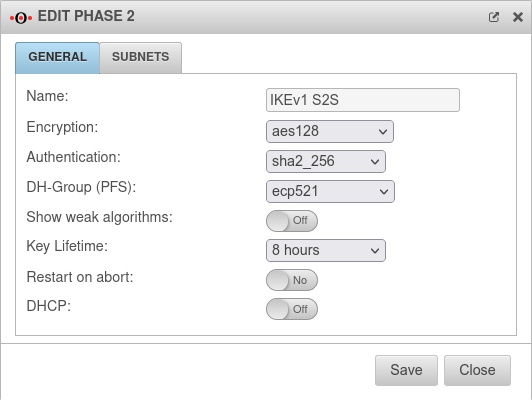
Phase 2 | ||||||
Tab Connections Button GeneralTab General : Settings that must be identical in the UTM and in the client: | ||||||
| Caption | Default-Werte UTM | Default-Werte NCP-Client | 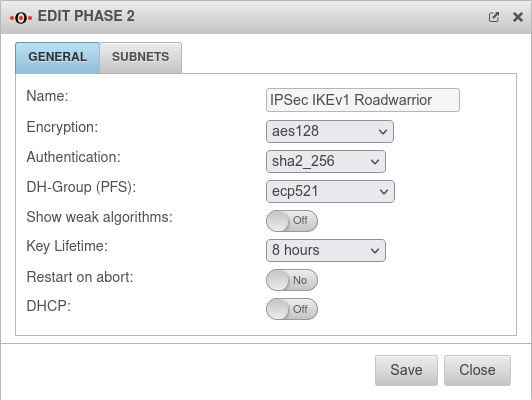 |
 |
 |
 |
| Encryption: | AES 128 Bit | |||||
| Authentication: | SHA2 256 Bit | |||||
| Diffie-Hellman Group: | IKE DH-Gruppe: DH2 (modp1024) | |||||
New default value as of v12.5.1
| ||||||
| Diffie-Hellman Group: | IKE DH-Gruppe: DH2 (modp1024) | |||||
| Schlüssel-Lebensdauer: | Validity period of the key in phase 2 | |||||
| Austausch-Modus | Main Mode (nicht konfigurierbar) | Aggressive Mode (IKEv1) The UTM does not support Aggressive Mode for security reasons. | ||||
Tab General: More settings | ||||||
| Show weak algorithms: notempty New as of v12.5 |
Off | Also shows algorithms in the selection dialogs that are considered weak and should not be used. | ||||
| Restart on abort: | No | If the connection was terminated unexpectedly, activating will restore the state configured under Startup behavior in phase 1. | ||||
| DHCP: | Out | When enabled (On), clients receive IP addresses from a local network. | ||||
Troubleshooting
Detailed Troubleshooting instructions can be found in the Troubleshooting Guide If an email address should be used as gateway ID, it is necessary to insert a double @@ in front of the ID (mail@... becomes @@mail@...). Otherwise the ID will be treated as FQDN
IKEv2
notempty
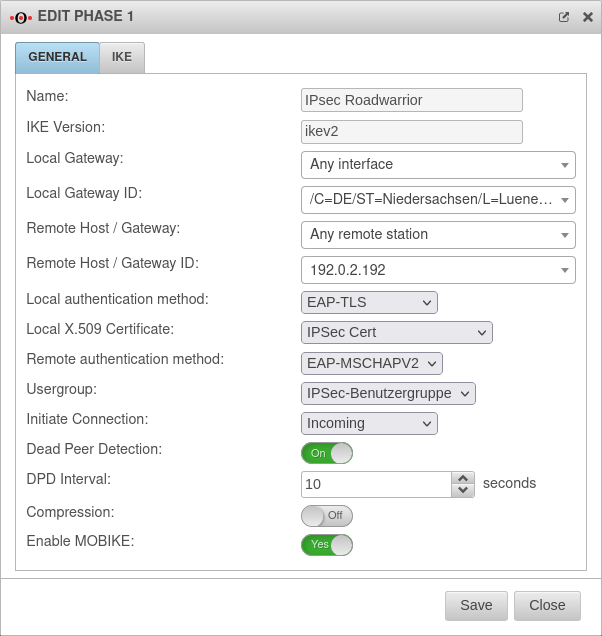
Phase 1 | ||||||
Tab Connections Button GeneralTab General | ||||||
| Caption | Value | Description | 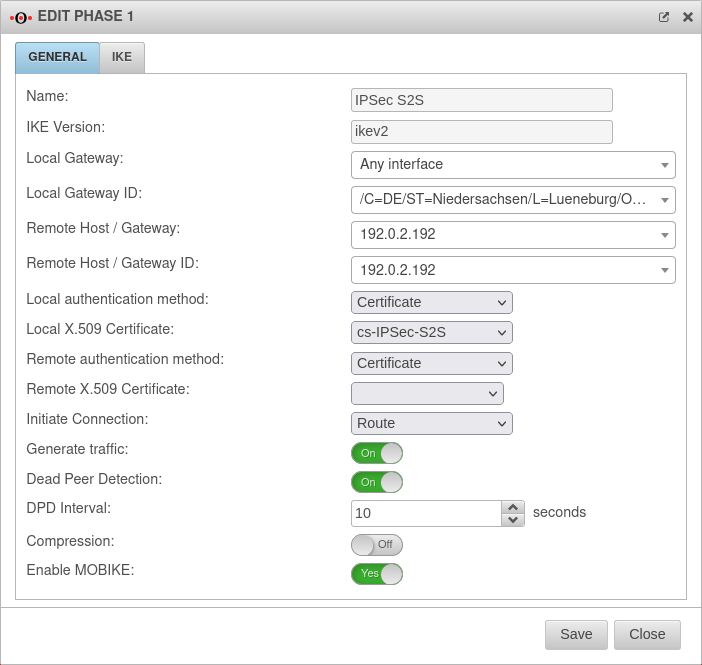 | |||
|---|---|---|---|---|---|---|
| Startup behavior: |
The tunnel is initiated by the UTM even if no packets are sent. Incoming requests are accepted. | |||||
| Default if Remote Host is any | The UTM accepts incoming tunnel requests. No outgoing connection is created. | |||||
| Default if Remote Host known | The tunnel is initiated by the UTM only when packets are to be sent.notempty Only set as default value if Any remote station is not selected as Remote Host / Gateway.
| |||||
| Deactivates the tunnel | ||||||
| Generate traffic: notempty New as of v12.4 For Initiate Connection Route |
On | Prevents unwanted disconnections when no data traffic is taking place | ||||
| Dead Peer Detection: | On | Checks at a set interval whether the tunnel still exists. If the tunnel was terminated unexpectedly, the SAs are dismantled. (Only then it is also possible to reestablish a new tunnel). | ||||
| DPD Timeout: | 30 seconds | Period before the state under Startup behavior is restored. The same values are used here as for regular packets. | ||||
| DPD Interval: | 10 seconds | Testing interval | ||||
| Compression: | Off | Compression is not supported by all remote stations | ||||
| Enable MOBIKE: | Yes Default |
Used to deactivate the MOBIKE option Deactivation prevents encrypted data from a remote station from being additionally encapsulated in 4500udp, which leads to problems in communication. | ||||
Tab IKE Settings that must be identical in the UTM and in the client: IKE | ||||||
| Caption | Default-Werte UTM | Default-Werte NCP-Client | 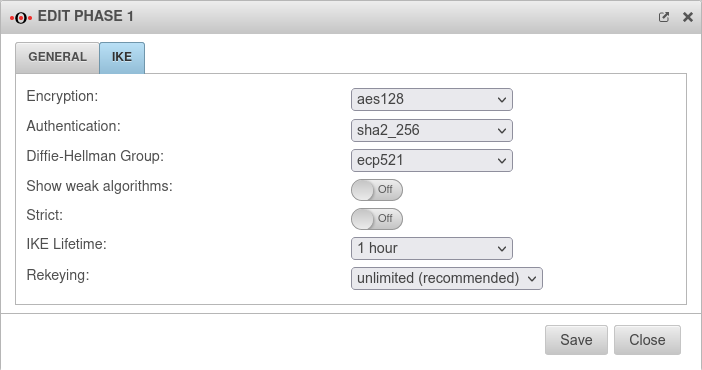 |
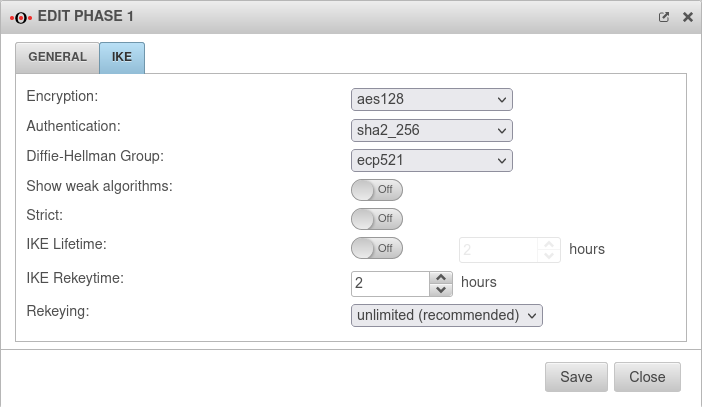 | ||
| Encryption: | AES 128 Bit | |||||
| Authentication: | Hash: SHA2 256 Bit | |||||
| Diffie-Hellman Group: | IKE DH-Gruppe: DH2 (modp1024) | |||||
New default value as of v12.5.1
| ||||||
| Tab IKE More settings: | ||||||
| Caption | Value | Description | ||||
| Show weak algorithms: notempty New as of v12.5 |
Off | Also shows algorithms in the selection dialogs that are considered weak and should not be used. | ||||
| Strict: | Off | The configured parameters (authentication and encryption algorithms) are preferred for connections | ||||
| On | No further proposals are accepted. A connection is only possible with the configured parameters. | |||||
| IKE Life time: notempty Change as of v12.5 |
Out 3 hours | Validity period of the Security Association: Agreement between two communicating entities in computer networks. It describes how the two parties apply security services to communicate securely with each other. When using multiple services, multiple security connections must also be established. (Source: Wikipedia 2022) in phase 1 Can be activated Vorlage:ButtonOn in addition to IKE Rekeytime. If the Lifetime is set, the value must be greater than the Rekeytime. | ||||
| IKE Life time: | Validity period of the Security Association: Agreement between two communicating entities in computer networks. It describes how the two parties apply security services to communicate securely with each other. When using multiple services, multiple security connections must also be established. (Source: Wikipedia 2022) in phase 1 | |||||
| IKE Rekeytime: notempty New as of: v12.4 notemptyChange as of v12.5 |
2 hours | The validity period in which the connection is established (initial or after termination) | ||||
| notempty Starting with version 12.5.0, for already existing' connections that have no rekeytime' set, the value of the lifetime is entered at this point and the value of the lifetime is set to 0.
This significantly increases the stability of the connection and should not bring any disadvantages. If a value has already been set for the rekeytime (possible from v12.4) no change is made. Example: Current version: ike_lifetime = 2 ike_rekeytime = 0 After update: ike_lifetime = 0 ike_rekeytime = 2 ---- Current version: ike_lifetime = 2 ike_rekeytime = 1 After update: (without change) ike_lifetime =2 ike_rekeytime = 1 | ||||||
| Rekeying: | Number of attempts to establish the connection (initial or after abort). For E2S connections (Roadwarrior), the setting 3 times can avoid endless attempts to connect to devices that are not correctly logged out. | |||||
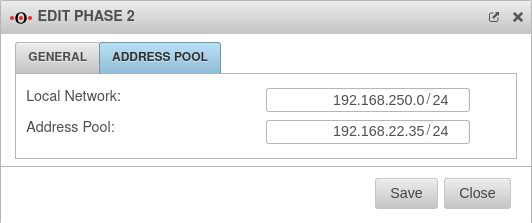
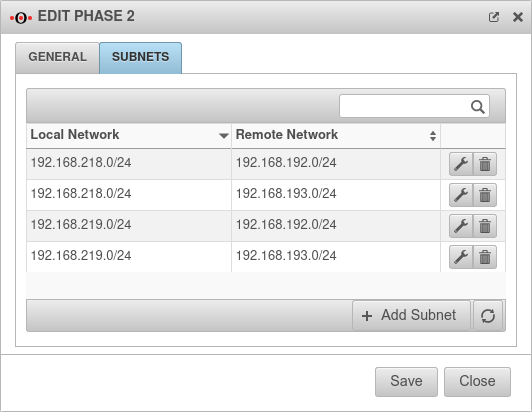
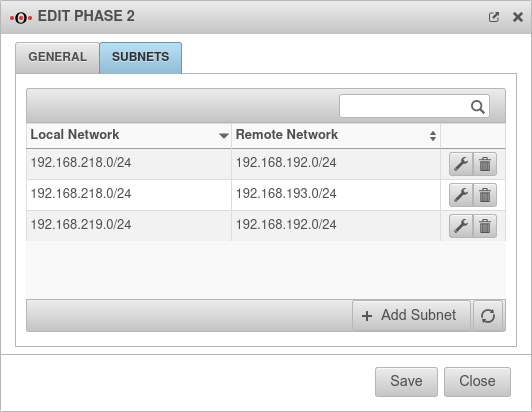
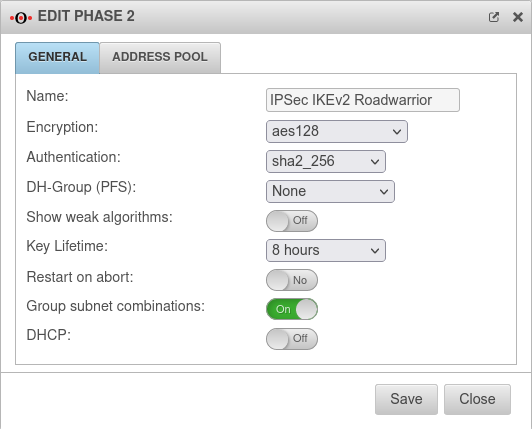
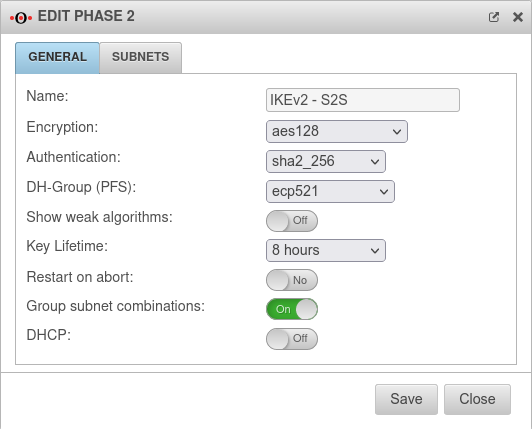
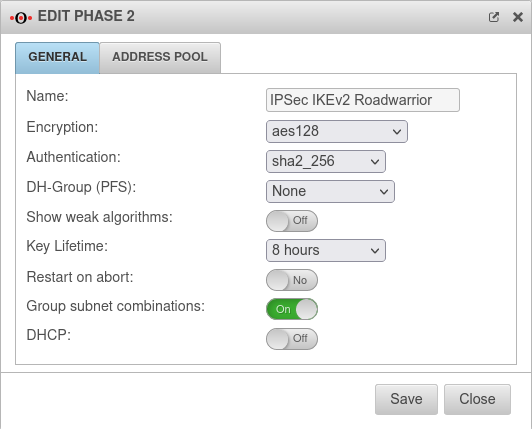
Phase 2 | ||||||
Tab Connections Button GeneralTab General : Settings that must be identical in the UTM and in the client: | ||||||
| Caption | Default-Werte UTM | Default-Werte NCP-Client | 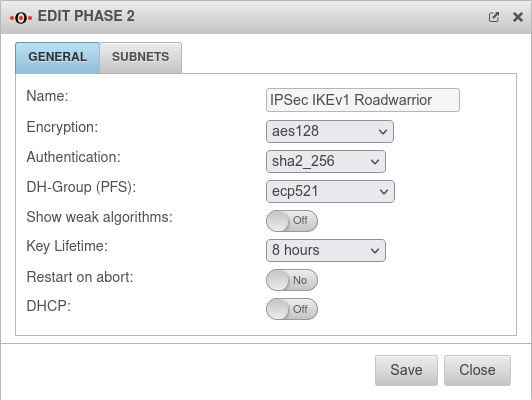 |
 |
 |
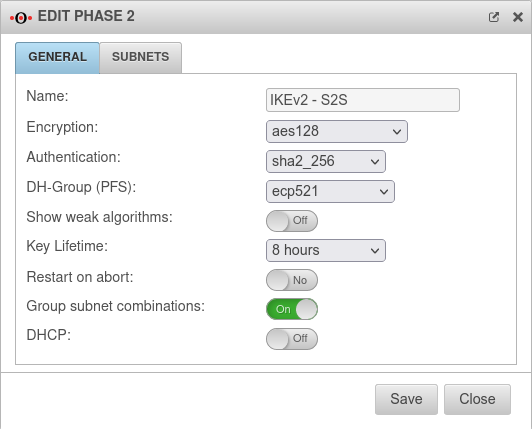 |
| Encryption: | AES 128 Bit | |||||
| Authentication: | SHA2 256 Bit | |||||
| Diffie-Hellman Group: | IKE DH-Gruppe: DH2 (modp1024) | |||||
New default value as of v12.5.1
| ||||||
| Diffie-Hellman Group: | IKE DH-Gruppe: DH2 (modp1024) | |||||
| Schlüssel-Lebensdauer: | Validity period of the key in phase 2 | |||||
| Austausch-Modus | Main Mode (nicht konfigurierbar) | Aggressive Mode (IKEv1) The UTM does not support Aggressive Mode for security reasons. | ||||
Tab General: More settings | ||||||
| Show weak algorithms: notempty New as of v12.5 |
Off | Also shows algorithms in the selection dialogs that are considered weak and should not be used. | ||||
| Restart on abort: | No | If the connection was terminated unexpectedly, activating will restore the state configured under Startup behavior in phase 1. | ||||
| Group subnet combinations: | Yes |
If more than one network is configured on the local side or at the remote gateway, a separate SA is negotiated for each subnet combination when it is deactivated. This results in numerous subnet combinations and thus many SAs, especially with multiple subnets, and leads to limitations and losses in the stability of the connections due to the design of the IPSec protocol. | ||||
| DHCP: | Out | When enabled (On), clients receive IP addresses from a local network. | ||||
Troubleshooting
Detailed Troubleshooting instructions can be found in the Troubleshooting Guide If an email address should be used as gateway ID, it is necessary to insert a double @@ in front of the ID (mail@... becomes @@mail@...). Otherwise the ID will be treated as FQDN
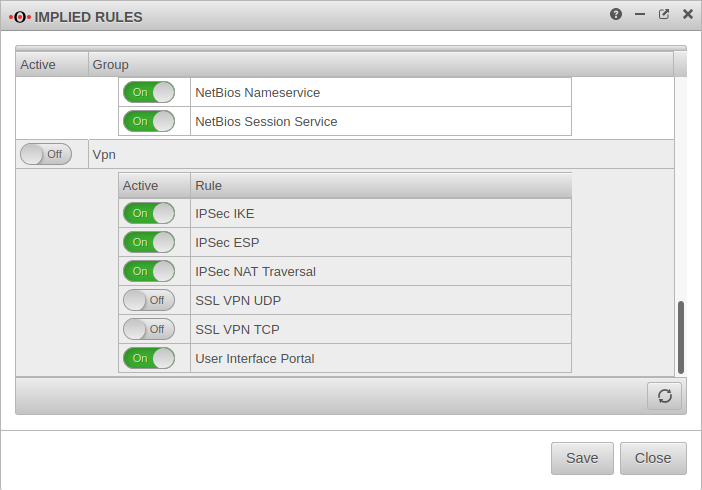
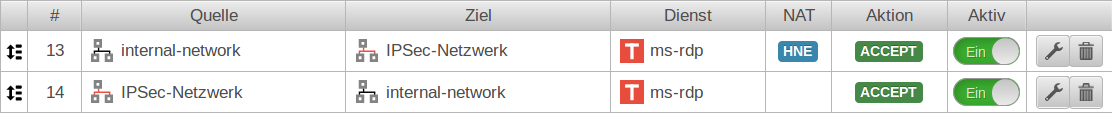
Rulebook
To grant access to the internal network, the connection must be allowed.
Configuration of the second gateway
It should be noted that the IKE version is identical on both sides.
Use of a Securepoint UTM
On the remote gateway, the settings must be made in a similar way
- A new IPSec VPN connection is created using the IPSec wizard
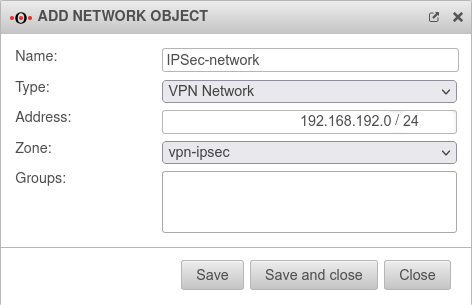
- A network object for the IPSec network is created
- Port filter rules are created
Remote Gateway step 2
- The same authentication method must be selected
- The same authentication key (PSK, certificate, RSA key) must be available
- The same IKE version must be used
Remote Gateway step 3
- As Local Gateway ID the Remote Gateway ID from step 4 of the first UTM must now be used
- Under Share Networks the (there remote) network from step 4 of the first UTM must also be used
Remote Gateway step 4
- The public IP address (or a hostname that can be resolved via DNS) of the first UTM must be entered as Remote Gateway.
(This address was not required in the wizard of the first UTM). - The Local Gateway ID from step 3 of the first UTM must be used as Remote Gateway ID
- Under Share networks the (there local) network from step 3 of the first UTM must also be used.
Create network object of the remote gateway
- The network object of the remote gateway represents the network of the first UTM.
Correspondingly, the network address of the local network of the first UTM must be entered under Address.
In the example 192.168.218.0/24
Notes
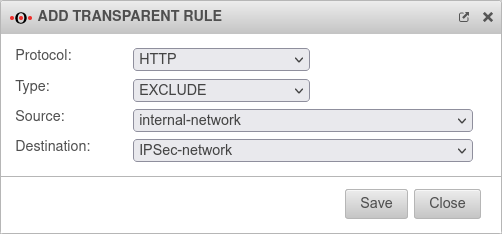
The transparent HTTP proxy
If a server behind the Site-to-Site connection is to be accessed from the internal network via HTTP, the transparent HTTP proxy may filter the packets.
This can lead to errors while accessing the target.
To prevent this from happening, a rule Exclude must be created in the Tab Transparent mode Button menu with source internal-network to target name-vpn-network-object and protocol HTTP.
Troubleshooting
Detailed Troubleshooting instructions can be found in the Troubleshooting Guide