|
Add rules for Securepoint Antivirus Pro
|
| Caption |
Value |
Description
|
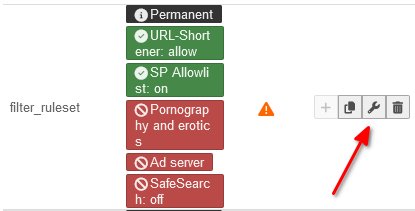
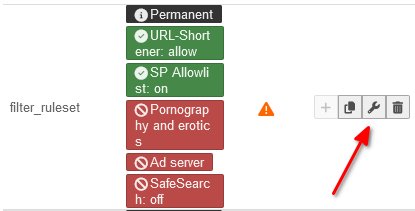 Edit rule set
|
|
Edit |
Click the corresponding button to edit the rule set
|
|
|
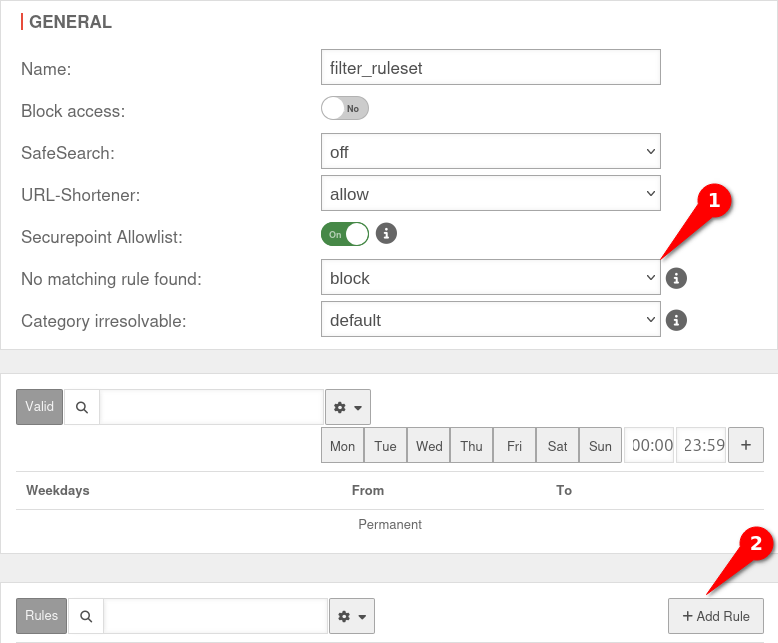
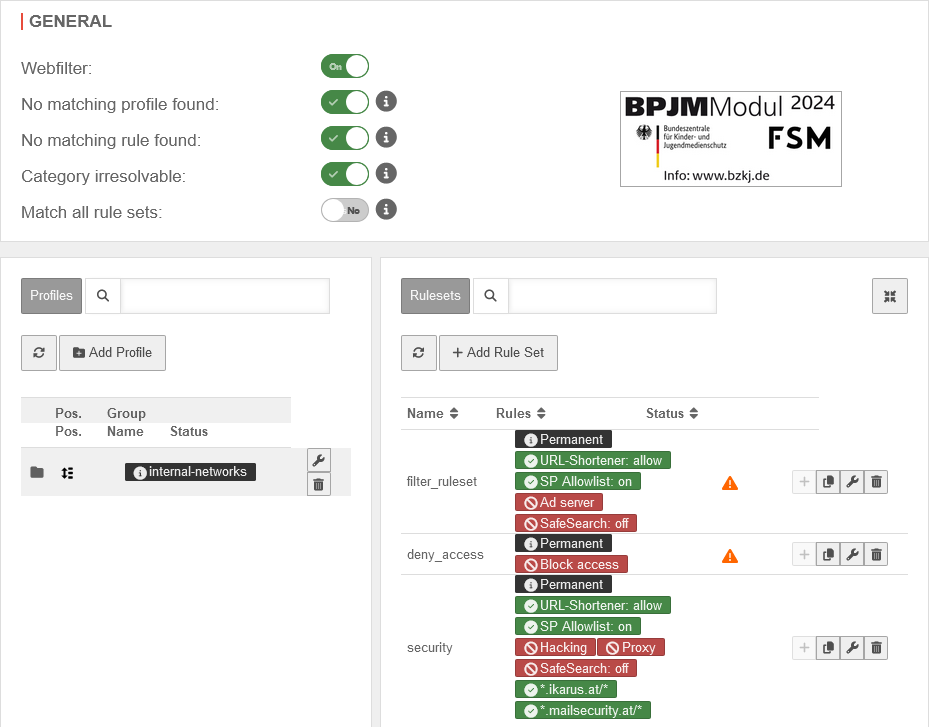
General
|
| No matching rule found |
block |
Select "Block"
|
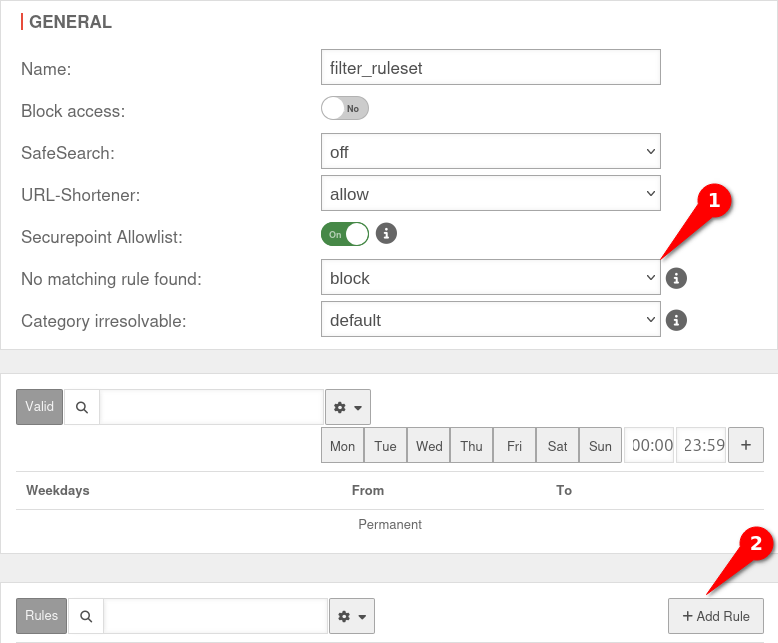 Edit rule set for Securepoint Antivirus Edit rule set for Securepoint Antivirus
|
|
+ Add rule |
Click the button to add a rule. 2
A new window opens with the message
|
|
|
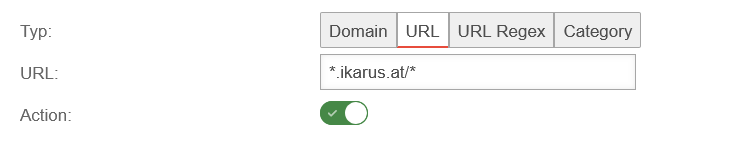
| Type: |
URL |
Select URL as the rule type
|
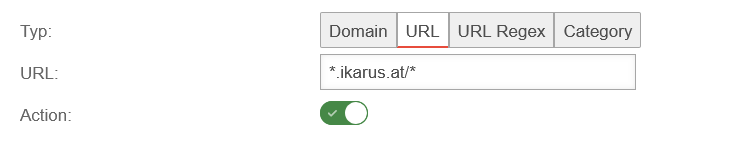 Add URL Add URL
|
| URL |
*.ikarus.at/* |
Add the following URL: *.ikarus.at/*
|
| Action |
|
Allow action
|
|
Save |
Save URL
|
| URL |
*.mailsecurity.at/* |
Add the following URL: *.mailsecurity.at/*
|
| Action |
|
Allow action
|
|
Save and close |
Save URL and close the dialog
|
notemptyFor the rule set to be applied, the rule set must be assigned to a profile that contains the corresponding computer!
|
|
|
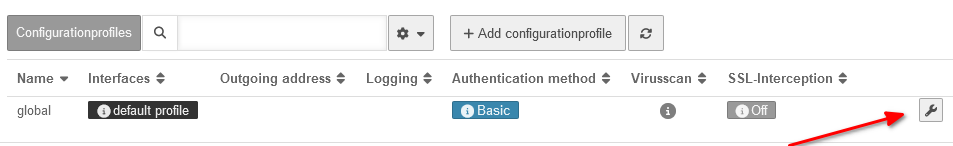
Virus scanner of the UTM
Call in menu
|
The virus scanner of the HTTP proxy already includes exceptions for ikarus.at and mailsecurity.at in the default profile.
If these have been deleted, you can assign the rules either to the default profile or to another configuration profile.
^[^:]*://[^\.]*\.ikarus\.at/
^[^:]*://[^\.]*\.mailsecurity\.at/
|
|
Edit |
Edit configuration profile / global configuration profile
|
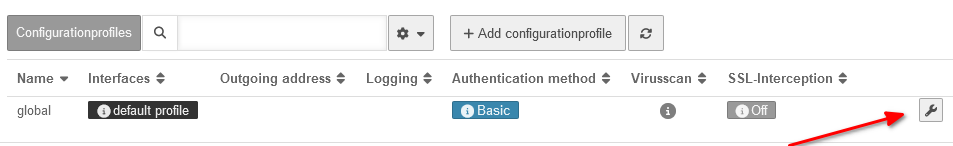 Edit a profile Edit a profile
|
| If the exceptions are restored in the standard profile, they will also apply to any additional configuration profiles you have created yourself.
If the exceptions are only to apply to one additional configuration profile (or several profiles), then insert the exceptions there.
|
|
|
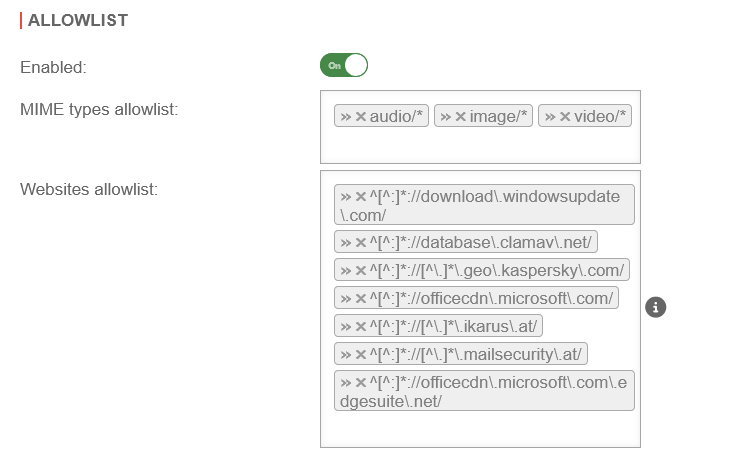
Virus scanner
Allowlist
|
| Website-Allowlist: |
^[^:]*://[^\.]*\.ikarus\.at/ |
Add exceptions for ikarus and mailsecurity
|
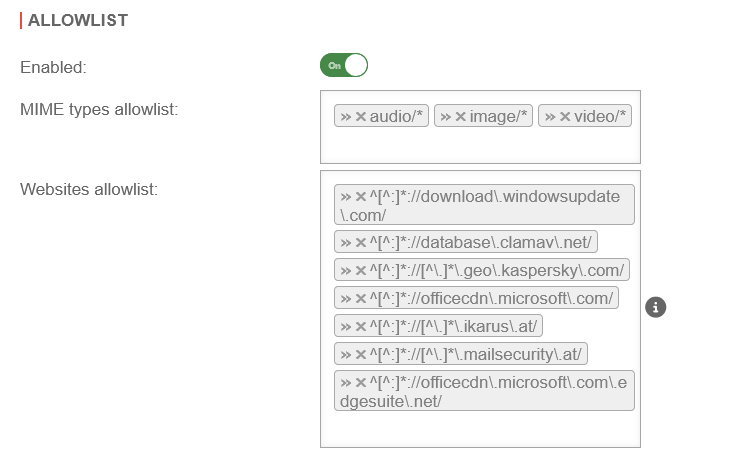 Add rules for the virus scanner Add rules for the virus scanner
|
| ^[^:]*://[^\.]*\.mailsecurity\.at/
|
|
|
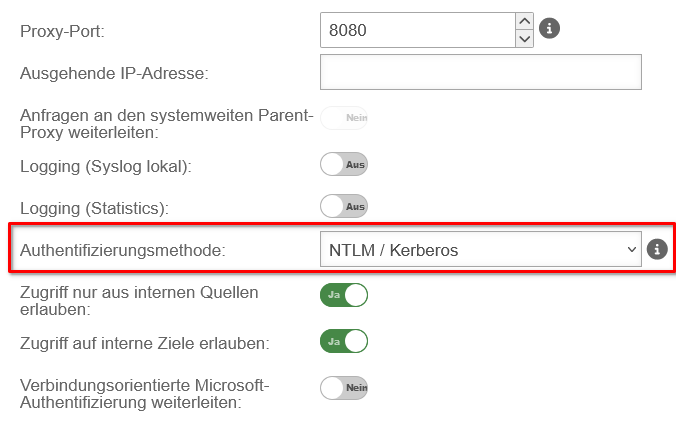
Scenario 2: Standard proxy with authentication
Call in menu Area General
|
To increase security, you can select an authentication method in the Securepoint NextGen UTM firewall.
|
| Authentication method: |
Basic |
With basic authentication, the users are queried against the stored users under Area User on the firewall
|
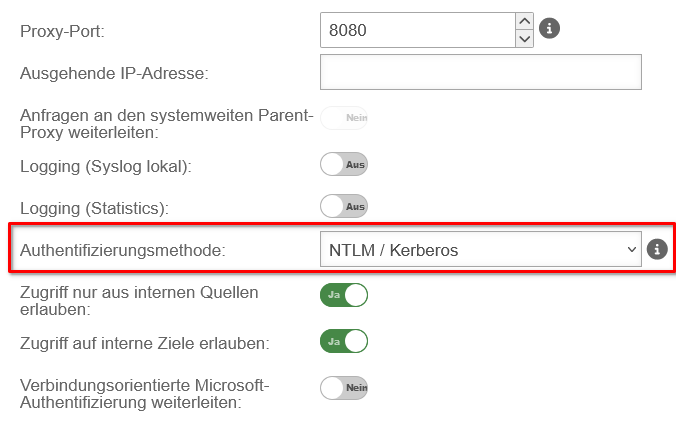 Select an authentication method
|
| NTLM/Kerberos |
Here the firewall must be made known to the server.
This can be set up in the web interface under
|
| Radius |
Here the firewall must be made known to the server.
This can be set up in the web interface under
|
|
|
Authentication exception
|
| Since the Securepoint Antivirus client cannot authenticate itself against the proxy with NTLM, additional 'authentication exceptions are required.
The exceptions for ikarus and mailsecurity are already present by default. They are accessed after activating the authentication exceptions On
If they have been deleted, they must be added again.
|
| Enabled: |
On |
Authentication exceptions must be enabled
|
 Authentication exceptions for ikarus and mailsecurity
|
| Exceptions (URL): |
\.ikarus\.at
\.mailsecurity\.at |
Add exceptions for ikarus and mailsecurity
|
|
|
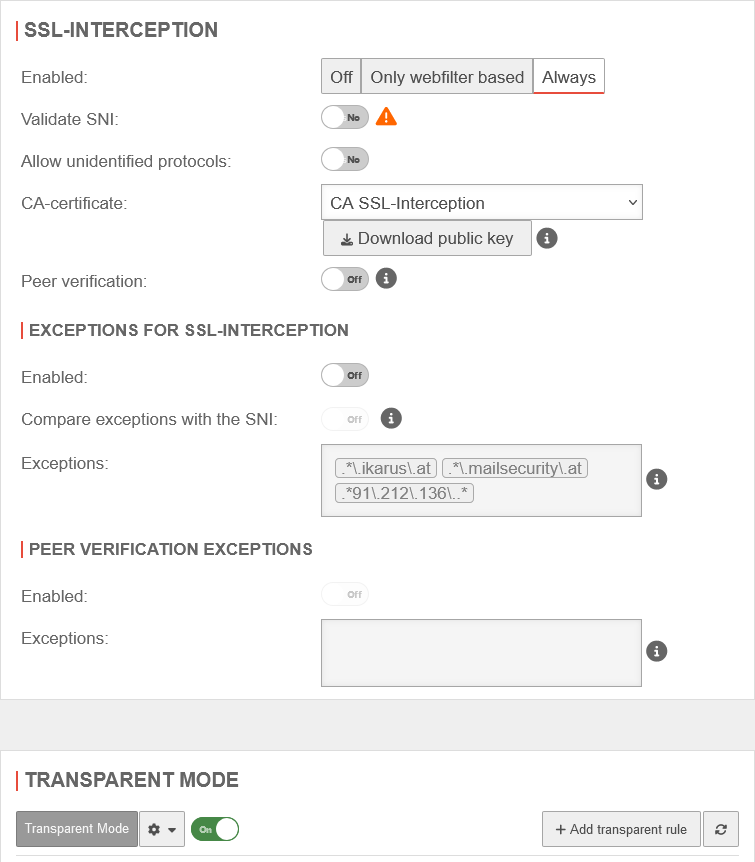
Scenario 3: Standard proxy with authentication via NTLM and with SSL interception
|
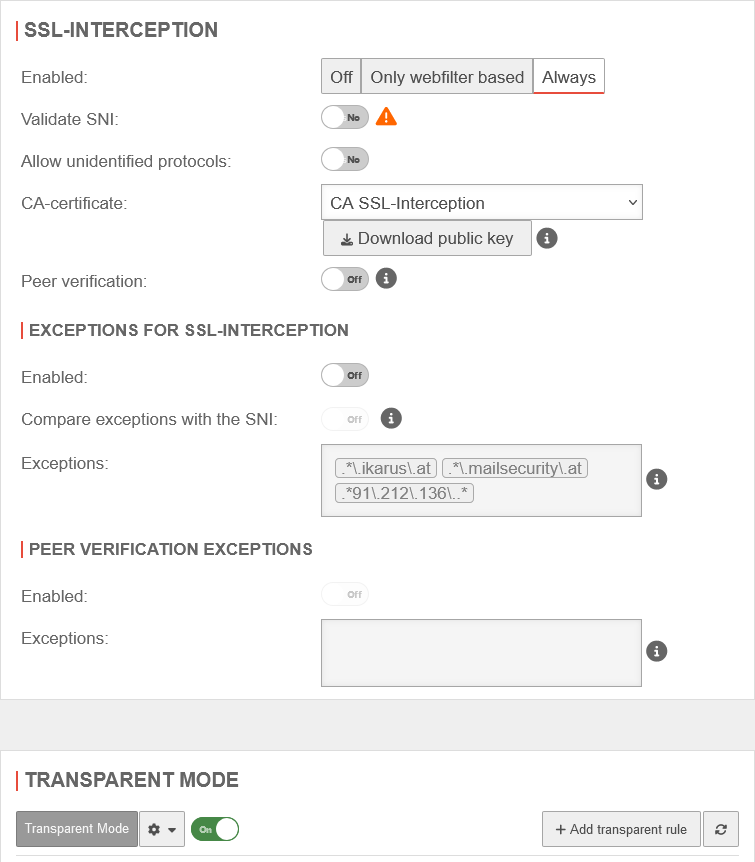
SSL-Interception
|
| Both for SSL interception and Transparent Mode, the exceptions for SSL interception are already configured system-wide. They take effect when SSL interception and Transparent Mode are activated.
If they are no longer present, add them manually
|
| Enabled: |
Always |
SSL interception has been activated
|
|
|
|
Exceptions for SSL interception
|
|
|
| Exceptions: |
.*\.ikarus\.at |
Add exceptions for ikarus and mailsecurity
|
| .*\.mailsecurity\.at
|
| .*91\.212\.136\..* |
Release of server IP addresses for Transparent Mode
|
|
|
Transparent Mode
|
|
|
|
On |
Transparent Mode is active.
|
|
|
 The UTM Web Filter
The UTM Web Filter