In dieser Seite werden die Variablen für unterschiedliche Sprachen definiert.
Diese Seite wird auf folgenden Seiten eingebunden
Configuration of a UTM when using a HTTP proxy and Securepoint Antivirus Pro
New:
notemptyThis article refers to a Beta version
Introduction
Securepoint Antivirus Pro regularly checks for new updates and downloads them.
Please note the following:
- With a direct Internet connection of a Windows client, this is not a problem because there are normally no rules for regulating website calls
- In a network environment, on the other hand, workstations usually have ‘'no’' direct Internet access.
The data traffic is filtered via packet filters and proxies.
This offers malware as little attack surface as possible.
notemptyWith a good firewall configuration, each client only gets the permissions it really needs.
This article presents three scenarios that allow the Antivirus Pro update via the HTTP proxy of a Securepoint NextGen UTM firewall and the web filter.
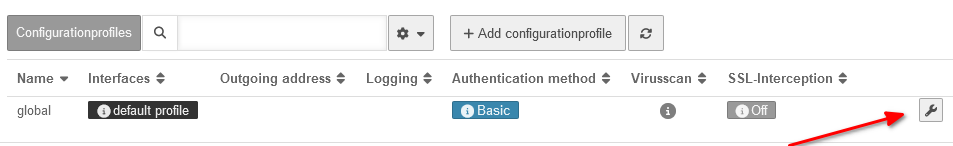
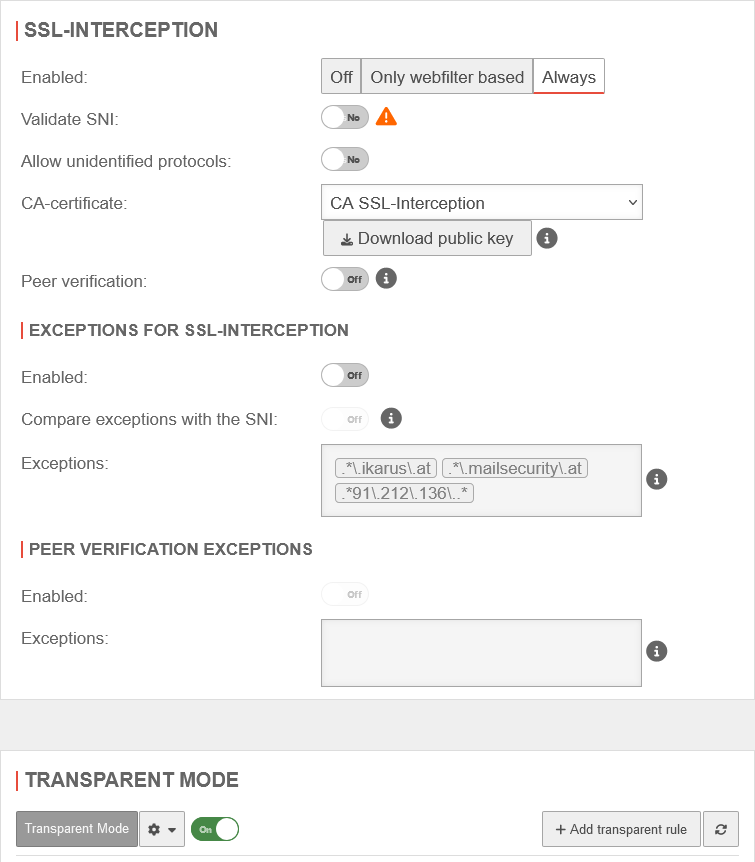
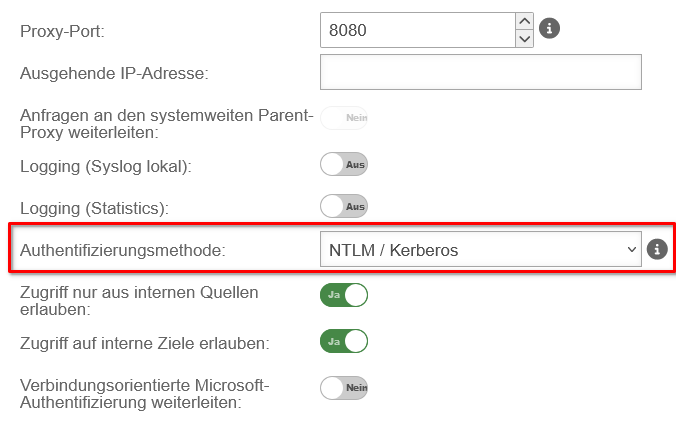
Scenario 1: Standard proxy without authentication
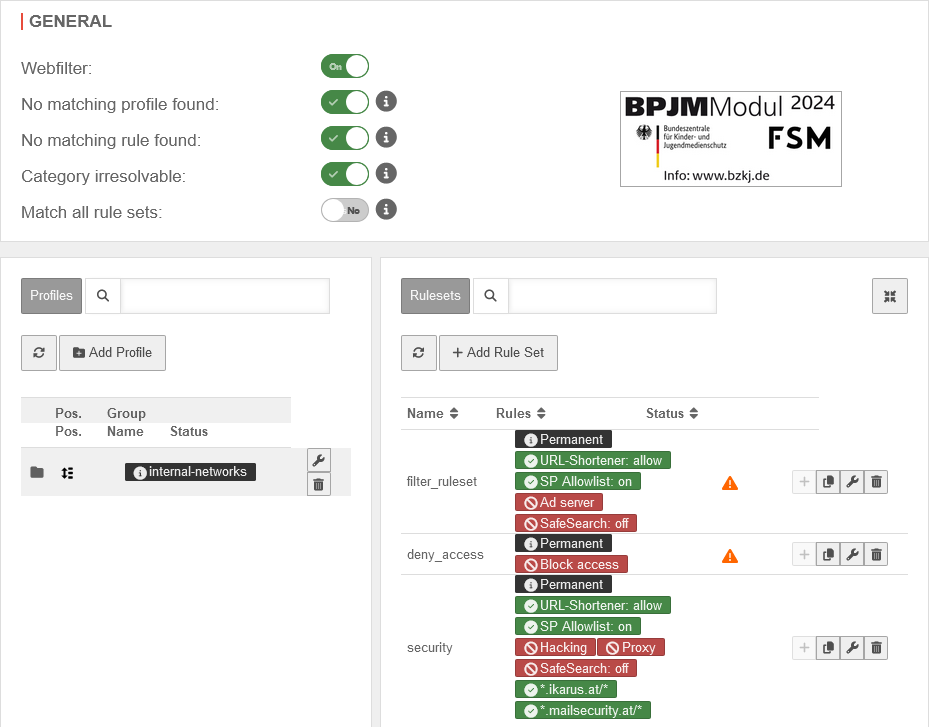
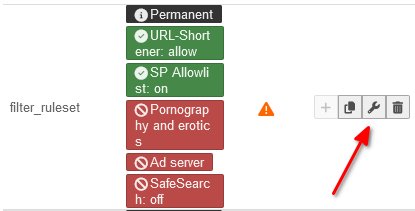
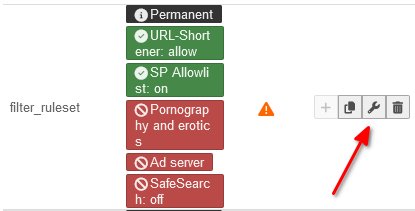
Webfilter
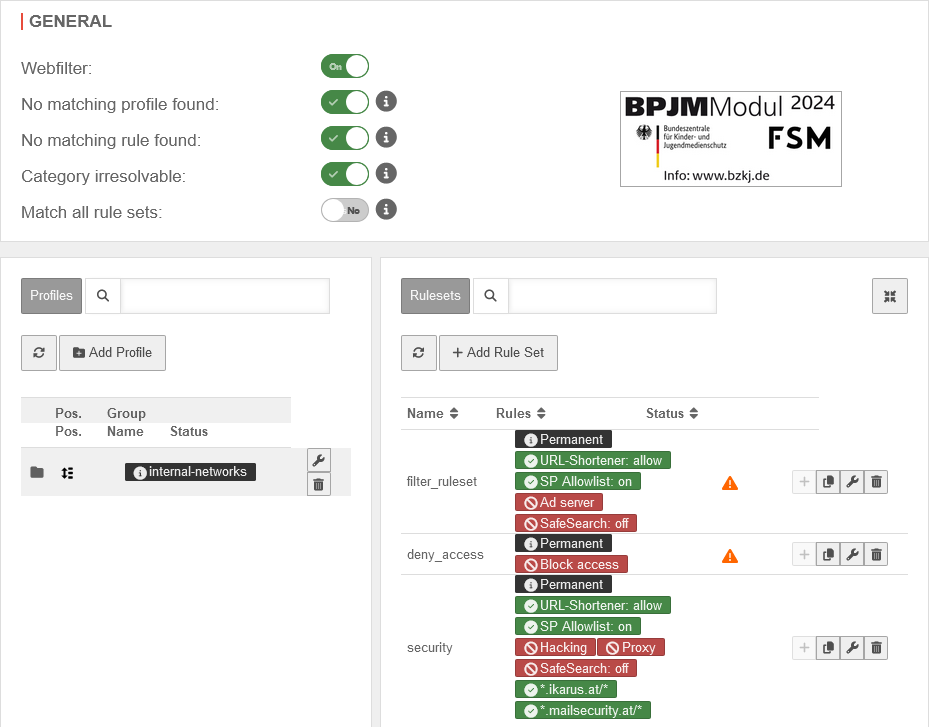
Call in menu
In this case, the HTTP proxy is used in Transparent mode.
In the
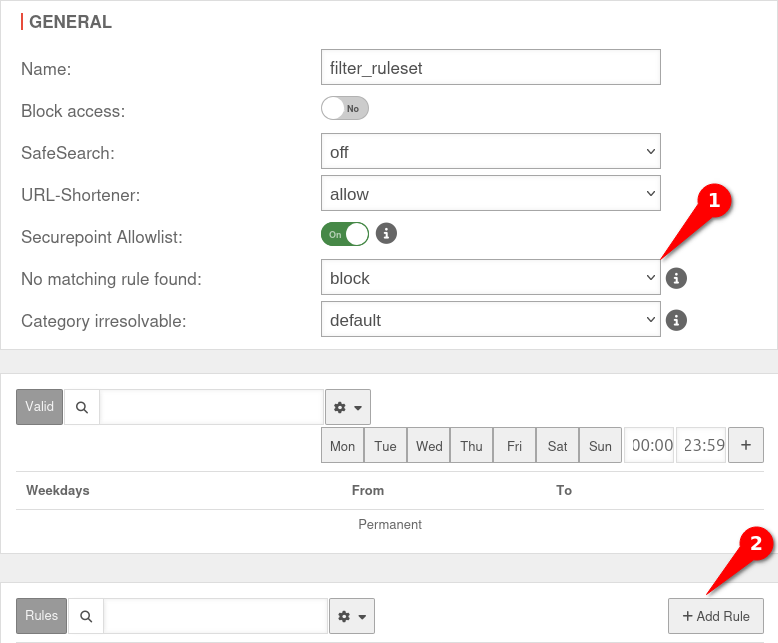
Webfilter, only the websites required for communication are enabled.
Each Securepoint Antivirus Pro user must be included in a rule set that enables the Securepoint Antivirus Pro update servers.
|
|
| Caption |
Value |
Description
|
|
|
|
|
|
|
|
|
|
|
|
|
|
+ |
|
|
|
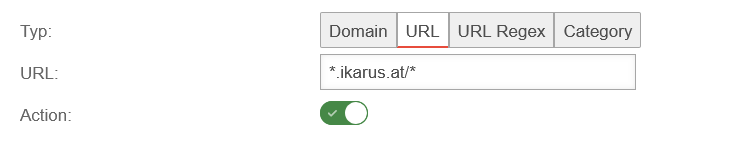
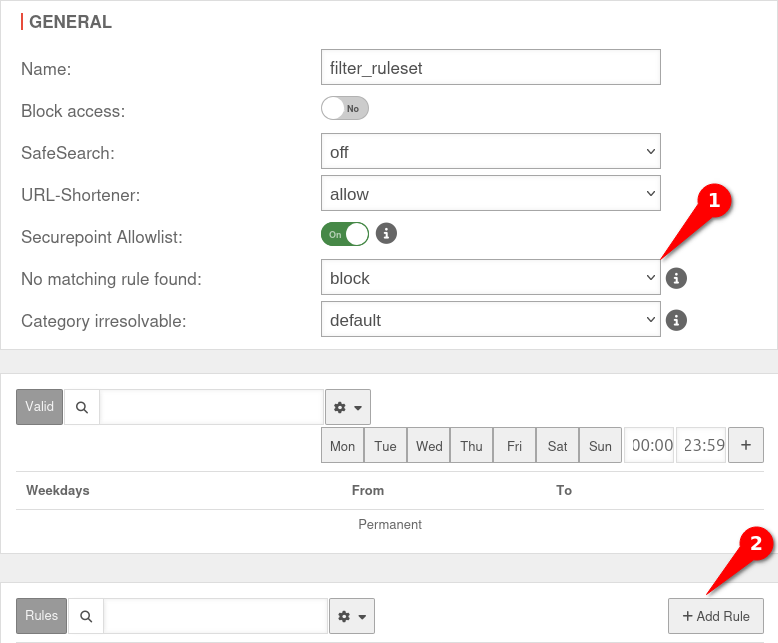
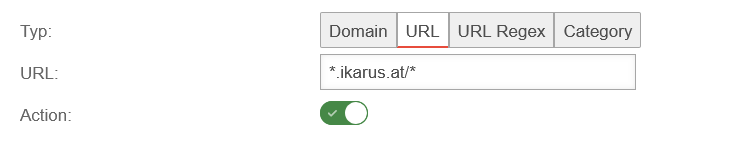
| Type: |
URL |
Select URL as the rule type
|
|
| URL |
*.ikarus.at/* |
: *.ikarus.at/*
|
|
|
|
|
|
|
| URL |
*.mailsecurity.at/* |
: *.mailsecurity.at/*
|
|
|
|
|
|
|
| notemptyFor the rule set to be applied, the rule set must be assigned to a profile that contains the corresponding computer!
|
|
|
Virus scanner of the UTM
Call in menu
|
^[^:]*://[^\.]*\.ikarus\.at/
^[^:]*://[^\.]*\.mailsecurity\.at/
|
|
|
|
|
|
|
|
|
Allowlist
|
| : |
^[^:]*://[^\.]*\.ikarus\.at/ |
|
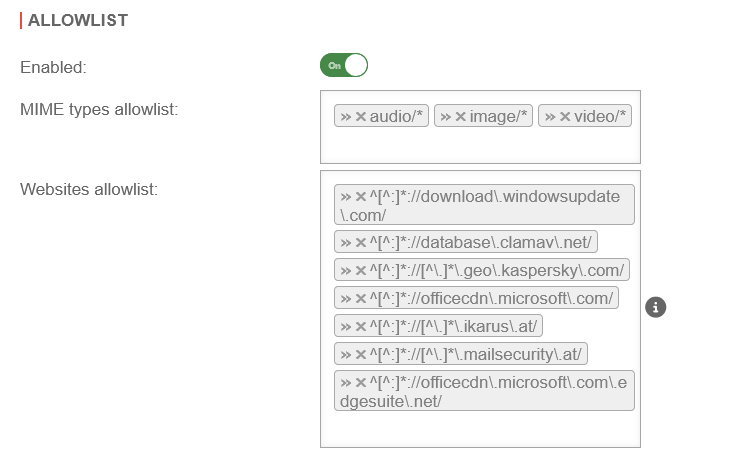
|
| ^[^:]*://[^\.]*\.mailsecurity\.at/
|
|
|
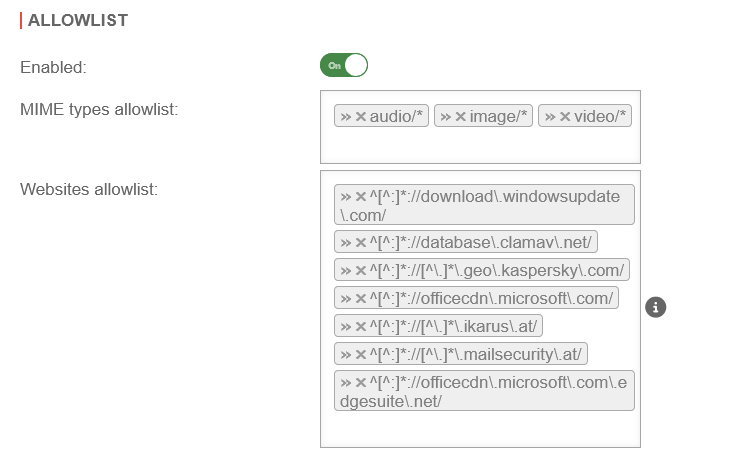
Scenario 2: Standard proxy with authentication
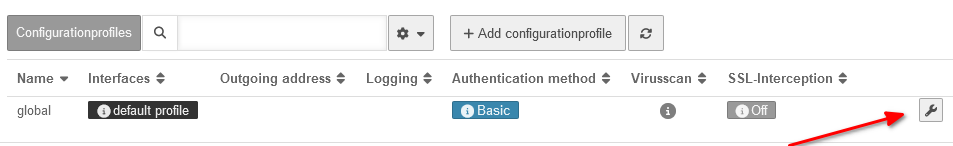
Call in menu Area General
|
|
- || Basic || With basic authentication, the users are queried against the stored users under Area User on the firewall
|
|
| NTLM/Kerberos |
Here the firewall must be made known to the server.
This can be set up in the web interface under
|
| Radius |
Here the firewall must be made known to the server.
This can be set up in the web interface under
|
|
|
Authentication exception
|
| Since the Securepoint Antivirus client cannot authenticate itself against the proxy with NTLM, additional 'authentication exceptions are required.
The exceptions for ikarus and mailsecurity are already present by default. They are accessed after activating the authentication exceptions Ein
If they have been deleted, they must be added again.
|
- || Ein ||
|

|
- || \.ikarus\.at
\.mailsecurity\.at ||
|
|
|
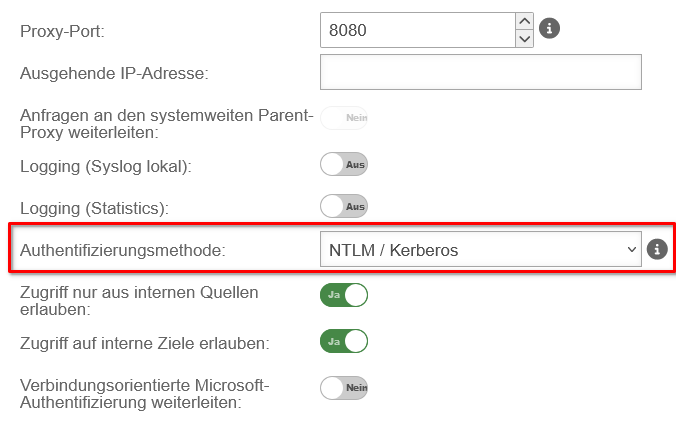
Scenario 3: Standard proxy with authentication via NTLM and with SSL interception
|
SSL-Interception
|
|
|
- || ||
|
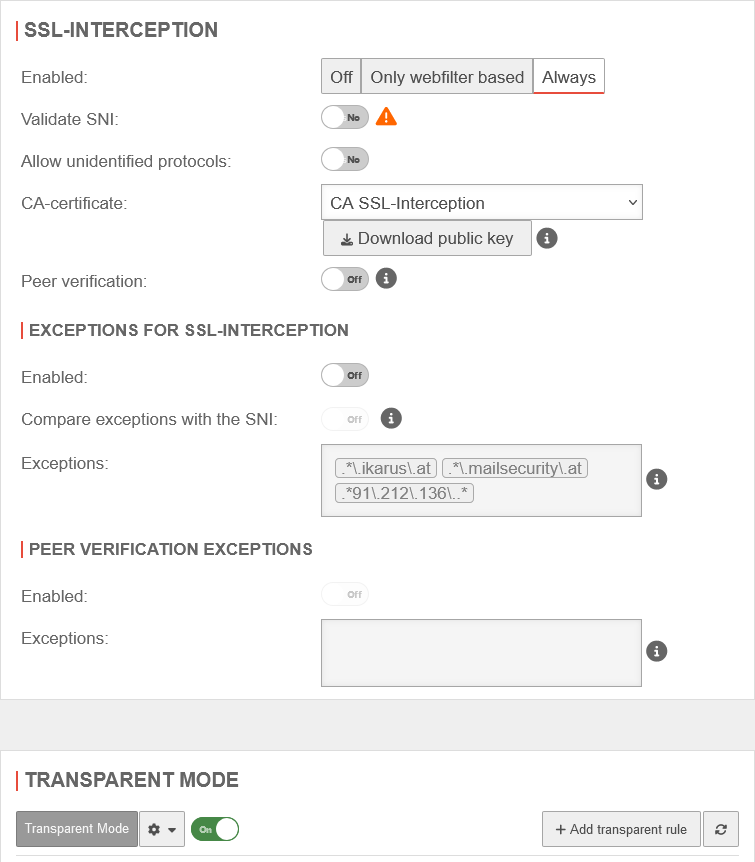
|
|
|
|
|
|
- || .*\.ikarus\.at || rowspan=2 |
|
| .*\.mailsecurity\.at
|
| .*91\.212\.136\..* |
|
|
|
|
|
|
|
Ein |
|
|
|