Configuration of the SSL interception in the HTTP proxy
Last adaptation to the version: 14.1.2 (02.2026)
New:
- BetaFor participants on the Beta Channel only:
- (v14.1.1)
- Updated to Redesign of the webinterface
notemptyThis article refers to a Beta version
Part of the HTTP-Proxy
notemptySupport for certificates with a key length of 1024 bits or less will be removed starting with UTM version 14.2.
Support for certificates with the SHA1 signing algorithm will also be removed starting with version 14.2.
HTTP proxy or SSL VPN connections with such outdated certificates will no longer work as of v14.2!
Insecure certificates should be replaced urgently!
The BSI recommends—as of January 2025—key lengths of 3000 bits or more and SHA256
BSI – Technical Guideline – Cryptographic Methods: Recommendations and Key Lengths BSI TR-02102-1 | Chapter 2.3: RSA encryption
OpenVPN
Mailrelay
Reverse-Proxy
Webserver
HTTP-Proxy
The BSI recommends—as of January 2025—key lengths of 3000 bits or more and SHA256
BSI – Technical Guideline – Cryptographic Methods: Recommendations and Key Lengths BSI TR-02102-1 | Chapter 2.3: RSA encryption
The default setting of the UTM for new certificates is RSA encryption with 3072 bits and SHA256 as the hash algorithm
SSL-Interception
| Caption | Value | Description | 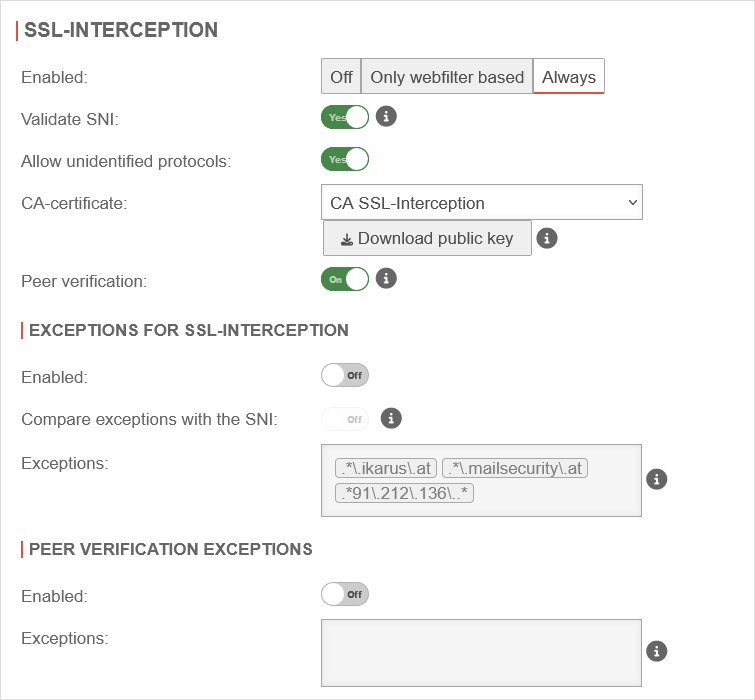 SSL Interception tab SSL Interception tab
|
|---|---|---|---|
| Enabled | The SSL-Interception is turned off | ||
| When enabled, only connections blocked by the web filter are intercepted. This avoids the problem that there are sites that do not tolerate an interruption of the encryption (e.g. banking software) without having to define an exception for it. | |||
| Activates the SSL interception | |||
| Validate SNI: Only in the global configuration profile Is inherited by additional configuration profiles |
Yes | When activated, any SNI in the ClientHello of the TLS handshake is checked. The host name contained is resolved and the addresses in the result are compared with the target address of the intercepted request. If they do not match, the connection is closed. Without Server Name Indication validation, clients can manipulate SNI arbitrarily to bypass the web filter. This setting should only be considered as a last resort when it seems impossible to standardize the DNS settings between the HTTP proxy and the UTM clients. If the client and UTM use different DNS servers, this can lead to false positives. | |
| Allow non identified protocols: | Yes | If this switch is deactivated, unrecognized protocols are blocked. | |
| CA-Certificate: | CA-SSL-Interception | Here, a CA must be selected that can re-encrypt the connection after decryption (and scanning). The public key of the CA must be installed on all client computers that are to use SSL Interception. Download can be done here directly with .
notempty
| |
| The public key should be installed on the clients that are going to use SSL interception to avoid certificate errors. | |||
| Peer verification: not for Only webfilter based Only in the global configuration profile Is inherited by additional configuration profiles |
On | This should definitely be enabled! With this, the HTTP proxy checks whether the certificate of the called page is trustworthy. Since the browser only sees the local certificate, a check by the browser is no longer possible. | |
Exceptions for SSL-Interception Exceptions for SSL-Interception not for Only webfilter based | |||
| Enabled | Off | It is possible to define exceptions in the format of Regular Expressions. However, since only https can arrive here, it is not filtered for protocols, unlike the virus scanner. New exceptions can be added directly in the input field. So an exception for www.securepoint.de would be:
.*\.securepoint\.de" | |
| Compare exceptions with the SNI: Only available if salidate SNI is active. |
Off | Applies Server Name Indication validation only to activated Exceptions of SSL-Interception . | |
| Exceptions: | .*\.ttt-point\.de Predefined in the Global Configuration Profile .*\.ikarus\.at.*\.mailsecurity\.at .*91\.212\.136\..* |
Define exceptions here for ttt-point.de | |
Peer verification exceptions Peer verification exceptions only if peer verification is active | |||
| Enabled | Off | Here exceptions for certificate verification in regex format can be added.
| |



