Last adaptation to the version: 12.7
- Updated to Redesign of the webinterface
- 14.1.1
- New options for moving elements now available
Specifications
Option 1: User groups
For the example scenario, there are specifications for three user groups.
- Each user group has its own set of rules
- Different permissions are required when accessing the website
Based on the user groups, three profiles are created in the web filter and linked to their respective sets of rules.
- User group Proxy_boss: No restrictions.
However, management should be protected from websites containing malware. - The user group Proxy_employees should also be protected from malware.
In addition, the following categories should be blocked:- Pornography and erotica
- Social networks and
- Shopping
However, it must be possible to shop online at Anyideas GmbH.
- Only the Securepoint website should be available to the user group Proxy_trainee.
In addition, trainees should be able to use Instagram during a specific time window.
Option 2: Network groups
Network groups are assigned to rule sets in profiles.
They are designed to protect non-authenticated devices via HTTP proxy and the web filter.
A distinction is made between three network groups:
- Network group nw_grp_GF: For management devices with the IP network 10.1.10.0/24
- Network group nw_grp_IT: For IT devices with the IP network 10.1.20.0/24
- Network group nw_grp_VT: For sales devices with the IP network 10.1.30.0/24
- All network groups should be protected against malware
- For sales, advertising services should also be blocked
Setting up the groups
Option 1: User groups
Call in menu Area Groups button Area Permissions
UTMuser@firewall.name.fqdn Authentication User
| Caption | Value | Description |
|---|---|---|
| Group name | Proxy_boss | Unique name for the user group |
| HTTP-Proxy | On | The web filter requires the HTTP proxy permission |
Create gropus
UTMuser@firewall.name.fqdn Authentication
Now create a separate user group for
- Proxy_boss
- Proxy_employees and
- Proxy_trainee
Create user
Call in menu Area Users Area General
If authentication does not take place via Active Directory, local users are required.
They should inherit the permissions from the user groups.

| Caption | Value | Description |
|---|---|---|
| Login name: | Emploeyees | Create users, such as employees |
| Password | ••••••••••••••••••• | Enter a secure password |
| Confirm password | ••••••••••••••••••• | Re-enter password |
| Expiration date | 2024-11-07 12:00:00 | Optional: Assign expiration date |
| Groups | Proxy_employees | Select the appropriate option in the Groups click box |
| Finally save and close |
Section User

Now we still need the users Boss and Trainee.
Option 2: Networkgroups

Network groups can also be used as an alternative to user groups.
To do this, create network objects and link them to the network groups.
Setting up the web filter
Create profile
Call in menu Profiles
The created groups are linked to the rule sets in order to set up a web filter.
To do this, profiles are created.

| Caption | Value | Description |
|---|---|---|
| Network or user group | Proxy_boss | Select one of the created network or user groups, such as Proxy_boss. |
| Generate new rule set | Leave set to Allow | |
| The new profile is created by clicking Save and Close. |

In this way, a profile is created for each of the network or user groups.
Rule sets
- Proxy_trainee_ruleset_1
- Proxy_employee_ruleset_1
- Proxy_boss_ruleset_1
| Area | button/Value | Description |
|---|---|---|
| Rule sets | The button opens a new dialog box for editing a rule set. | |
| Clicking on the button opens another dialog box.
Here you can block or allow
| ||
| | | By default, the respective action is blocked.
Clicking on the button allows it. |
Rule set for user group Proxy_boss
Default settings for user group Proxy_boss UTMuser@firewall.name.fqdn Applications Webfilter Edit rule set
- Edit rule set and create rule: Type Hacking
| Description | |
|---|---|
| Edit rule set and open a new dialog box | |
| Click on the button | |
| class=aktiv | Choose type |
| Hacking | Select category |
| Set action (default: block) | |
| Save rule |
- Create another rule with Threat Intelligence Feed
Alternative to creating a new rule set: copy an existing one.
Advantage: Significantly reduces the amount of work required if it already contains all or some of the desired categories, URL regex, etc.
For example, the predefined rule set “security” blocks websites from the categories Hacking and Threat Intelligence Feed.
- Copy rule set security and assign it to Proxy_boss:
| Description | |
|---|---|
| Copy rule set | |
| Modify copied rule set | A new dialog box will open. Rename the rule set to Proxy_chef_ruleset_1. Optional: Further customize the rule set |
| Save the copied rule set and close the dialog box. | |
| Click on the button. A new dialog box opens | |
| Proxy chef | Select network or user group |
| Click on the button | |
| This button appears. It does not create a rule set. | |
| Proxy_chef_ruleset1 | Select copied rule set |
| Save and add profile |
Default set for user group Proxy_employees
Default settings for user group Proxy_employeesFor the rule set of the user group Proxy_employees, copy the rule set security to protect against malware.
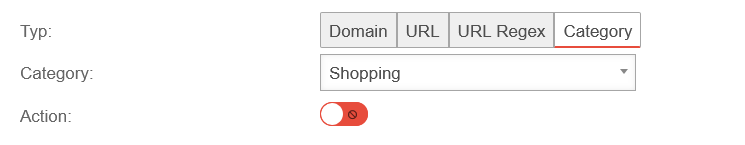
Rules are established for
- Shopping
- Pornography and erotica
- Social networks and
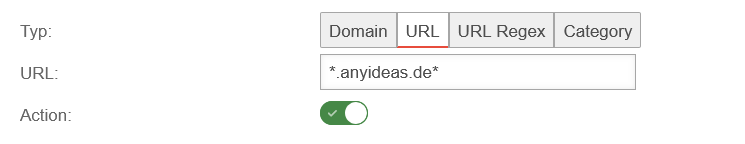
- the special case of shopping at Anyideas GmbH using wildcards
| Description | |
|---|---|
| Edit rule set and open a new dialog box | |
| Click on the button | |
| Choose type | |
| Shopping | Select category |
| Block | |
| Save rule | |
| Block pornography and erotica and social networks in the same way | |
| Choose type | |
| URL | Place a wildcard * before and after anyideas.de (allows all subdomains and paths on the website) |
| Permit | |
| Save and close | |
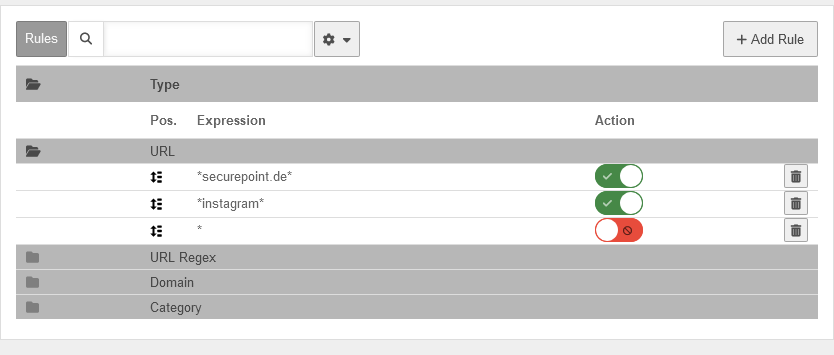
Default setting for the user group Proxy_trainee
Default setting for the user groupThe user group Proxy_trainee is a special case.
- Trainees should only be allowed to use Instagram within a clearly defined time frame
- All other URLs should be blocked without exception
- Exception: The Securepoint website should be accessible at all times (and is therefore required in every rule set)
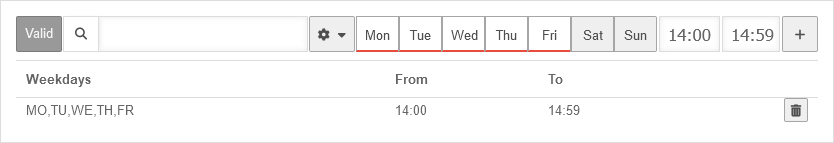
Therefore, two sets of rules are required:
- One for the time component (Monday - Friday from 14:00 - 14:59)
- Another one that applies outside the specified time frame
Important:
- All rule sets must be fully configured
- Processing is not top-down, meaning one rule set is implemented after the other
- It is only checked whether the time matches a rule set or not
Procedure
- Create rule set 1 for Proxy_trainee:
- Rule 1: Allow the URL securepoint.de
- Rule 2: Block all other URLs
- Copy rule set - saves time:
- Rename new rule set
- Specify timeframe
- Create URL rule for Instagram
- Drag and drop rule set 2 in front of rule set 1 and save
Schritt-für-Schritt-Anleitung
Step 1: Create rule set 1

| Area | button/Value | Description |
|---|---|---|
| Profiles | Click on the button and open a new dialog | |
| Proxy_trainee | Select user group Proxy_azubi | |
| Generate a new rule set and create the rule set Proxy_trainee_ruleset_1. | ||
| Save and close the dialog | ||
| Rule sets | Proxy_trainee_ruleset_1' | Edit rule set and open a new dialog box |
| Rules | Click on the button and open a new dialog | |
| Choose type | ||
| URL | Enter securepoint.de | |
| Permit | ||
| Save rule | ||
| * | Enter wildcard | |
| Block | ||
| Save and close the dialog | ||
| Save again and finish editing the rule set |
Step 2: Copy and extend rule set 1
| Area | button/Value | Description |
|---|---|---|
| Rule sets | Proxy_trainee_ruleset_1' |
Click on the button, copy the rule set and open a new dialog |
| Name: | Rename to Proxy_trainee_ruleset_2 | |
Define time frame: Mon-Fri 2:00 p.m. - 2:59 p.m.
For multiple entries: Their display in the table can be customized as described in the article on the UTM toolbar | ||
| Click the button and add the time frame to the rule set | ||
| Rules | Click on the button and open a new dialog | |
| Choose type | ||
| URL | *instagram* → The flexible URL rule with wildcards allows
| |
| Allow action | ||
| Save and close the dialog | ||
| Rules | URL notempty Additional options available by right-clicking on the icon New as of v14.1.1 |
Move the Instagram rule in front of the wildcard rule via drag and drop |
| Save and close. | ||
| Rule sets | Proxy_trainee_ruleset_2 | After saving, an exclamation mark appears next to the rule set because: The rule set
|
| Profiles |
Proxy_trainee | Mark with the mouse |
| Rule sets | Proxy_trainee_ruleset_2 | Click the button and link the rule set to the profile Proxy_trainee |
Step 3: Move rule set
The rule sets for the network groups are set up in the same way as the Defaults mentioned above.
Wildcards
Wildcards can be used very flexibly.
Here are a few examples:
| Wildcard examples | Description |
|---|---|
| *ttt-point* | Allows all characters before and after ttt-point
Examples:
|
| *.ttt-point.* | Allows any number of characters before and after the string .ttt-point.. Unlike the first example, this specification is a little more restrictive. It requires a period before and after ttt-point. |
| *ttt-point․de (or .net, .com etc.) | Any characters are permitted before ttt-point․de in unlimited numbers. However, no further characters are permitted after the country domain de. The result: potential subdirectories on the respective server cannot be accessed. |
| https://*ttt-point․de* | All characters after https:// are permitted, provided that they are followed by ttt-point․de. Any other characters may follow ttt-point․de |
| https://*ttt-point․* | The same specifications as in the previous example, except that all domain extensions such as .com, .fr or .site are permitted. |
| https://ttt-point․de* | Only allows addresses that begin with https://ttt-point.com.
Examples of blocked addresses:
Any number of characters can follow the domain extension. |
| https://ttt-point․de | Allows only the address <nowiki>https://ttt-point.de (no additional subdomains, etc.). |
Enable web filter
Section General

| Area | Button/Value | Description |
|---|---|---|
| Web filter | Check whether the web filter is still enabled (UTM factory setting) | |
| No matching profile found | By default, the web filter also accepts network and user groups
| |
If you enable blocking, any user will be blocked
| ||
| Save configuration after modifications |
Set up HTTP-proxy
Call in the menu

Authentication for proxy user groups is required in the UTM.
To do this, select the appropriate authentication method in the HTTP proxy.
Please note:
- For the Basic authentication method, users are required on the UTM.
- For NTLM, the UTM must first be integrated into the domain.
Transparent mode
Area Transparent Mode Button
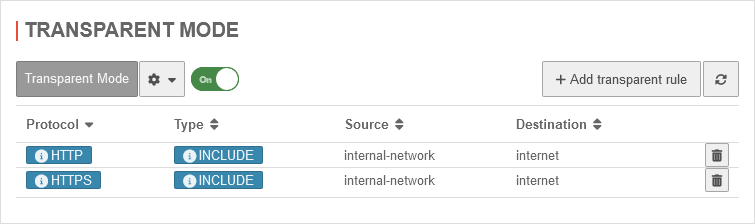
Network group users are controlled via the proxy's transparent mode.
Members of network groups with the Internet destination should always be redirected via the HTTP proxy for HTTPS using the include type.
Appropriate rules are created for this purpose.

| Area | Button/Value | Description |
|---|---|---|
| Protocol: | HTTPS | Select protocol HTTPS |
| Type: | INCLUDE | Set type to INCLUDE |
| Source: | nw_grp_GF | Define nw_grp_GF as source |
| Target: | internet | Select internet as target |
| Save and close |
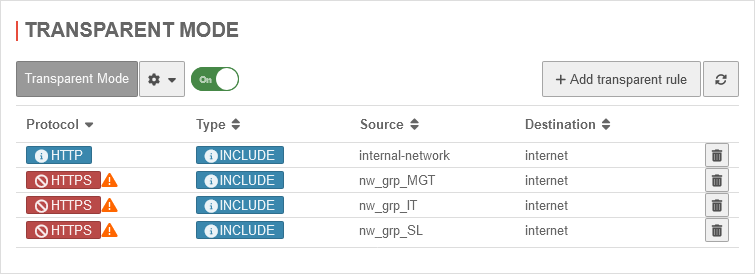
The rules are only applied if SSL Interception is enabled.
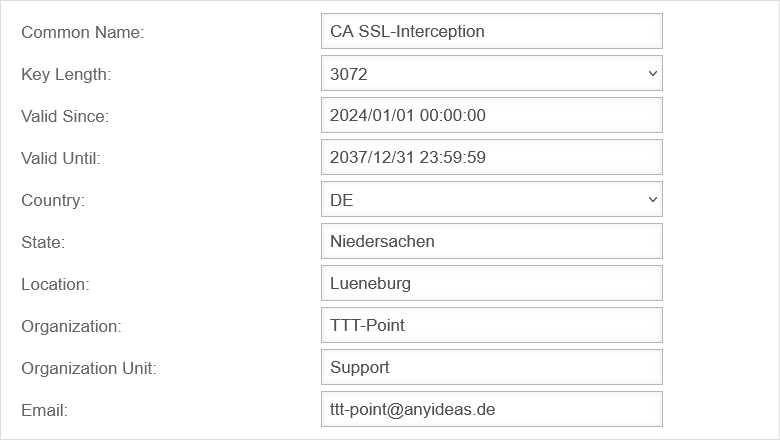
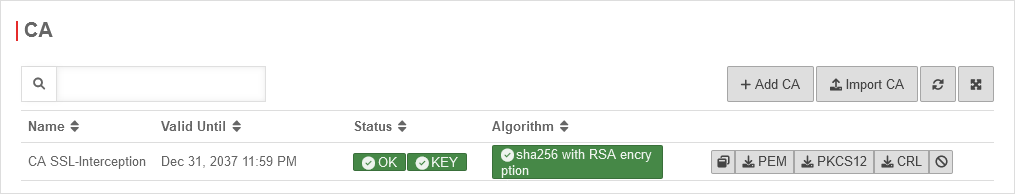
SSL-Interception
The CA certificate's public key must then be stored in the certificate management of the client browsers.
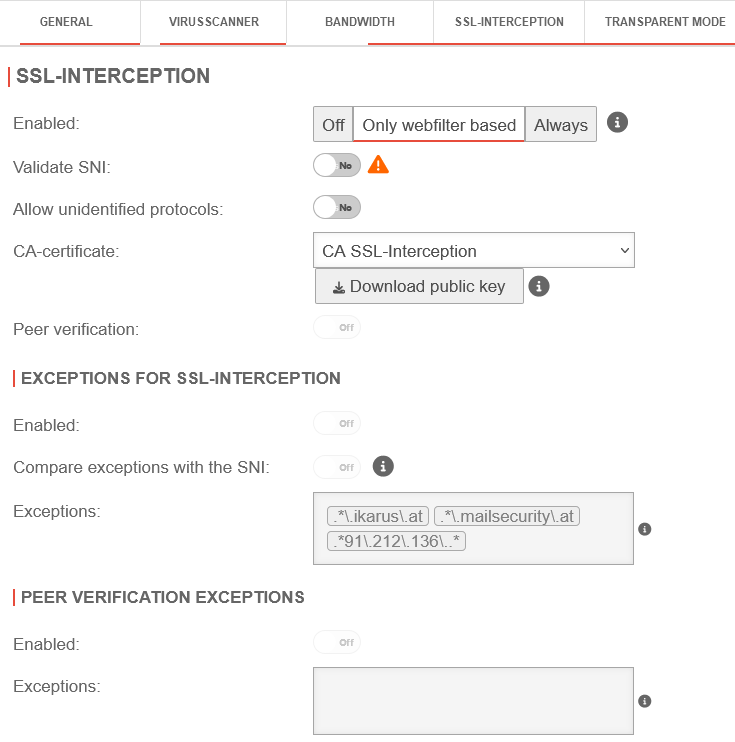
| Area | Button/Value | Description |
|---|---|---|
| Enabled: | oder |
Specify whether SSL interception is
active |
| CA certificate: | CA SSL-Interception | Select CA certificate |
| Save and close | ||
Packet filter
Call in menu
Only after that will the rules be applied!
/ →
- Access to the UTM services must be permitted
- Website requests without a proxy for HTTP and HTTPS should be blocked

The UTM already receives auto-generated rules by default.
The proxy rule already contains the required services for web cache port 8080 and name server port 53 for UDP and TCP.

In this example, no other rule may allow HTTP and HTTPS. This means, for example, that rules with the any service must be deactivated or deleted.
Alternatively, they can be replaced with a self-created service group without HTTP and HTTPS.
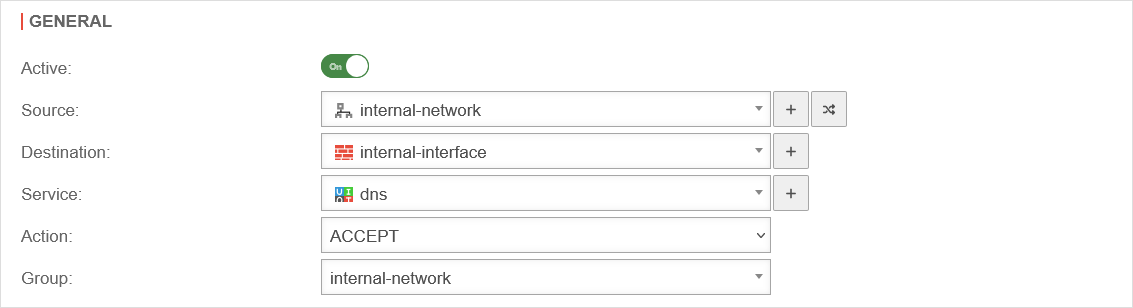
Packet filter rule for user groups
internal-network Button Area General
User group members must configure their browsers for the HTTP proxy.
The proxy port is entered in the browser.
This requires a rule that allows this port from this internal network on the corresponding interface.
By default, this is port 8080, which is already created with the Webcache service.

Packet filter rule for network groups
Both HTTP on port 80 and HTTPS on port 443 are redirected through the proxy.
Name resolution is required for this.
A rule is required that allows DNS from the private network on the associated network interface.
Prerequisite: The UTM is registered as a name server on the clients.
Browser settings for user groups
No further settings are required in the browser for transparent mode.
However, the browser requires the IP address and port of the proxy for authentication.
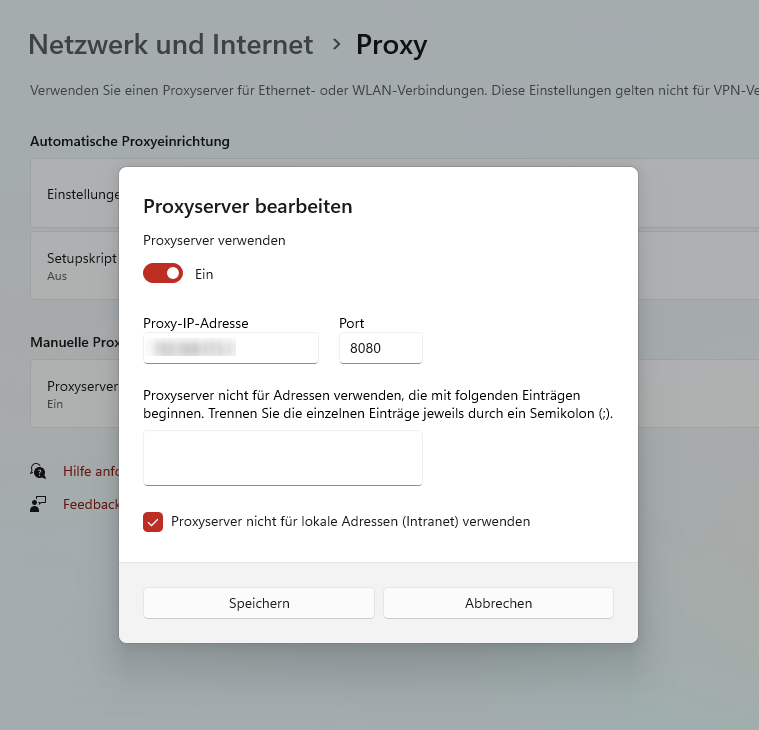
Chrome and Edge use Windows settings.
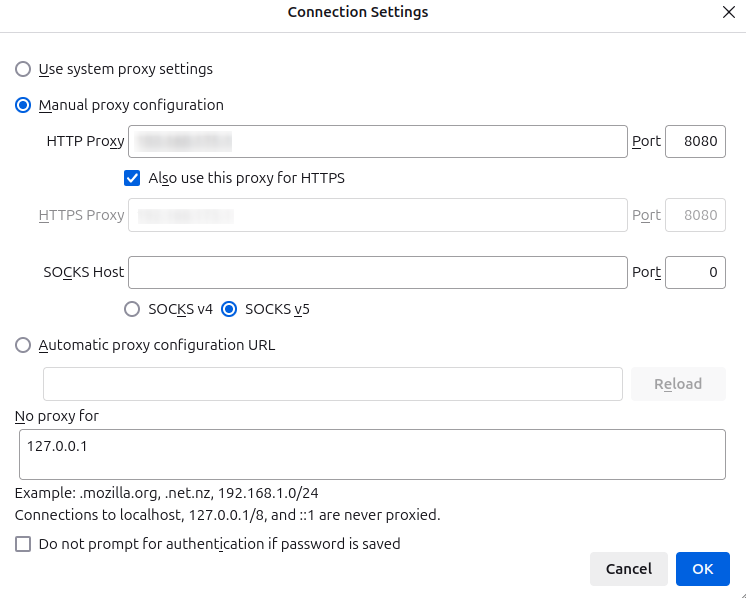
In Firefox, settings are set independently of Windows.
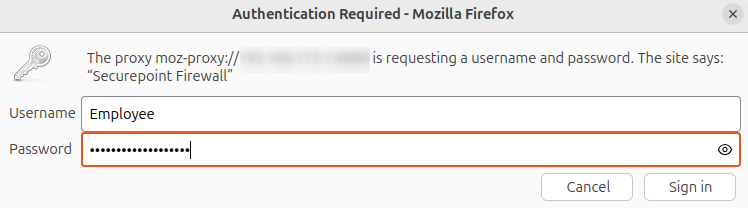
Once the browser has been set up in this way, an authentication screen will appear the first time you visit the website.
Enter your username and password here.
If
- the UTM is integrated into the Active Directory domain
- the client is also a member of the domain and
- Chrome or Edge is used
then authentication usually no longer takes place after the browser is started. Single sign-on is then active here, so that the authentication data is taken from the Windows login.