notempty
- Automatic login throttling at high values at Max. Attempts
Preamble
IDS (Intrusion Detection System) and IPS (Intrusion Prevention System) can detect and prevent attacks from the Internet or a network.
These features are useful for stopping the server from flooding with malicious connection attempts.
Firewall monitoring
Activation of monitoring
The activation / deactivation of the monitoring is done in the menu in the group 'BlockChain'.
| On | BlockChain The monitoring for these accesses can be switched off. | ||
| Default | Rule | rule description | |
|---|---|---|---|
| On | FailToBan_ssh | Access by ssh | |
| On | FailToBan_http_admin | Access via the Admin interface | |
| On | FailToBan_http_user | Access via the user interface | |
| On | FailToBan_smtp | Access via the mail gateway | |
Bans
BansAccess to the firewall can be blocked after a certain number of incorrect login attempts.
The settings are configured in the menu.
| Caption | Value | Decritption | 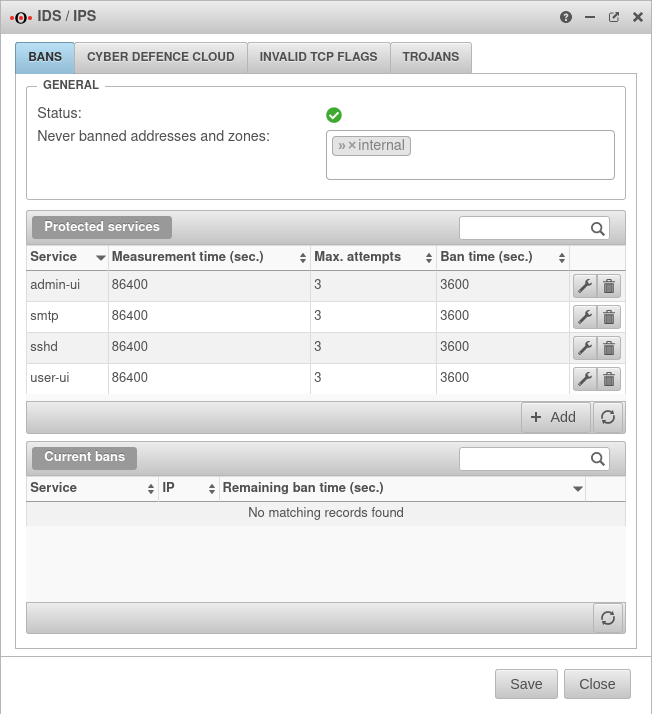 |
|---|---|---|---|
| Status | The "IPS Locks" application is enabled. | ||
| The "IPS Locks" application is disabled. | |||
| Never blocked addresses and zones: | » ✕internal | These IP addresses and zones, are not blocked by IDS/IPS. Examples: » ✕internal » ✕external_v6 » ✕vpn-ipsec » ✕192.0.2.192 | |
| Protected Services The following values can be configured : | |||
| Service | Dienst, der geschützt werden soll | ||
| Authentication via the admin interface. (default login port for administrators under 192.168.175.1:11115) | |||
| Authentication via ssh protocol (e.g. PuTTY) | |||
| Authentication via the user interface. (Default login port for users under: 192.168.175.1:443) | |||
| Authentication via the mail gateway | |||
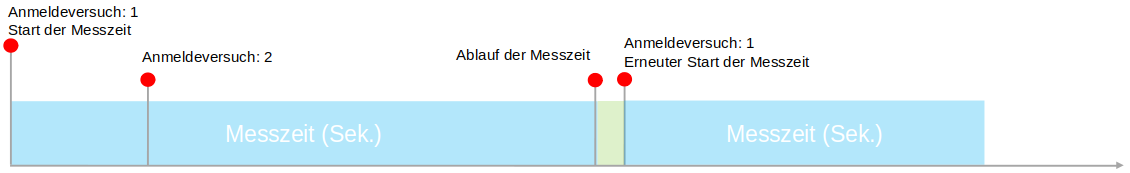
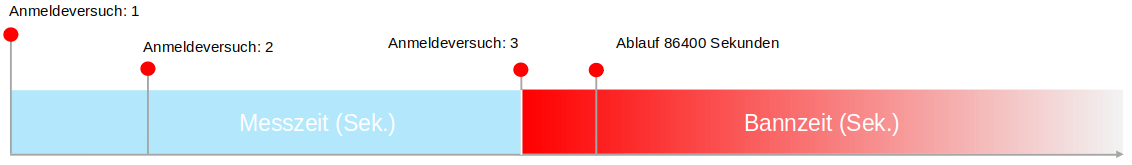
| measurment time: | 86400 seconds | measurement time can be counted within the failed attempts. | |
| Max. attempts |
3 | Number of failed authentication attempts notempty Independently of this, a general login throttling takes effect for the admin and user interface from the 8th consecutive failed attempt. notemptyNew as of: v12.5
| |
| Ban time: | 3600 seconds | Period for which access to this authentication is blocked. | |
Releasing blocked accesses again
Under Current bans , blocked IP addresses can be released again for renewed access to a service before the ban time expires with the button .
Unlocking is also possible via the CLI:
utm.name.local> spf2bd ip remove service admin-ui ip 192.0.2.192
Here the ip {code
Notification of bans
In the Alerting Center you can set under IPS Lockouts whether and how you want to be notified about such lockouts.
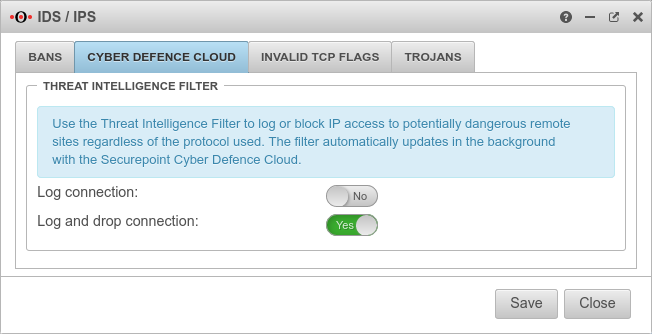
Cyber Defence Cloud
Cyber Defence CloudThe Threat Intelligence Filter logs or blocks access to potentially dangerous remote peers based on the IP address, regardless of the protocol used. As soon as a connection is established to an IP address that is known, for example, as a control server for malware, the Threat Intelligence Filter detects this.
The filter updates itself automatically in the background via the Securepoint Cyber Defence Cloud.
Block such connections with Log and drop connection: Yes
- For New installations, the Log and drop connection option is enabled New default behavior
- For Updates the option Log connection is enabled.
If a connection is blocked due to the Threat Intelligence Filter, a log entry is created.
Notification of these log messages can be configured in Alerting Center.
Default: Level 8 - Alarm → Message: Malicious connection detected. → Immediate Report & Regular Report
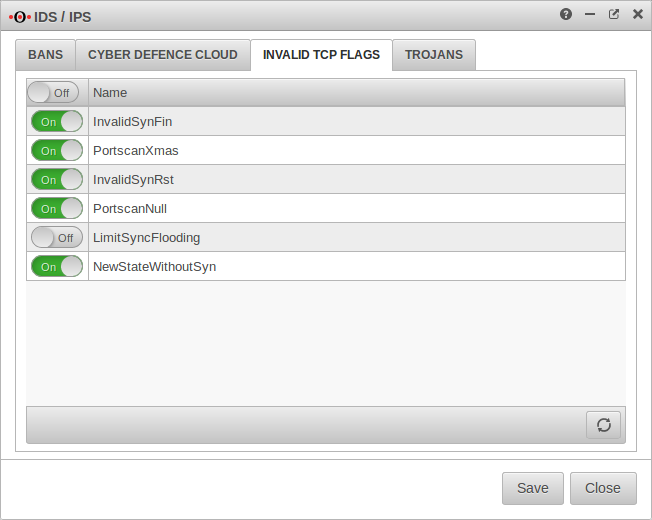
Invalid TCP Flags
Invalid TCP Flags
The detection of known flags in the TCP protocol can be enabled or disabled in the Invalid TCP Flags tab.
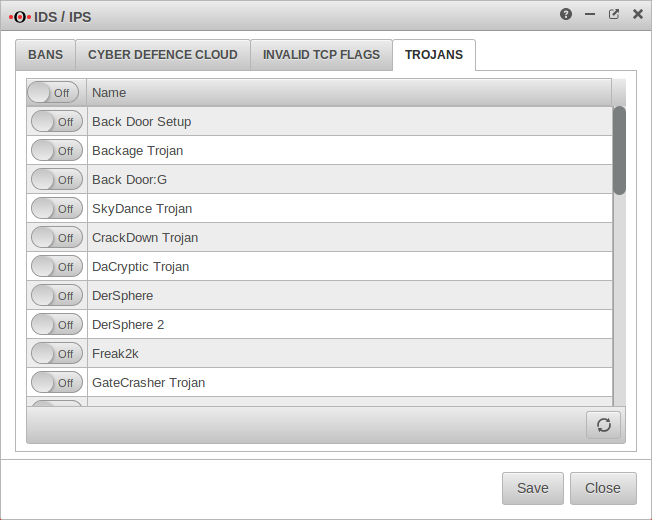
Trojans
TrojansTo make it more difficult for trojans to penetrate and spread in the network, access to ports known to be used by some trojans can be blocked here.
To do this, On closes all (header) or individual ports that are assigned to individual Trojans.
In case of problems with other software that also uses such ports, only selected entries can be activated.
notemptyBlocked ports overview
| Trojans | Protocoll | Port |
|---|---|---|
| Back Door Setup | TCP | 5000 |
| Backage Trojan | TCP | 411 |
| Back Door:G | TCP | 1234 |
| SkyDance Trojan | TCP | 4000 |
| CrackDown Trojan | TCP | 4444 |
| DaCryptic Trojan | TCP | 1074 |
| DerSphere | TCP | 1000 |
| DerSphere 2 | TCP | 2000 |
| Freak2k | TCP | 7001 |
| GateCrasher Trojan | TCP | 6970 |
| Hacka Tack | TCP | 31785 - 31792 |
| ICKiller | TCP | 1027 |
| ICQ Nuke 98 Trojan | TCP | 1029 |
| NetSpy Trojan | TCP | 1024 |
| Kaos Trojan | TCP | 1212 |
| Kuang2 Trojan | TCP | 17300 |
| Mneah Trojan | TCP | 4666 |
| Multidropper Trojan | TCP | 1035 |
| NoBackO Trojan | TCP | 1201 |
| Maniac Rootkits | TCP | 6667 |
| RAT Trojan | TCP | 1097 - 1098 |
| Remote Storm | TCP | 1025 |
| RexxRave Trojan | TCP | 1104 |
| Shadyshell Trojan | TCP | 1337 |
| Subseven | TCP | 27374 |
| Terror Trojan | TCP | 3456 |
| TheFlu Trojan | TCP | 5534 |
| TransScout Trojan | TCP | 2004 - 2005 |
| Trinoo Trojan | TCP | 1524 |
| WinHole Trojan | TCP | 1081 |
| Xanadu Trojan | TCP | 1031 |