notempty
- Information on the Authenticator apps regarding the supported hash algorithms
- CLI commands to assign OTP to the applications
- The hash algorithm can be selected (v12.4)
- Security note for OTP seed with LDAP (03.2023)
- Interval for validity is configurable 11.3
Preliminary remarks
If the OTP method is activated, login is only possible by entering a correct OTP.
Exception on user basis is not possible
SSL-VPN:
Since SSL VPN re-authenticates every hour, a new OTP must also be entered every hour.
Of course, disabling is not recommended. A change is transmitted by the UTM to the SSL VPN clients.
Saving the password in the SSL VPN client is not possible because the password that is passed is composed of the static user password and the OTP.
In case of malfunction of the OTP generator (smartphone or hardware token), the OTP can only be generated if there is access to the QR code or the secret code.
This can be found under .
notempty
If this is not available, access to the UTM is only possible with physical access directly at the device (keyboard and monitor at the UTM).
Printout of this code for the administrators as described in OTP Secret. File in the documentation.
The time of the UTM system can be checked in three ways:
- Using the administration web interface: The time is shown in the widget selection if it is not expanded or in the network menu under server settings in the time settings section.
- Using the CLI with the command system date get
- Using the root console with the command date
The system time can then be set using the following options:
- Using the administration web interface in the network menu under the menu item server settings in the section time settings
- Using the CLI with the command system date set date then seperated with spaces the current date and time in the format YYYY-MM-DD hh:mm:ss
OTP - One-Time-Password
The One-Time-Password (OTP) is an additional authentication mechanism that provides extra security when a user logs in.
In the UTM the time-based method is being used (TOTP = Time-based One Time Password). A new OTP is calculated every 30 seconds based on the shared secret code and the current time.
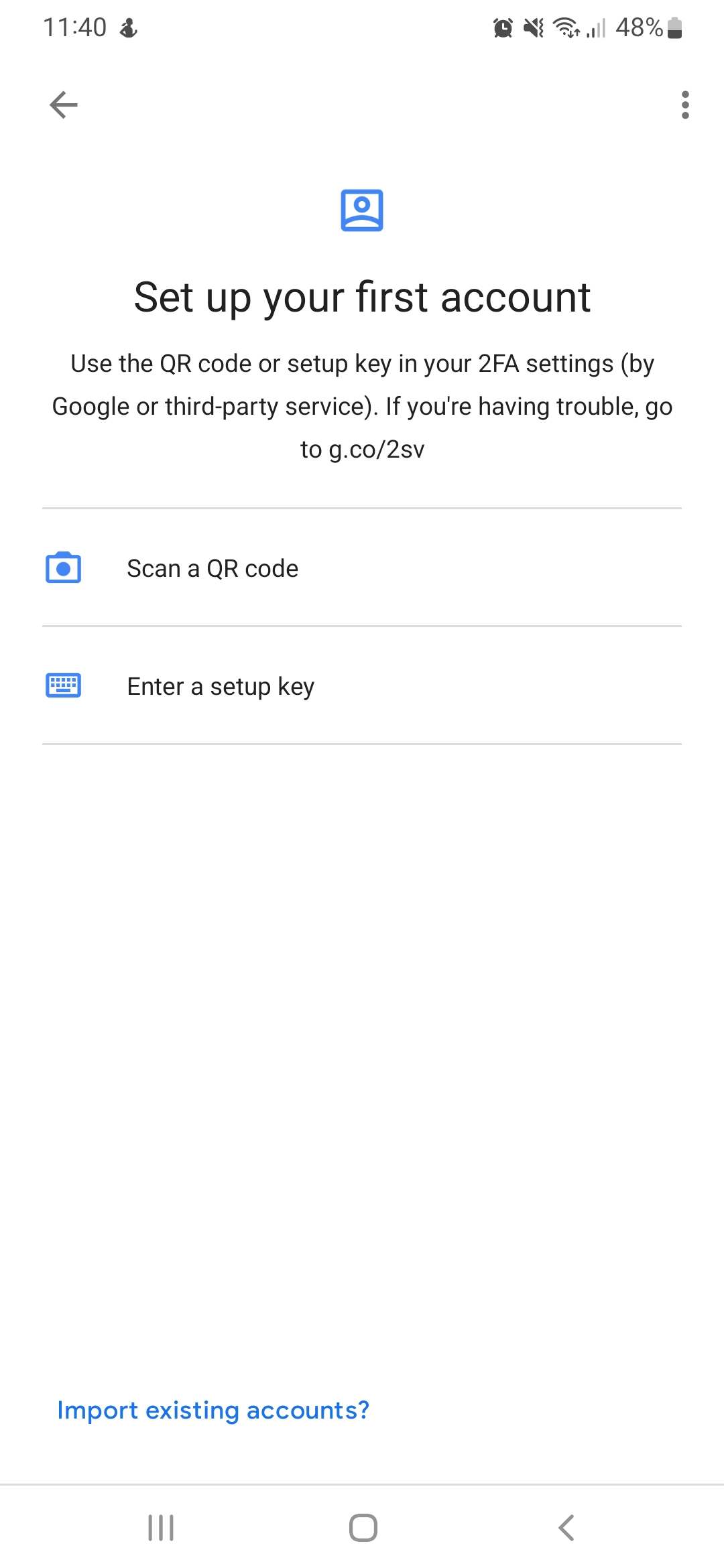
To generate this 6-digit password, a smartphone app is used as the token, such as the Google Authenticator. This is available for Android, as well as for iOS devices.
Other apps, such as FreeOTP for Android, are also possible.
Set up OTP
Activation procedure
- Ensure that the time of the UTM and the token runs synchronously
- Transmission of the secret code to the token
- Activating the OTP method on the UTM
- Testing the login, before the current session has ended
Exceptions are not possible.
Configure OTP User
First, the users are created under as usual.
See also Benutzerverwaltung.
The OTP code for this user can only be displayed after the user's entries have been saved.
Display or change by clicking on the edit button in the user row in the tab OTP on the right side.
The code can be created automatically by the Securepoint UTM and is available in two formats.
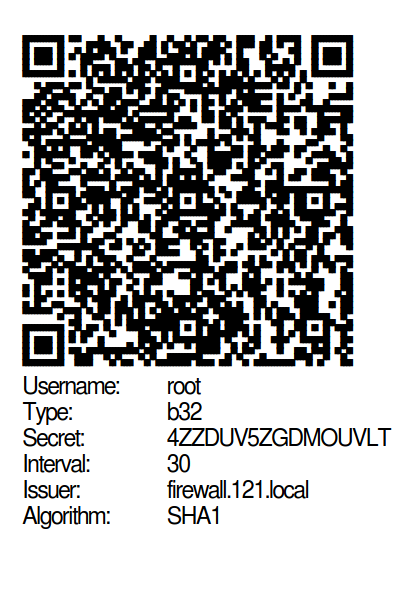
On the one hand as a QR code, which can simply be photographed with the smartphone app, and on the other hand in text form to be entered using the keyboard.
OTP Configuration
| |||
| Input format: | Default setting, base32 encoded, 16 characters length Codes less than 26 characters in length may be flagged as insecure by OTP apps |
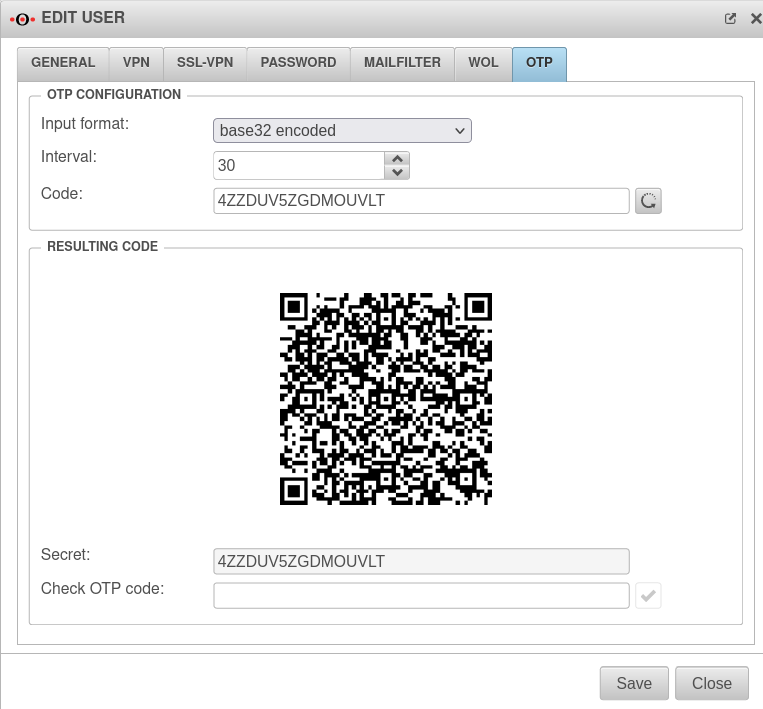 | |
| base64 encoded, length 16 - 168 characters (in blocks of 4), manual input | |||
| HEX coded, valid characters: A-F, a-f and 0-9 / length 10-128 pairs, manual input | |||
| Hash algorithm: |
Default |
The hash algorithm can be selected | |
| notempty Not every authenticator app supports every hash algorithm! Some of these apps do not support sha256, or sha512. When using these apps, the default value may have to be retained. | |||
| Interval: | 30 | The interval should be set to 30 seconds If a hardware token is used, its value must be adopted. OTP apps are often optimized to update the token every 30 seconds. Adjustable as of v12.3
| |
| Code: | 4ZZDUV5ZGDMOUVLT | Gives the code in text form It is also possible to enter a code manually, e.g. a hardware token.
| |
| Creates a new code with the default settings (base32 coded, interval 30 seconds) | |||
Resulting Code
| |||
| Secret: | Gives the code in text form | ||
| Check OTP code: | An OTP code generated with a corresponding OTP generator can be entered here to check whether the OTP generator has been set up correctly. | ||
OTP Secret
For distribution to the users there is a possibility to print the created codes.
A document in PDF format will then be generated as follows:
Setting up an Authenticator
Use of a hardware token
The use of a hardware token is also possible.
This should be a RFC 6238 compatible password generator.
We currently support the Feitian OTP c200.
A download link for the HEX code is sent by the supplier for this purpose, which must be registered with the user as described above.
The following parameters must be used:
- SHA algorithm: SHA1
- Time interval: 30 seconds
- Optional: SEED programming Background on SEED programming: In case the token happens to be created in in non-trustworthy countries and you want to make sure that it does not already contain malicious code or is otherwise compromised upon delivery, i.e. Mtrix will reprogram it for a small amount.
notempty
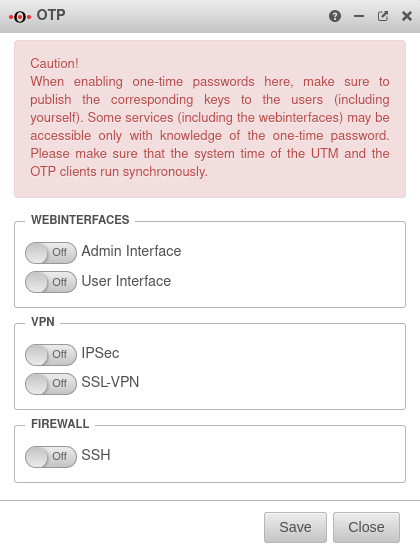
Assign OTP to applications
Under you can select for which applications the users should additionally authenticate themselves with the one-time password.
Web interfaces
| ||
| Off | Admin Web Interface The CLI command to enable OTP for the admin interface is: extc global set variable GLOB_AI_OTP_AUTH value 1 | |
| Off | User web interface he CLI command to enable OTP for the user interface is: extc global set variable GLOB_UI_OTP_AUTH value 1 | |
VPN (Roadwarrior connection)
| ||
| Off | IPSec The cli command for IPSec is: extc value set application ipsec variable USE_OTP value 1 | |
| Off | SSL-VPN The cli command for SSL VPN is: extc value set application openvpn variable USE_OTP value 1 | |
Firewall
| ||
| Off | SSH (console) SSL-VPN The cli command for SSH is: extc value set application sshd variable USE_OTP value 1 | |
If this is not available, access to the UTM is only possible with physical access directly at the device (keyboard and monitor at the UTM).
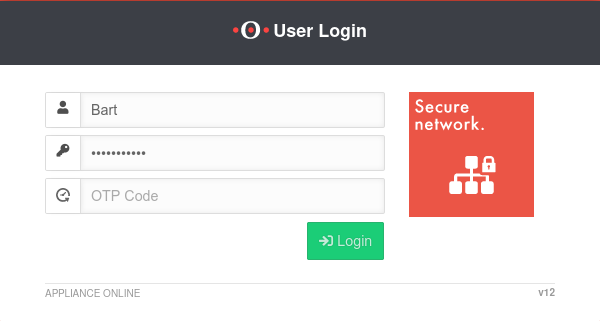
Use OTP
Web interface
When logging in to the administration or user web interface, there is now an additional authentication field for the OT code.
Here, in addition to the user name and password, the generated code is entered.
VPN
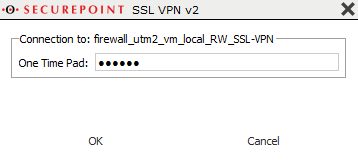
In the SSL-VPN Client, you can set whether the OTP code is to be requested separately. A more detailed explanation can be found here.
If the remote terminal allows a separate transmission of the OTP password (UTM from version 11.8), the following procedure can be followed:
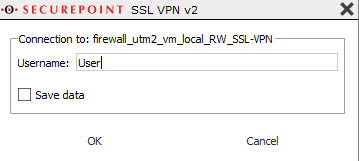
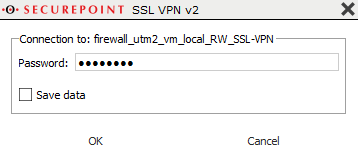
Start the SSL VPN connection on the client (on Windows: double-click the lock icon in the taskbar).
Establish the connection by clicking on ![]()
The connection is established in three steps:
If OTP is used in combination with an SSL VPN or Xauth VPN connection and the remote terminal does not support the separate transmission of the OTP code, the OTP code must be entered directly after the user password without spaces during the password query.
Example:
| Password: | insecure | Saving the password in the SSL VPN client is not possible because the password that is passed is composed of the static user password and the alwys changing OTP. |
| OTP: | 123456 | |
| password | insecure123456 |
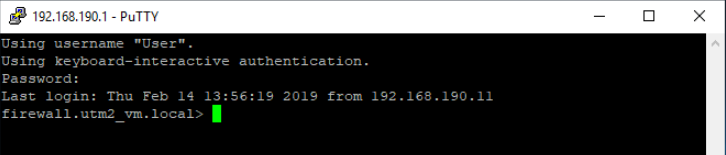
SSH connection
If access is used with an SSH console and OTP, the OTP code is requested in a separate row Pin.
When accessing with an SSH console and OTP, and the counterpart does not allow separate transmission of the OTP code, the OTP code is entered without spaces directly after the user password.
Example:
| Password in UTM:: | insecure |
| OTP: | 123456 |
| Password: | insecure123456 |