New article with version: 2.0.0
notemptyThis article refers to a Beta version
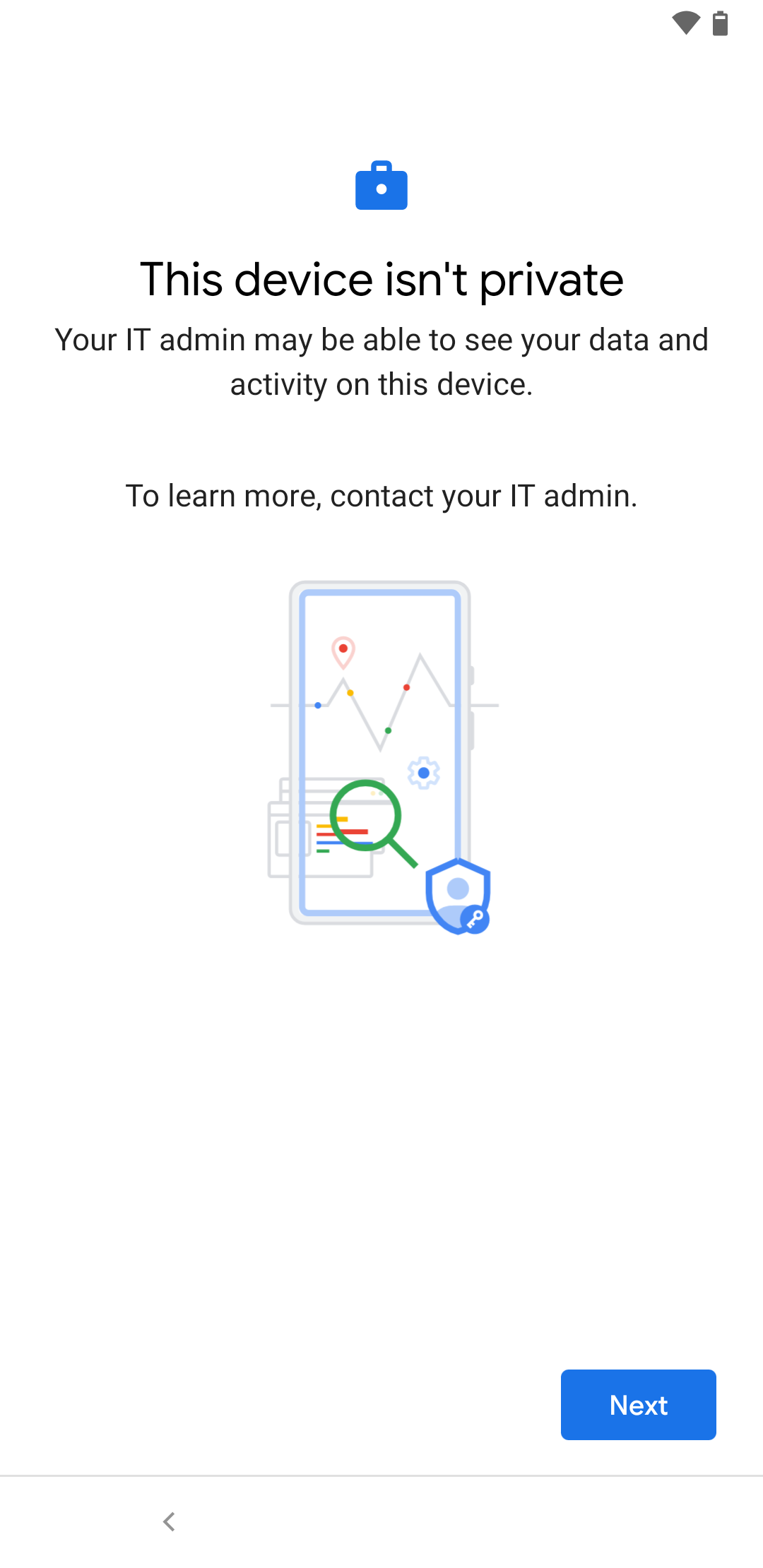
Company owned, business only - Company owned without private use:
- The devices are intended for use in the enterprise environment only.
- The IT administrator has full control over the smartphone
- Private data is strictly prohibited on the device
- Settings under: : Private use is not allowed
Flow chart
The steps required to connect Android devices are described here:
Prerequisite:
- Securepoint Mobile Device Management (MDM) must be linked to a Google account as Android Enterprise account
- In Securepoint Unified Security Portal configured Android Enterprise Profile
Enrollment:
- Securepoint Mobile Device Management (MDM) must be linked to a Google account as Android Enterprise account
- In Securepoint Unified Security Portal configured Android Enterprise Profile
Enrollment:
- Securepoint Mobile Device Management (MDM) must be linked to a Google account as Android Enterprise account
- In Securepoint Unified Security Portal configured Android Enterprise Profile
Enrollment:
- Securepoint Mobile Device Management (MDM) must be linked to a Google account as Android Enterprise account
- In Securepoint Unified Security Portal configured Android Enterprise Profile
Enrollment:
Preparation
There must be a connection from the Securepoint Mobile Security Portal to an Android Enterprise account.
COBO: Link Google Enterprise with Securepoint Mobile Security
There must be an Android profile that can be assigned to the device.
COBO: Android Profile
Under you can Add profile or Import profile or edit an existing profile (click on profile tile or → Edit )
Various configurations are made here, e.g:
- Install and configure Apps
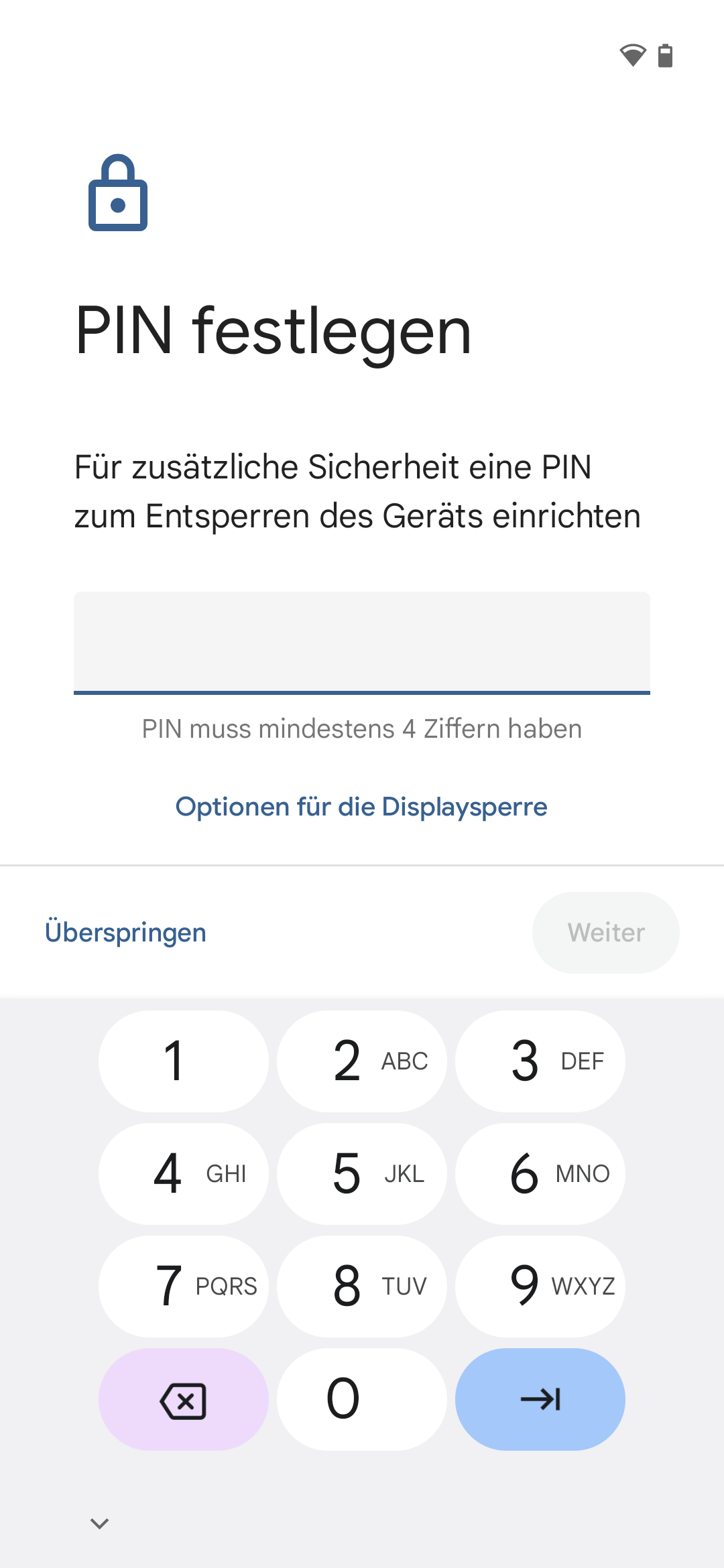
- Password policies
- Security settings
- Control of the app store for private applications
- Release of professional address books for private use (e.g. for incoming calls).
- WiFi configurations
- Restrictions
- Password policies
- Security settings
notemptyIn addition to configuring the basic settings, restrictions, networks, etc., the following settings are required in the profile:
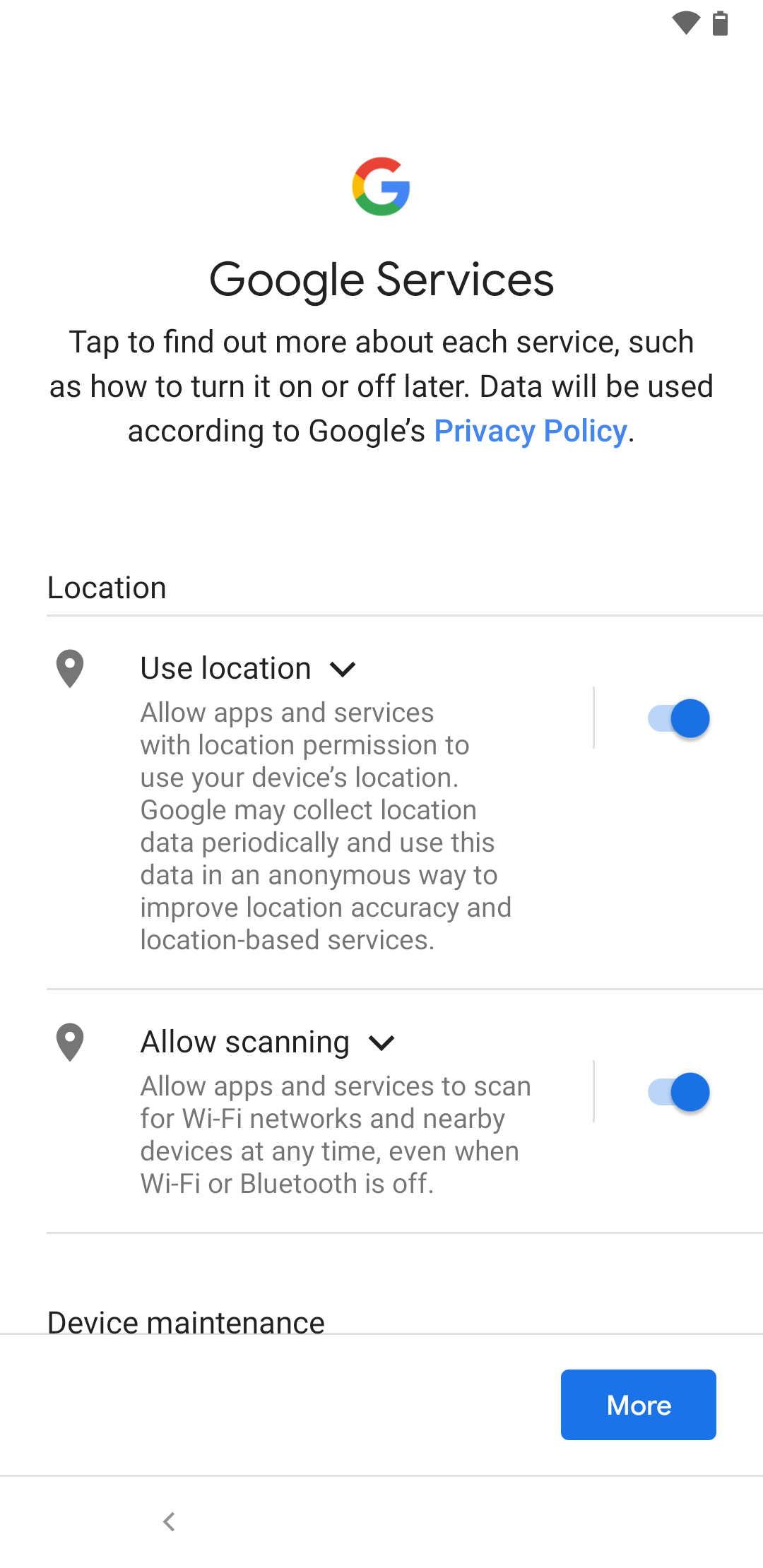
Applications Applications
Installation type Kiosk must be added in the Applications tab for a single app | |||
| Caption | Value | Description | 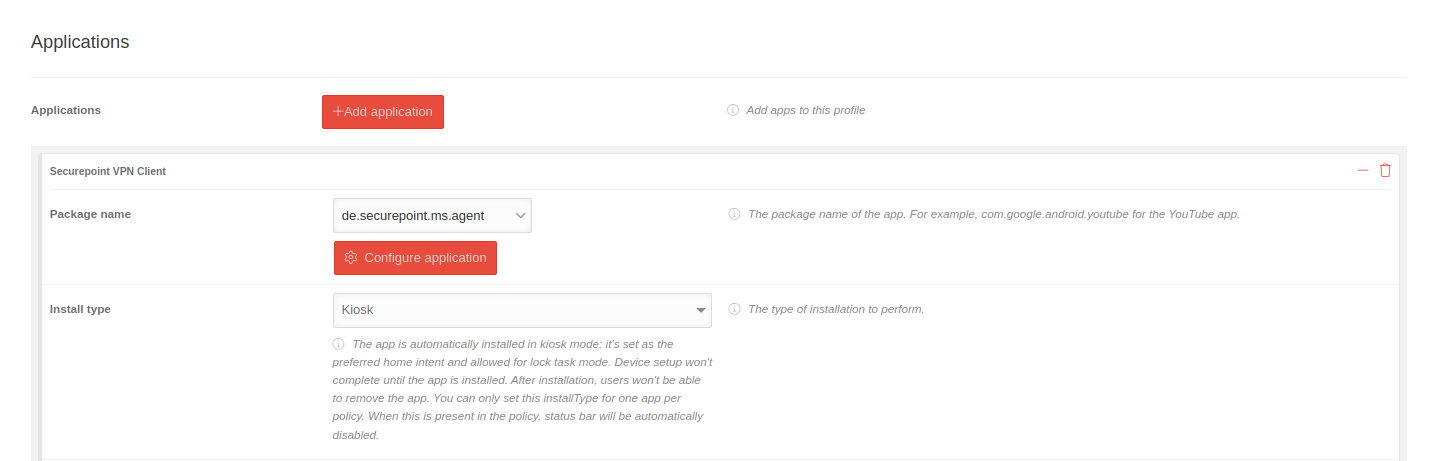 |
|---|---|---|---|
| Add application | |||
| Packetname | en.selected.app | Select package from dropdown menu or add with select application | |
| Installation type | Kiosk |
| |
Restrictions Restrictions
Settings in the Restrictions tab for the kiosk mode | |||
| Activate the custom kiosk launcher | Hides all system apps on the homescreen and shows only the apps installed via the profile. It is recommended to additionally disable the status bar to block access to device settings. | ||
| Power Button Actions | Not specified | Sets the behavior of a device in kiosk mode when a user presses and holds the on / off button. Available by default | |
| Available | The on / off menu (e.g. power off, restart) is displayed when a user long presses the on / off button of a device in kiosk mode | ||
| Blocked | The On / Off menu (e.g. power off, restart) is not displayed when a user long presses the On / Off button of a device in kiosk mode | ||
| System error warnings | Not specified | Specifies whether to block system error dialogs for crashed or unresponsive apps in kiosk mode. Muted by default. | |
| Activated | All system error dialogs such as crash and app not responding (ANR) are displayed. | ||
| Mute | All system error dialogs like crash and unresponsive app (ANR) are blocked. When blocked, the system forcibly stops the app as if the user closes the app from the user interface. | ||
| Systemnavigation | Not specified | Indicates which navigation functions are enabled in Kiosk mode (e.g. Home, overview keys). | |
| Activated | Home and overview buttons are activated. | ||
| Deactivated | The Home and Overview buttons cannot be accessed. | ||
| Home button only | Only the home button is enabled. | ||
| Status bar | Not specified | Specifies whether system information and notifications are disabled in kiosk mode. By default, notifications and system information are disabled. | |
| Notifications and system information enabled | System informations and notifications are displayed in the status bar in kiosk mode | ||
| Notifications and system informations disabled | System informations and notifications are disabled in kiosk mode | ||
| System informations only | Only system information is displayed in the status bar | ||
| Device settings | Not specified | Specifies whether a user can access the app settings of the device in kiosk mode Allowed by default | |
| Allowed | Access to the Settings app is allowed in Kiosk mode | ||
| Blocked | Access to the Settings app is not allowed in Kiosk mode | ||
notemptyIn addition to configuring the basic settings, restrictions, networks, etc., the following settings are required in the profile:
Personal use Personal use
In the tab Personal use this must be explicitly allowed and if necessary further settings must be made. | |||
| Caption | Value | Description | 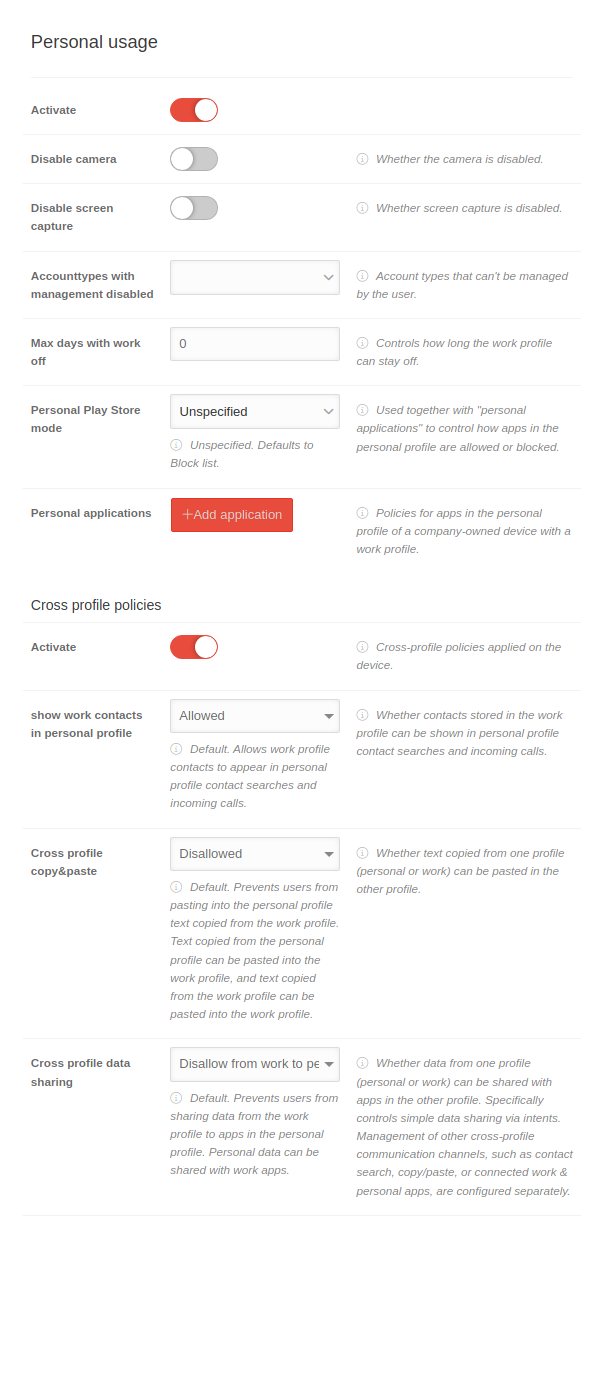 |
|---|---|---|---|
| Activate | default: off |
Enables the control of private use notemptyIf this switch is not enabled, the user can install private apps without any restrictions! | |
| Disable camera | Disables the camera in the personal profile In order to use the camera for business applications, it must be stored as an app in the Applications tab. | ||
| Deactivate the screen recording | Screen recordings (screenshots) are not possible when activated | ||
| Account types with disabled management | Account types that cannot be managed by the user. com.google prevents adding Google accounts in apps, for example.
| ||
| Max. days without work | 0 | Controls how long the work profile can stay off. (In the app overview, the apps and notifications of the work profile can be deactivated.) | |
| Personal Play Store mode | Not specified | Specifies whether to allow or block the apps in the Personal apps section of the personal profile. Standard block list. It is also necessary to specify the Installation type. | |
| Approval list | Only apps that are explicitly specified in Personal apps and whose Installation type is set to Available may be installed in the personal profile. | ||
| Blocklist | All Play Store apps can be installed in the personal profile, except for those whose installation type is "Blocked" under "Personal apps". | ||
| Personal applications | Add application | Guidelines for apps in the personal profile of a company-owned device with a work profile | |
| Packetname | en.selected.app | Select package from dropdown menu or add with select application | |
| Installation type | Not specified | The way the installation is performed. (Not specified=Default: Available) | |
| Block | The app is blocked and cannot be installed. If the app was installed using an old profile, it will be uninstalled | ||
| Available | The app is ready for installation | ||
| Cross-profile guidelines | |||
| Activate | Policies that, when activated, define restrictions on communication between private and business profile | ||
| Show work contacts in personal profile | Allowed default value |
Allows work profile contacts to appear when searching for personal profile contacts and incoming calls | |
| Not allowed | Prevents contacts from the work profile from being displayed when searching for personal profile contacts and incoming calls | ||
| Not specified | Corresponds to Allowed | ||
| Cross-profile copy & paste | Prevents users from pasting text copied from the work profile into the personal profile. Text copied from the personal profile can be pasted into the work profile and text copied from the work profile can be pasted into the work profile. | ||
| Allowed | Text copied in one of the profiles can be pasted in the other profile | ||
| Not specified | Corresponds to Not allowed | ||
| Cross-profile data sharing | Refuse from work to personal profile default value |
Prevents users from sharing work profile data with apps in the personal profile. Personal data can be shared with work apps. | |
| Prevents data from being passed from both the personal profile to the work profile and from the work profile to the personal profile. | |||
| Allowed | Data from one of the profiles can be shared with the other profile. | ||
| Not specified | Corresponds to Not allowed | ||
| Save | All data must be stored in order to be transferred to the devices. | ||
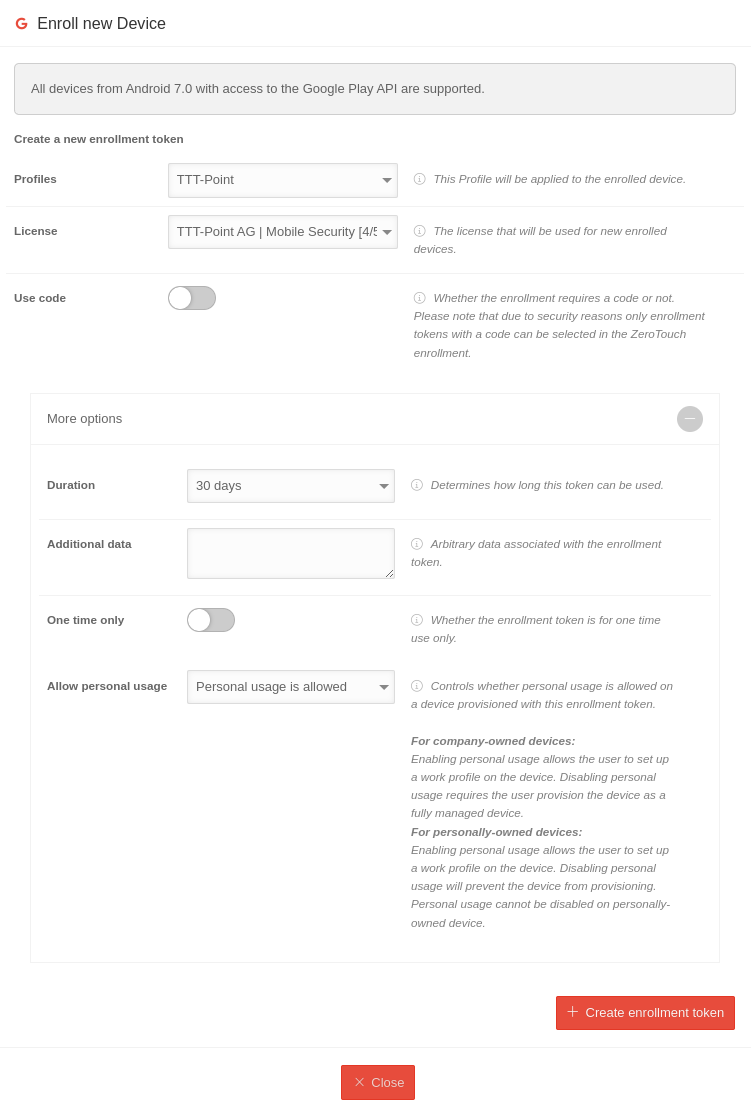
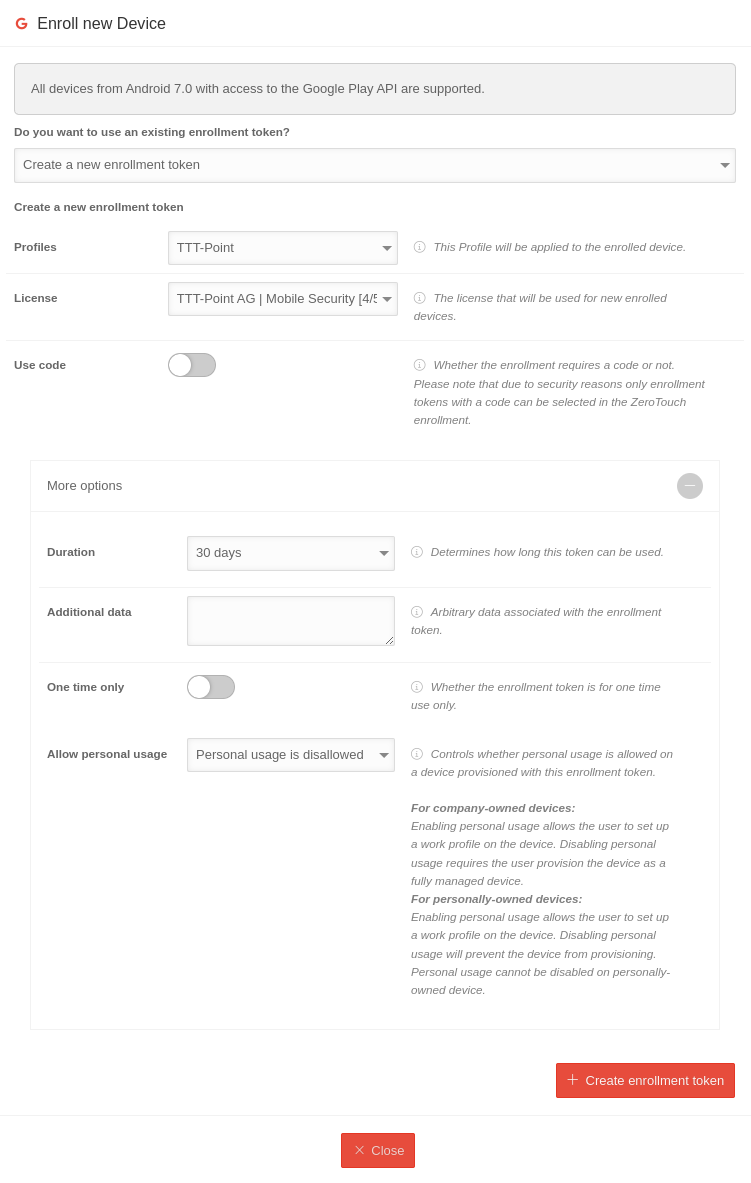
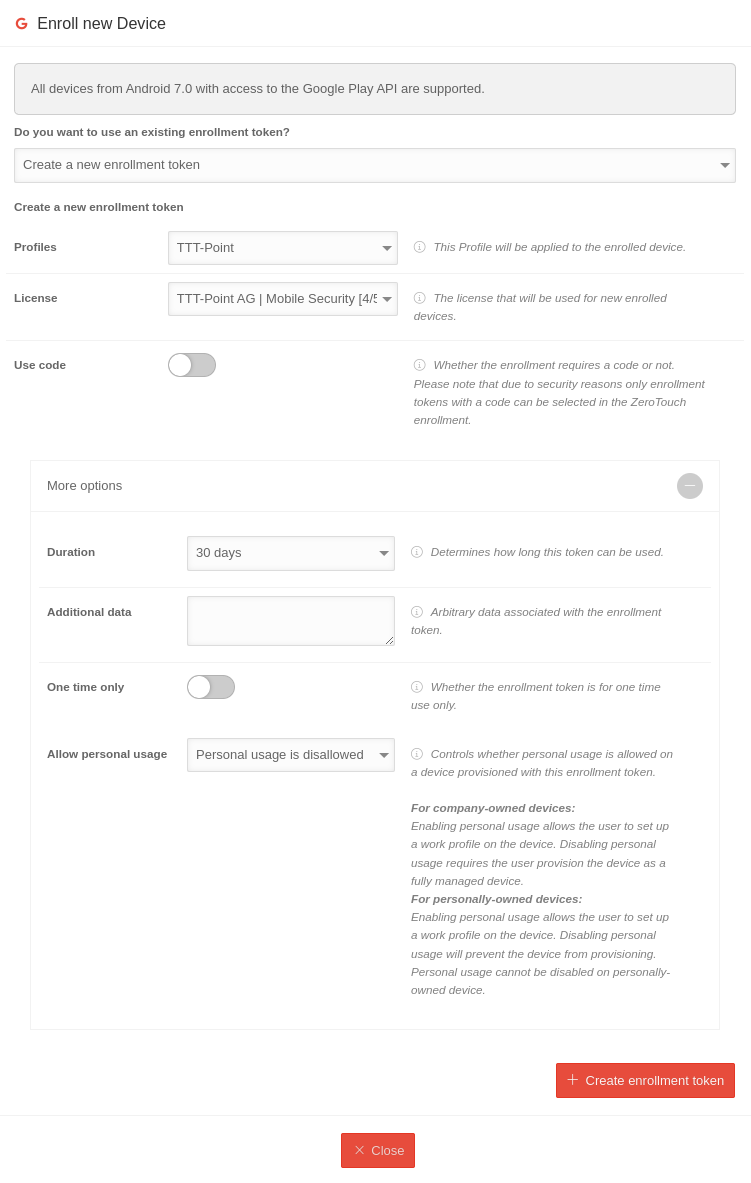
Device enrollment
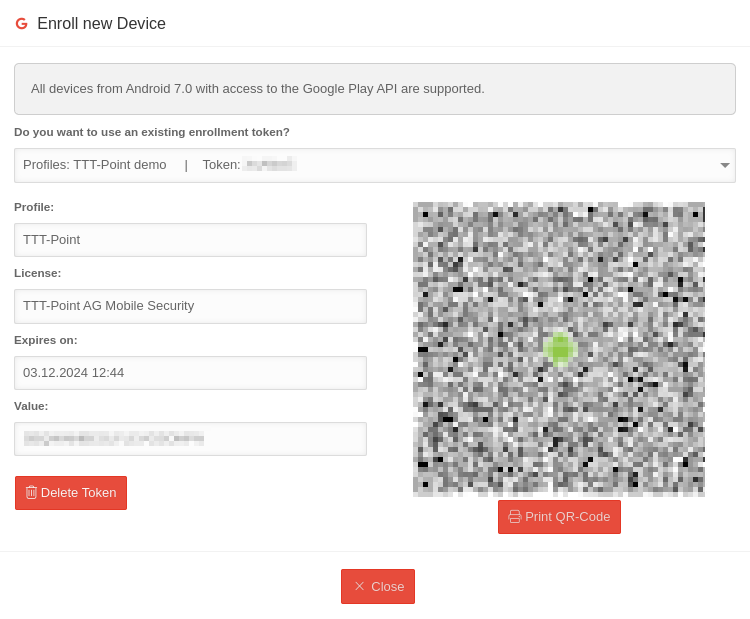
COBO: Registration Token for a Profile
Under it is possible to Register new device
| Caption | Option | Description | 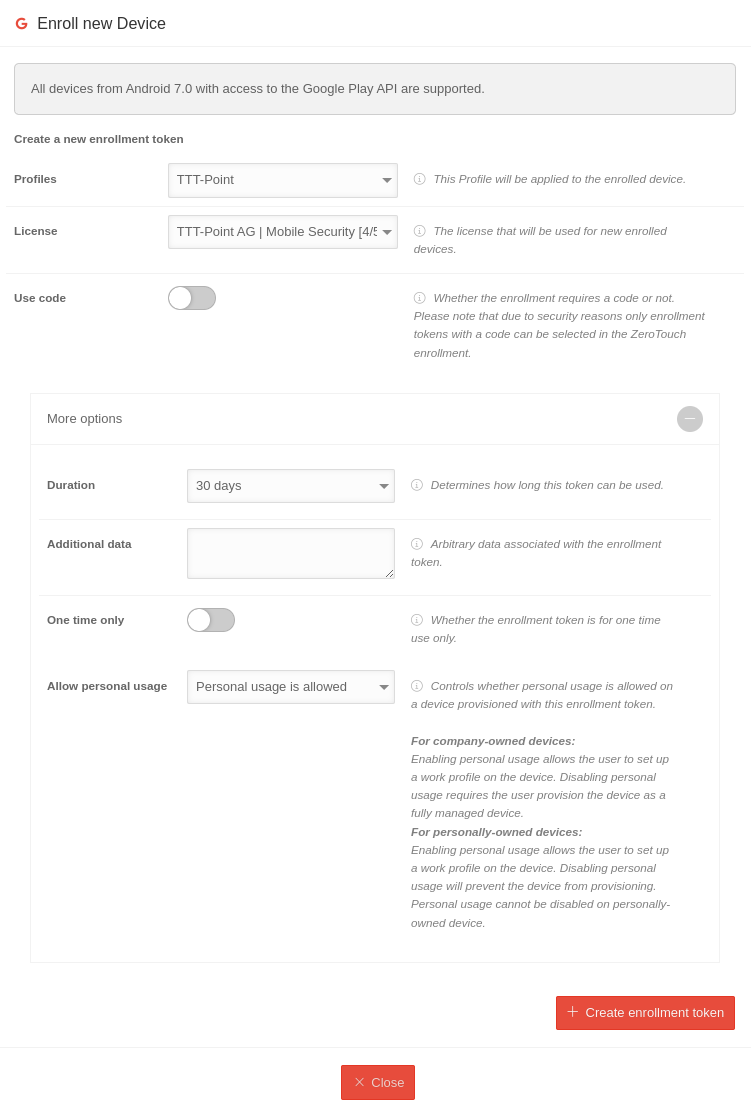 |
 |
 |
 | ||
|---|---|---|---|---|---|---|---|---|
| Would you like to use an existing registration token? | Create a new registration token | If a registration token has already been created that has not yet expired, it can be selected and displayed here. (Fig. see below) | ||||||
| Profile | Android Enterprise Profil | This profile is to be applied to the device to be registered. | ||||||
| License | TTT-Point AG | MDM [0/10] (aaaa) | Select the license to be used for new enrolled devices. It is possible to assign devices to a new License after a runtime license expires. | ||||||
| Use code | Determines whether or not a code is required during enrollment at the end of device registration notempty Should be enabled to prevent devices that have fallen into unauthorized hands from being registered with configured credentials or other company secrets notemptyFor security reasons for ZeroTouch Enrolment, only enrolment tokens that have been provided with a PIN can be selected. | |||||||
| More options | ||||||||
| Duration | 30 days | Specifies how long this token can be used After this, device registration with this token is no longer possible. Possible values: 30 minutes Technically, it is a limit of 10,000 years | ||||||
| Additional data | Any data associated with the registration token. Displayed under in the device overview | |||||||
| Only once | Specifies whether the registration token may only be used once. | |||||||
| Allow private use | Private use is permitted | Determines whether private use is allowed on a device logged in with this registration token. For private devices: A work profile is set up on the device. |
Private use is permitted | Determines whether private use is allowed on a device logged in with this registration token. For corporate devices: A working profile is set up on the device. |
Private use is not permitted | Determines whether private use is allowed on a device logged in with this registration token. Disabling private use prevents the creation of a work container. |
Private use is not permitted | Determines whether private use is allowed on a device logged in with this registration token. Disabling private use prevents the creation of a work container. |
| Create registration token | Creates a registration token with QR code and a value that can be entered using the keyboard. The name of the associated profile is displayed, as well as the date on which it expires and can no longer be used. |
 | ||||||
COBO: Register device
Fully managed devices (COBO, COSU)
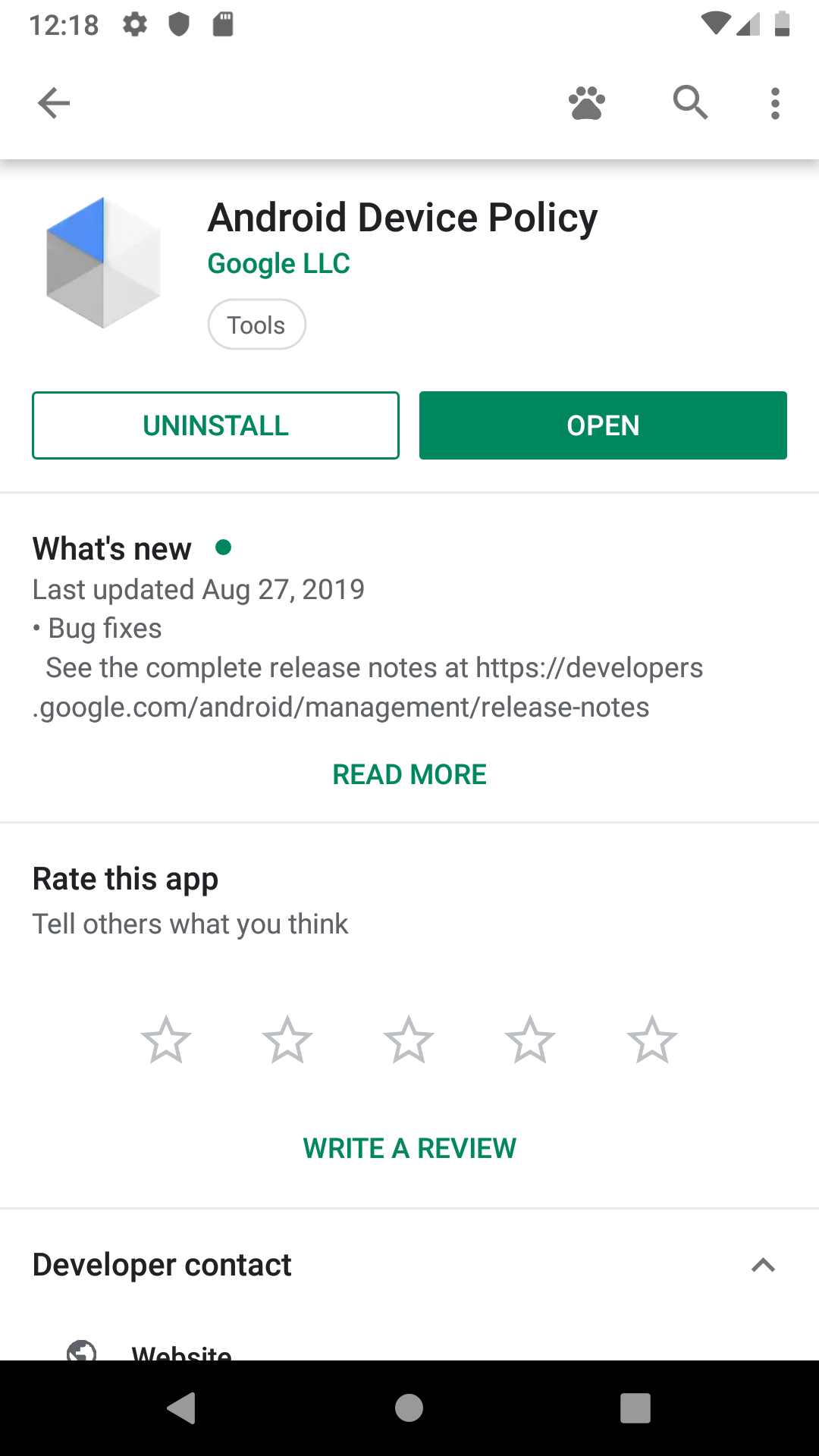
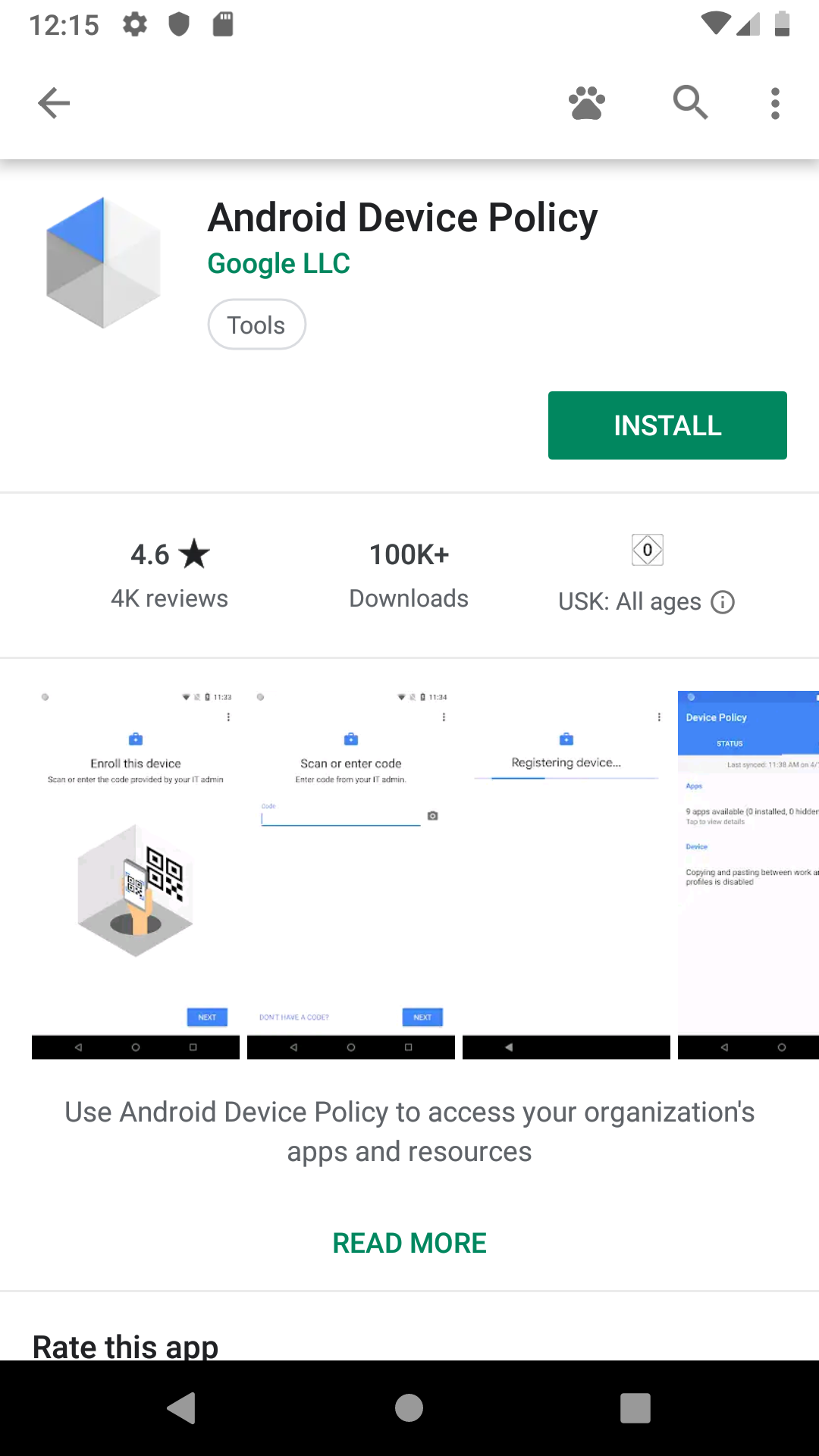
In order to be able to distinguish private from business apps, the app Android Device Policy is required.
On private devices in which only the work profile is managed by an organisation - and thus by the Securepoint Mobile Security Profile - this app must be installed manually from the Android App Store.
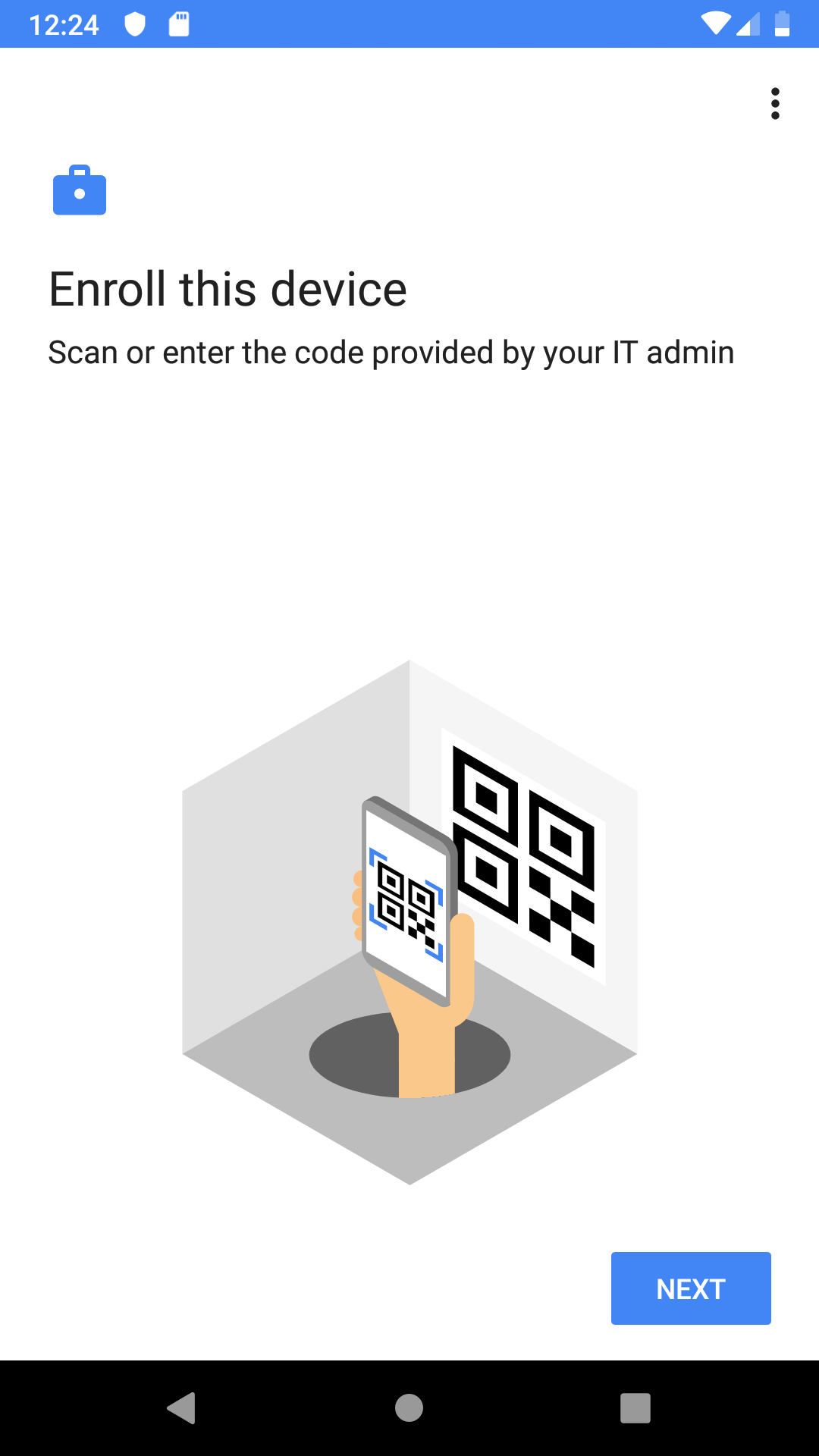
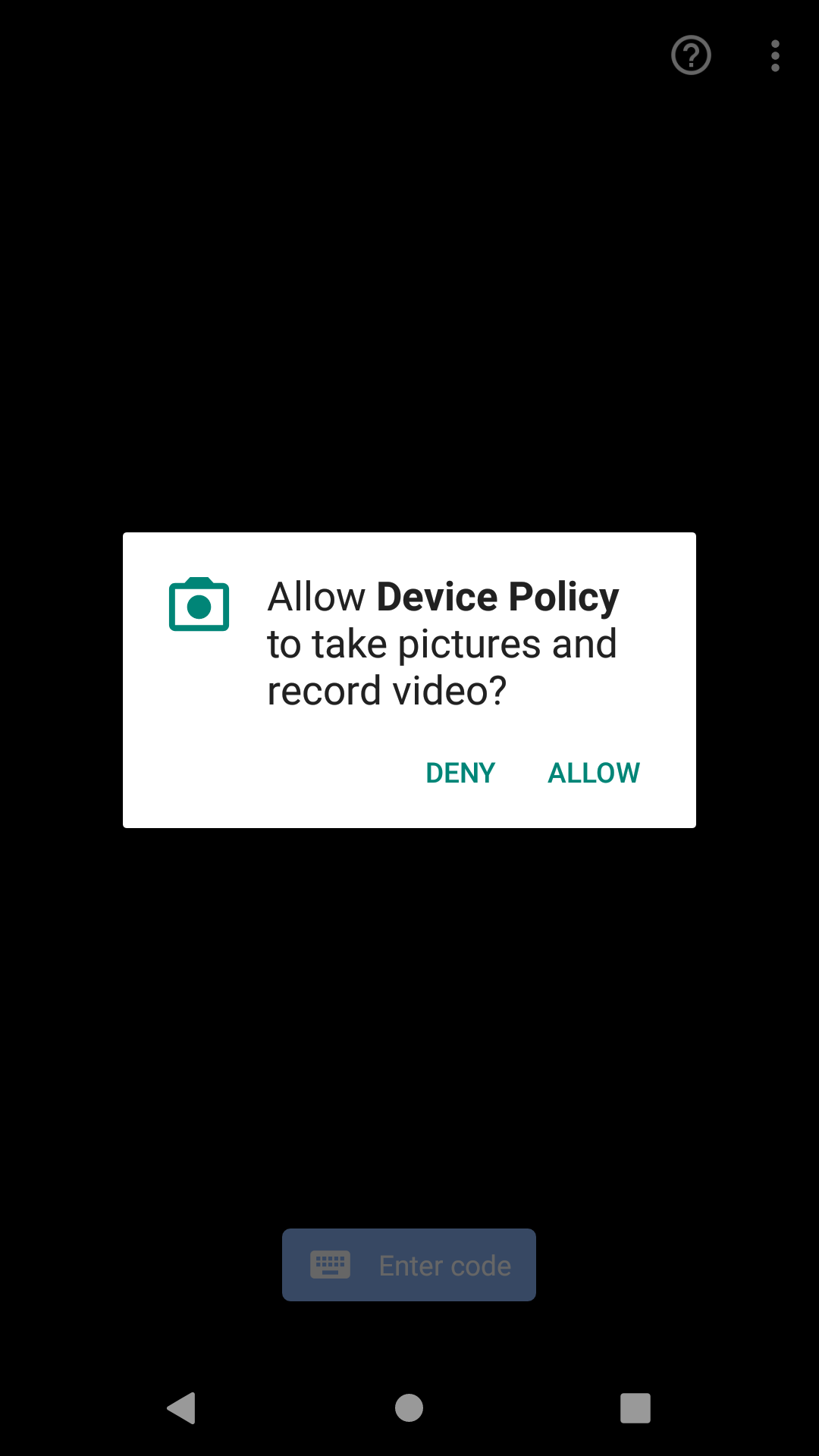
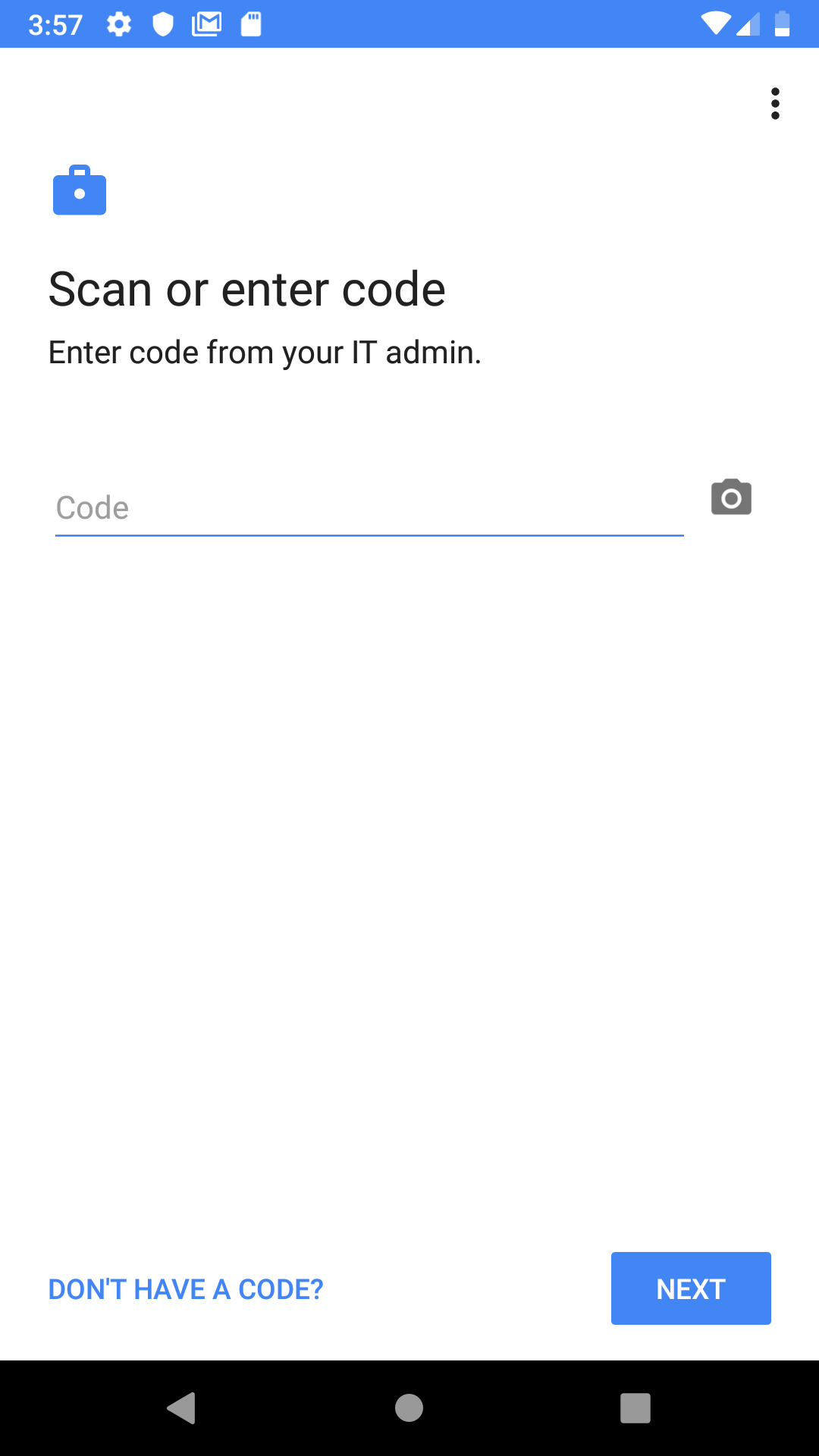
With this app the registration token is scanned or entered via the keyboard and the devices can be registered and configured in the portal.
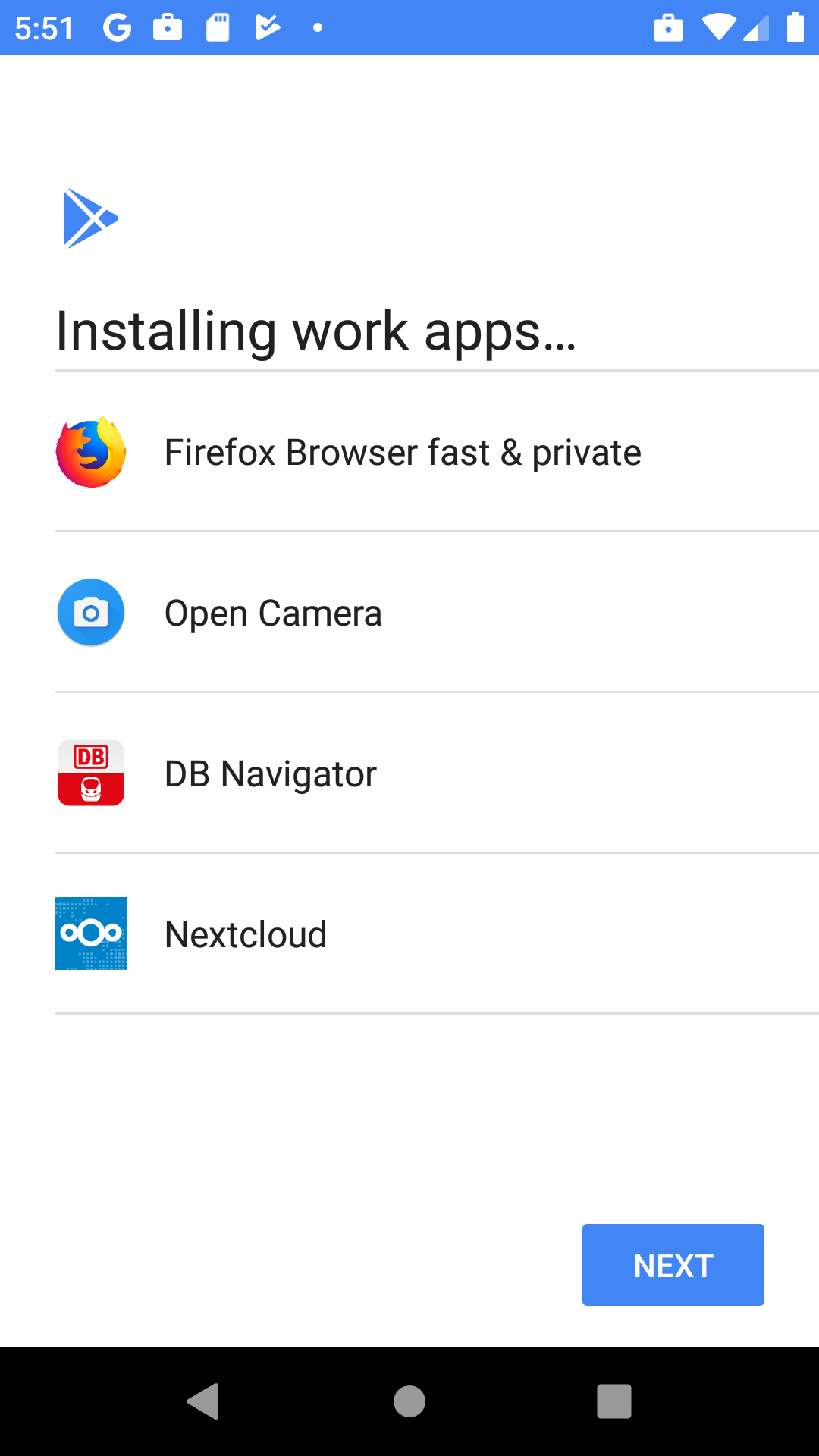
- Installing the app Android Device Policy from the Google App Store
- Scanning the QR code or entering the registration token via the keyboard
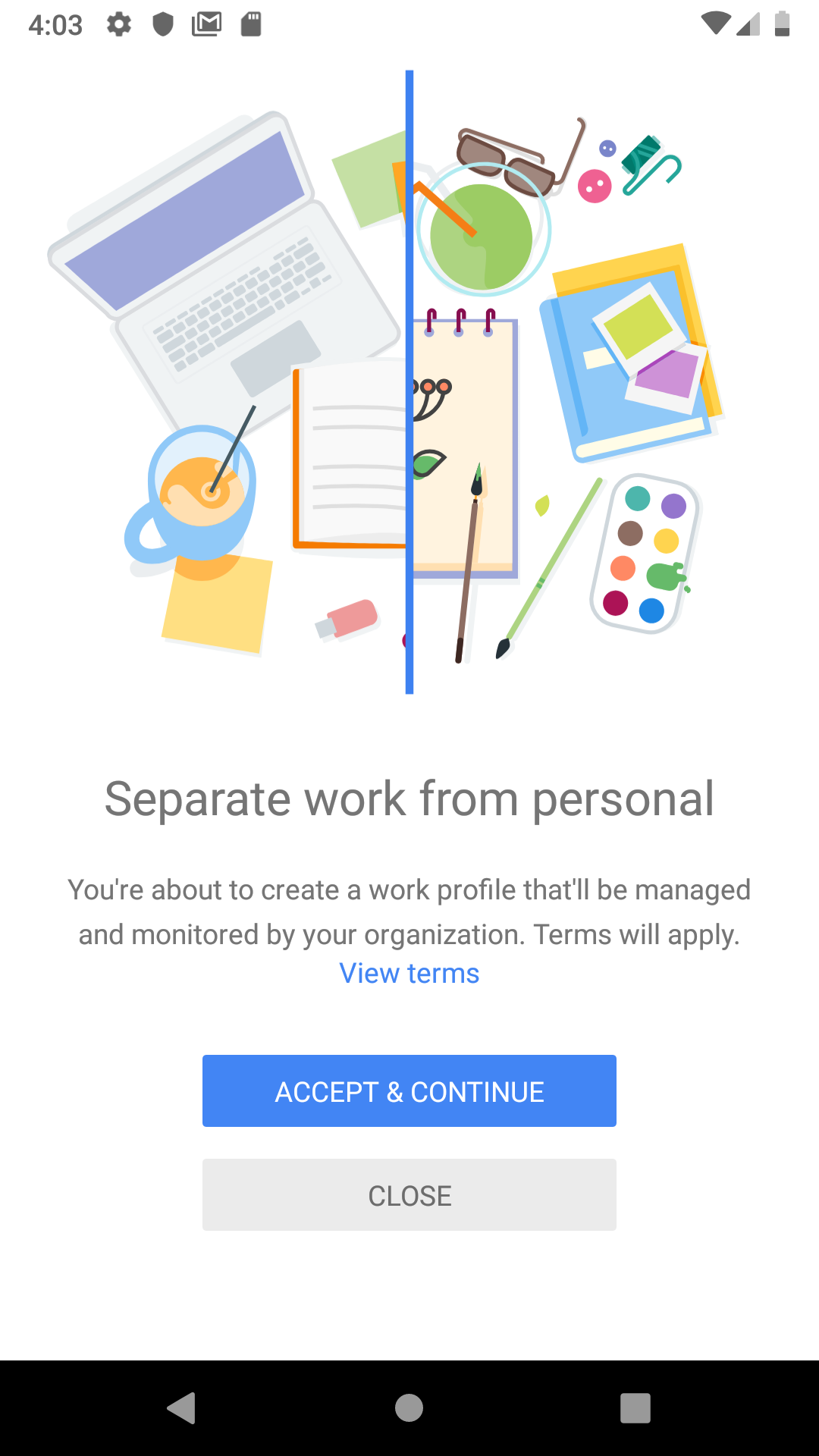
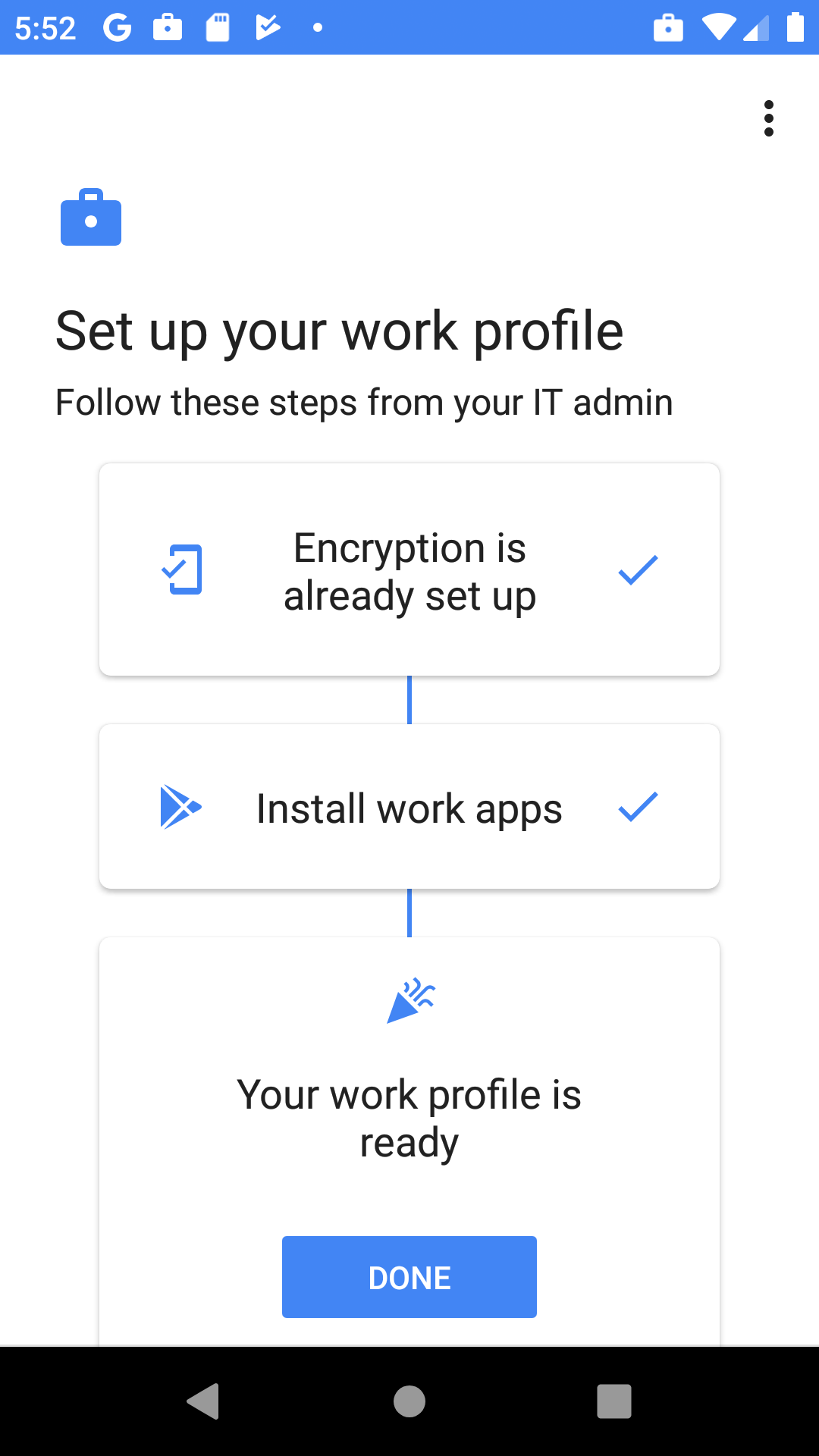
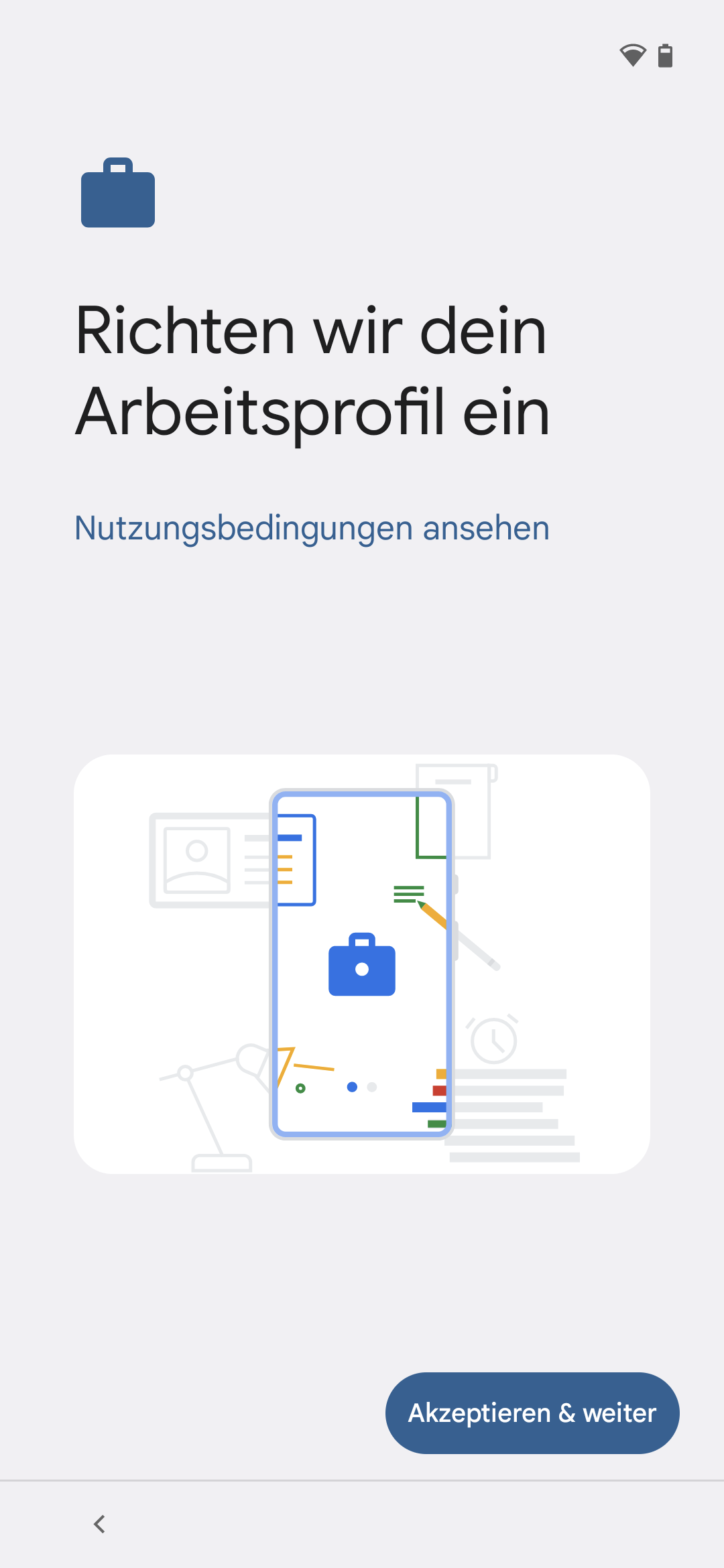
- A work profile is created on the device for the Enterprise profile.
- All configured applications, restrictions etc. are created and applied within the work profile.
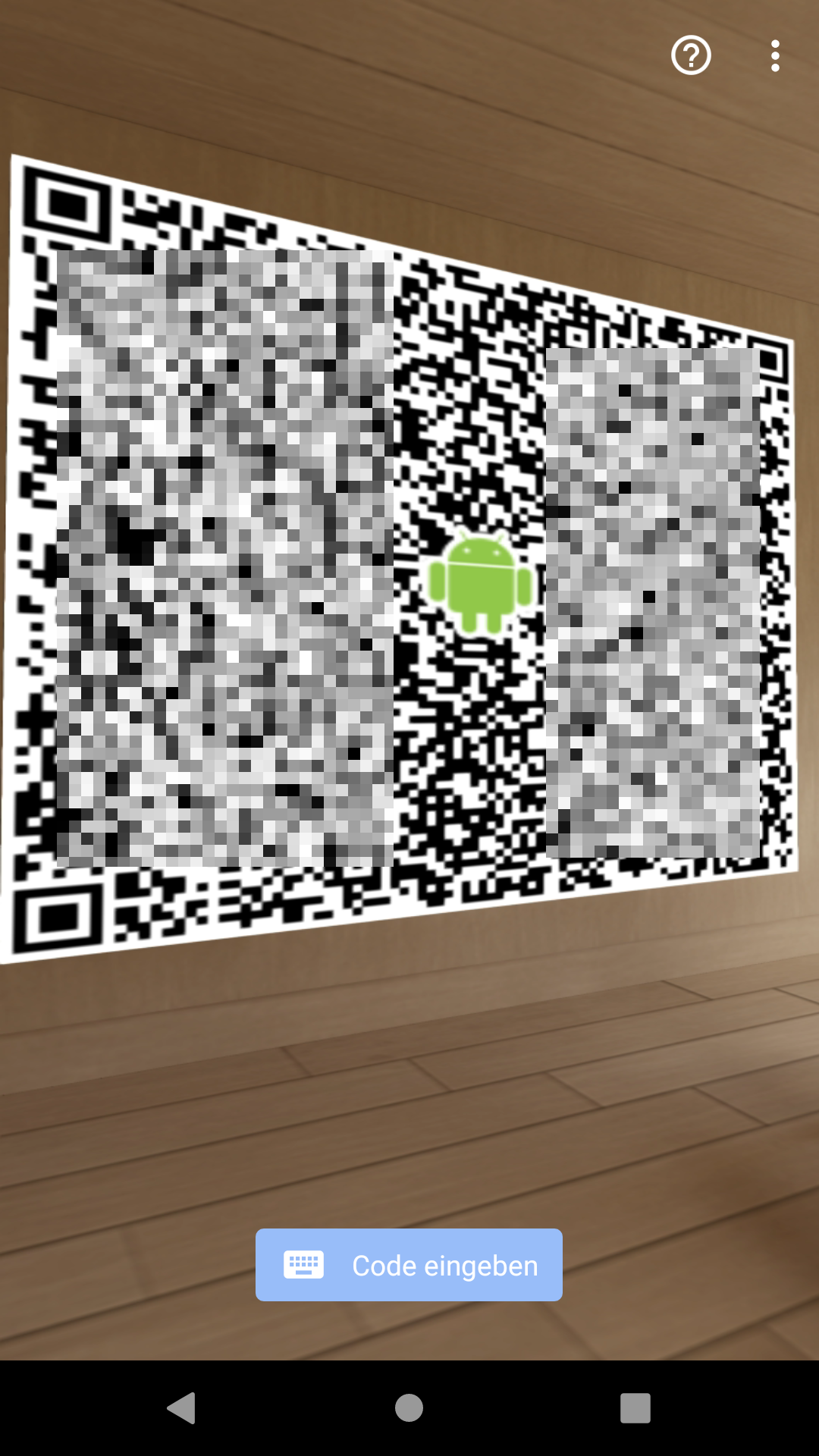
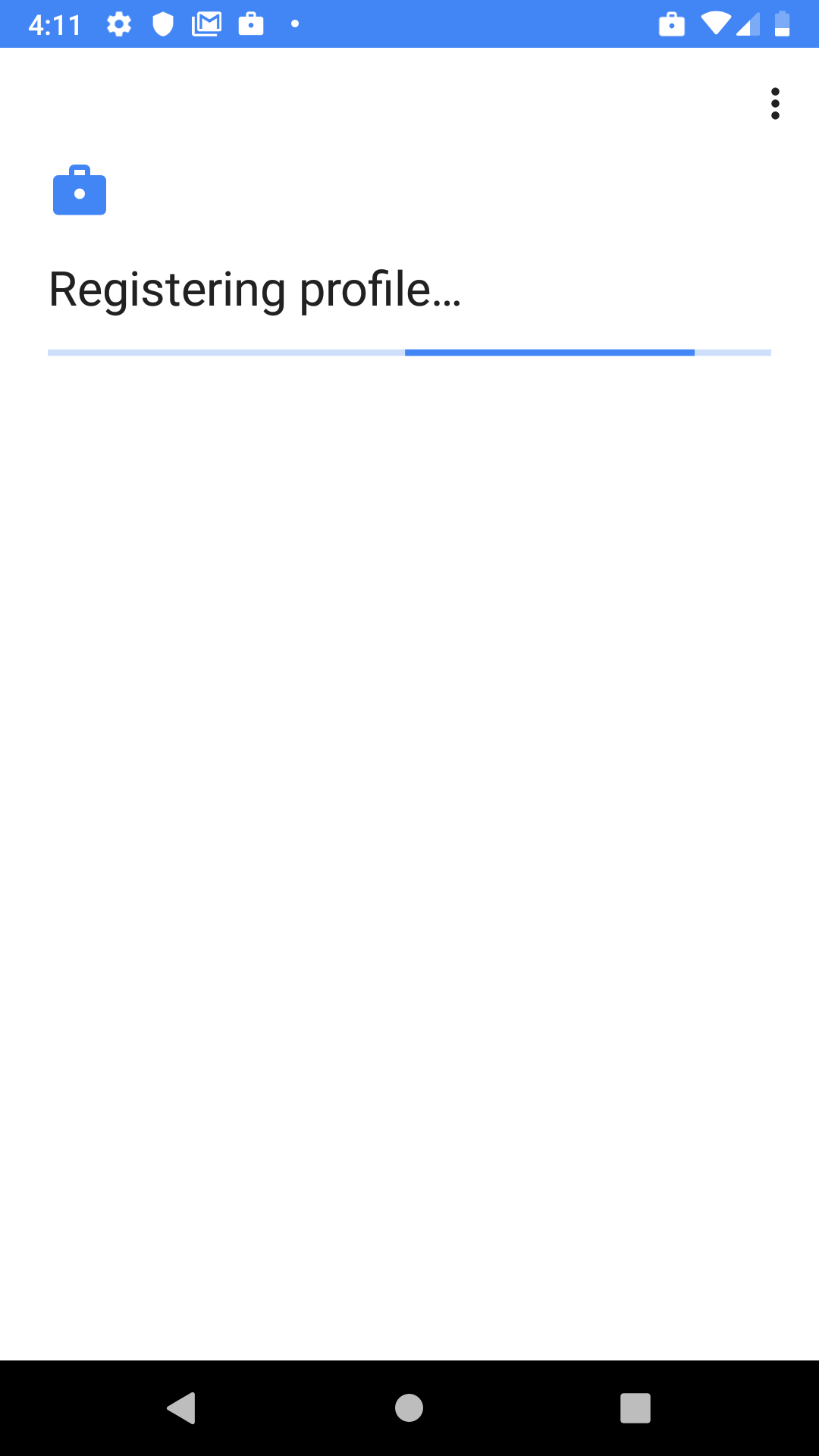
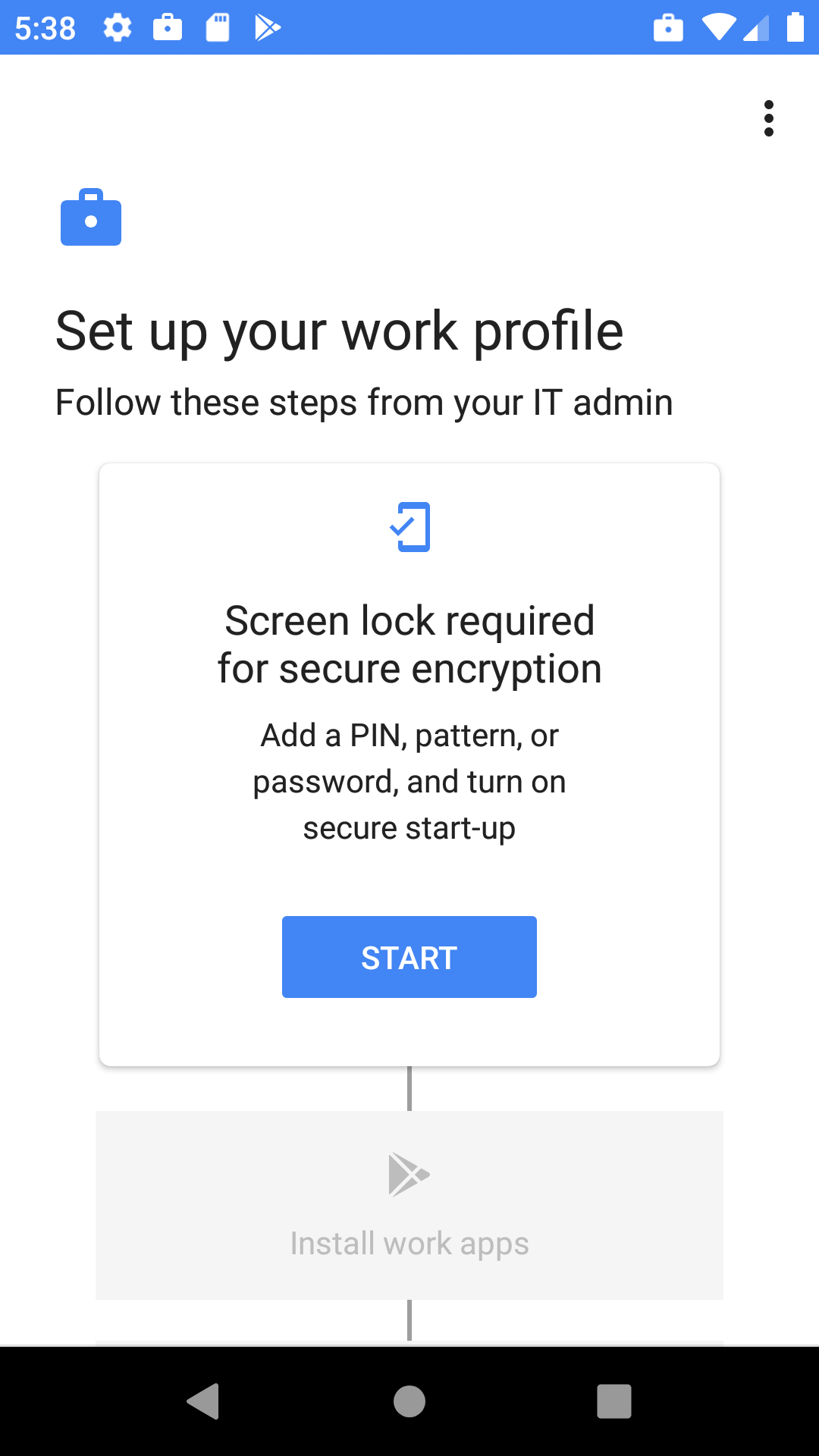
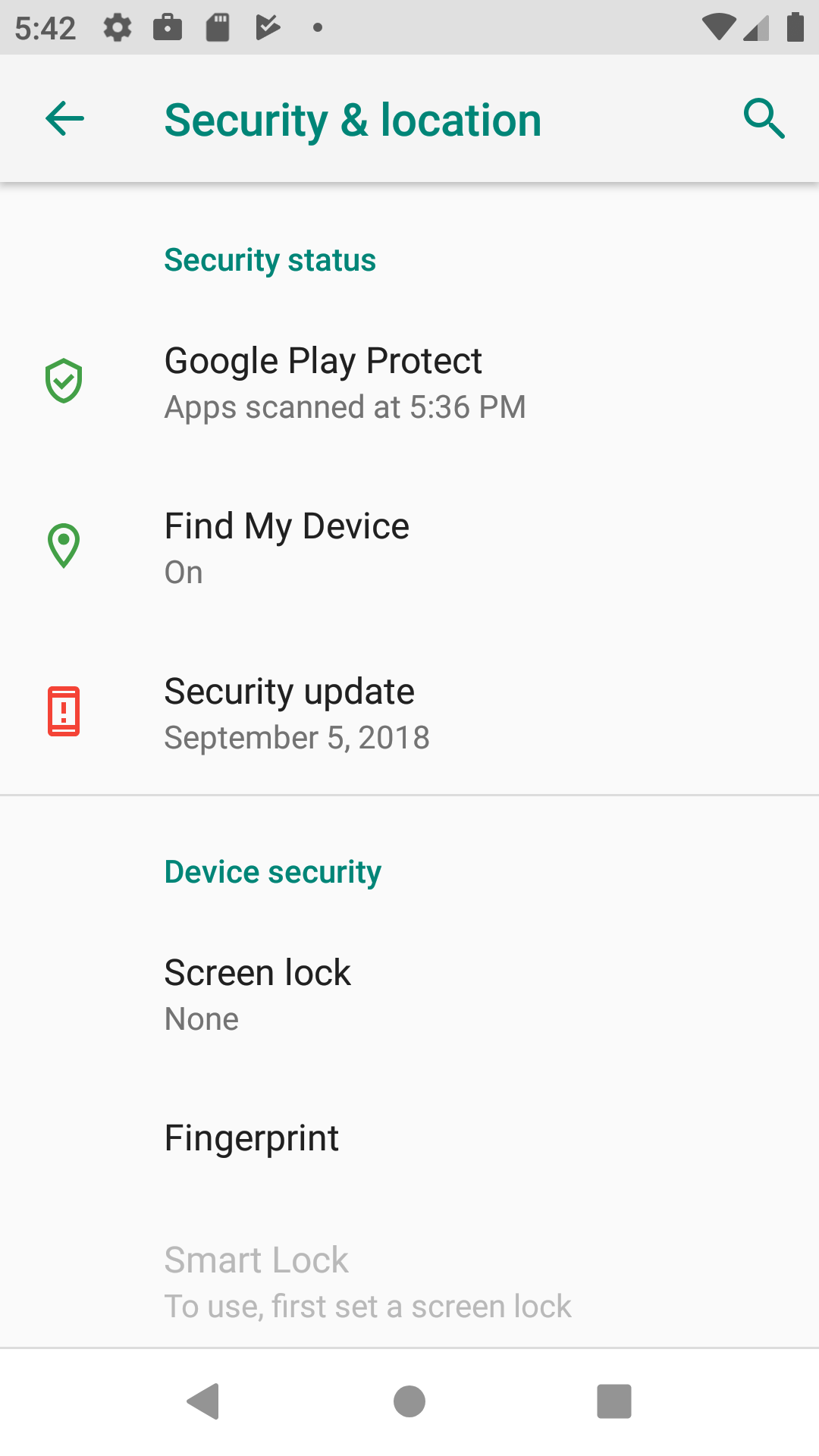
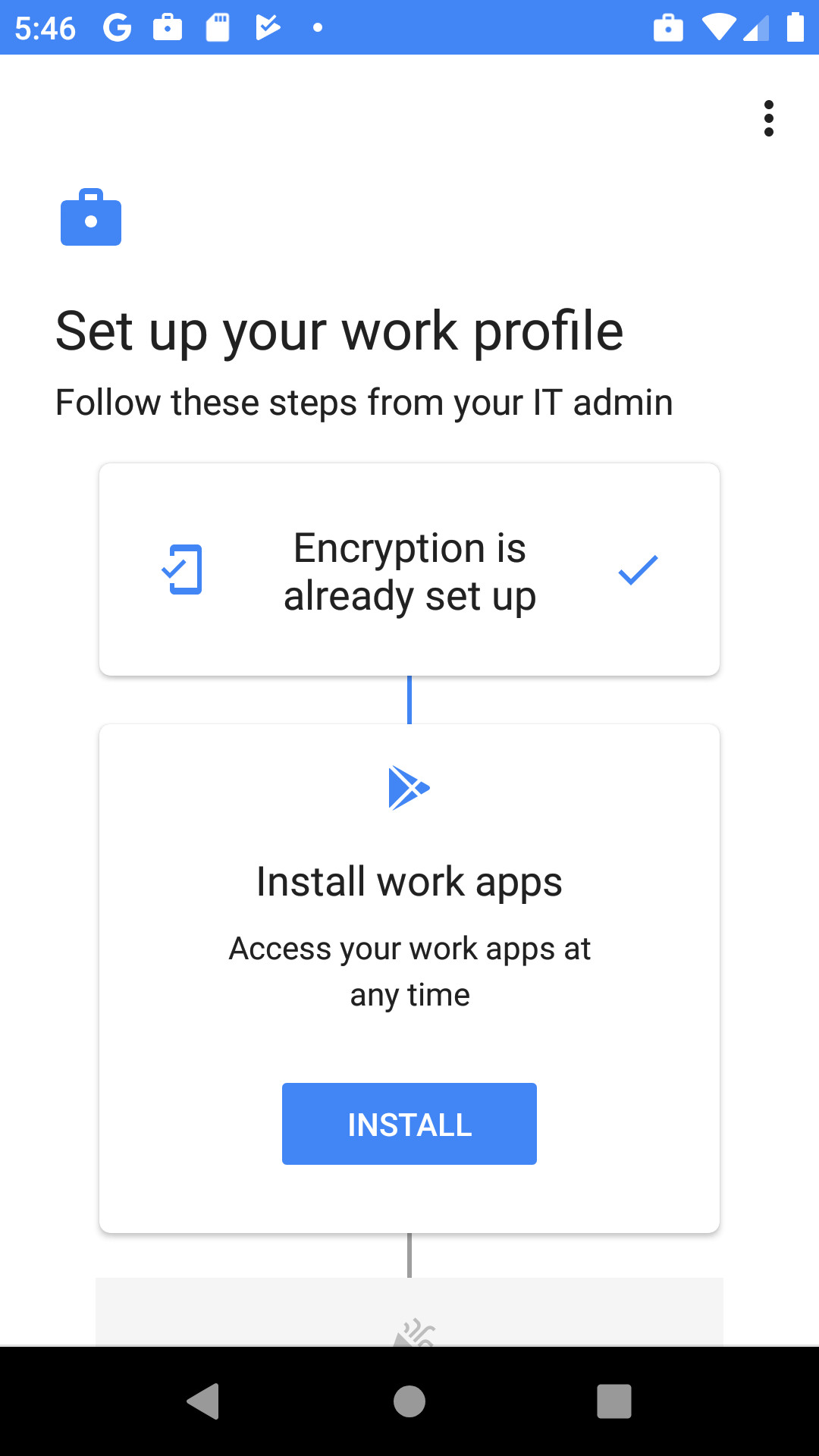
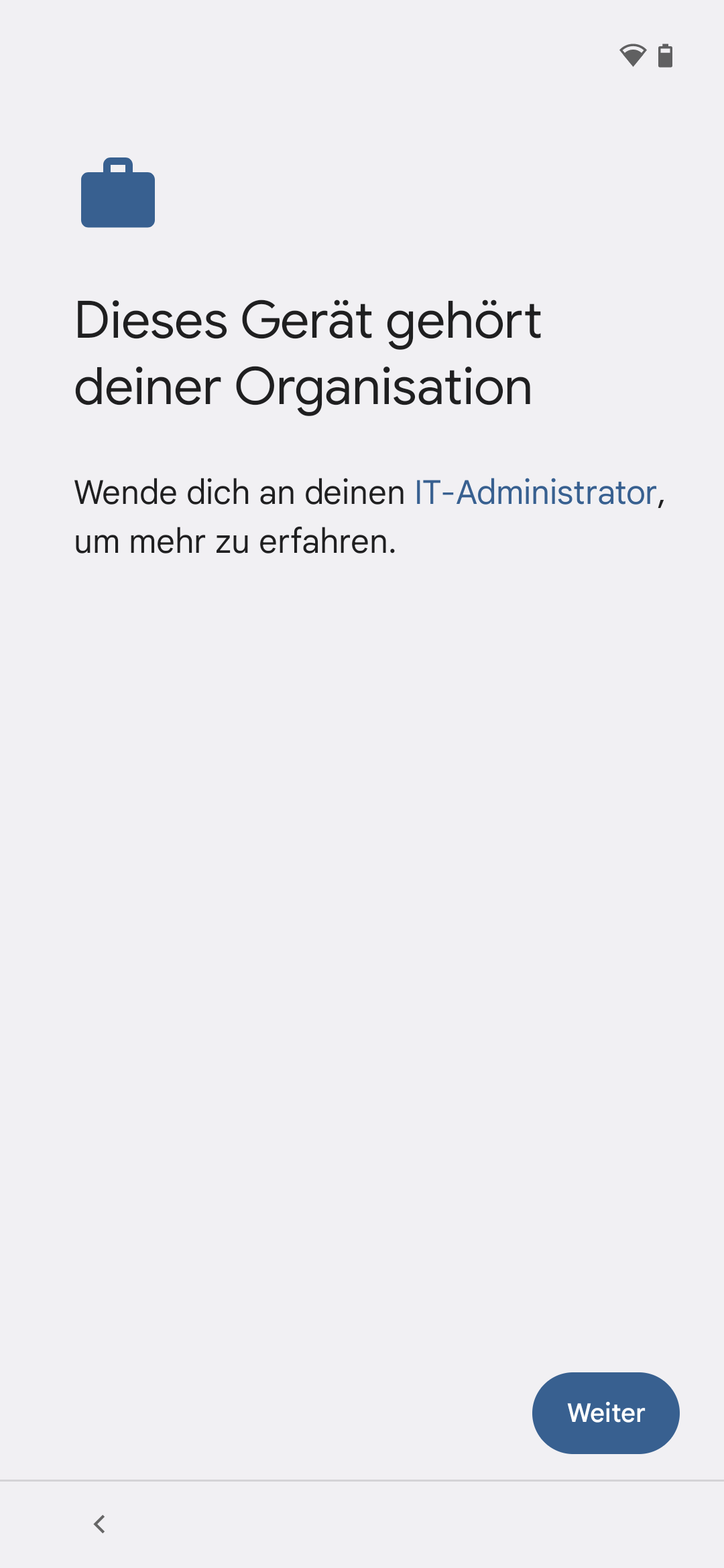
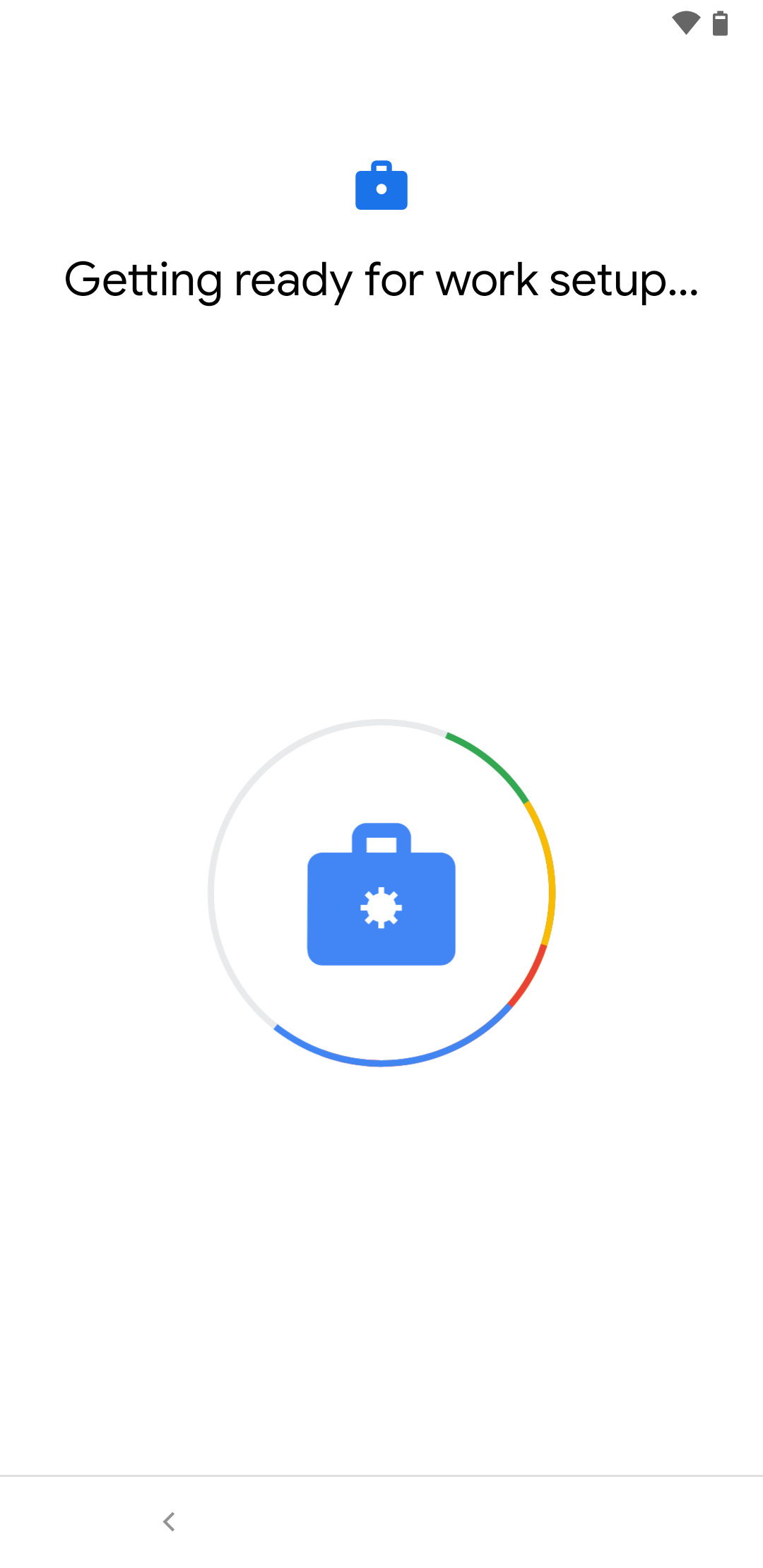
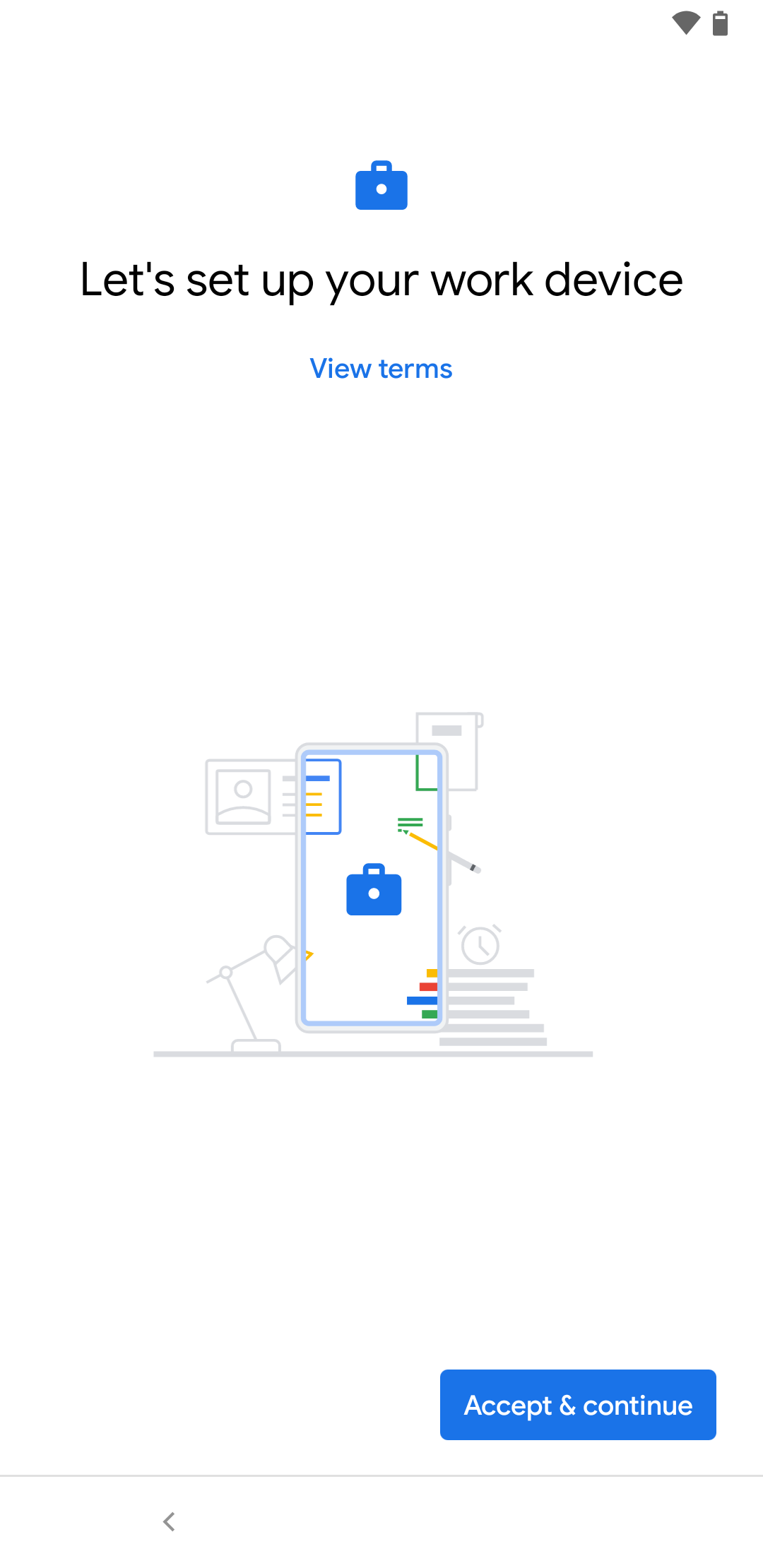
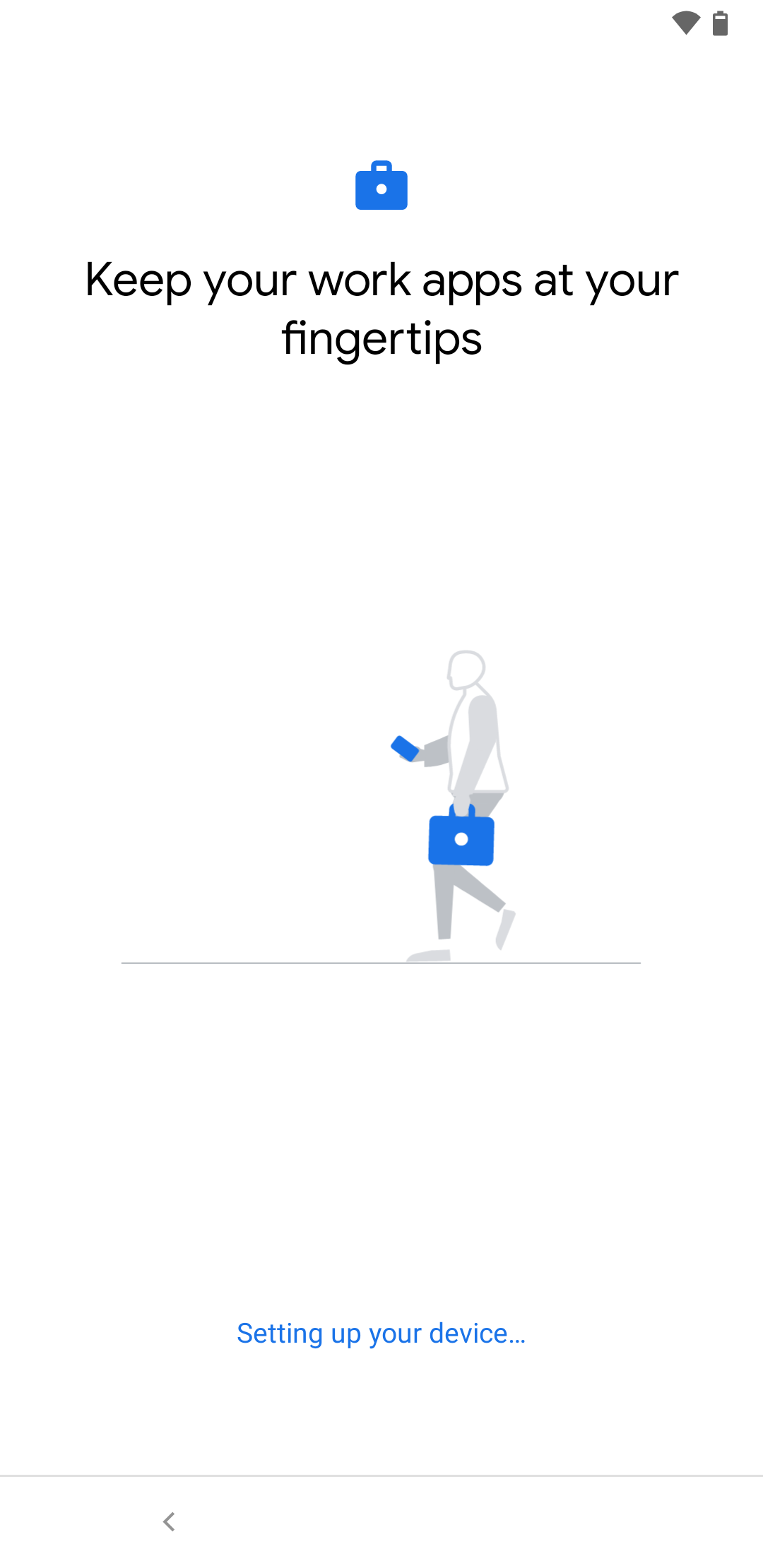
| 1. | 2. | 3. |
| Abb.1 | Abb.2 | Abb.3 |
| Abbildungen | ||
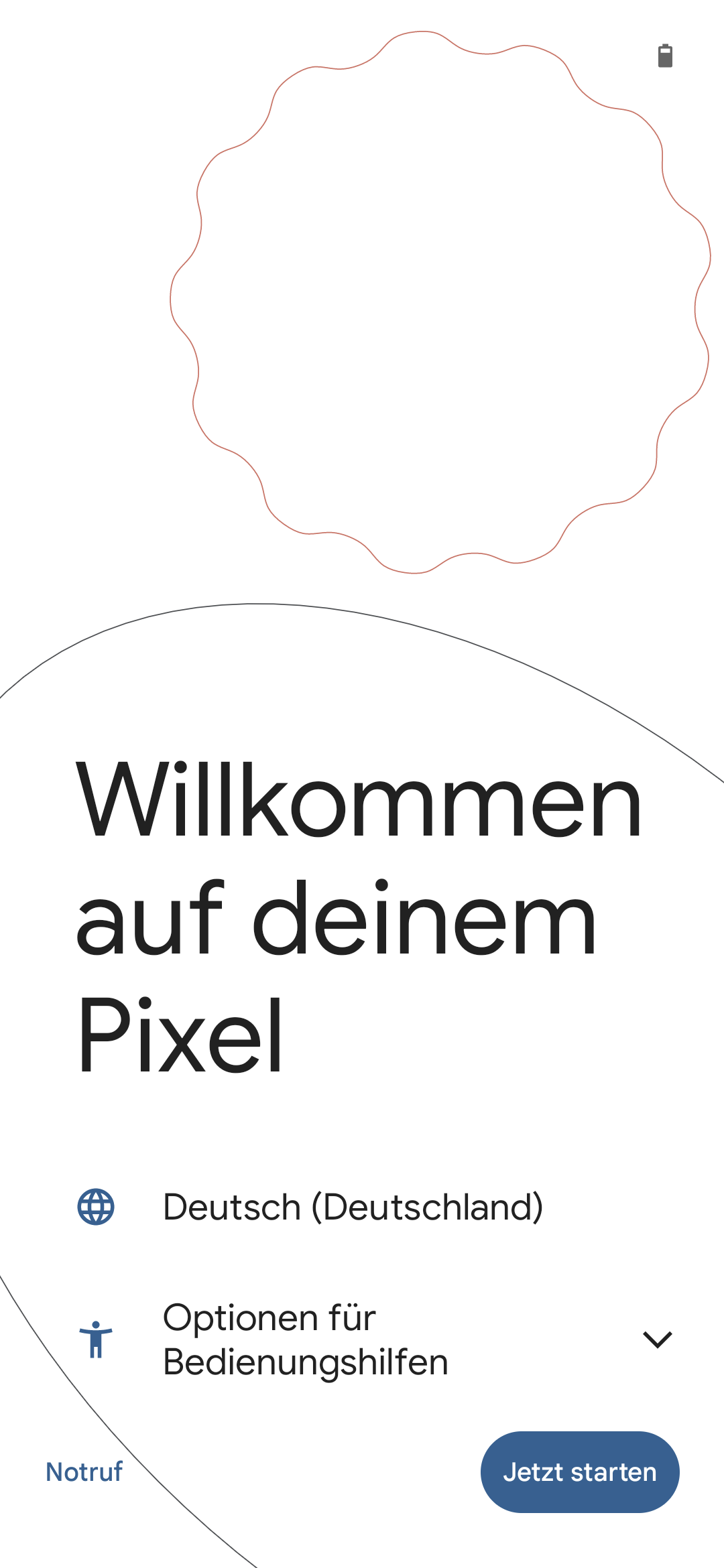
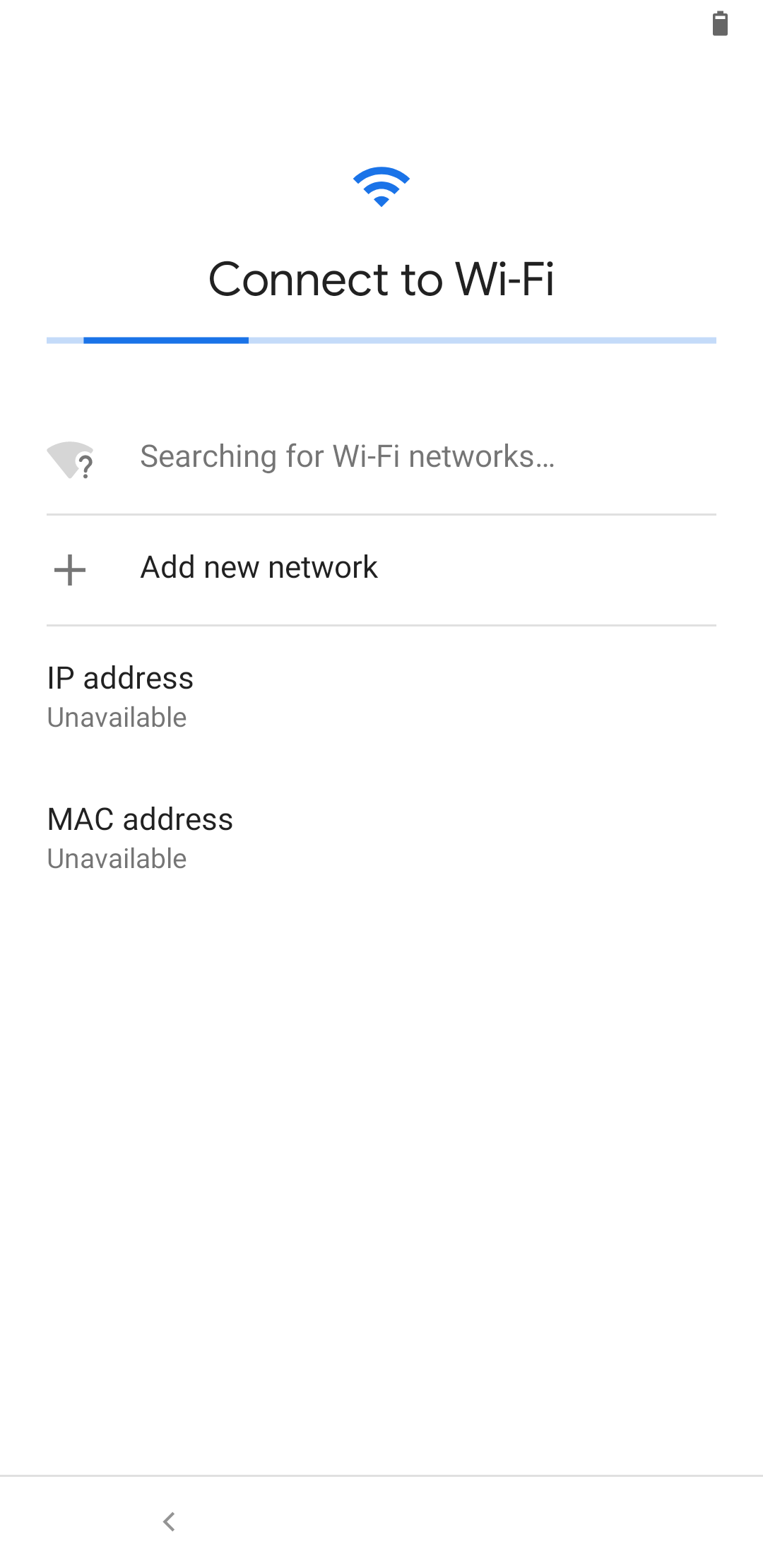
- Switching on for the first time or device reset (factory settings)
- Country settings selection
- Tapping the display 7 times quickly opens a QR code scanner
- Scanning of the profile QR code (see above)
- A work profile is created on the device
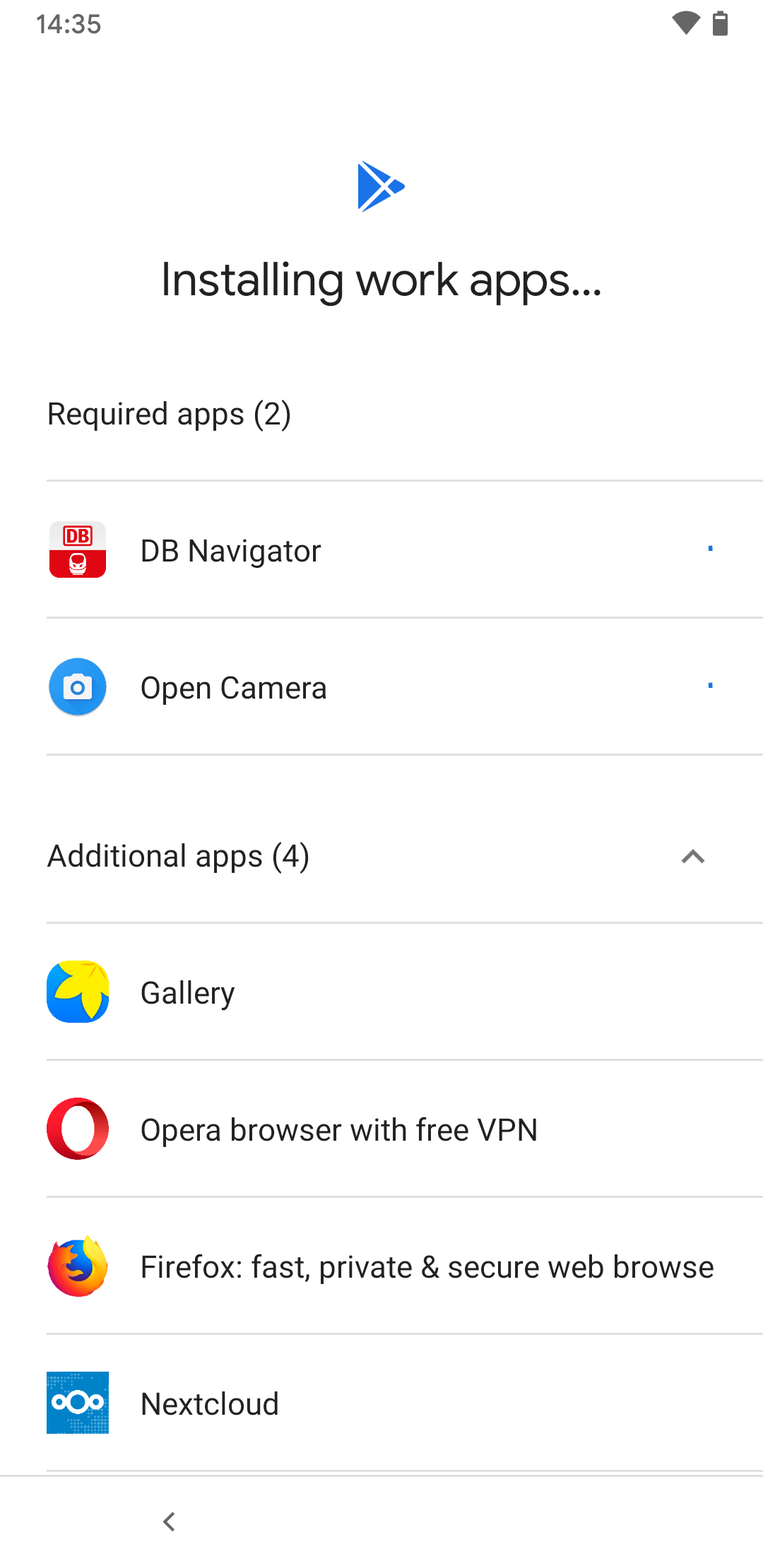
- All configured apps, restrictions, etc. are created and applied within the work profile.
- Apps are displayed in the "Business area and marked with a suitcase icon
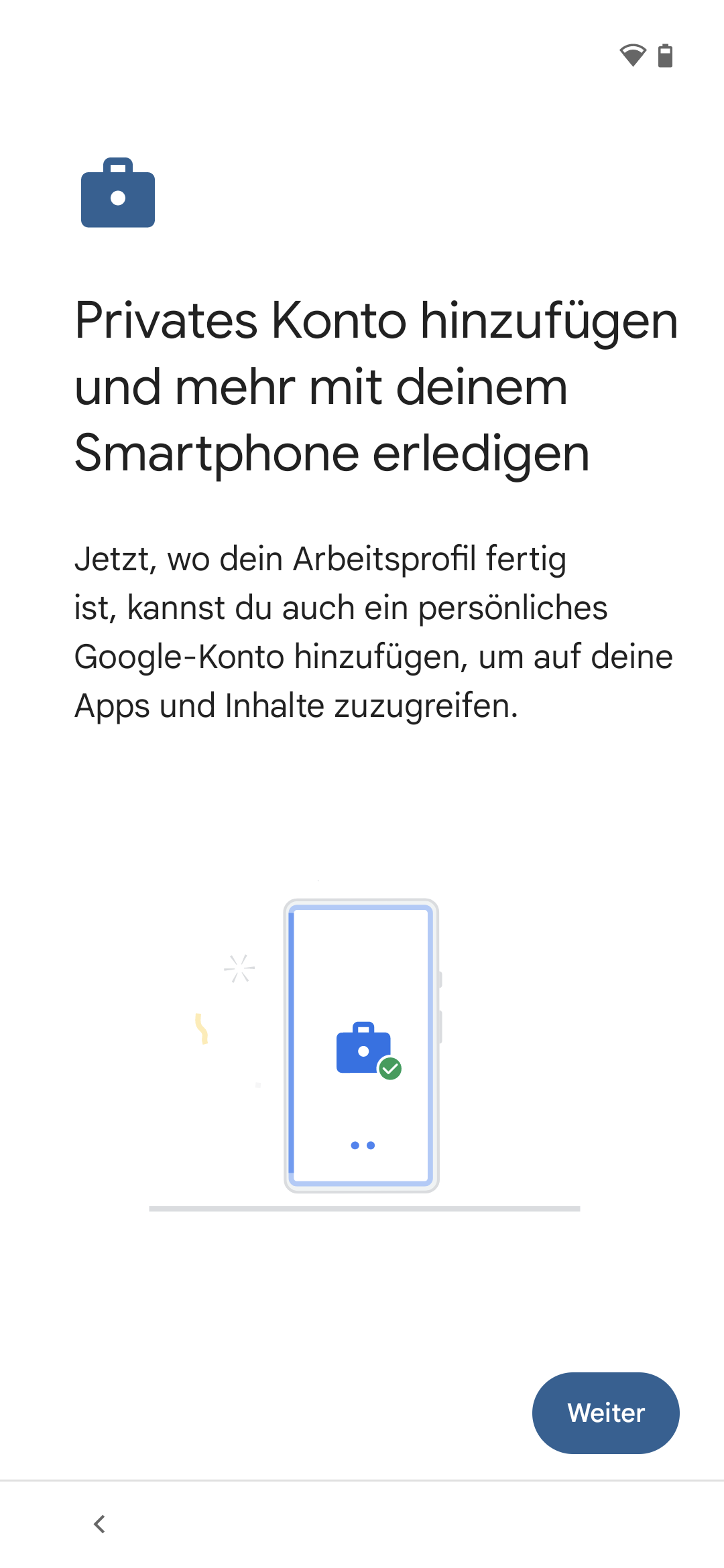
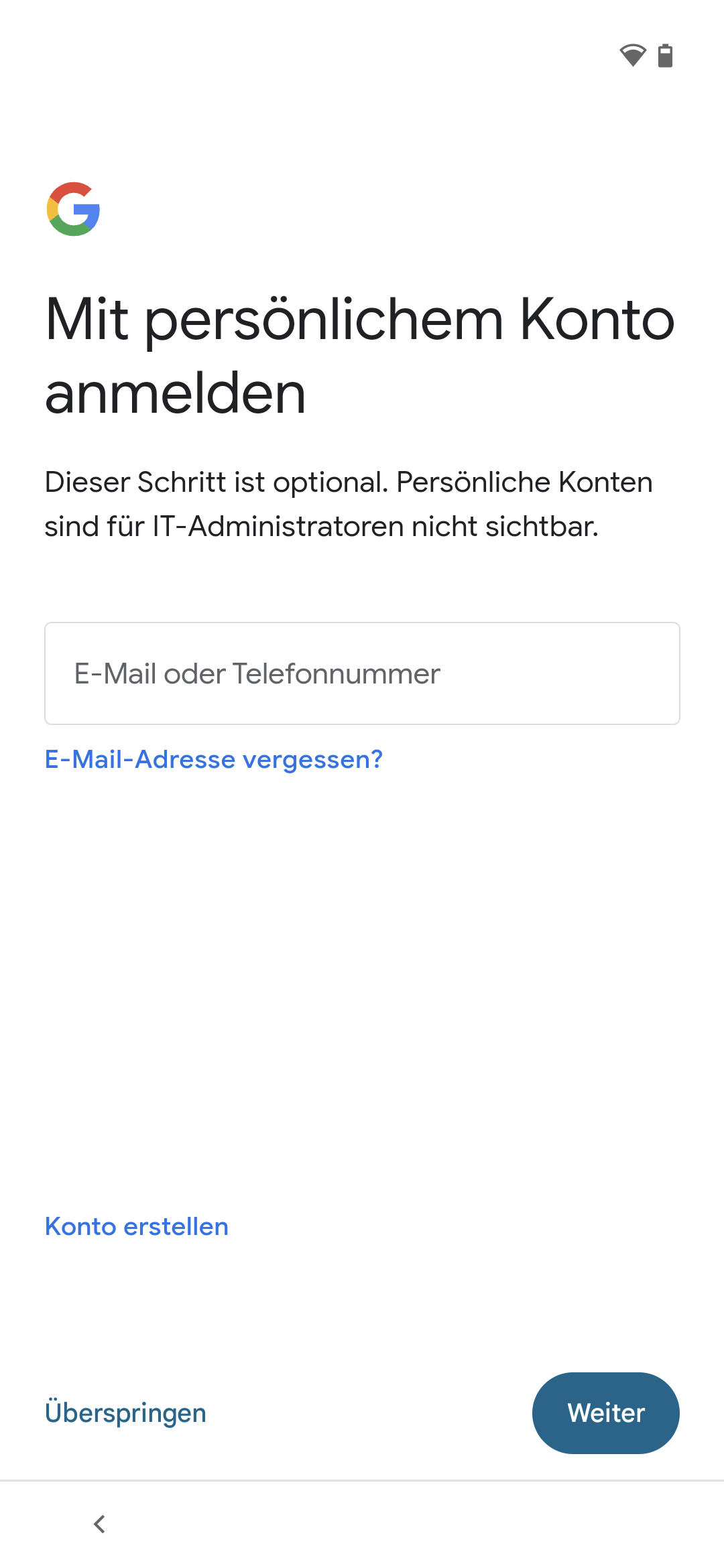
- A private Google account can be stored additionally
This step can also be done later- A private profile is created
- There is a separate area Private with its own playstore
Fully managed devices (COPE, Company Owned personal enabled) are connected directly to the Android Enterprise profile during initial setup or after a device reset. The link to a Google account and thus to an app store is defined by the assigned profile.
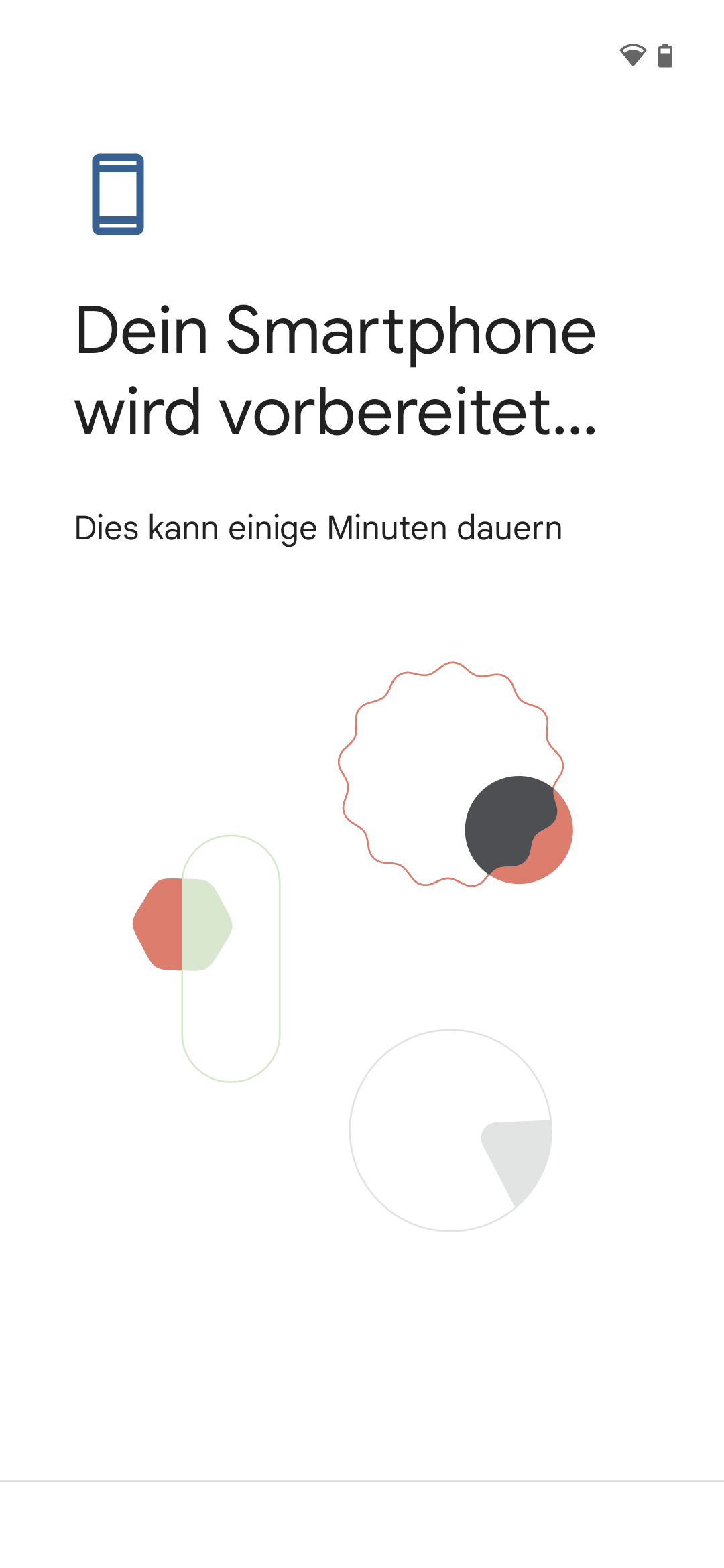
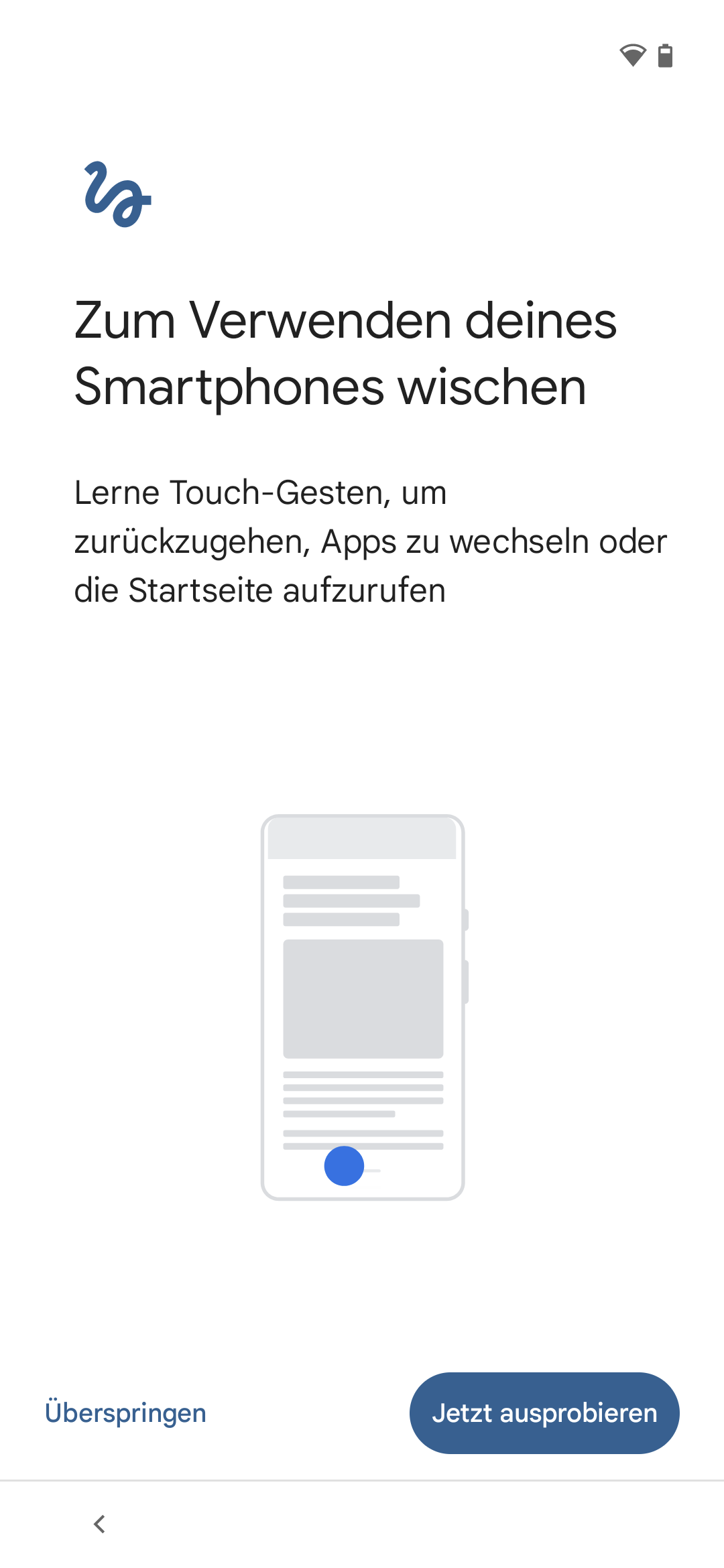
- Initial power-up or device reset (factory settings)
- Selection of regional settings
- Tap the display 7 times quickly to open a QR code scanner
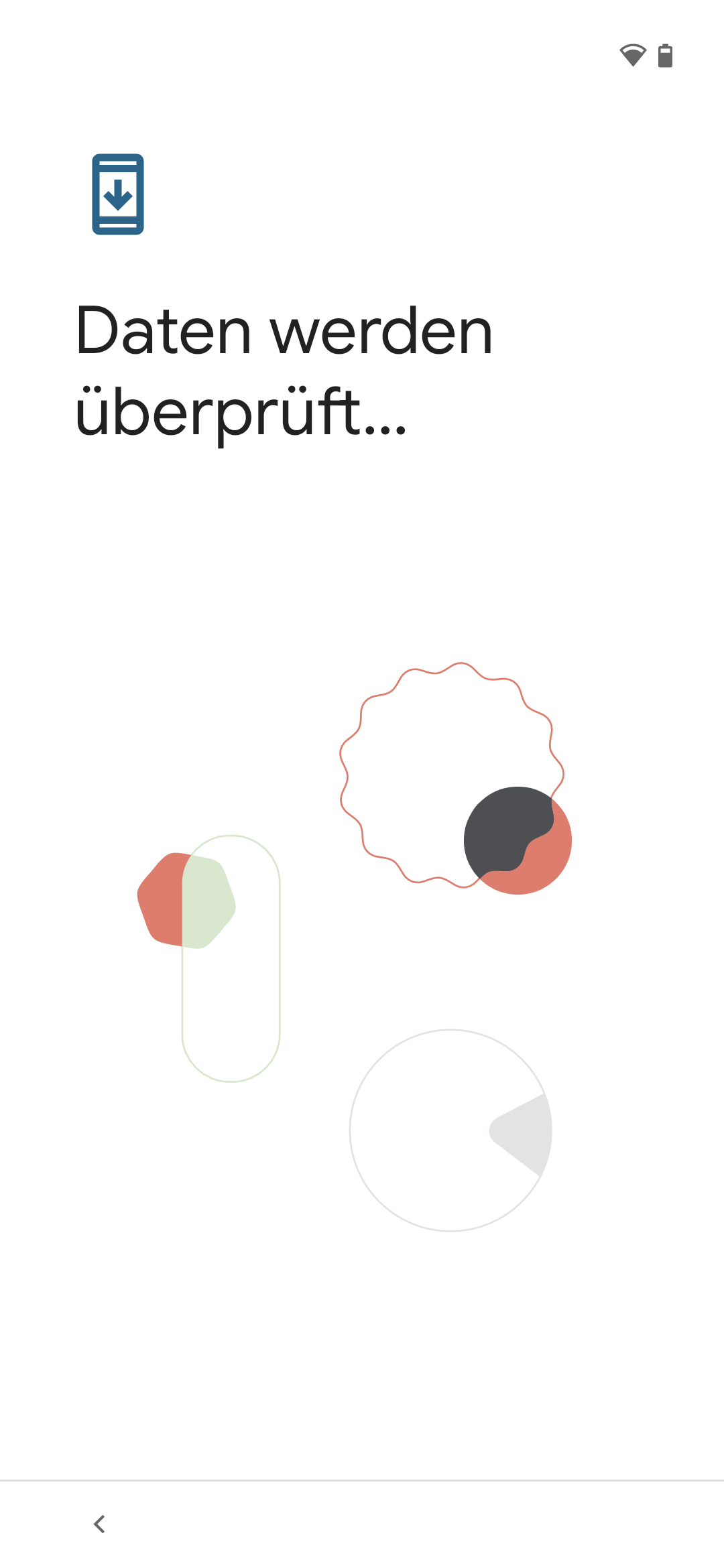
- Scanning the profile QR code (see above)
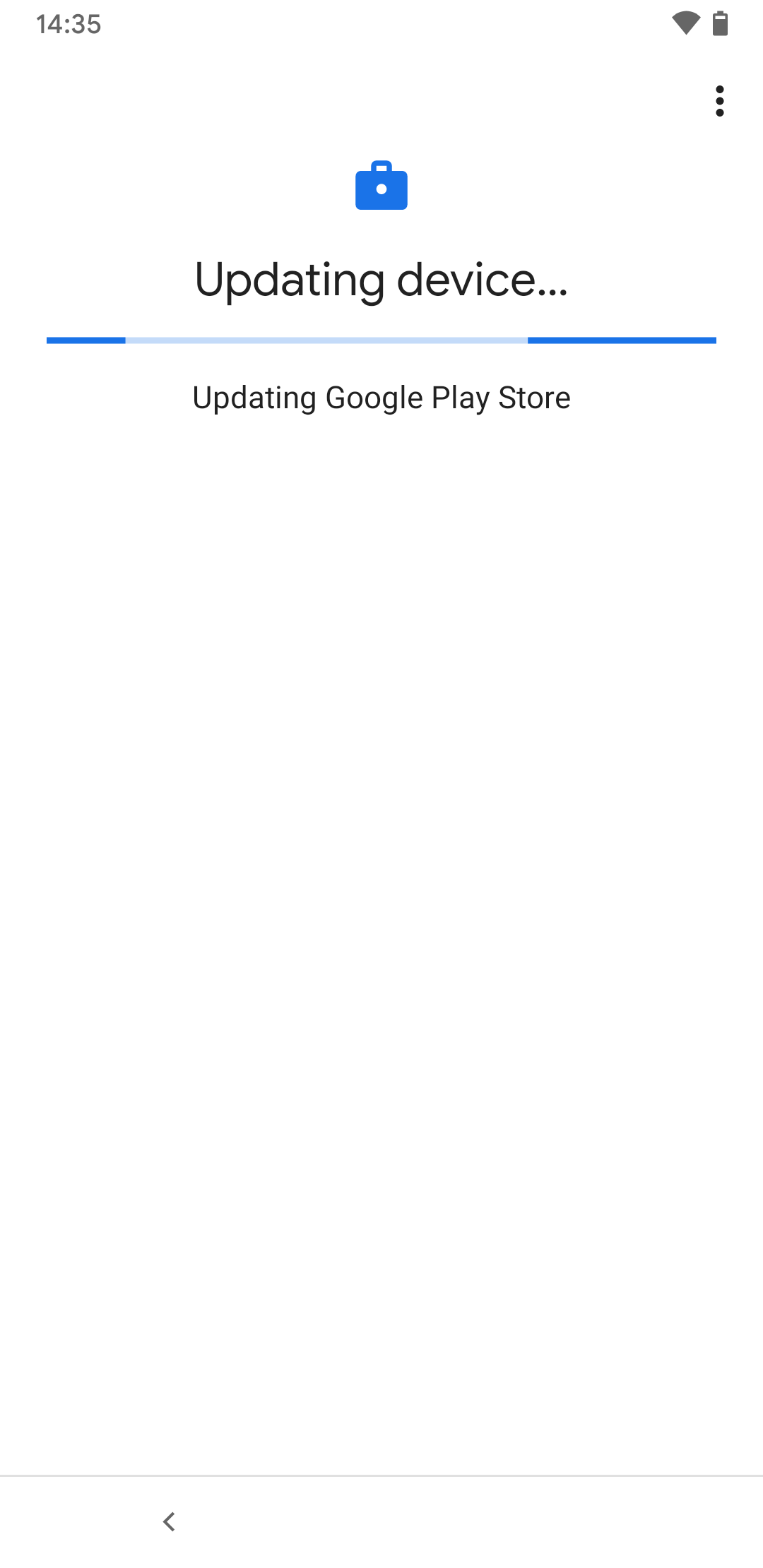
- The device is configured as a fully managed device.
- All policies, apss and restrictions stored in the profile will be applied directly to the device
This process may take a few minutes during the initial installation!
- All policies, apss and restrictions stored in the profile will be applied directly to the device
| 1. | 2. | 3. |
| Abb.1 | Abb.2 | Abb.3 |
| Abbildungen | ||

7 quick taps on the display opens a QR code scanner
Devices with Android ≤ 9 (Pie) already require a temporary WLAN connection to load a QR code scanner.
Zero touch devices
Registration in the menu
Either
- Add device to an existing configuration:
- Edit configuration: Click on the device tile (or via the hamburger menu in the device tile at the top right) / Edit)
- if necessary, select a new valid enrollment token Enrollment tokens are valid for a maximum of 30 days
- Select device(s) by IMEI or serial number
- Save information
or
- with the button Add configuration
- select enrollment token
- select customer
- Fill in other details (company name, contact details...)
- Select device(s) by IMEI or serial number
- Save details
The enrollment on the device itself is, depending on the configuration, exactly as described in the sections COPE, COBU or COSU.
Only the scanning of the enrollment token is omitted!
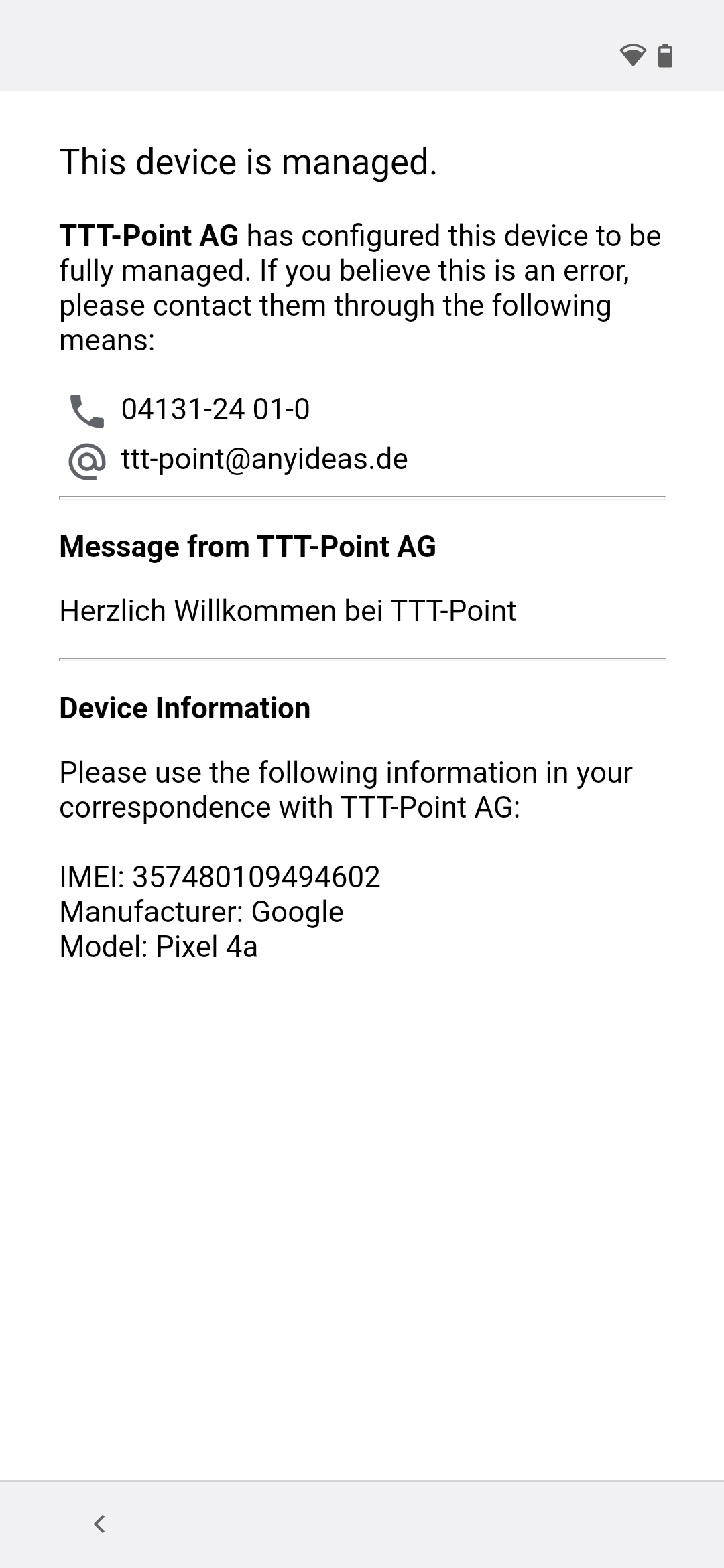
| Name | TTT-Point Zero Touch | Configuration name | [[Datei: ]] |
| Enrollment token | Profile: Selected profile | Token abCD12 | The selected enrollment token (as created in the Devices / Enroll new device menu) will be applied to all devices enrolled with this configuration.
notemptyFor security reasons for ZeroTouch Enrolment, only enrolment tokens that have been provided with a PIN can be selected.
| |
| Customer | SecurepointCustomer | The description for the customer as it was transmitted to the device retailer. If several Gmail addresses were linked to the zero touch portal, different descriptions can be selected here. | |
| Standard | Defines whether this configuration is the default or not. When is enabled, new zero touch devices are automatically added to this configuration unless another is specified Note: At least one configuration should be defined as default. | ||
| Company | TTT-Point | Freely selectable designation for the company to which this device is to be assigned. | |
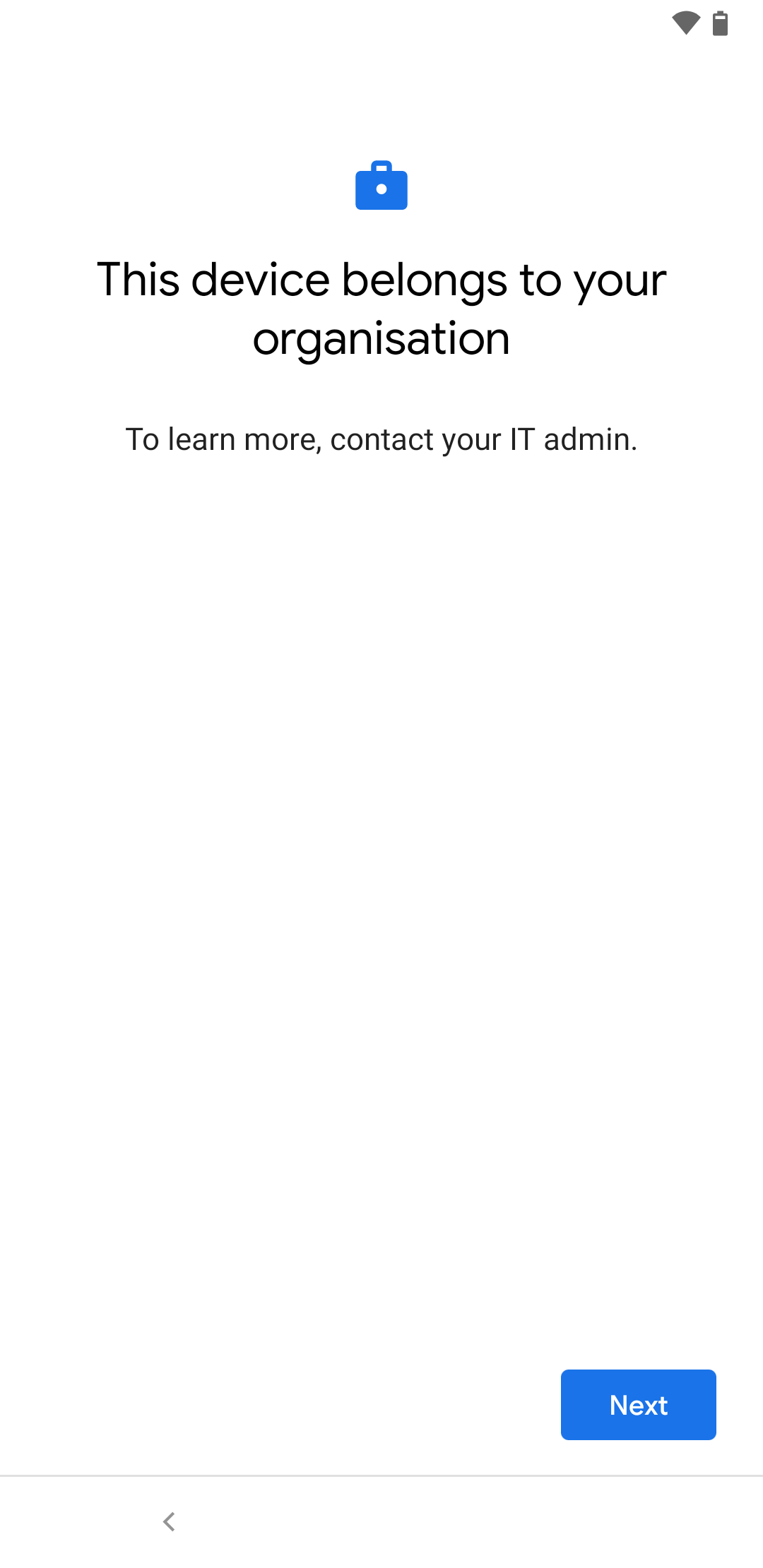
| admin@anyideas.de | Contact Email Address Displays on mobile during the setup process when IT Administrator is tapped on the "This device belongs to your organization" screen. | ||
| Phone number | 01234-56789 | Contact phone number display see above | |
| Custom message | Welcome to TTT-Point | Shown on the display during device setup | |
| Devices | 123456789012345 | This configuration can be assigned to devices based on their IMEI or serial number | |
| Save | Saves the configuration | ||
| Zero touch configuration with assigned device | 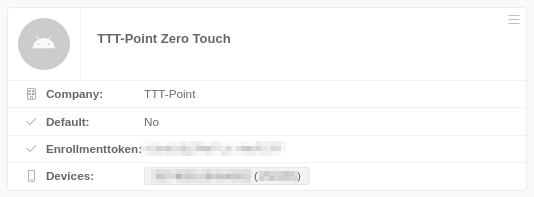 | ||
Closing by user
The configuration from the profile is then automatically applied to the device.
Remove devices from Mobile Security management
Fully managed devices
Under / Delete in the respective device tile the administration can be removed from the devices:
- All data will be deleted.
- The devices are reset automatically and immediately to their factory status!