Lauritzl verschob die Seite UTM/VPN/IPSec-Troubleshooting nach UTM/VPN/IPSec-Troubleshooting v12.2 Markierung: Neue Weiterleitung |
K Weiterleitung auf UTM/VPN/IPSec-Troubleshooting v12.2 entfernt Markierung: Weiterleitung entfernt |
||
| Zeile 1: | Zeile 1: | ||
# | {{Set_lang}} | ||
{{#vardefine:headerIcon|spicon-utm}} | |||
{{:UTM/VPN/IPSec-Troubleshooting.lang}} | |||
</div>{{TOC2|Bild={{#var:Log-Level--Bild}}|cap={{#var:Log-Level--val}} }}{{Select_lang}} | |||
{{Header|12.2.3| | |||
* {{#var:neu--Log-Level per GUI}} | |||
|[[UTM/VPN/IPSec-Troubleshooting_v12.2 | 12.2]] | |||
[[UTM/VPN/IPSec-Troubleshooting_v11.7 | 11.7]] | |||
[[UTM/VPN/IPSec-Troubleshooting_v11.6 | 11.6.12]] | |||
}} | |||
== {{#var:Vorbereitung}} == | |||
{{h3| {{#var:Reiter}} {{#var:Log}} | {{Reiter| {{#var:Log}} }} }} | |||
<div class="Einrücken"> | |||
{{#var:Log-Level--desc}} | |||
{{Hinweis-neu| !! {{#var:Log-Level--Hinweis}}|class=flex }} | |||
{| class="sptable2 pd5 block zh1" | |||
|- | |||
| rowspan=4" class=mw7| {{b|Log-Level:}} <br>{{Hinweis-neu|{{#var:Neu ab}} 12.2.3|12.2.3|status=neu}} || {{Button|{{#var:Rudiemntär}}|dr|class=mw13}} || {{#var:Rudiemntär--desc}} | |||
<!-- | |||
| class="Bild" rowspan="5" | {{Bild | {{#var:Log-Level--Bild}}|{{#var:Log-Levelg--cap}} }} | |||
--> | |||
|- | |||
| {{Button|{{#var:Ausführlich}}|dr|class=mw13}} || {{#var:Ausführlich--desc}} | |||
|- | |||
| {{Button|{{#var:Sehr Ausführlich}}|dr|class=mw13}} || {{#var:Sehr Ausführlich--desc}}<li class="list--element__alert list--element__warning">{{#var:Sehr Ausführlich--Hinweis}}</li> | |||
|- | |||
| {{Button|{{#var:Benutzerdefiniert}}|dr|class=mw13}} || {{#var:Benutzerdefiniert--desc}} | |||
|- class="Leerzeile" | |||
| colspan="3" | {{#var:Speichern und neustarten--desc}} | |||
<li class="list--element__alert list--element__warning">{{#var:Speichern und neustarten--Hinweis}}</li> | |||
|} | |||
</div> | |||
<div class=h-top>{{#var:Alternative}}</div> | |||
=== {{#var:CLI-Befehl}} === | |||
<div class="Einrücken"> | |||
{{#var:CLI-Befehl--desc}} | |||
<li class="list--element__alert list--element__warning">{{#var:IPSec neu starten}} }}<p>{{#var:IPSec neu starten--Menu}}</p></li> | |||
</div> | |||
<div class=h-top>{{#var:Alternative}}</div> | |||
=== {{#var:extc-Variable setzen}} === | |||
<div class="Einrücken">{{#var:extc-Variable setzen--desc}} | |||
<li class="list--element__alert list--element__warning">{{#var:IPSec neu starten}} }}<p>{{#var:IPSec neu starten--Menu}}</p></li> | |||
</div> | |||
<div class=h-top>{{#var:Alternative}}</div> | |||
=== SSH === | |||
<div class="Einrücken">{{#var:per SSH--desc}}<li class="list--element__alert list--element__positiv">{{#var:per SSH--Hinweis}}</li> | |||
* {{#var:per SSH bis 12.1.8--desc}} | |||
* {{#var:per SSH ab 12.2--desc}} | |||
</div> | |||
</div><br clear=all> | |||
== {{#var:IKEv1 Troubleshooting}} == | |||
{{Bild | {{#var:IKEv1 Troubleshooting--Bild}}|{{#var:IKEv1 Troubleshooting--cap}} }} | |||
{{#var:IKEv1 Troubleshooting--desc}} | |||
<br clear=all> | |||
=== {{#var:Phase 1}} === | |||
<div class="Einrücken"> | |||
==== {{#var:Der normale Verbindungsaufbau}} ==== | |||
{| class="sptable2 pd5 Einrücken" | |||
|- class="Leerzeile" | |||
| colspan="2" | {{#var:Der normale Verbindungsaufbau--desc}} | |||
|- | |||
! Dienst !! Nachricht | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">10[IKE]</span> <span class="log na">IKE_SA Standort_1_2[1] established between 198.51.100.75[198.51.100.75]...198.51.100.1[198.51.100.1]</span> | |||
|} | |||
==== {{#var:Falsches Proposal}} ==== | |||
{| class="sptable2 pd5 einrücken" | |||
|- class="Leerzeile" | |||
| colspan="2" | {{#var:Falsches Proposal--desc}} | |||
|- class="Leerzeile" | |||
| colspan="2" | '''{{#var:Initiator-Log}}''' | |||
|- | |||
! Dienst !! Nachricht | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">10[IKE]</span> <span class="log na">received NO_PROPOSAL_CHOSEN notify error</span> | |||
|- class="Leerzeile" | |||
| colspan="2" | '''{{#var:Responder-Log}}''' | |||
|- | |||
! Dienst !! Nachricht | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">05[CFG]</span> <span class="log na">selecting proposal:</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">05[CFG]</span> <span class="log na">no acceptable ENCRYPTION_ALGORITHM found</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">05[CFG]</span> <span class="log na">selecting proposal:</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">05[CFG]</span> <span class="log na">received proposals: IKE:BLOWFISH_CBC_256/HMAC_SHA2_512_256/PRF_HMAC_SHA2_512/MODP_8192</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">05[CFG]</span> <span class="log na">configured proposals:IKE:AES_CBC_128/HMAC_SHA2_256_128/PRF_HMAC_SHA2_256/MODP_2048,IKE:AES_CBC_128/AES_CBC_192/AES_CBC_256/3DES_CBC/CAMELLIA_CBC_128/CAMELLIA_CBC_192/CAMELLIA_CBC_256/AES_CTR_128/AES_CTR_192/AES_CTR_256/CAMELLIA_CTR_128/CAMELLIA_CTR_192/CAMELLIA_CTR_256/HMAC_MD5_96/HMAC_SHA1_96/HMAC_SHA2_256_128/HMAC_SHA2_384_192/HMAC_SHA2_512/AES_XCBC_96/AES_CMAC_96/PRF_HMAC_MD5/PRF_HMAC_SHA1/PRF_HMAC_SHA2_256/PRF_HMAC_SHA2_512/256/AES_XCBC_96/AES_CMAC_96/PRF_AES128_CMAC/MODP_2048/MODP_2048_224/MODP_2048_256/MODP_1536/MODP_3072/MODP_4096/MODP_8192/MODP_1024/MODP_1024_160/ECP_256/ECP_384/ECP_512/ECP_224/ECP_192/ECP_224_BP/ECP_256_BP/ECP_384_BP_ECP_512_BP,IKE:AES_GCM_8_128/AES_GCM_8_192/AES_GCM_8_256/AES_GCM_12_128/AES_GCM_12_192/AES_GCM_12_256/AES_GCM_16_128/AES_GCM_16_192/AES_GCM_16_256/PRF_HMAC_MD5/PRF_HMAC_SHA1/PRF_HMAC_SHA2_256/PRF_HMAC_SHA2_384/PRF_HMAC_SHA2_512/PRF_AES128_XCBC/PRF_AES128_CMAC/MODP_2048/MODP_2048_224/MODP_2048_256/MODP_1536/MODP_3072/MODP_4096/MODP_8192/MODP_1024/MODP_1024_160/ECP_256/ECP_384/ECP__521/ECP_224/ECP_192/ECP_224_BP/ECP_256_BP/ECP_384_BP/ECP_512_BP</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">10[IKE]</span> <span class="log na">received proposals inacceptable</span> | |||
|} | |||
==== {{#var:Falsche Remote-Gateway-Adresse}} ==== | |||
{| class="sptable2 pd5 einrücken" --> | |||
|- class="Leerzeile" | |||
| colspan="2" | {{#var:Falsche Remote-Gateway-Adresse--desc}} | |||
|- class="Leerzeile" | |||
| colspan="2" | '''{{#var:Responder-Log}}''' | |||
|- | |||
! Dienst !! Nachricht | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">11[CFG]</span> <span class="log na">looking for an ike config for 198.51.100.75...195.51.100.1</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">11[IKE]</span> <span class="log na">no IKE config found for 198.51.100.75...195.51.100.1, sending NO_PROPOSAL_CHOSEN</span> | |||
|} | |||
==== {{#var:Falsche ID Initiator}} ==== | |||
{| class="sptable2 pd5 einrücken" | |||
|- class="Leerzeile" | |||
| colspan="2" | {{#var:Falsche ID Initiator--desc}} | |||
|- class="Leerzeile" | |||
| colspan="2" | '''{{#var:Initiator-Log}}''' | |||
|- | |||
! Dienst !! Nachricht | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">09[IKE]</span> <span class="log na">received AUTHENTICATION_FAILED error notify</span> | |||
|- class="Leerzeile" | |||
| colspan="2" | '''{{#var:Responder-Log}}''' | |||
|- | |||
! Dienst !! Nachricht | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">07[CFG]</span> <span class="log na">looking for pre-shared key peer configs matching 198.51.100.75...198.51.100.1[blubb]</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">07[IKE]</span> <span class="log na">no peer config found</span> | |||
|} | |||
==== {{#var:Falsche ID Responder}} ==== | |||
{| class="sptable2 pd5 einrücken" | |||
|- class="Leerzeile" | |||
| colspan="2" | {{#var:Falsche ID Responder--desc}} | |||
|- class="Leerzeile" | |||
| colspan="2" | '''{{#var:Initiator-Log}}''' | |||
|- | |||
! Dienst !! Nachricht | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">05[IKE]</span> <span class="log na">IDir 'blubb' does not match to '198.51.100.75'</span> | |||
|} | |||
==== {{#var:Falscher PSK}} ==== | |||
{| class="sptable2 pd5 einrücken" | |||
|- class="Leerzeile" | |||
| colspan="2" | {{#var:Falscher PSK--desc}} | |||
|- class="Leerzeile" | |||
| colspan="2" | '''{{#var:Initiator-Log}}''' | |||
|- | |||
! Dienst !! Nachricht | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">15[IKE]</span> <span class="log na">message parsing failed</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">15[IKE]</span> <span class="log na">ignore malformed INFORMATIONAL request</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">15[IKE]</span> <span class="log na">INFORMATIONAL_V1 request with message ID 1054289493 processing failed</span> | |||
|- class="Leerzeile" | |||
| colspan="2" | '''{{#var:Responder-Log}}''' | |||
|- | |||
! Dienst !! Nachricht | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">14[IKE]</span> <span class="log na">message parsing failed</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">14[IKE]</span> <span class="log na">ID_PROT request with message ID 0 processing failed</span> | |||
|} | |||
==== {{#var:Falscher RSA-Key Initiator}} ==== | |||
{| class="sptable2 pd5 einrücken" | |||
|- class="Leerzeile" | |||
| colspan="2" | {{#var:Falscher RSA-Key Initiator--desc}} | |||
|- class="Leerzeile" | |||
| colspan="2" | '''{{#var:Initiator-Log}}''' | |||
|- | |||
! Dienst !! Nachricht | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">15[IKE]</span> <span class="log na">authentication of 'Filiale' (myself) succesful</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">16[IKE]</span> <span class="log na">received AUTHENTICATION_FAILED error notify</span> | |||
|- class="Leerzeile" | |||
| colspan="2" | '''{{#var:Responder-Log}}''' | |||
|- | |||
! Dienst !! Nachricht | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">14[CFG]</span> <span class="log na">looking for RSA signature peer configs matching 198.51.100.75...198.51.100.1[Filiale]</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">14[CFG]</span> <span class="log na">candidate "Standort1_4", match: 1/20/28 (me/other/ike)</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">14[CFG]</span> <span class="log na">selected peer config "Standort1_4"</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">14[CFG]</span> <span class="log na">using trusted certificate "Filiale"</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">14[IKE]</span> <span class="log na">ignature validation failed, looking for another key</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">14[IKE]</span> <span class="log na">no trusted RSA public key found for 'Filiale'</span> | |||
|} | |||
==== {{#var:Falscher RSA-Key Responder}} ==== | |||
{| class="sptable2 pd5 einrücken" | |||
|- class="Leerzeile" | |||
| colspan="2" | {{#var:Falscher RSA-Key Responder--desc}} | |||
|- class="Leerzeile" | |||
| colspan="2" | '''{{#var:Initiator-Log}}''' | |||
|- | |||
! Dienst !! Nachricht | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">16[CFG]</span> <span class="log na">authentication of 'Filiale' (myself) succesful</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">16[IKE]</span> <span class="log na">using trusted certificate "Zentrale"</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">16[IKE]</span> <span class="log na">signature validation failed, looking for another key</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">15[IKE]</span> <span class="log na">no trusted RSA public key found for 'Zentrale'</span> | |||
|- class="Leerzeile" | |||
| colspan="2" | '''{{#var:Responder-Log}}''' | |||
|- | |||
! Dienst !! Nachricht | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">10[CFG]</span> <span class="log na">looking for RSA signature peer configs matching 198.51.100.75...198.51.100.1[Filiale]</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">10[CFG]</span> <span class="log na">candidate "Standort1_4", match: 1/20/28 (me/other/ike)</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">10[CFG]</span> <span class="log na">selected peer config "Standort1_4"</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">10[CFG]</span> <span class="log na">using trusted certificate "Filiale"</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">10[IKE]</span> <span class="log na">authentication of 'Filiale' with RSA succesful</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">10[IKE]</span> <span class="log na">authentication of 'Zentrale' (myself) succesful</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">10[IKE]</span> <span class="log na">IKE_SA Standort1_4[1] established between 198.51.100.75[Zentrale]...198.51.100.1[Filiale]</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">10[IKE]</span> <span class="log na">IKE_SA Standort1_4[1] established between 198.51.100.75[Zentrale]...198.51.100.1[Filiale]</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">10[IKE]</span> <span class="log na">scheduling reauthentication in 2593s</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">10[IKE]</span> <span class="log na">maximum IKE_SA lifetime 3133s</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">13[IKE]</span> <span class="log na">received DELETE for IKE_SA Standort_4[1]</span> | |||
|} | |||
=== {{#var:Phase 2}} === | |||
==== {{#var:Der normale Verbindungsaufbau}} ==== | |||
{| class="sptable2 pd5 einrücken" | |||
|- class="Leerzeile" | |||
| colspan="2" | {{#var:Phase2-Der normale Verbindungsaufbau--desc}} | |||
|- class="Leerzeile" | |||
| colspan="2" | '''{{#var:Initiator-Log}} & {{#var:Responder-Log}}''' | |||
|- | |||
! Dienst !! Nachricht | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">05[IKE]</span> <span class="log na">CHILD_SA Zentrale_2{1} established with SPIs ca7520e3_i c562f9d6_o and TS 10.1.10.0/24</span> <span class="log na">===</span> <span class="log na">10.0.0.0/24</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">05[IKE]</span> <span class="log na">CHILD_SA Zentrale_2{1} established with SPIs ca7520e3_i c562f9d6_o and TS 10.1.10.0/24</span> <span class="log na">===</span> <span class="log na">10.0.0.0/24</span> | |||
|} | |||
==== {{#var:Falsche Subnetzkonfiguration}} ==== | |||
{| class="sptable2 pd5 einrücken" | |||
|- class="Leerzeile" | |||
| colspan="2" | {{#var:Falsche Subnetzkonfiguration--desc}} | |||
|- class="Leerzeile" | |||
| colspan="2" | '''{{#var:Initiator-Log}}''' | |||
|- | |||
! Dienst !! Nachricht | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">13[CFH]</span> <span class="log na">proposing traffic selectors for us:</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">13[CFG]</span> <span class="log na">10.1.0.0/24</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">13[CFG]</span> <span class="log na">proposing traffic selectors for other:</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">13[CFG]</span> <span class="log na">11.0.0.0/24</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">05[IKE]</span> <span class="log na">received INVALID_ID_INFORMATION error notify</span> | |||
|- class="Leerzeile" | |||
| colspan="2" | '''{{#var:Responder-Log}}''' | |||
|- | |||
! Dienst !! Nachricht | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">11[CFG]</span> <span class="log na">looking for a child config for 11.0.0.0/24</span> <span class="log na">===</span> <span class="log na">10.1.0.0/24</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">11[CFG]</span> <span class="log na">proposing traffic selectors for us:</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">11[CFG]</span> <span class="log na">10.0.0.0/24</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">11[CFG]</span> <span class="log na">proposing traffic selectors for other:</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">11[CFG]</span> <span class="log na">10.1.0.0/24</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">11[IKE]</span> <span class="log na">no matching CHILD_SA config found</span> | |||
|} | |||
</div> | |||
== {{#var:IKEv2 Troubleshooting}} == | |||
{{pt3| {{#var:IKEv2 Troubleshooting--Bild}} | {{#var:IKEv2 Troubleshooting--cap}} }} | |||
{{#var:IKEv2 Troubleshooting--desc}} | |||
<div class="Einrücken"> | |||
=== {{#var:Verbindungsaufbau}} === | |||
==== {{#var:IKEv1--Verbindung kommt zustande}} ==== | |||
{| class="sptable2 pd5 einrücken" | |||
|- class="Leerzeile" | |||
| colspan="2" | {{#var:IKEv1--Verbindung kommt zustande--desc}} | |||
|- class="Leerzeile" | |||
| colspan="2" | '''{{#var:Initiator-Log}} & {{#var:Responder-Log}}''' | |||
|- | |||
! Dienst !! Nachricht | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">11[CFG]</span> <span class="log na">selected proposal_ ESP_AES_CBC_128/HMAC_SHA2_256_128/NO_EXT_SEQ</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">11[CFG]</span> <span class="log na">selecting traffic selectors for us:</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">11[CFG]</span> <span class="log na">config: 10.1.0.0/24, received: 10.1.0.0/24</span> <span class="log na">=></span> <span class="log na">match: 10.1.0.0/24</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">11[CFG]</span> <span class="log na">selecting traffic selectors for ther:</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">11[CFG]</span> <span class="log na">config: 10.0.0.0/24, received: 10.0.0.0/24 0</span> <span class="log na">=></span> <span class="log na">match: 10.0.0.0/24</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">11[IKE]</span> <span class="log na">CHILD_SA Zentrale_3{2} established with SPIs c24bb346_i c8e52c94_o and T S 10.1.0.0/24</span> <span class="log na">===</span> <span class="log na">10.0.0.0/24</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">11[IKE]</span> <span class="log na">CHILD_SA Zentrale_3{2} established with SPIs c24bb346_i c8e52c94_o and T S 10.1.0.0/24</span> <span class="log na">===</span> <span class="log na">10.0.0.0/24</span> | |||
|} | |||
==== {{#var:IKEv2: Falsche Remote-Gateway-Adresse}} ==== | |||
{| class="sptable2 pd5 einrücken" | |||
|- class="Leerzeile" | |||
| colspan="2" | {{#var:IKEv2: Falsche Remote-Gateway-Adresse--desc}} | |||
|- class="Leerzeile" | |||
| colspan="2" | '''{{#var:Responder-Log}}''' | |||
|- | |||
! Dienst !! Nachricht | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">11[CFG]</span> <span class="log na">looking for an ike config fo 198.51.100.75...198.51.100.1</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">11[IKE]</span> <span class="log na">no IKE config for 198.51.100.75...198.51.100.1, sending NO_PROPOSAL_CHOSEN</span> | |||
|} | |||
==== {{#var:IKEv2: Falsche ID Initiator}} ==== | |||
{| class="sptable2 pd5 einrücken" | |||
|- class="Leerzeile" | |||
| colspan="2" | {{#var:IKEv2: Falsche ID Initiator--desc}} | |||
|- class="Leerzeile" | |||
| colspan="2" | '''{{#var:Initiator-Log}}''' | |||
|- | |||
! Dienst !! Nachricht | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">09[IKE]</span> <span class="log na">received AUTHENTICATION_FAILED error notify</span> | |||
|- class="Leerzeile" | |||
| colspan="2" | '''{{#var:Responder-Log}}''' | |||
|- | |||
! Dienst !! Nachricht | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">07[CFG]</span> <span class="log na">looking for pre-shared key peer configs matching 198.51.100.75...198.51.100.1[blubb]</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">07[IKE]</span> <span class="log na">no peer config found</span> | |||
|} | |||
==== {{#var:IKEv2 Falsche ID Responder}} ==== | |||
{| class="sptable2 pd5 einrücken" | |||
|- class="Leerzeile" | |||
| colspan="2" | {{#var:IKEv2 Falsche ID Responder--desc}} | |||
|- class="Leerzeile" | |||
| colspan="2" | '''{{#var:Initiator-Log}}''' | |||
|- | |||
! Dienst !! Nachricht | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">05[IKE]</span> <span class="log na">IDir 'blubb' does not match to '198.51.100.75'</span> | |||
|} | |||
==== {{#var:IKEv2: Falscher PSK}} ==== | |||
{| class="sptable2 pd5 einrücken" | |||
|- class="Leerzeile" | |||
| colspan="2" | {{#var:XXX--desc}} | |||
|- class="Leerzeile" | |||
| colspan="2" | '''{{#var:Initiator-Log}}''' | |||
|- | |||
! Dienst !! Nachricht | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">13[IKE]</span> <span class="log na">received AUTHENTICATION_FAILED notify error</span> | |||
|- class="Leerzeile" | |||
| colspan="2" | '''{{#var:Responder-Log}}''' | |||
|- | |||
! Dienst !! Nachricht | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">10[IKE]</span> <span class="log na">tried 2 shared keys for '198.51.100.75' - '198.51.100.1', but MAC mismatched</span> | |||
|} | |||
==== {{#var:IKEv2: Falsche Subnetzkonfiguration}} ==== | |||
{| class="sptable2 pd5 einrücken" | |||
|- class="Leerzeile" | |||
| colspan="2" | {{#var:IKEv2: Falsche Subnetzkonfiguration--desc}} | |||
|- class="Leerzeile" | |||
| colspan="2" | '''{{#var:Initiator-Log}}''' | |||
|- | |||
! Dienst !! Nachricht | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">10[IKE]</span> <span class="log na">received T S_UNACCEPTABLE notify, no CHILD_SA built</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">10[IKE]</span> <span class="log na">failed to establish CHILD_SA, keeping IKE_SA</span> | |||
|- class="Leerzeile" | |||
| colspan="2" | '''{{#var:Responder-Log}}''' | |||
|- | |||
! Dienst !! Nachricht | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">05[CFG]</span> <span class="log na">looking for a child config for 10.0.0.0/24</span> <span class="log na">===</span> <span class="log na">11.1.0.0/24</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">05[CFG]</span> <span class="log na">proposing traffic selectors for us:</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">05[CFG]</span> <span class="log na">10.0.0.0/24</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">05[CFG]</span> <span class="log na">proposing traffic selectors for other:</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">05[CFG]</span> <span class="log na">10.1.0.0/24</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">10[IKE]</span> <span class="log na">traffic selectors 10.0.0.0/24</span> <span class="log na">===</span> <span class="log na">11.1.0.0/24 inacceptable</span> | |||
|- | |||
| <span class="log service">IPSec(charon)</span> || <span class="log gr">10[IKE]</span> <span class="log na">failed to establish CHILD_SA, keeping IKE_SA</span> | |||
|} | |||
Version vom 22. Juli 2022, 20:14 Uhr
Letzte Anpassung zur Version: 12.2.3
Vorbereitung - Log-Level erhöhen
Reiter
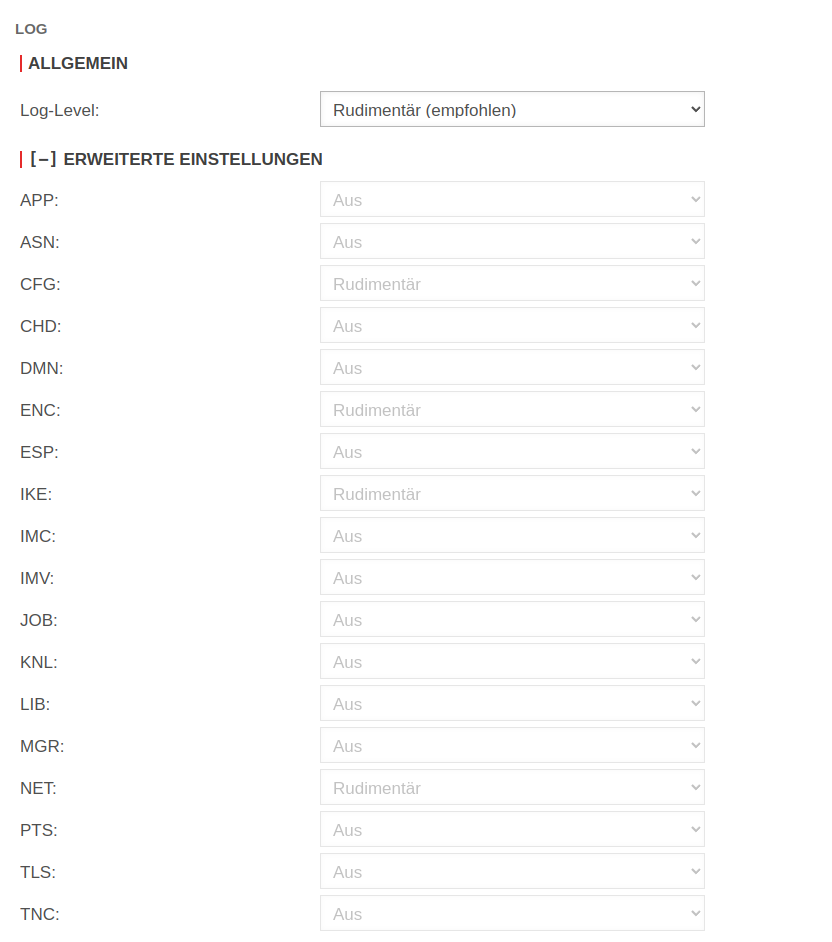
Als Voraussetzung für das erfolgreiche Troubleshooting muss das Log-Level zunächst erhöht werden.
| Log-Level: Neu ab 12.2.3 |
||
| Geeignet für ein ausführliches Troubleshooting | ||
| Kann für spezielle Fehlersuchen erforderlich sein | ||
| Alle Werte lassen sich im Abschnitt [–] Erweiterte Einstellungen in 5 unterschiedlichen Stufen protokollieren
| ||
| Speichern der geänderten Einstellungen mit
| ||
CLI-Befehl
Menü Anwendung IPSec Schaltfläche
extc-Variable setzen
Bereich extc-Variablen Suche nach Variable DBG_LVL_IKE und Wert ändern auf »2
Menü Anwendung IPSec Schaltfläche
SSH
- (nur bis Version 12.1.8):
ipsec stroke loglevel ike 2
Mit diesem Befehl ist die Einstellung nach einem Neustart wieder auf ihrem Ursprungswert!
- (ab Version 12.2):
spcli extc value set application ipsec variable DBG_LVL_IKE value 2
spcli appmgmt config
swanctl --reload-settings
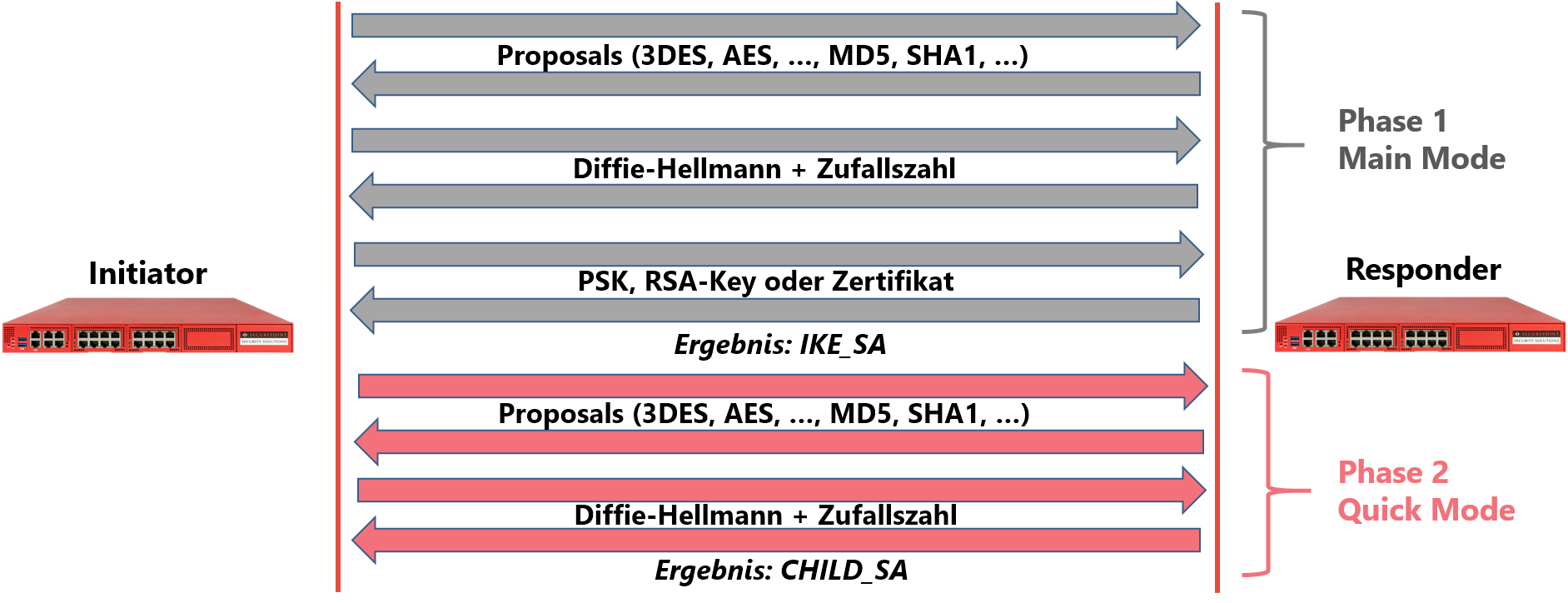
Der Aufbau einer IPSec-Verbindung unter Verwendung von IKEv1 erfolgt in zwei Phasen. In der Phase 1 erfolgt die Authentifizierung beider Gateways gegeneinander. Dies kann auf zwei verschiedene Arten erfolgen: Dem „Aggressive Mode“ oder dem „Main Mode“. Der aggressive Mode verschlüsselt den Pre Shared Key (PSK) über einen einfachen HashAlgorithmus. Außer diesem PSK sind keine weiteren Identifikationen vorgesehen. Daraus ergeben sich folgende Nachteile:
- Bei Anbindung von mehreren Gegenstellen können diese in der Phase 1 nicht voneinander unterschieden werden. Deshalb muss in allen Verbindungen der gleiche PSK verwendet werden. Die Wahrscheinlichkeit der Kompromittierung steigt mit der Anzahl der Gegenstellen.
- Die einfache Hash-Verschlüsselung des PSK macht ihn gegen Wörterbuch-Attacken verwundbar, und zwar umso mehr, je einfacher dieser ist. Da außer dem PSK kein weiteres Identifikationsmerkmal vorgesehen ist, können solche Attacken von jedem beliebigen Rechner mit Internetzugang durchgeführt werden.
Aus diesen Gründen findet der aggressive Mode von IPSec keine Verwendung in Verbindung mit Securepoint NextGen UTM. Es wird ausschließlich der sichere Main Mode eingesetzt. Dieser fordert außer dem PSK noch ein weiteres Identifikationsmerkmal, die sog. ID. Zudem wird die Übertragung des PSK durch das Diffie-Hellman-Schlüsselaustauschverfahren abgesichert. Dieses macht, mathematisch bewiesen, das Abhören eines übertragenen Schlüssels unmöglich. Weiterhin gestattet der Main Main Mode außer PSKs auch RSA-Schlüssel oder X.509-Zertifikate zur Authentifizierung.
Der normale Verbindungsaufbau
| Kommt es in der Phase 1 zu keinem Fehler, ist dies durch einen Eintrag im LiveLog zu erkennen, der die erfolgreiche Etablierung einer IKE_SA meldet. Findet sich dieser Eintrag sowohl im Log des Initiators als auch in dem des Responders, ist die Phase 1 fehlerfrei konfiguriert und ein eventueller Konfigurationsfehler in der Phase 2 zu suchen. | |
| Dienst | Nachricht |
|---|---|
| IPSec(charon) | 10[IKE] IKE_SA Standort_1_2[1] established between 198.51.100.75[198.51.100.75]...198.51.100.1[198.51.100.1] |
Falsches Proposal
| Können sich beide Seiten nicht auf für beide Seiten annehmbare Verschlüsselungsparameter einigen, dann meldet dies der Responder in seinem Livelog. Der Initiator bekommt die Meldung „NO_PROPOSAL_CHOSEN“. | |
| ' | |
| Dienst | Nachricht |
|---|---|
| IPSec(charon) | 10[IKE] received NO_PROPOSAL_CHOSEN notify error |
| ' | |
| Dienst | Nachricht |
| IPSec(charon) | 05[CFG] selecting proposal: |
| IPSec(charon) | 05[CFG] no acceptable ENCRYPTION_ALGORITHM found |
| IPSec(charon) | 05[CFG] selecting proposal: |
| IPSec(charon) | 05[CFG] received proposals: IKE:BLOWFISH_CBC_256/HMAC_SHA2_512_256/PRF_HMAC_SHA2_512/MODP_8192 |
| IPSec(charon) | 05[CFG] configured proposals:IKE:AES_CBC_128/HMAC_SHA2_256_128/PRF_HMAC_SHA2_256/MODP_2048,IKE:AES_CBC_128/AES_CBC_192/AES_CBC_256/3DES_CBC/CAMELLIA_CBC_128/CAMELLIA_CBC_192/CAMELLIA_CBC_256/AES_CTR_128/AES_CTR_192/AES_CTR_256/CAMELLIA_CTR_128/CAMELLIA_CTR_192/CAMELLIA_CTR_256/HMAC_MD5_96/HMAC_SHA1_96/HMAC_SHA2_256_128/HMAC_SHA2_384_192/HMAC_SHA2_512/AES_XCBC_96/AES_CMAC_96/PRF_HMAC_MD5/PRF_HMAC_SHA1/PRF_HMAC_SHA2_256/PRF_HMAC_SHA2_512/256/AES_XCBC_96/AES_CMAC_96/PRF_AES128_CMAC/MODP_2048/MODP_2048_224/MODP_2048_256/MODP_1536/MODP_3072/MODP_4096/MODP_8192/MODP_1024/MODP_1024_160/ECP_256/ECP_384/ECP_512/ECP_224/ECP_192/ECP_224_BP/ECP_256_BP/ECP_384_BP_ECP_512_BP,IKE:AES_GCM_8_128/AES_GCM_8_192/AES_GCM_8_256/AES_GCM_12_128/AES_GCM_12_192/AES_GCM_12_256/AES_GCM_16_128/AES_GCM_16_192/AES_GCM_16_256/PRF_HMAC_MD5/PRF_HMAC_SHA1/PRF_HMAC_SHA2_256/PRF_HMAC_SHA2_384/PRF_HMAC_SHA2_512/PRF_AES128_XCBC/PRF_AES128_CMAC/MODP_2048/MODP_2048_224/MODP_2048_256/MODP_1536/MODP_3072/MODP_4096/MODP_8192/MODP_1024/MODP_1024_160/ECP_256/ECP_384/ECP__521/ECP_224/ECP_192/ECP_224_BP/ECP_256_BP/ECP_384_BP/ECP_512_BP |
| IPSec(charon) | 10[IKE] received proposals inacceptable |
Falsche Remote-Gateway-Adresse
| Versucht der Initiator den Verbindungsaufbau von einer anderen als der auf Seiten des Responders konfigurierten Gateway-Adresse, kann der Responder diese Verbindung nicht zuordnen. Dies wird entsprechend im LiveLog gemeldet. Der Initiator bekommt die Meldung NO_PROPOSAL_CHOSEN. | |
| ' | |
| Dienst | Nachricht |
|---|---|
| IPSec(charon) | 11[CFG] looking for an ike config for 198.51.100.75...195.51.100.1 |
| IPSec(charon) | 11[IKE] no IKE config found for 198.51.100.75...195.51.100.1, sending NO_PROPOSAL_CHOSEN |
Falsche ID Initiator
| Meldet sich der Initiator mit einem anderen Identifikator (ID) als in der Konfiguration des Responders hinterlegt, kann dieser keine PSK-Konfiguration für diesen Verbindungsversuch feststellen und meldet dies entsprechend im LiveLog. Der Initiator erhält die Fehlermeldung AUTHENTICATION_FAILED. | |
| ' | |
| Dienst | Nachricht |
|---|---|
| IPSec(charon) | 09[IKE] received AUTHENTICATION_FAILED error notify |
| ' | |
| Dienst | Nachricht |
| IPSec(charon) | 07[CFG] looking for pre-shared key peer configs matching 198.51.100.75...198.51.100.1[blubb] |
| IPSec(charon) | 07[IKE] no peer config found |
Falsche ID Responder
| Meldet sich der Responder mit einer anderen ID als in der Konfiguration des Initiators, dann wird dies im Log des Initiators entsprechend gemeldet. | |
| ' | |
| Dienst | Nachricht |
|---|---|
| IPSec(charon) | 05[IKE] IDir 'blubb' does not match to '198.51.100.75' |
Falscher PSK
| Im Gegensatz zu älteren Software-Versionen findet sich bei nicht übereinstimmenden PSKs bei Verwendung von IKEv1 kein klar lesbarer Hinweis im Log. Indirekt weist der Hinweis auf „deformierte“ Pakete auf diesen Fehler hin. | |
| ' | |
| Dienst | Nachricht |
|---|---|
| IPSec(charon) | 15[IKE] message parsing failed |
| IPSec(charon) | 15[IKE] ignore malformed INFORMATIONAL request |
| IPSec(charon) | 15[IKE] INFORMATIONAL_V1 request with message ID 1054289493 processing failed |
| ' | |
| Dienst | Nachricht |
| IPSec(charon) | 14[IKE] message parsing failed |
| IPSec(charon) | 14[IKE] ID_PROT request with message ID 0 processing failed |
Falscher RSA-Key Initiator
| Verwendet der Initiator der Verbindung einen anderen RSA-Key als in der Konfiguration des Responders eingestellt, kann keine Authentifizierung erfolgen. Der Initiator erhält die Fehlermeldung „AUTHENTICATION_FAILED“. | |
| ' | |
| Dienst | Nachricht |
|---|---|
| IPSec(charon) | 15[IKE] authentication of 'Filiale' (myself) succesful |
| IPSec(charon) | 16[IKE] received AUTHENTICATION_FAILED error notify |
| ' | |
| Dienst | Nachricht |
| IPSec(charon) | 14[CFG] looking for RSA signature peer configs matching 198.51.100.75...198.51.100.1[Filiale] |
| IPSec(charon) | 14[CFG] candidate "Standort1_4", match: 1/20/28 (me/other/ike) |
| IPSec(charon) | 14[CFG] selected peer config "Standort1_4" |
| IPSec(charon) | 14[CFG] using trusted certificate "Filiale" |
| IPSec(charon) | 14[IKE] ignature validation failed, looking for another key |
| IPSec(charon) | 14[IKE] no trusted RSA public key found for 'Filiale' |
Falscher RSA-Key Responder
| Verwendet der Responder einen anderen RSA-Schlüssel als in der Konfiguration des Initiators angegeben, dann schlägt wiederum auf Seiten des Initiators die Authentifizierung fehl. Der Responder, der bereits eine IKE_SA etabliert hat, wird angewiesen, diese wieder zu löschen. | |
| ' | |
| Dienst | Nachricht |
|---|---|
| IPSec(charon) | 16[CFG] authentication of 'Filiale' (myself) succesful |
| IPSec(charon) | 16[IKE] using trusted certificate "Zentrale" |
| IPSec(charon) | 16[IKE] signature validation failed, looking for another key |
| IPSec(charon) | 15[IKE] no trusted RSA public key found for 'Zentrale' |
| ' | |
| Dienst | Nachricht |
| IPSec(charon) | 10[CFG] looking for RSA signature peer configs matching 198.51.100.75...198.51.100.1[Filiale] |
| IPSec(charon) | 10[CFG] candidate "Standort1_4", match: 1/20/28 (me/other/ike) |
| IPSec(charon) | 10[CFG] selected peer config "Standort1_4" |
| IPSec(charon) | 10[CFG] using trusted certificate "Filiale" |
| IPSec(charon) | 10[IKE] authentication of 'Filiale' with RSA succesful |
| IPSec(charon) | 10[IKE] authentication of 'Zentrale' (myself) succesful |
| IPSec(charon) | 10[IKE] IKE_SA Standort1_4[1] established between 198.51.100.75[Zentrale]...198.51.100.1[Filiale] |
| IPSec(charon) | 10[IKE] IKE_SA Standort1_4[1] established between 198.51.100.75[Zentrale]...198.51.100.1[Filiale] |
| IPSec(charon) | 10[IKE] scheduling reauthentication in 2593s |
| IPSec(charon) | 10[IKE] maximum IKE_SA lifetime 3133s |
| IPSec(charon) | 13[IKE] received DELETE for IKE_SA Standort_4[1] |
Der normale Verbindungsaufbau
| Ist auch die Phase 2 korrekt konfiguriert, wird der erfolgreiche Aufbau einer CHILD_SA im Livelog beider Seiten dokumentiert. | |
| & | |
| Dienst | Nachricht |
|---|---|
| IPSec(charon) | 05[IKE] CHILD_SA Zentrale_2{1} established with SPIs ca7520e3_i c562f9d6_o and TS 10.1.10.0/24 === 10.0.0.0/24 |
| IPSec(charon) | 05[IKE] CHILD_SA Zentrale_2{1} established with SPIs ca7520e3_i c562f9d6_o and TS 10.1.10.0/24 === 10.0.0.0/24 |
Falsche Subnetzkonfiguration
| Stimmen die konfigurierten Subnetze (die sogenannten Traffic-Selektoren) in der Phase 2 von Initiator und Responder nicht überein, kann auf der zuvor etablierten IKE_SA kein Tunnel aufgesetzt werden, d.h. es wird keine CHILD_SA etabliert. Dieser Hinweis findet sich im Livelog des Responders. | |
| ' | |
| Dienst | Nachricht |
|---|---|
| IPSec(charon) | 13[CFH] proposing traffic selectors for us: |
| IPSec(charon) | 13[CFG] 10.1.0.0/24 |
| IPSec(charon) | 13[CFG] proposing traffic selectors for other: |
| IPSec(charon) | 13[CFG] 11.0.0.0/24 |
| IPSec(charon) | 05[IKE] received INVALID_ID_INFORMATION error notify |
| ' | |
| Dienst | Nachricht |
| IPSec(charon) | 11[CFG] looking for a child config for 11.0.0.0/24 === 10.1.0.0/24 |
| IPSec(charon) | 11[CFG] proposing traffic selectors for us: |
| IPSec(charon) | 11[CFG] 10.0.0.0/24 |
| IPSec(charon) | 11[CFG] proposing traffic selectors for other: |
| IPSec(charon) | 11[CFG] 10.1.0.0/24 |
| IPSec(charon) | 11[IKE] no matching CHILD_SA config found |

Der Aufbau der Verbindung mit IKEv2 ist im Vergleich zu IKEv1 massiv vereinfacht worden. Er wird nun nicht mehr aufgeteilt in Phase 1 (Authentifizierung) und Phase 2 (Tunnelaufbau), vielmehr werden mit jeweils einem Nachrichtenpaar zunächst Proposals und DH-Schlüssel und anschließend die Authentifizierung und die Traffic-Selektoren (Subnetze) ausgetauscht. Das macht den Verbindungsaufbau einfacher und weniger störanfällig.
Verbindungsaufbau
Verbindung kommt zustande
| & | |
| Dienst | Nachricht |
|---|---|
| IPSec(charon) | 11[CFG] selected proposal_ ESP_AES_CBC_128/HMAC_SHA2_256_128/NO_EXT_SEQ |
| IPSec(charon) | 11[CFG] selecting traffic selectors for us: |
| IPSec(charon) | 11[CFG] config: 10.1.0.0/24, received: 10.1.0.0/24 => match: 10.1.0.0/24 |
| IPSec(charon) | 11[CFG] selecting traffic selectors for ther: |
| IPSec(charon) | 11[CFG] config: 10.0.0.0/24, received: 10.0.0.0/24 0 => match: 10.0.0.0/24 |
| IPSec(charon) | 11[IKE] CHILD_SA Zentrale_3{2} established with SPIs c24bb346_i c8e52c94_o and T S 10.1.0.0/24 === 10.0.0.0/24 |
| IPSec(charon) | 11[IKE] CHILD_SA Zentrale_3{2} established with SPIs c24bb346_i c8e52c94_o and T S 10.1.0.0/24 === 10.0.0.0/24 |
Falsche Remote-Gateway-Adresse
| Stimmen die Gateway-Adresse des Initiators und die in der Konfiguration des Responders angegebene Remote-Gateway-Adresse nicht überein, kann der Verbindungsversuch nicht zugeordnet werden. Dies wird so im Log des Responders gemeldet. Der Initiator erhält die Fehlermeldung „NO_PROPOSAL_CHOSEN“. | |
| ' | |
| Dienst | Nachricht |
|---|---|
| IPSec(charon) | 11[CFG] looking for an ike config fo 198.51.100.75...198.51.100.1 |
| IPSec(charon) | 11[IKE] no IKE config for 198.51.100.75...198.51.100.1, sending NO_PROPOSAL_CHOSEN |
Falsche ID Initiator
| Stimmt die konfigurierte Remote ID nicht mit der ID überein, die der Initiator meldet, dann kann auch hier der Verbindungsversuch nicht zugeordnet werden und dies wird im Responder-Log dokumentiert. Der Initiator bekommt die Fehlermeldung AUTHENTICATION_FAILED. | |
| ' | |
| Dienst | Nachricht |
|---|---|
| IPSec(charon) | 09[IKE] received AUTHENTICATION_FAILED error notify |
| ' | |
| Dienst | Nachricht |
| IPSec(charon) | 07[CFG] looking for pre-shared key peer configs matching 198.51.100.75...198.51.100.1[blubb] |
| IPSec(charon) | 07[IKE] no peer config found |
Falsche ID Responder
| Umgekehrt wird eine andere als die beim Initiator konfigurierte Responder-ID entsprechend im Log des Initiators gemeldet. | |
| ' | |
| Dienst | Nachricht |
|---|---|
| IPSec(charon) | 05[IKE] IDir 'blubb' does not match to '198.51.100.75' |
Falscher PSK
| ' | |
| Dienst | Nachricht |
|---|---|
| IPSec(charon) | 13[IKE] received AUTHENTICATION_FAILED notify error |
| ' | |
| Dienst | Nachricht |
| IPSec(charon) | 10[IKE] tried 2 shared keys for '198.51.100.75' - '198.51.100.1', but MAC mismatched |
Falsche Subnetzkonfiguration
| Stimmen im zweiten Schritt die konfigurierten Subnetze (die sogenannten Traffic-Selektoren) von Initiator und Responder nicht überein, kann auf der zuvor etablierten IKE_SA kein Tunnel aufgesetzt werden, d.h. es wird keine CHILD_SA etabliert. Dieser Hinweis findet sich im Livelog des Responders. | |
| ' | |
| Dienst | Nachricht |
|---|---|
| IPSec(charon) | 10[IKE] received T S_UNACCEPTABLE notify, no CHILD_SA built |
| IPSec(charon) | 10[IKE] failed to establish CHILD_SA, keeping IKE_SA |
| ' | |
| Dienst | Nachricht |
| IPSec(charon) | 05[CFG] looking for a child config for 10.0.0.0/24 === 11.1.0.0/24 |
| IPSec(charon) | 05[CFG] proposing traffic selectors for us: |
| IPSec(charon) | 05[CFG] 10.0.0.0/24 |
| IPSec(charon) | 05[CFG] proposing traffic selectors for other: |
| IPSec(charon) | 05[CFG] 10.1.0.0/24 |
| IPSec(charon) | 10[IKE] traffic selectors 10.0.0.0/24 === 11.1.0.0/24 inacceptable |
| IPSec(charon) | 10[IKE] failed to establish CHILD_SA, keeping IKE_SA |