Inbetriebnahme
New article: 06.2022
Preparation
Have login information ready
- When operating on a modem or fiber optic connection:
- Have login information of the Internet service provider ready
- Who has the current login information of the ISP?
- Is the login information available at the installation site?
- Is the login information available at the time of installation?
- if applicable: Is the person who has the login information available at the time of installation?
- When operating with a router:
- What is the IP address of the router?
- Can the UTM get a fixed IP?
- For new installations, DHCP is activated on the external interface
- Local network:
- What is the network IP of the local network(s)?
- Which IP addresses should the interfaces of the UTM in these networks receive?
As a rule, this should always be a fixed IP address!
Prepare firmware update
- If an existing configuration file is to be used, the installed firmware version must be identical or newer.
- Latest features and patches are available immediately.
Several firmware versions may have been released between the manufacturing and delivery. - Damage due to manipulation of the firmware in transit (unlikely, but not impossible) can thus be excluded.
- A USB stick with the UTM image is required.
This Securepoint Imaging Tool can be used. (Resellerportal → Menu → Tools x ) - Connect keyboard and monitor
(not Autoinstall or Autoupdate)
- The prepared USB stick must be connected to the UTM
- Switch on the UTM
- Under Save & Exit execute
The USB stick should then be listed at the top of the boot menu of the device, preceded by the TAG UEFI - Execute under Save & Exit
- Perform installation/ update
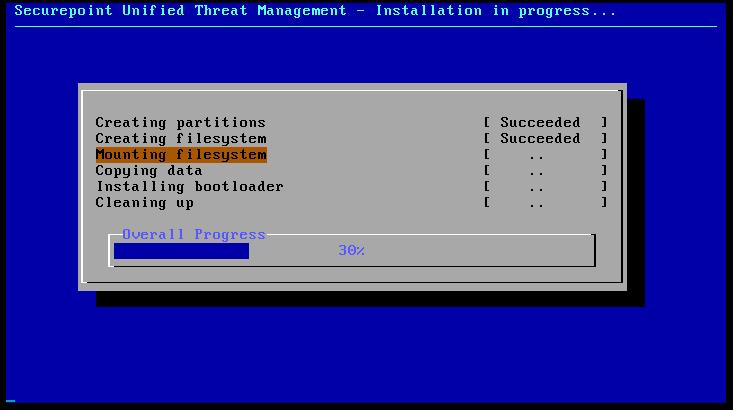
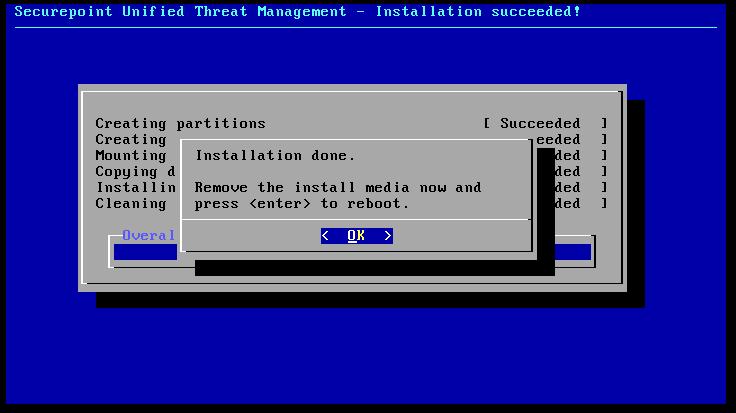
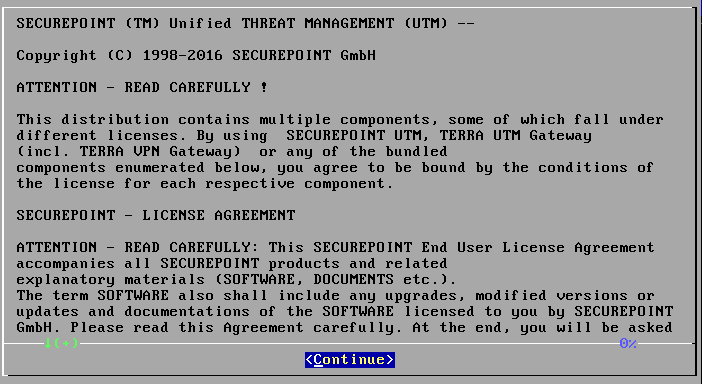
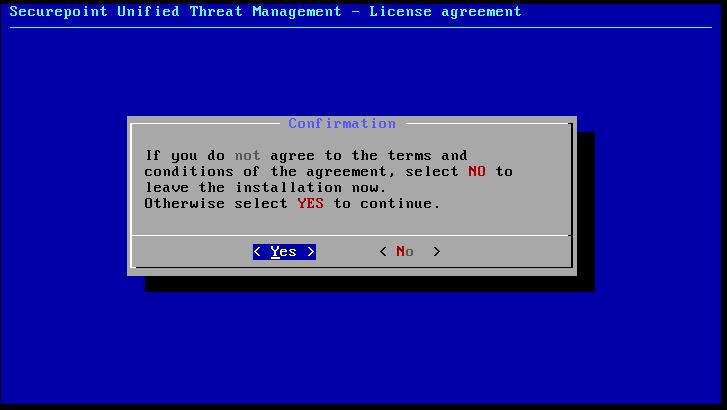
Installing the firmware
The firmware is installed in just a few steps. The preselection options only need to be confirmed.
- Display and confirmation of the license conditions
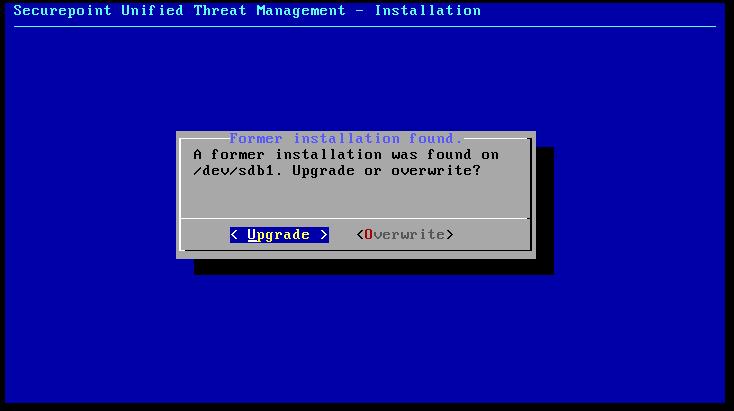
- Decision as to whether an upgrade should be carried out
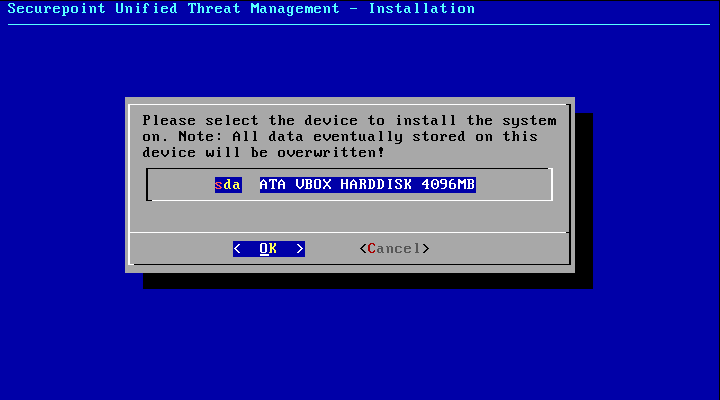
Default: Upgrade - Selection of the hard disk on which the firmware is to be installed
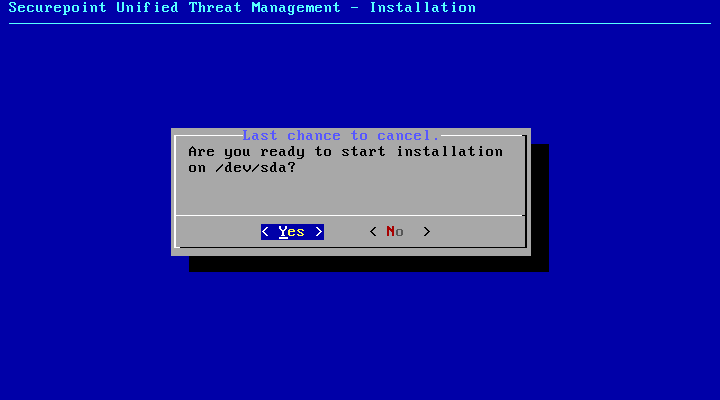
- Starting the installation
- Request to remove the USB stick
- Reboot
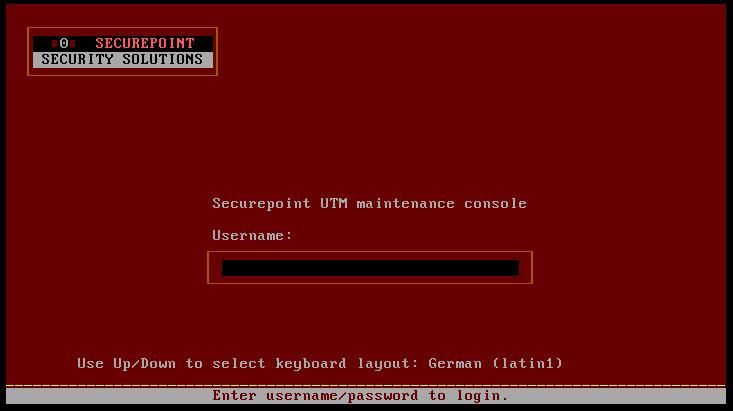
- Display of the login console
| 1. | 2. | 3. |
| Abb.1 | Abb.2 | Abb.3 |
| Abbildungen | ||
Integration into the local network
Adjust IP addresses of the UTM via CLI
If administration via the CLI is not an issue, the IP adresses can be provided directly to the UTM via CLI
In this case, the monitor and keyboard remain directly connected to the UTM.
The login is done on the console.
To be able to administer the UTM, the admin interface must be accessed via the IP of the UTM and the port of the admin interface via the interface LAN2.
In the factory settings, the UTM can be reached via https://192.168.175.1:11115.
If the IP or the interface cannot be reached from the local network, changes must be made.
- Connecting keyboard and monitor directly to the UTM
- Log in to the UTM: Username admin / Password: insecure
- the Command Line Interface appears.
- change network configuration:
- Determine the existing interfaces: interface get
- Determine the ID of the IP addresses: interface address get
LAN2 corresponds to the internal interface through which the admin interface can be reached.
The ID is needed for changing the IP address in the next step. - Change the interface IPs: interface address set id 1 address 192.168.12.1/24
system update interface (desired IP of the internal network with subnet mask) - Activate an interface: interface address new device LAN1 or A0 address 192.168.x.y/24
system update interface
- Set up administration access:
In the factory settings, access to the admin interface of the UTM is only possible via the internal interface LAN2. If the admin interface is to be accessible via another interface, the IP of the host (or a net IP with subnet mask) must be released:
manager new hostlist 192.168.168.0/24
system update rule Here: All hosts in the network 192.168.168.0 (no matter at which interface) can access the admin interface
Attention: If e.g. the IP 192.168.175.1 is at LAN1 or A0 and the admin interface should be called from a computer in the network at LAN1, the IP 192.168.175.x must be released extra nevertheless.
Adjust the IP address of your own computer
The IP address of your own computer is temporarily adapted to the default network of the internal interface of the UTM.
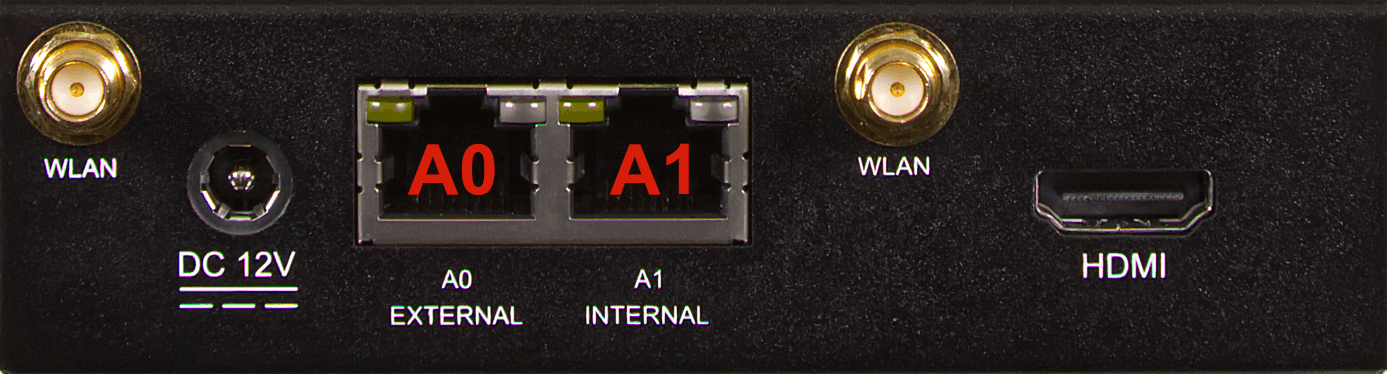
This is followed by connecting your own computer to interface A1 (the internal interface) of the UTM.
The correct interface can be seen in the figure and table above.
This is how it works
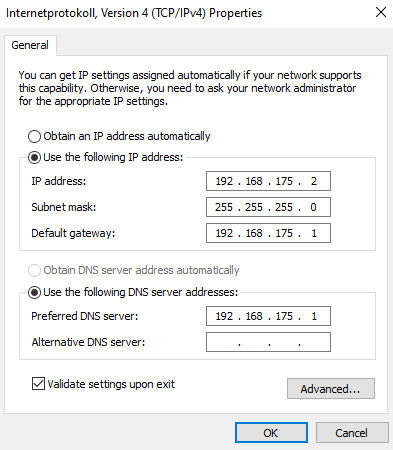
Change IP address on Windows
- Display of network connections: r ncpa.cpl↵
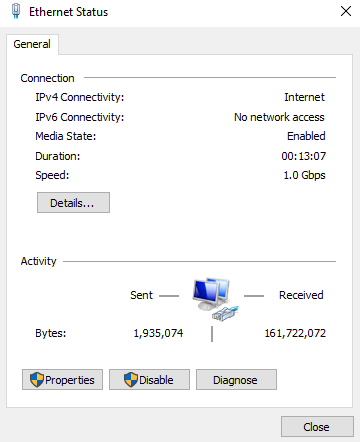
- Show status of Ethernet connection with double click
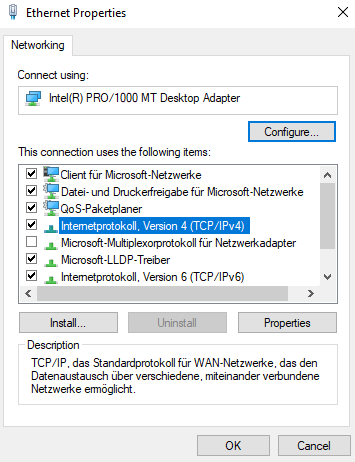
- Show properties of the interface
- Show properties of the TCP/IPv4 connection
- Set IP address:
- IP address:192.168.175.2
- Subnet mask:255.255.255.0
- Default gateway:192.168.175.1 (=Default address of the internal interface of the UTM)
| 1. | 2. | 3. |
| Abb.1 | Abb.2 | Abb.3 |
| Abbildungen | ||
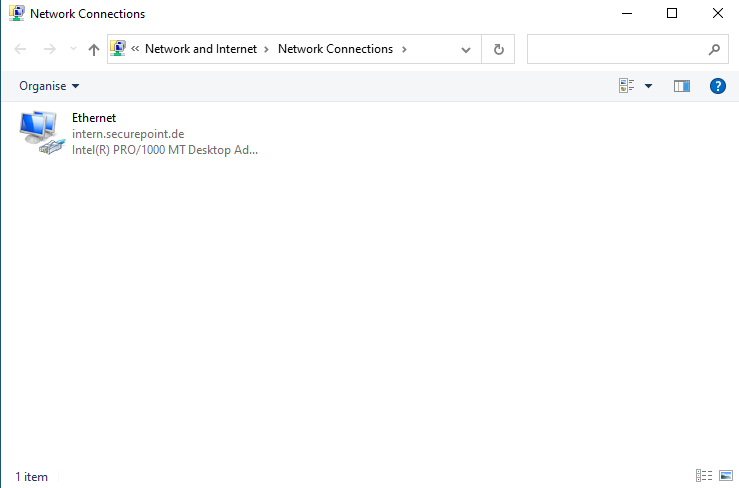
- Access via desktop display:
- Click on the network icon in the taskbar next to the clock
- Click on Network and Internet settings.
- Click on Change adapter options.
- Access by command:
- Windows key r ncpa.cpl
- Double-click on the interface used to display the status of the ethernet connection
Change IP address on Linux
Please refer to the corresponding documentation of the used distribution.
Examples for Ubunutu:
- Opening the terminal
- Identify the name of the interface: ip a
- Change IP address: (In the example enp0s3 is the interface used: sudo ip address add 192.168.175.2/24 dev enp0s3
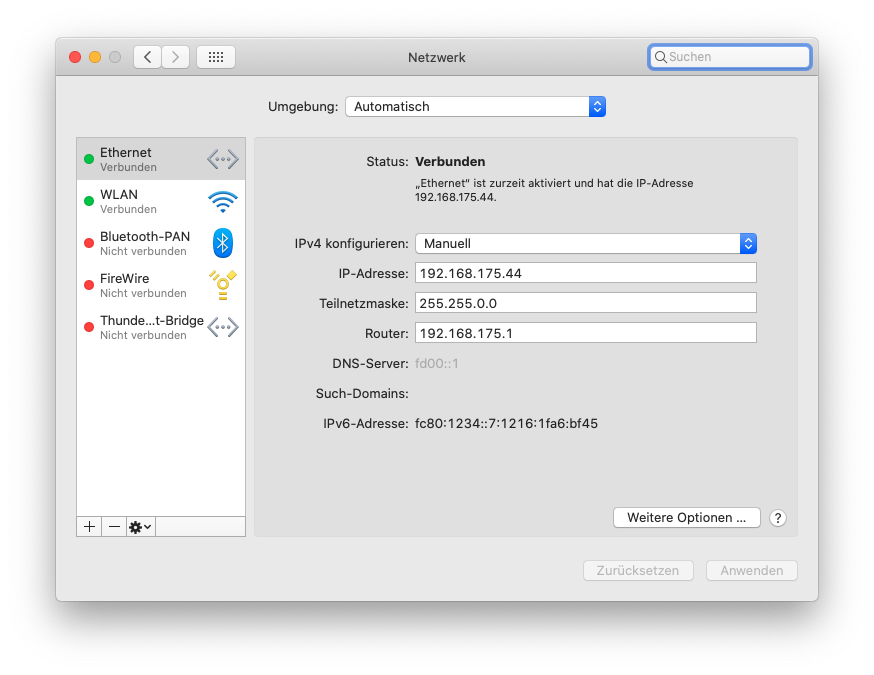
Change IP address on a MAC
Change IP address on a MAC
- Menu System settings / network
- Configure IPv4: Manuell▴▾ select in the dropdown menu
- IP address:192.168.175.2
- Subnet mask:255.255.255.0
- Router:192.168.175.1 (=Default address of the internal interface of the UTM)
- Button
For further configuration, the IP address of your own computer must then be changed again.
Setting the original IP address:
- Fixed IP Addresses: Enter as described above
- Enable DHCP:
- Windows: Properties Internet Protocol Version 4 (TCPIPv4) → select Obtain an IP address automatically
- Linux: Example for Ubuntu: sudo ip address del 192.168.175.2/24 dev enp0s3
sudo dhclient enp0s3
If necessary, refer to the documentation of the distribution used. - MAC: coming soon...
First access
If not already done, the following connections must be made now physically:
- Connect interface for the external interface (A0) towards the Internet (modem, router, etc.).
- Connect the internal interface (A1)
- with your own computer, if the IP address has been adjusted on it.
- to the network from which the UTM is to be administered, if the IP address of the UTM has been adjusted.
https://192.168.175.1:11115 (Default) or
https://172.16.0.1:11115, if the IP address of the UTM was changed to 172.16.0.1
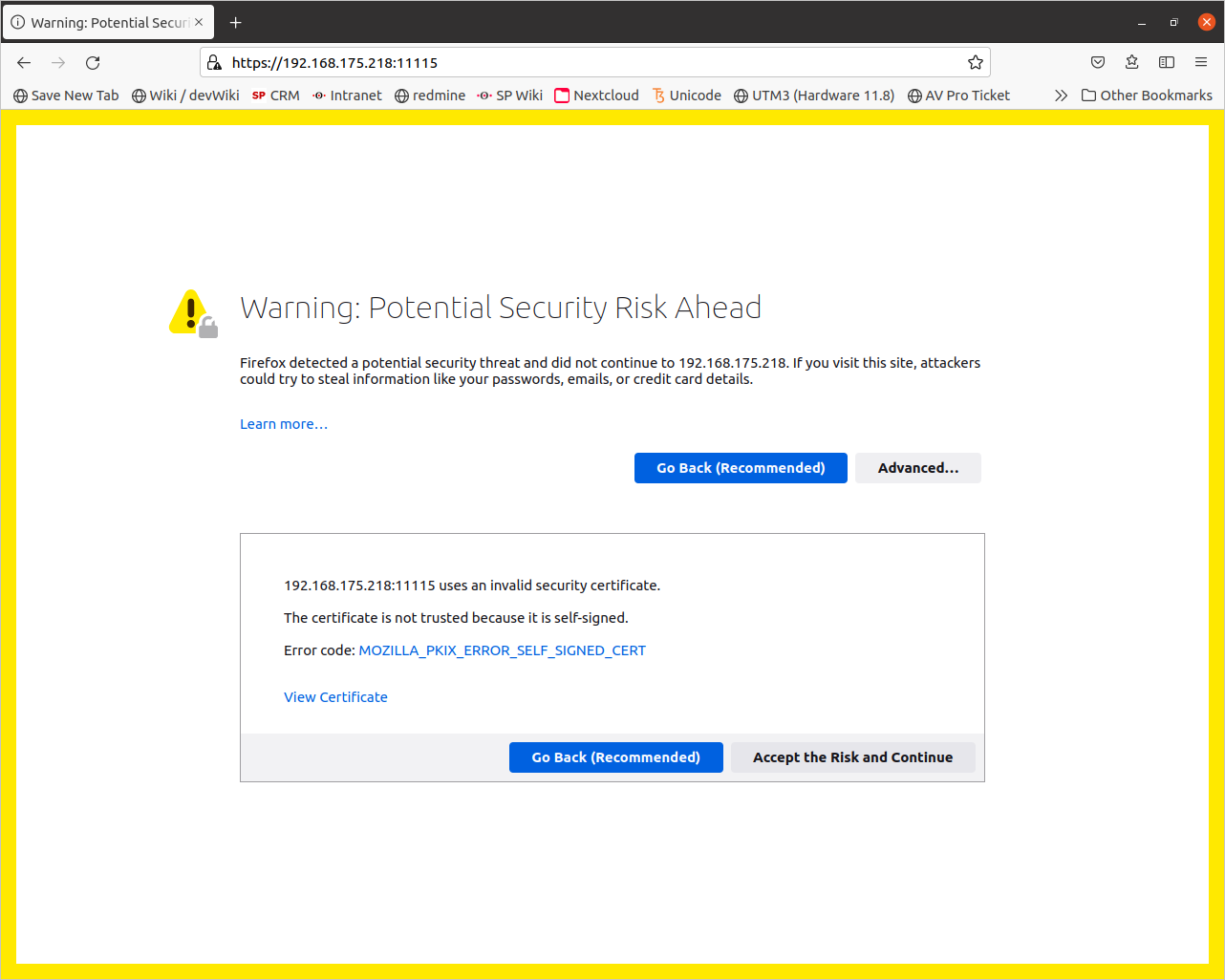
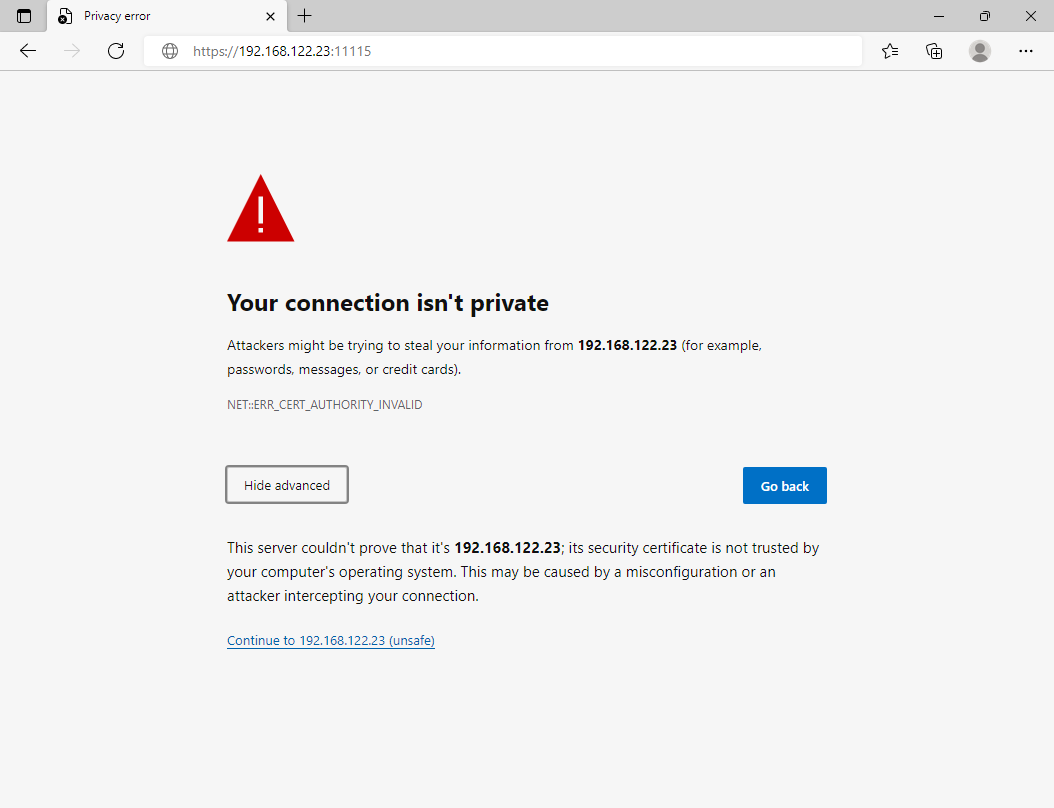
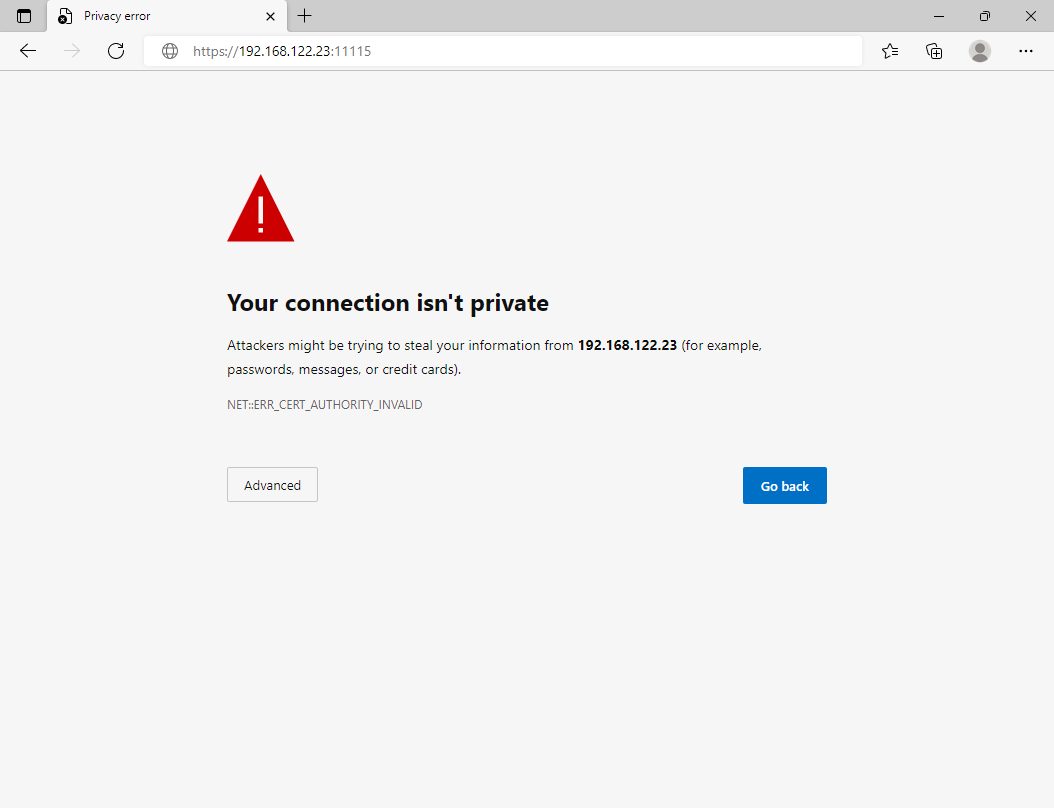
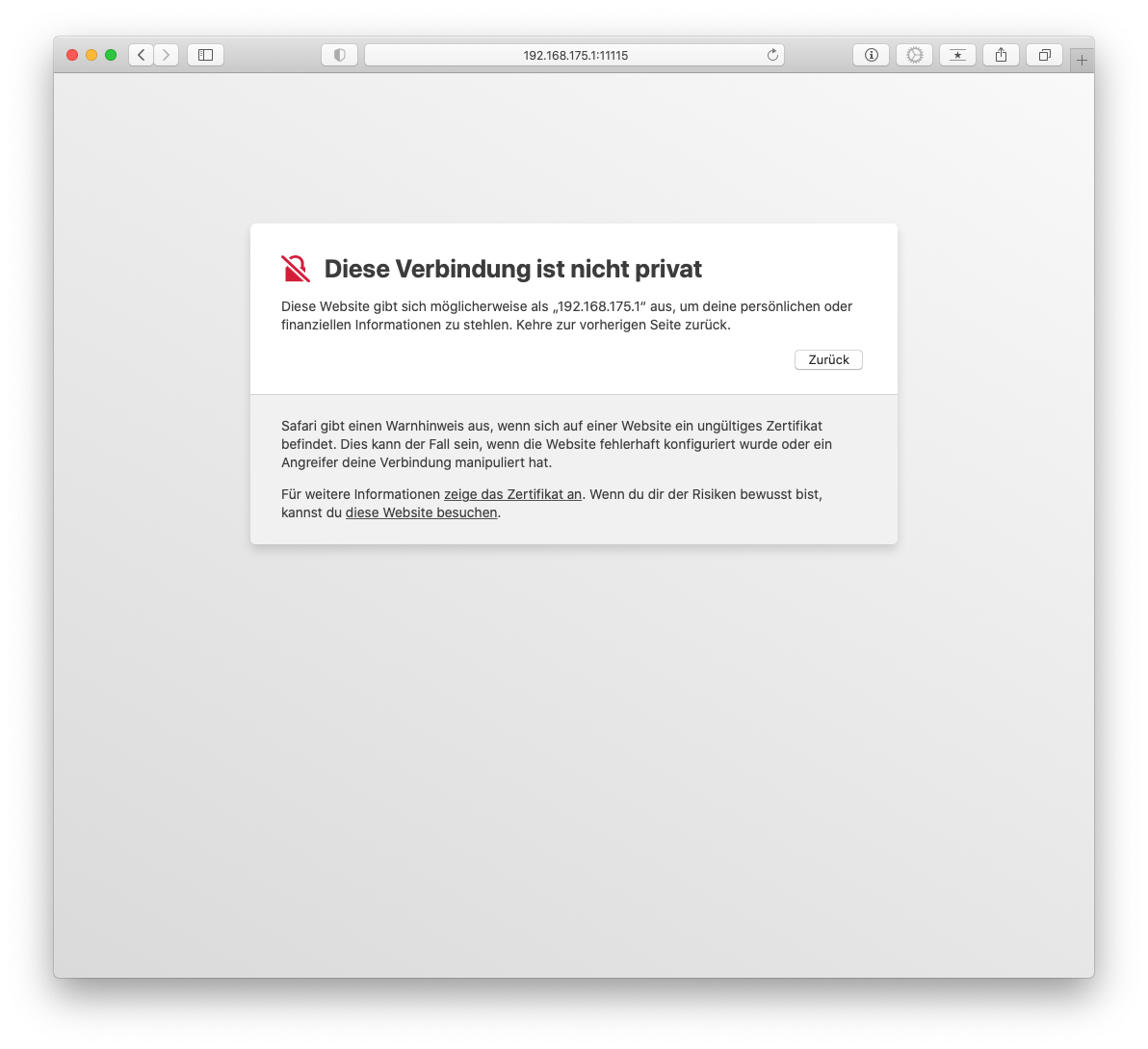
When the admin interface is called up for the first time, a certificate warning appears in the browser.
Since the browser doesn't know the certificate of the UTM, a security warning is issued.
This warning must be ignored.
First registration | |||
| Caption | Value | Description | 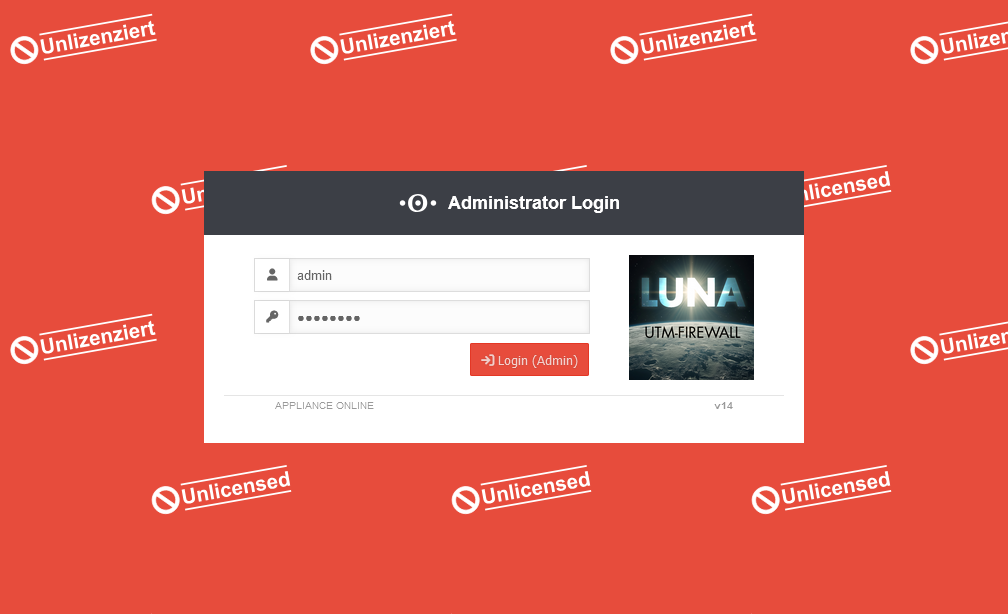 |
|---|---|---|---|
| User | Login with the default login information of the factory settings: admin | ||
| Password | Login with the default login information of the factory settings: insecure | ||
| Login (admin) | |||
Agree to license agreement and privacy policy | |||
| The license agreement and privacy policy must be accepted by clicking the button. | UTM 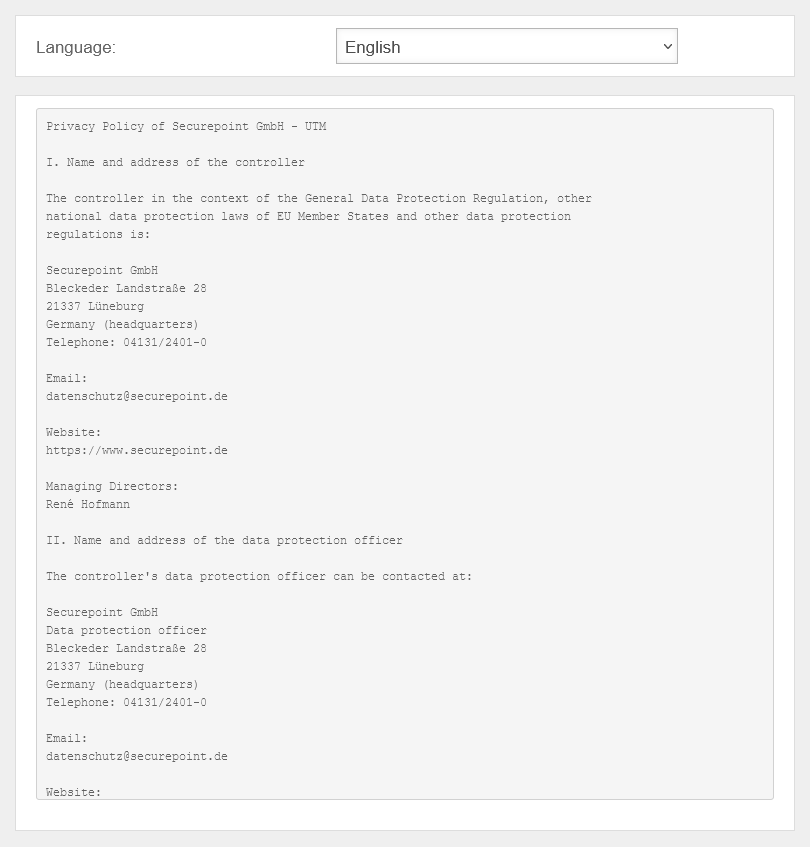 The privacy policy must be agreed to. UTM The privacy policy must be agreed to. UTM 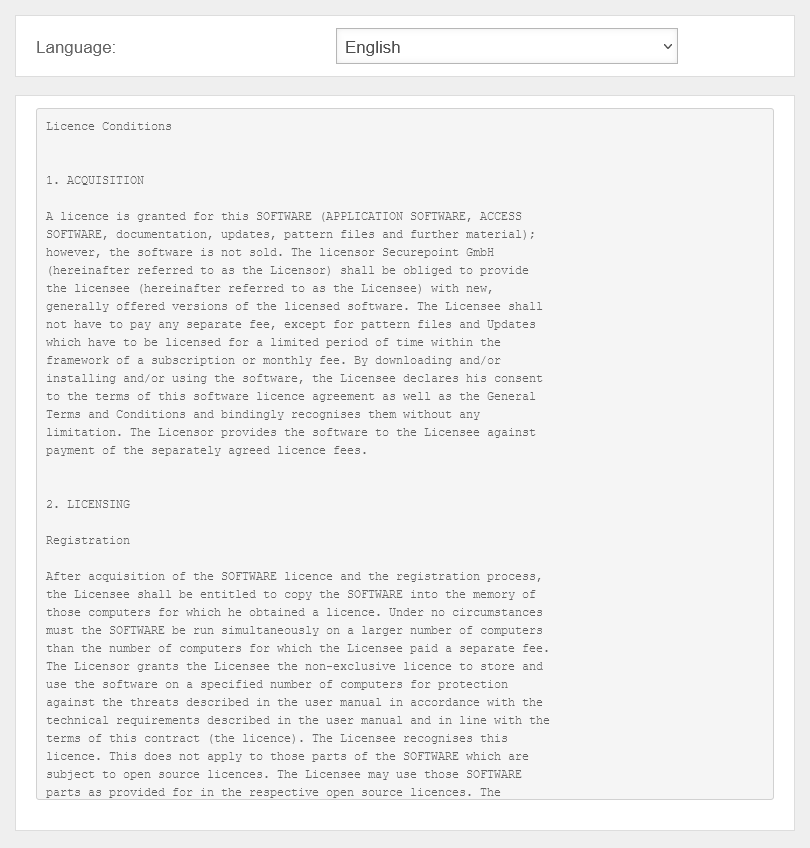 The license agreement must be agreed to. The license agreement must be agreed to.
| ||
Basic configurations | |||
| Firewall name | firewall.ttt-point.local | An individual firewall name must be assigned. |
UTMuser@firewall.name.fqdn 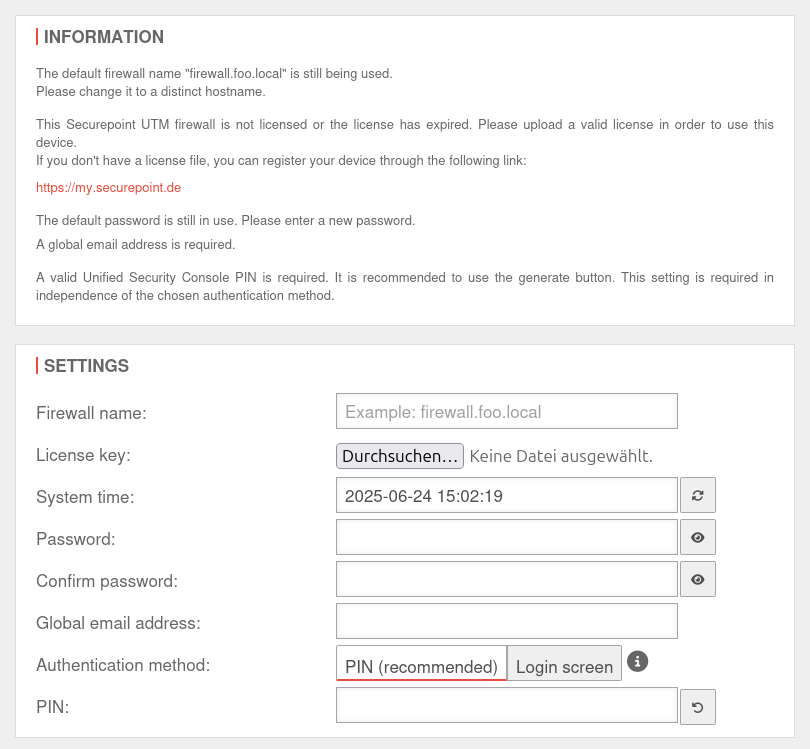 Basic configurations The fields displayed may vary depending on what information is already available on the UTM
|
| License key | Import valid license. | ||
| System time | yyyy-mm-dd hh-m--ss | The system time should be correct. It is compared with other servers, e.g. for user authentication (Kerberos, OTP, etc.). If the deviation is too large, for example, login will not be possible. | |
| Password Confirm password |
|
The default password insecure Passwords must meet the following criteria:
notempty
New in v14.0.7: Password change required upon first login | |
| Global email address: notempty
New as of v12.4.4 |
admin@ttt-point.de | Required information e.g. for the mail connector and the proxy. Also serves as postmaster address for the mail relay. | |
| Authentication method: notempty
New as of v12.5.1 |
Authentication method for Web sessions via USC The web session PIN also secures the use of the following actions within the scope of the USC:
If the PIN is not used, these actions cannot be called up from the Unified Security Portal. | ||
| PIN: | PIN as additional security for Websessions No number sequences or duplications are allowed | ||
| Creates a secure PIN | |||
| Displays the license agreement | |||
| Displays the privacy policy | |||
| Logs off again. No settings are saved! | |||
| Complete | Completes the login process and opens the Welcome window. | ||
Welcome | |||
| Basic settings are completed with the welcome dialog. | UTMuser@firewall.name.fqdn  Welcome dialog Welcome dialog
| ||
| Starts the Installation Wizard. | |||
| Starts a tour that explains the admin interface and menus in 15 steps. | |||
Configure interfacesnotempty
New as of v12.7.0 | |||
| Do you want to configure the interfaces now? | This message appears if not all existing interfaces are configured correctly. However, it is recommended to do this to prevent possible problems. The button opens the network configuration directly. | 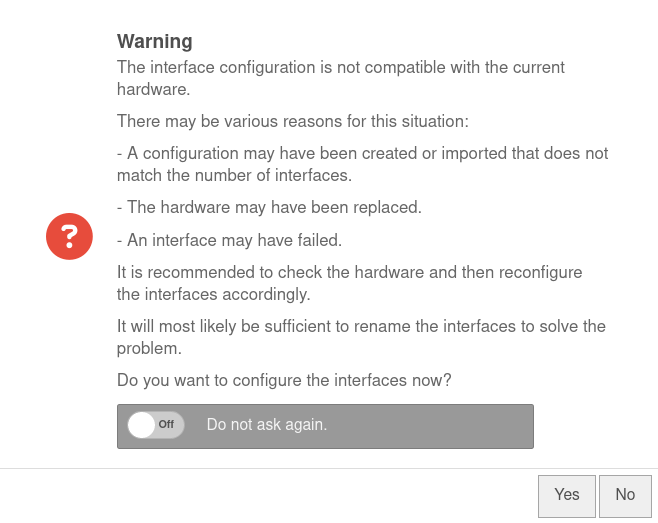 | |
| Do not ask again. | Off | If this message is not desired, it can be set here so that it is not displayed again. | |
Einrichtung mit Installationsassistenten
Warnung: Der Anzeigetitel „Installation wizard“ überschreibt den früheren Anzeigetitel „Commission Black Dwarf (G5)“.
Last adaptation to the version: 14.0.1
Prefaces
- Usually, the installation wizard appears during the initial setup of the UTM.
This checks whether a configuration already exists that is marked as the boot configuration. (Status )
If this is not the case, the wizard opens automatically. - It is not advisable to start the installation wizard later, as other settings made in the meantime may be overwritten.
Installation wizard
Step 1 - General
| Caption | Value | Description | UTMuser@firewall.name.fqdnConfiguration management 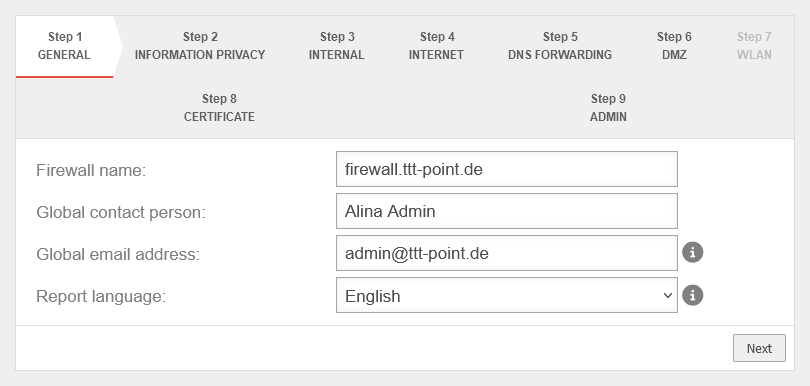 Step 1 Step 1
|
|---|---|---|---|
| Firewall Name: | firewall.ttt-point.local | This is about how the UTM responds to requests. For example, if the mail relay is to be used, it may be useful to enter the Fully Qualified Domain Name (FQDN) of the mail exchange (MX) here so that other mail servers can match it via the reverse resolution of the PTR Resource Record (PTR). This setting is made in the Authentication → AD/LDAP Authentication → tab Settings Appliance Account entry. | |
| Global contact person: | Alina Admin | In this field, the name of the administrator or the organization is entered, which is later specified in the UTM error messages for questions. | |
| Global email address: | admin@ttt-point.de | Important system messages are sent to this email address. | |
| Language of reports: | Language in which the reports and system messages are sent | ||
Step 2 - Privacy | |||
| Anonymize all applications | Yes | When activated (default), the appliance's applications are anonymized in accordance with the GDPR. Under anonymization can also be activated individually for each application. |
 |
Step 3 - Internal | |||
Without WLAN moduleWithout WLAN module
| |||
| Internal firewall IP address: | The IP address of the internal interface (A1) as well as the subnet mask (as CIDR-notation) for the internal network. | 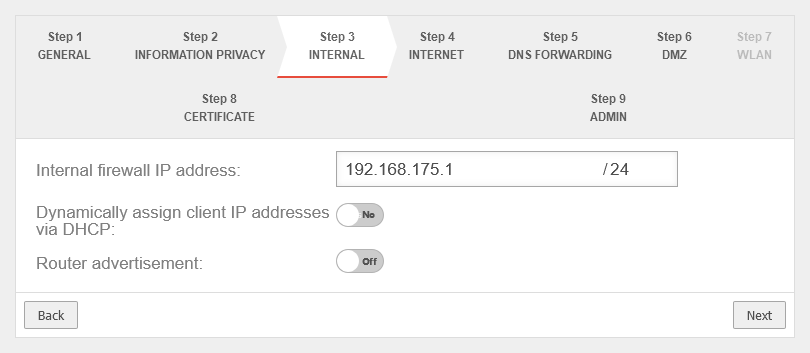 | |
| Dynamically assign Client IP Addresses via DHCP: | No | When enabled Yes, the UTM works as a DHCP server: All clients in the internal network receive an IP address via DHCP. This sets the UTM as the default gateway and DNS server for the clients. | |
| Router Advertisement: | Off | If the UTM has received an IPv6 prefix, it can advertise the subnet via router advertisement in the network segment behind the interface. (See article IPv6 Prefix Delegation) | |
With WLAN module With WLAN module
| |||
| Internal firewall IP address: | The IP address of the internal interface (A1) as well as the subnet mask (as CIDR-notation) for the internal network. | 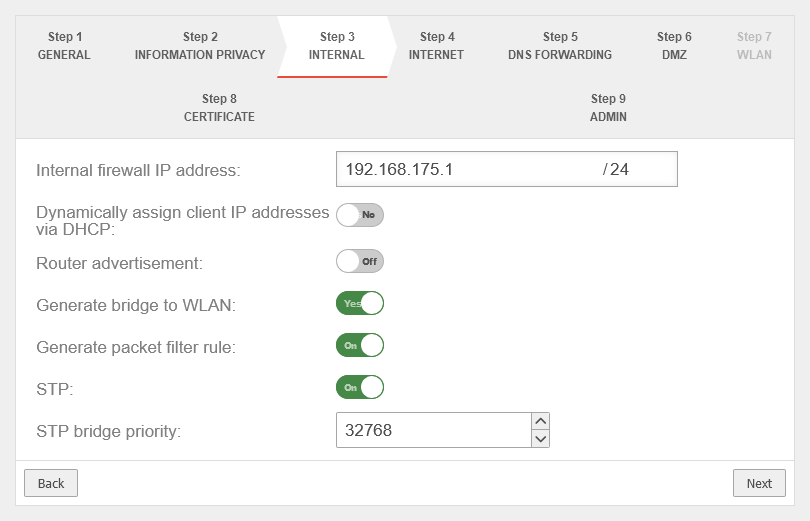 | |
| Dynamically assign Client IP Addresses via DHCP: | No | When enabled Yes, the UTM works as a DHCP server: All clients in the internal network receive an IP address via DHCP. This sets the UTM as the default gateway and DNS server for the clients. | |
| Generate WLAN Bridge: | No Default |
Creates a bridge so that this network and the WLAN are on the same network. | |
| Generate portfilter rule: Shown when Generate WLAN Bridge is enabled |
No | When activated, a port filter rule is automatically generated | |
| STP: Shown when Generate WLAN Bridge is enabled |
Off | When activated, STP (Spanning Tree Protocol) is used | |
| STP Bridge Priority: Shown when Generate WLAN Bridge is enabled |
32768▴▾ Default |
The priority of the STP Bridge is set | |
Step 4 - InternetThis is where the Internet connection is configured on the external interface (A0). | |||
Connection type PPPoE / VDSL Connection type:
| |||
| With this type, an ADSL or SDSL modem is connected to the external interface (A0). The connection is initiated by the UTM. | |||
| Username: | (Shares ISP) | The login information is provided by the ISP (Internet Service Provider). | 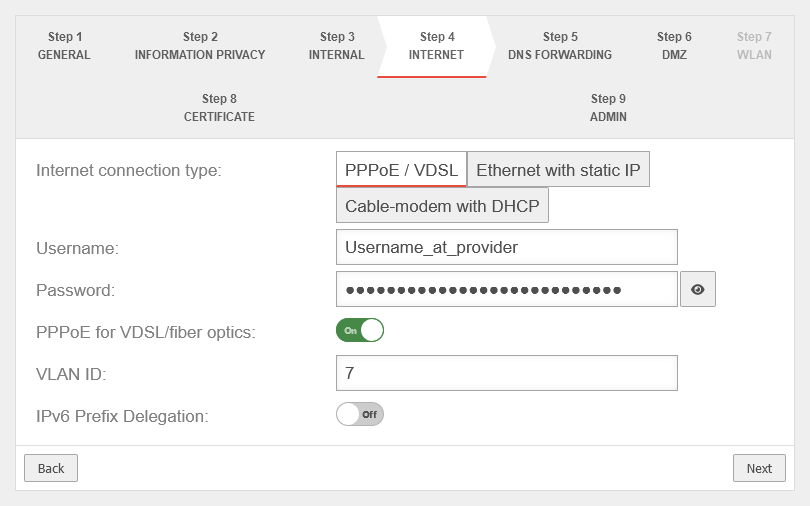 |
| Password: | (Shares ISP) | ||
| PPPoE for VDSL/fiber optics: | Off | Check the box if PPPoE is connected via a VDSL modem or via fibre. | |
| VLAN ID: Shown when PPPoE for VDSL/fiber optics is enabled |
7 | The VLAN ID is usually specified by the network operator | |
| IPv6 Prefix Delegation: | Off | Allows an IPv6 network assigned by the Internet Service Provider to be split into /64 networks and assigned to individual interfaces via Router Advertisement. Example: Network assigned by ISP: 2001:0db8:aaaa:bb::/56 Networks distributed at internal interfaces via router adviertisement: 2001:0db8:aaaa:bb00::/64 2001:0db8:aaaa:bb01::/64 | |
notempty
The option Use DNS server of the provider has been moved to step 5 | |||
Connection type Ethernet with static IP Connection type:
| |||
| With this connection type, a router is connected to the external interface (A0), which itself initiates the connection to the Internet. The login information of the provider is stored in the preceding router and not on the UTM. | |||
| External IP address: | The IP address of the external interface (A0) and the IP address range for the external network (subnet mask in CIDR notation). The default is an already existing IP address, if applicable. The external interface receives an IP address via DHCP by default, provided a DHCP server is available in the external network. |
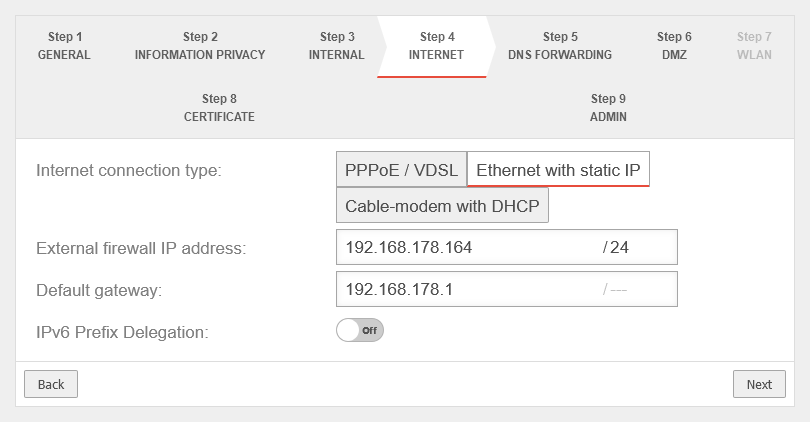 | |
| Default Gateway: | IP address of the default gateway for the UTM so that it knows which is the closest router for all networks that are not on an internal interface: As a rule: the Internet. | ||
| IPv6 Prefix Delegation: | Off | Allows an IPv6 network assigned by the Internet Service Provider to be split into /64 networks and assigned to individual interfaces via Router Advertisement. Example: Network assigned by ISP: 2001:0db8:aaaa:bb::/56 Networks distributed at internal interfaces via router adviertisement: 2001:0db8:aaaa:bb00::/64 2001:0db8:aaaa:bb01::/64 | |
Connection type Cable modem with DHCP Connection type:
Originally mostly devices that cable providers provided to their customers. | |||
| Also with this connection type, a router is connected to the external interface (A0), which itself initiates the connection to the Internet. The login information of the provider is stored in the preceding router and not on the UTM. |
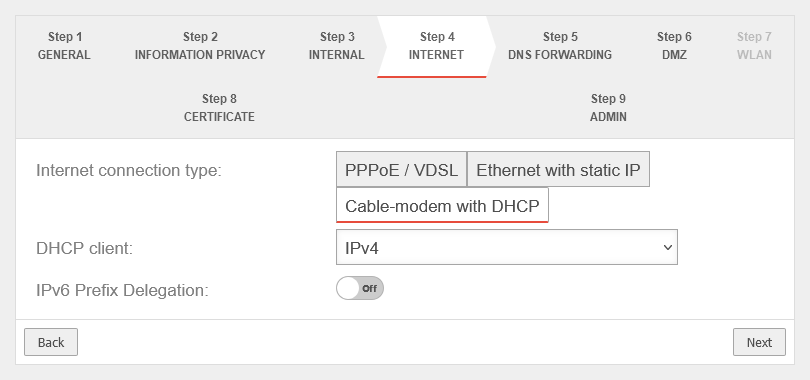 | ||
| DHCP Client: | Selection with which protocol the interface receives IP addresses from the preceding router with DHCP server. | ||
| Use the provider's DNS server: | Off | When activated, the provider's DNS server is used. | |
| IPv6 Prefix Delegation: | Off | Allows an IPv6 network assigned by the Internet Service Provider to be split into /64 networks and assigned to individual interfaces via Router Advertisement. Example: Network assigned by ISP: 2001:0db8:aaaa:bb::/56 Networks distributed at internal interfaces via router adviertisement: 2001:0db8:aaaa:bb00::/64 2001:0db8:aaaa:bb01::/64 | |
Connection type LTE / others Connection type:
| |||
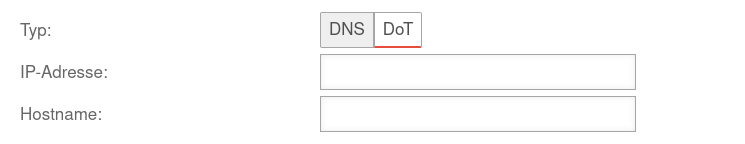
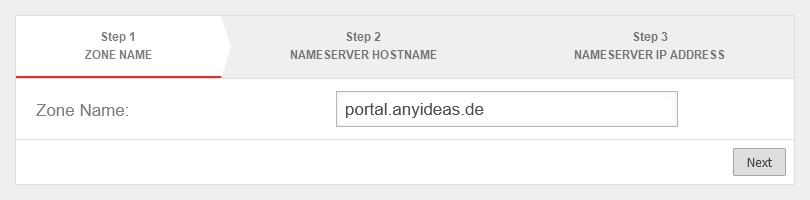
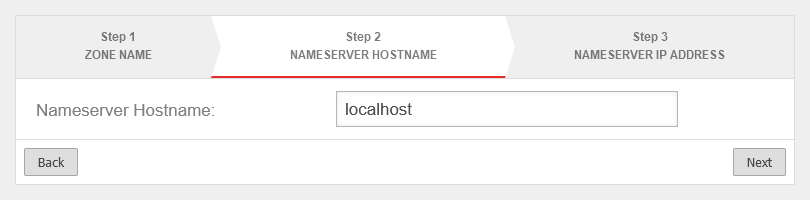
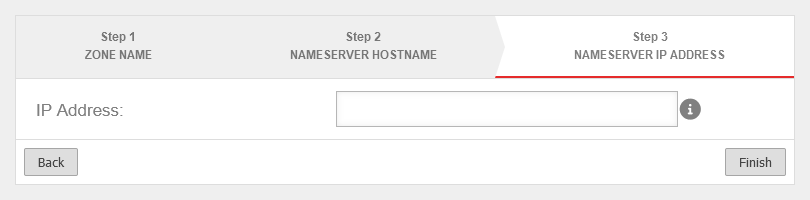
Step 5 - DNS Forwardingnotempty
New step from v14.0.1 The DNS forwarding of the name server can be configured here. There are the same options as under Area DNS Forwarding. For more detailed information, see the Nameserver article. | |||
notempty New in the installation wizard from v14.0.1 |
Adds DNS Forwarding. It is possible to select classic DNS or DNS over TLS (DoT). Further information in the Article on DNS forwarding in the nameserver. |
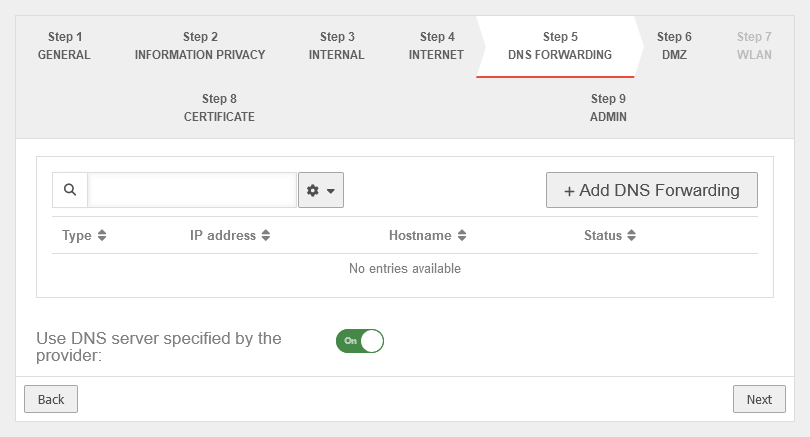 | |
| Use the provider's DNS server: | On | When activated, the provider's DNS server is used. | |
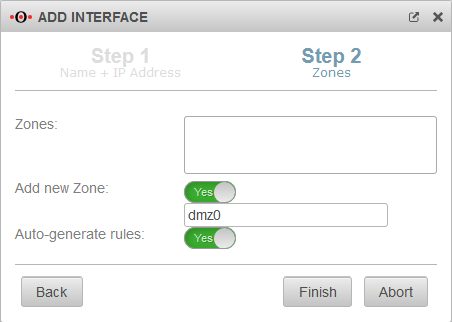
Step 6 - DMZThe Black Dwarf (G5) only has 2 interfaces. | |||
| DMZ IP address: | The IP address of the interface none and the subnet mask (as CIDR notation) for the DMZ network. | 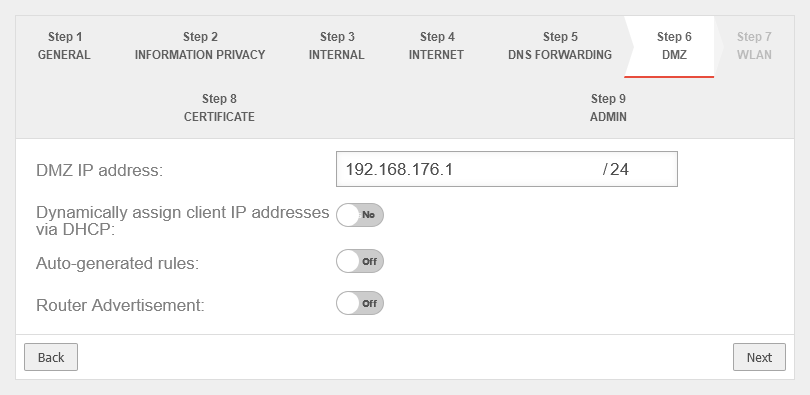 | |
| Assign the IP addresses to the clients in this network via DHCP: | No | When enabled Yes, the UTM works as a DHCP server: All clients in the DMZ network receive an IP address via DHCP. This sets the UTM as the default gateway and DNS server for the clients. | |
| Autogenerated rules: | No | Port filtering rules can be automatically created for this network, allowing traffic to the Internet on the interface to the external interface (A0). Likewise, rules are created that also allow traffic from the internal network into the DMZ network. notempty These any rules are intended for testing purposes and should be disabled and replaced with well-defined rules in production mode. | |
| Router Advertisement: | No | If the UTM has received an IPv6 prefix, it can advertise the subnet via router advertisement in the network segment behind the interface. (See article IPv6 Prefix Delegation) | |
| Generate WLAN Bridge: Only if a WLAN module is present |
No | Creates a bridge so that this network and the WLAN are on the same network. | |
Step 7 - WLANIn the delivery configuration, a WLAN module is installed in the Black Dwarf (G5). | |||
| WLAN IP address: Not in bridge mode |
The IP address of the WLAN interface (wlan0) and the subnet mask (as CIDR notation) for the WLAN network. In bridge mode, the setting from the internal network in which bridge mode was activated is used here. |
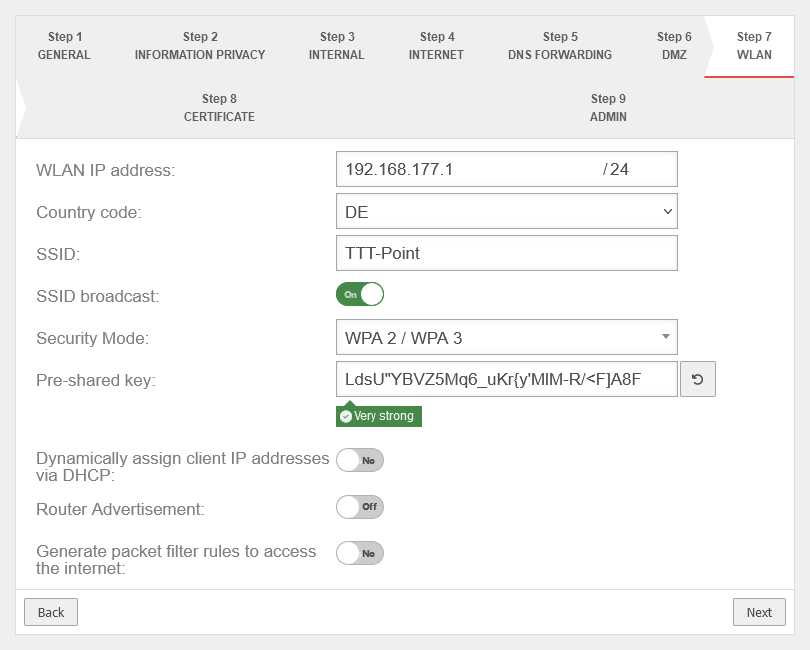 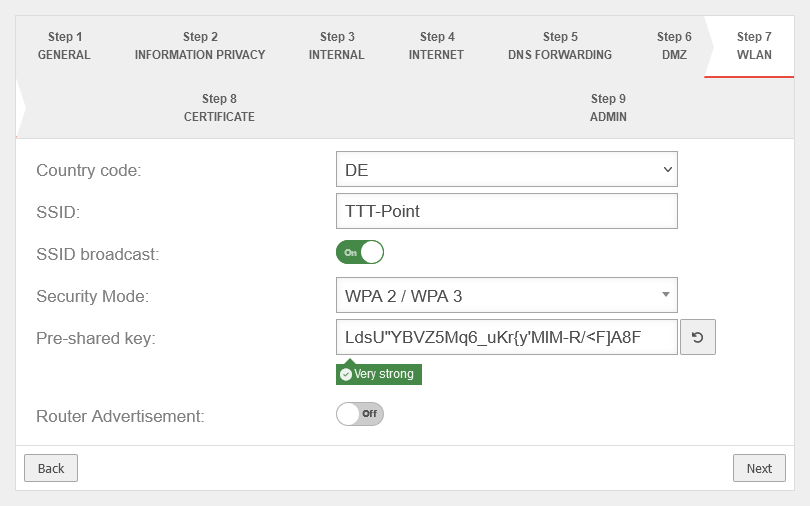 | |
| Country code: | The country code is used to determine which frequencies and which signal strengths may be used. The frequencies used and the transmission power can be found in a Wikipedia article. | ||
| SSID: | TTT-POINT | The Service Set Identifier (SSID) is the name under which the WLAN network is presented to the clients. This must be entered in any case. | |
| SSID Broadcast: | On | This option can be used to define whether the WLAN network can be seen by every client or whether the transmission of the SSID should be suppressed. (Off) | |
| Security Mode: | WPA | Is considered unsafe and only exists for backwards compatibility. (TKIP is used as encryption method) | |
| WPA2 | Standard with enhanced security AES128 is used as encryption method: https://en.wikipedia.org/wiki/WPA2 | ||
| WPA3 | Standard with highest available level of security AES256 and SAE are used as encryption methodes: https://en.wikipedia.org/wiki/WPA3 | ||
| Pre-Shared Key: | Don'tcopythis:Ei)#W~X$… | The base station and mobile device must have the same PSK (≙password). The security of the encryption depends directly on the length and complexity of the PSK! | |
| Automatically generates a very strong PSK | |||
| Assign the IP addresses to the clients in this network via DHCP: Not in bridge mode |
Off | When enabled, the UTM works as a DHCP server: All clients in the WLAN network receive an IP address via DHCP. This sets the UTM as the default gateway and DNS server for the clients. In bridge mode, the setting from the internal network in which bridge mode was activated is used here. | |
| Router Advertisement: | No | If the UTM has received an IPv6 prefix, it can advertise the subnet via router advertisement in the network segment behind the interface. (See article IPv6 Prefix Delegation) | |
| Generate rules for Internet access: Not in bridge mode |
Off | Port filtering rules can be automatically created for this network, allowing traffic to the Internet on the interface to the external interface (A0). Likewise, rules are created that also allow data traffic from the internal network into the WLAN network. notempty These any rules are intended for testing purposes and should be disabled and replaced with well-defined rules in production mode. In bridge mode, the setting from the internal network in which bridge mode was activated is used here. | |
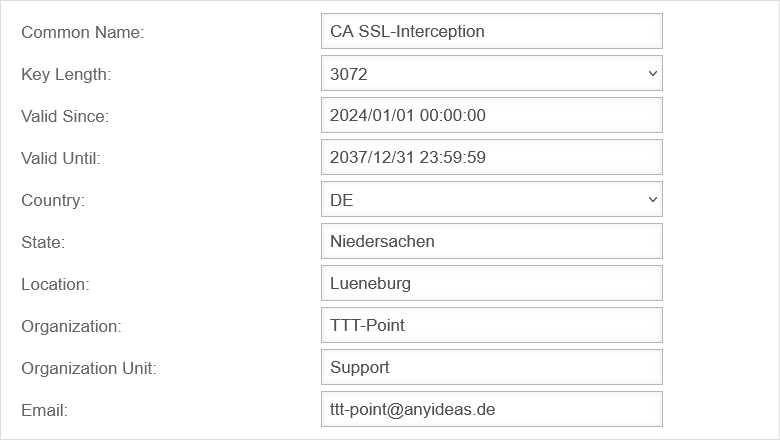
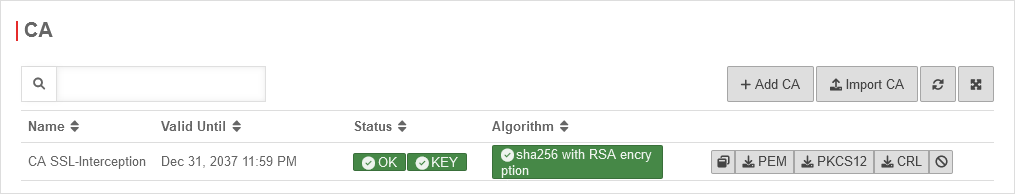
Step 8 - Certificate | |||
| Generate CA and server certificate: | Yes Default |
If Yes is enabled, a CA and server certificate will be generated. |
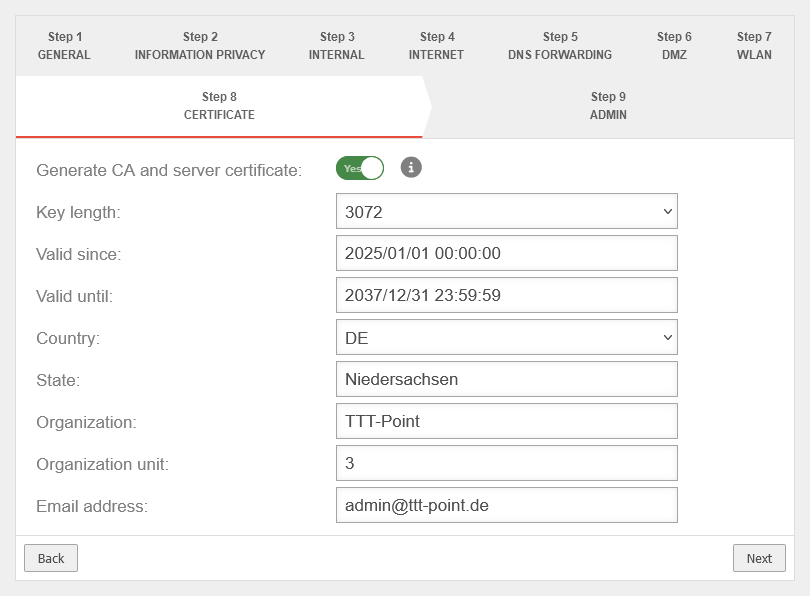 |
| Key length: | Select the bit length of the key | ||
| Valid since: | 2024/01/01 00:00:00 | ||
| Valid until: | 2037/12/31 23:59:59 | ||
| Country: | Detailed information is used to identify who issued the certificate | ||
| State: | Lower Saxony | ||
| Organization: | TTT Point | ||
| Department: | Support | ||
| Email address: | admin@ttt-point.de | ||
Step 9 - Administrator | |||
| User | admin | The username admin cannot be changed at this point | 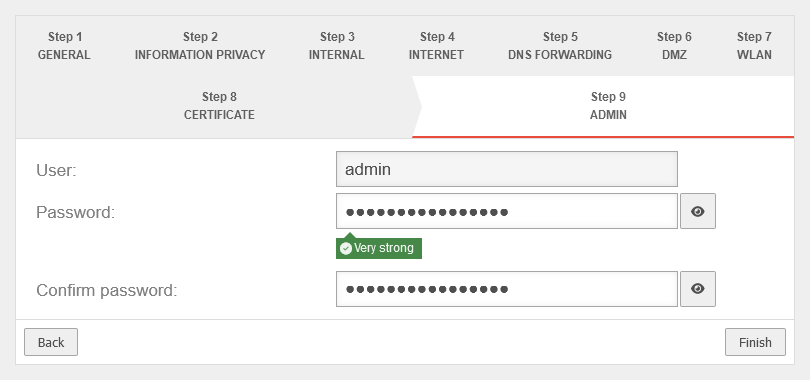 |
| Password: | •••••••••••••• |
Passwords must meet the following criteria:
| |
| Confirm password: | •••••••••••••• | ||
| |||
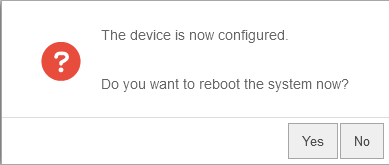
Reboot
| |||
| Do you want to reboot the system now? | In order for the configuration changes to be applied, the respective services must be restarted in the correct order. This is achieved by a reboot of the device. |
 | |
notempty
If your own IP address was changed to reach the admin interface of the UTM and the default was changed in Step 3 - Internal, the internal interface of the UTM is now located in this network. For further configuration, the IP address of your own computer must then be changed again. See the [1] | |||
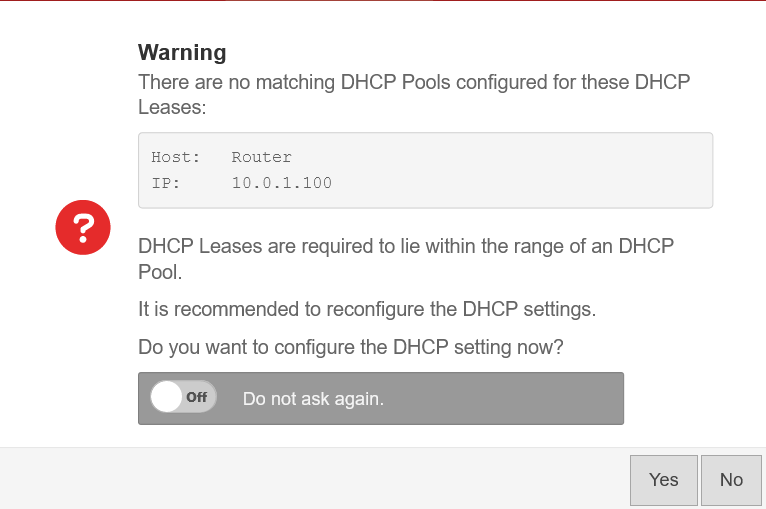
Configure interfacesnotempty
New as of v12.7.0 | |||
| Do you want to configure the interfaces now? | This message appears if not all existing interfaces are configured correctly. However, it is recommended to do this to prevent possible problems. The button opens the network configuration directly. | 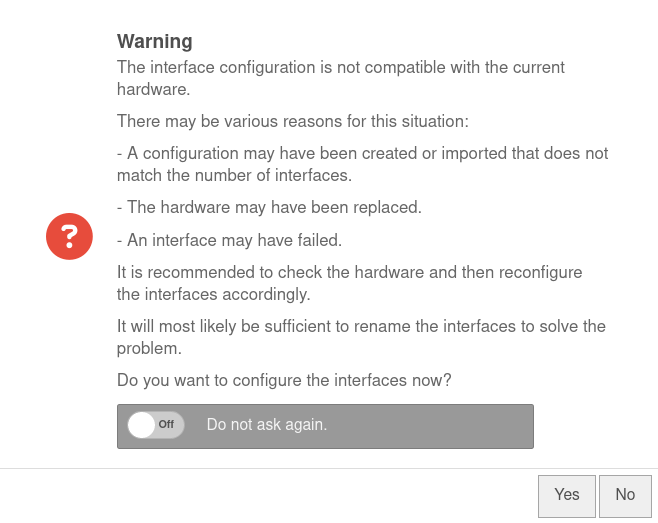 | |
| Do not ask again | Off | If this message is not desired, it can be set here so that it is not displayed again the next time you log in. | |
Servereinstellungen
Warnung: Der Anzeigetitel „Appliance Settings“ überschreibt den früheren Anzeigetitel „Installation wizard“.
Last adaptation to the version: 14.1.2
- Hinweis zu den aktuellen Zertifikats-Anforderungen hinzugefügt
- Several NTP server can be stored (v14.1.0)
```markdown
The BSI recommends—as of January 2025—key lengths of 3000 bits or more and SHA256
BSI – Technical Guideline – Cryptographic Methods: Recommendations and Key Lengths BSI TR-02102-1 | Chapter 2.3: RSA encryption
The default setting of the UTM for new certificates is RSA encryption with 3072 bits and SHA256 as the hash algorithm
| Caption | Value | Description | UTMuser@firewall.name.fqdnNetwork 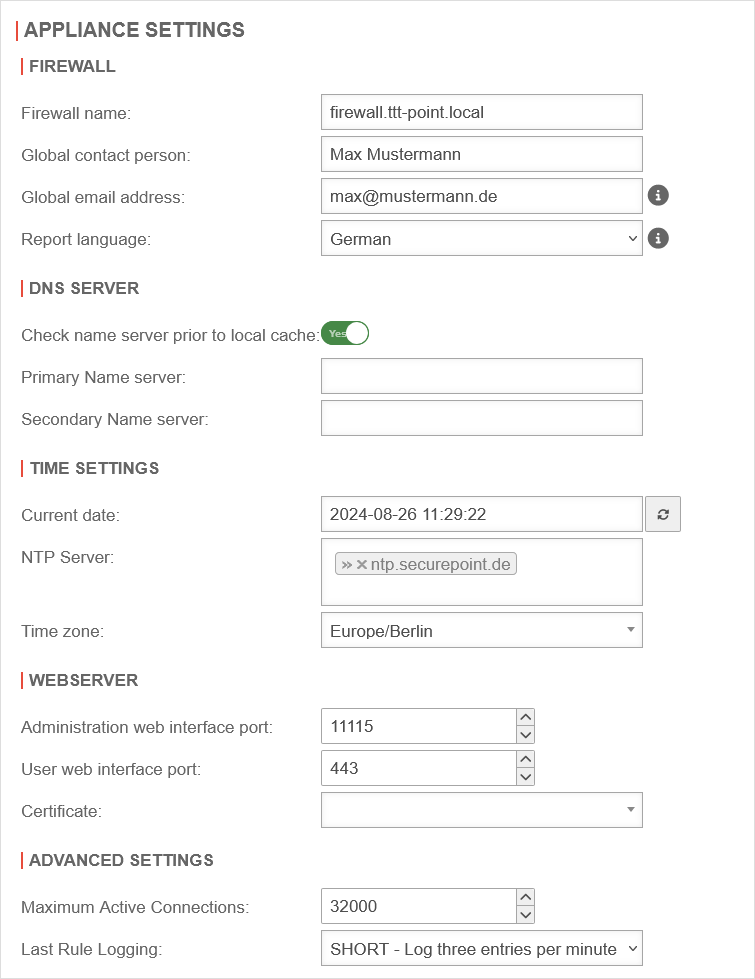 Appliance Settings Appliance Settings
|
|---|---|---|---|
FirewallFirewall
| |||
| Firewall Name: | Full Qualified Domain Name-Compliant firewall name. Here you can define how the UTM responds to requests. If the mail relay is to be used, it may be useful to enter the FQDN of the mail exchange (MX) here so that other mail servers can match it using the reverse resolution of the PTR resource record (PTR). Read out: | ||
| Global contact person: | This field is used to enter the name of the administrator or organization that will later be specified in the UTM error messages for queries. | ||
| Global email address: | An email address is entered here to which mails can be sent that otherwise cannot be delivered. Otherwise, undeliverable mails remain on the hard disk space, which can lead to the fact that the available space is no longer sufficient at some point and no more mails will be accepted. As of version v12.4.2 have an email address has to be stored here. Otherwise the mail connector and proxy will not start! A global email address will be requested when logging in. notempty
The global email address is also the postmaster address for the mail relay. Read out: | ||
| Report language: | German | Language in which UTM reports are sent. Alternatively to choose: English | |
DNS-Server DNS-Server
| |||
| Check Nameserver prior to local cache: | Off (Default) | The local cache of the UTM initially answers the DNS queries (corresponds to 127.0.0.1) as the primary name server. On activation, the name servers entered here will check the name resolution before the local cache of the UTM. | |
| Primary Nameserver: Secondary Nameserver: |
|
The IP addresses of two external name servers to which the UTM should forward the DNS queries can be entered here. notempty
Please do not enter a DNS server from your own internal network. | |
Time Settings Time Settings
| |||
| Current Date: | 2020-20-32 25:00:20 | The current time can also be entered manually. Refreshes the display. | |
| NTP-Server: notempty updated: Multiple entries possible |
»ntp.securepoint.de | The required NTP servers can be entered here. | |
| Timezone: | Europe/Berlin | Correct time zone | |
Webserver Webserver
| |||
Access may still be possible:
| |||
| Administration Webinterface Port: | 11115▴▾ | Port to reach the administration interface (which is used e.g. to display the web page shown in the image. In delivery state: 192.168.175.1:11115 | |
| User Webinterface Port: | 443▴▾ | Port to reach the user interface. This is used for example to access filtered mails and VPN configurations. notempty The user interface port must be changed if port 443 (HTTPS) is used for the reverse proxy. notempty
The user interface port must be changed if port 443 (HTTPS) is forwarded. | |
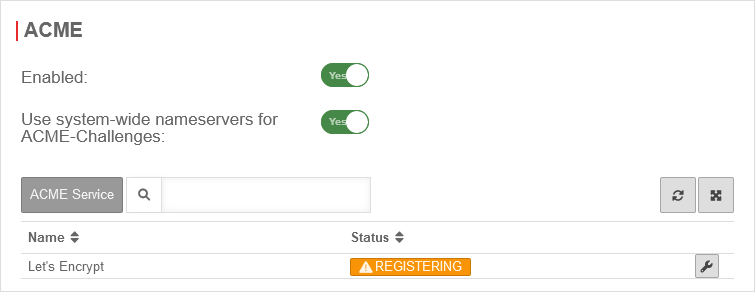
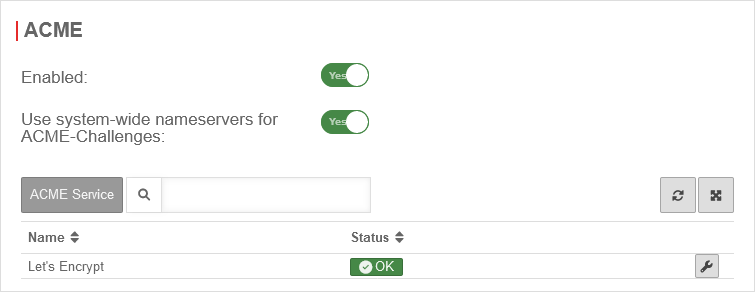
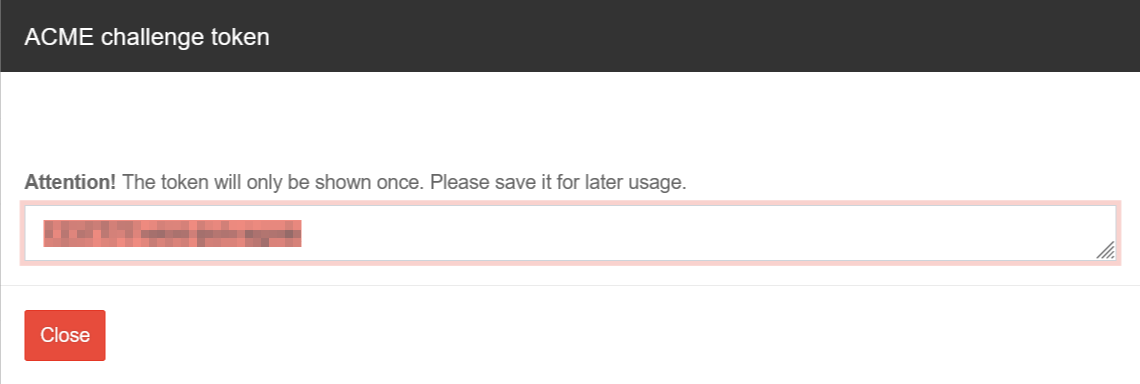
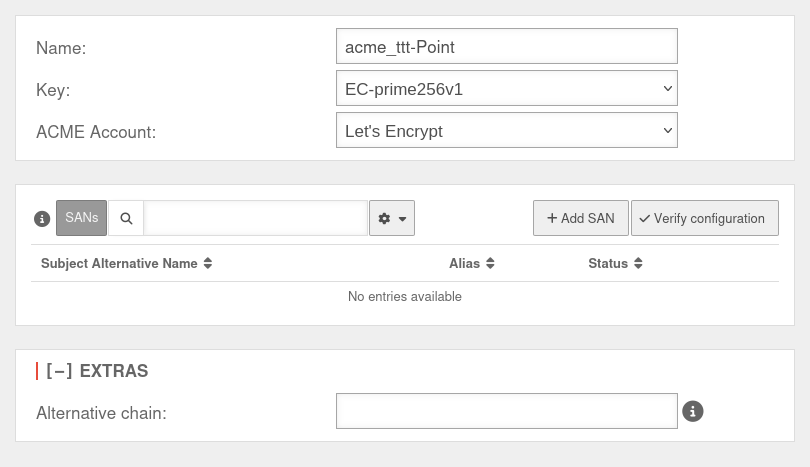
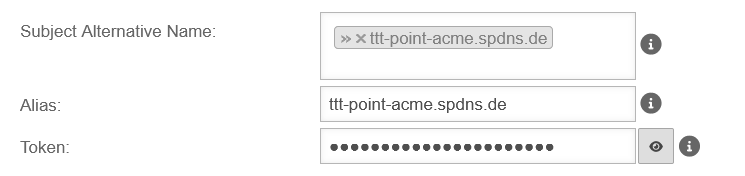
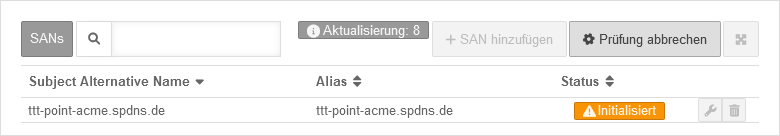
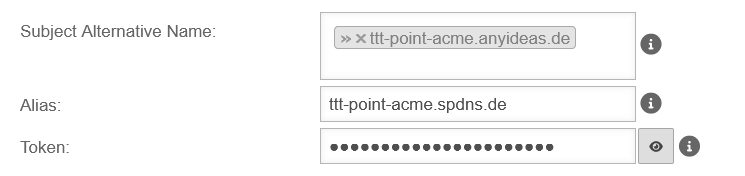
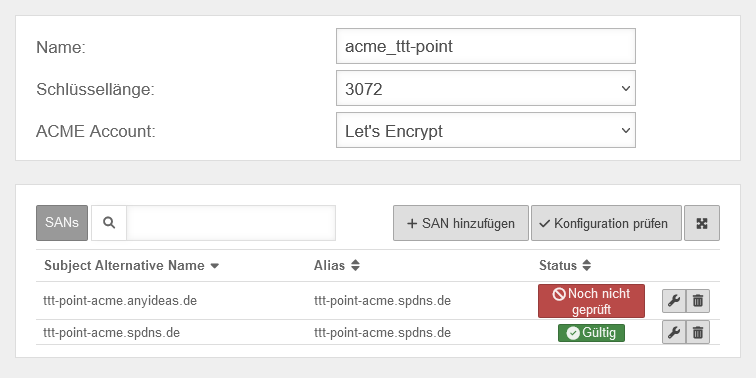
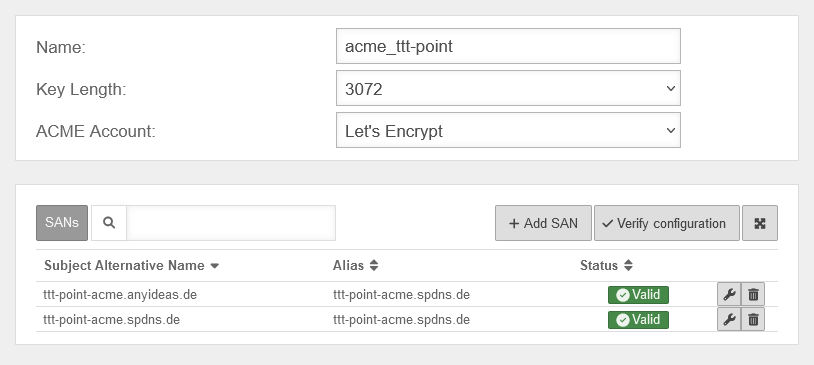
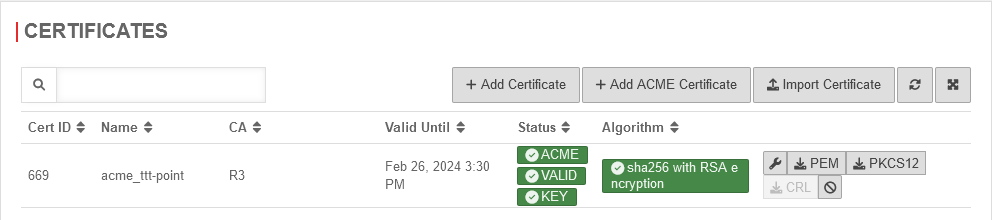
| Certificate: | ```markdown
notempty
If the UTM should be recognized by the browser with a valid certificate, proceed as follows:
| ||
Advanced SettingsAdvanced Settings
| |||
| Maximum Active Connections: | 32000▴▾ | Maximum number of active connections to the UTM. This includes:
| |
| Last-Rule-Logging: | The Last-Rule-Logging setting controls the number of messages that are written to the Syslog.
notempty
We recommend to leave the setting at short. | ||
Ethernet Konfiguration
Warnung: Der Anzeigetitel „Ethernet Interfaces“ überschreibt den früheren Anzeigetitel „Appliance Settings“.
Last adaptation to the version: 14.0.0
- New autonegotiation option: Default
- Speed and duplex are adjustable, even if autonegotiation is switched on
- Interfaces can be reset
Network interfaces General
| Only if → Show reset interface options On | |||
| Button | Description | UTMuser@firewall.name.fqdnNetwork 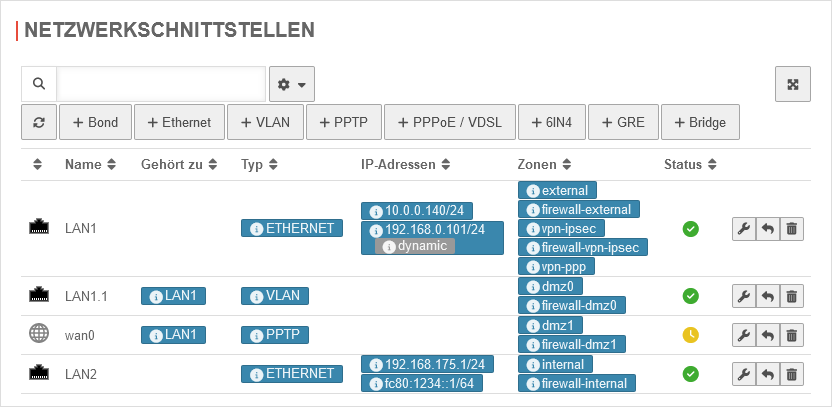 Network interfaces overview Network interfaces overview
| |
|---|---|---|---|
| Edit | Edit the respective interface | ||
| Reset notempty New as of v14.0.0 |
Resetting the interface options, this includes everything that is found with the CLI command interface get in the options column (list here), as well as the hotwire configuration. | ||
| Delete | Deletes the respective interface | ||
| In the table settings (), the display and content of the table can be configured. notempty
New as of v14.0.0 | |||
| Show reset of interface options: | Off | When activated On, the button for resetting a network interface is displayed |  |
| Style: | Customizes the style of the table for this table (for more detailed information on the configuration options, see Tools) | ||
| Entries per page: | Adjusts the entries per page of the table individually for this table (for more detailed information on the configuration options, see | ||
| Max height: | Adjusts the maximum display height of the table for this table individually (for more detailed information on the configuration options, see | ||
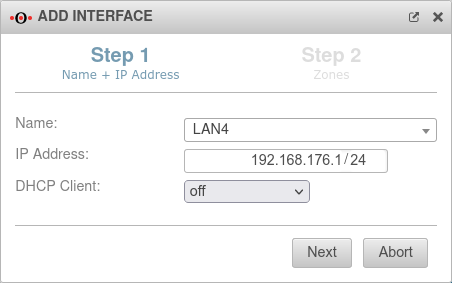
Creating an Ethernet interface
On UTMs with the naming scheme “LAN”x or “A”x, only interfaces that actually exist can be created.
Finish the wizard with the button.
Edit an Ethernet interface
The configuration of an Ethernet interface is done in the menu Area Network interfaces button
General
| Caption | Value | Description | UTMuser@firewall.name.fqdnNetworkNetwork configuration 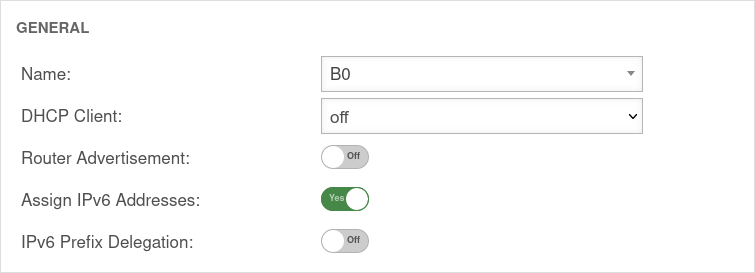
|
|---|---|---|---|
| Name: | LAN1 | The name of the interface cannot be changed afterwards. | |
| DHCP-Client: | Here the setting is made whether - and if so, for which IP protocol - the interface should obtain its IP addresses from a DHCP server. | ||
| Router Advertisement: | Off | If the UTM has received an IPv6 prefix (on an external interface), it can make the Default Gateway and the subnet known via router advertisement and at the same time distribute corresponding IPv6 addresses in the connected network. (See article IPv6 Prefix Delegation). | |
| Assign IPv6 addresses: | On | If it is not desired that the UTM distributes IPv6 addresses, but only the default gateway, then this option must be deactivated. | |
| IPv6 Prefix Delegation: | Off | Enables IPv6 prefex delegation to get IPv6 prefixes allocated on this interface. (For external interfaces only.) | |
SettingsSettings | |||
| MTU: | 1500▴▾ | The Maximum Transmission Unit specifies the maximum packet size that can be transmitted without fragmentation. Depending on the type of network (cable, Ethernet, VPN use), other values can help with connection problems here. |
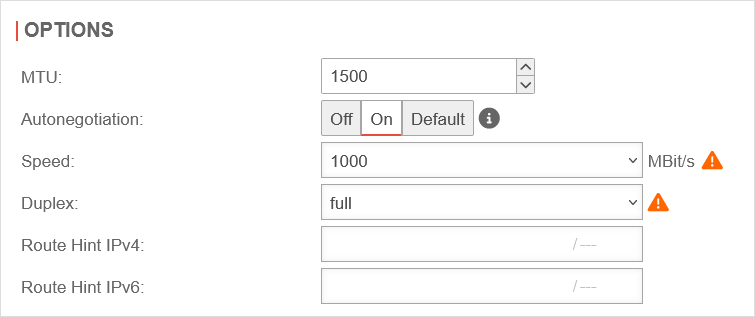 |
| Autonegotiation: notempty New option: Default |
Allows (on) or prohibits (off) Ethernet network ports from independently negotiating and configuring the maximum possible transmission speed and duplex mode.
Or does not perform an autonegotiation check (default) and therefore does not generate an error if the option cannot be changed. | ||
| Speed: notempty Even with autonegotiation activated |
MBit/s MBit/s MBit/s |
Speed of network communication | |
| Duplex: notempty Even with autonegotiation activated |
Duplex allows data packets to be sent and received simultaneously. HUBs usually only support Halfduplex. If autonegotiation mode is enabled at one end of the link and full-duplex operation is forced at the other end, the autonegotiating subscriber will recognize the link as half-duplex, resulting in a large number of transmission errors. →Wikipedia | ||
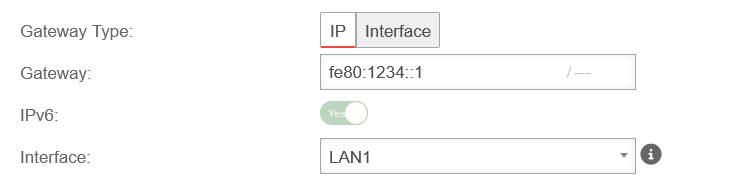
| Route Hint IPv4: | Via the field "Route Hint" it is possible to define the gateway of the interface. This has the advantage, for example, that only the interface (e.g. LAN3) has to be specified in routing and not directly the gateway IP. | ||
| Route Hint IPv6: | Via the field "Route Hint" it is possible to define the gateway of the interface. This has the advantage, for example, that only the interface (e.g. LAN3) has to be specified in routing and not directly the gateway IP. | ||
Enable autonegotiate: interface set name "LAN1" options [ pause_autoneg=1 ] | |||
IP AddressesIP Addresses | |||
| IP Addresses | »192.168.121.1/24»fc80:1234::1/64 | Under the menu item IP addresses one or more addresses can be assigned to an interface. | 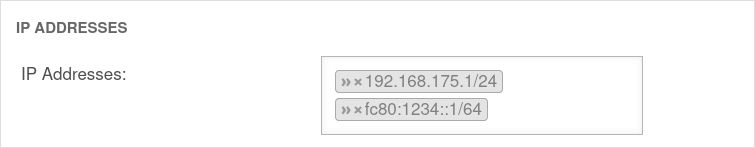 |
ZonesZones | |||
| Zones | »internal»firewall-internal»internal_v6»fireall-internal_v6 | Under the menu item Zones the zones of the interface are defined. If the zone internal is not assigned to an interface and the administration via the web interface is not explicitly enabled, the web interface can not be accessed anymore! |
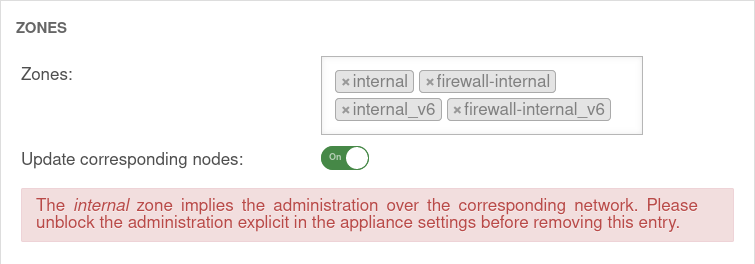 |
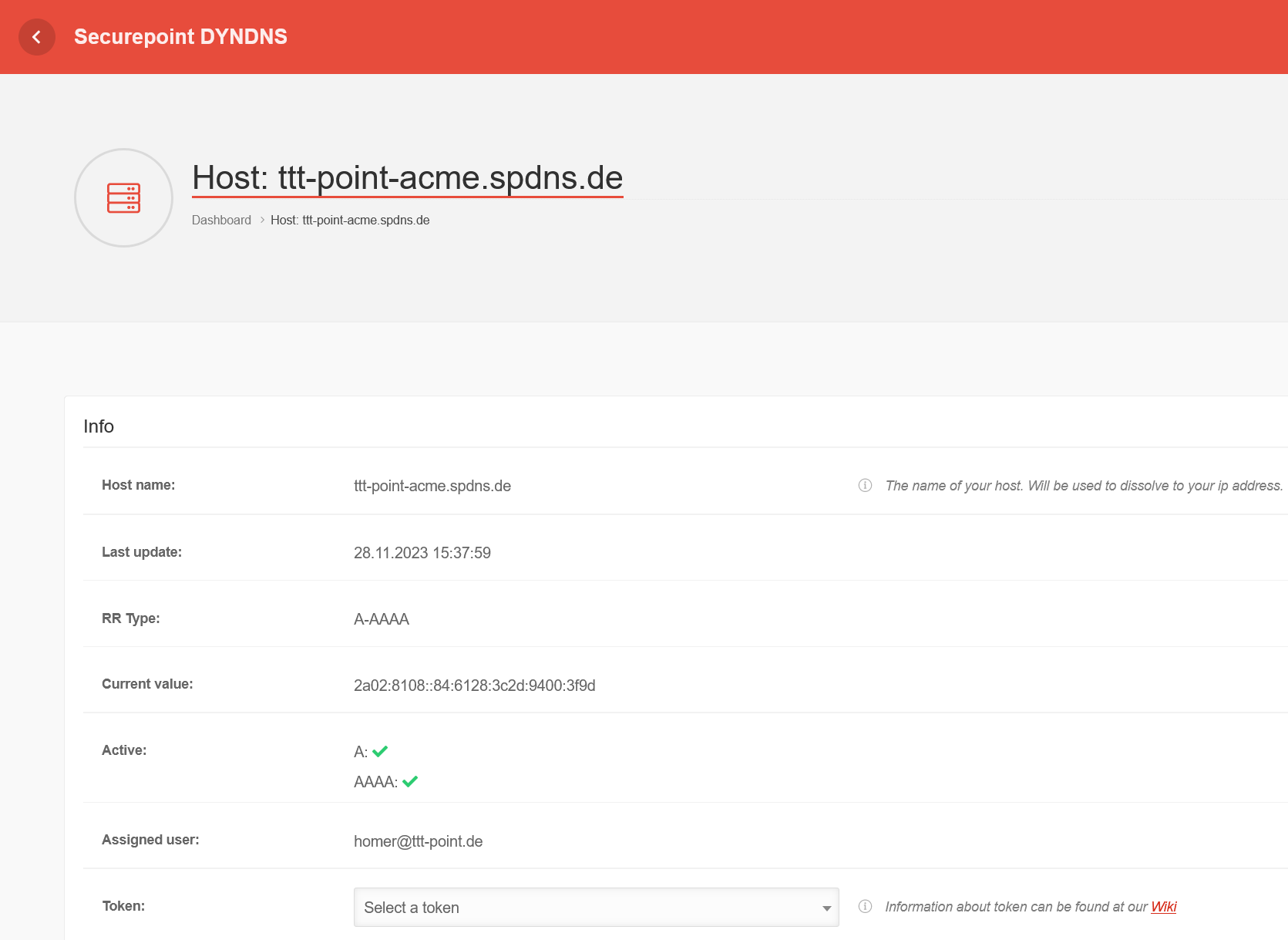
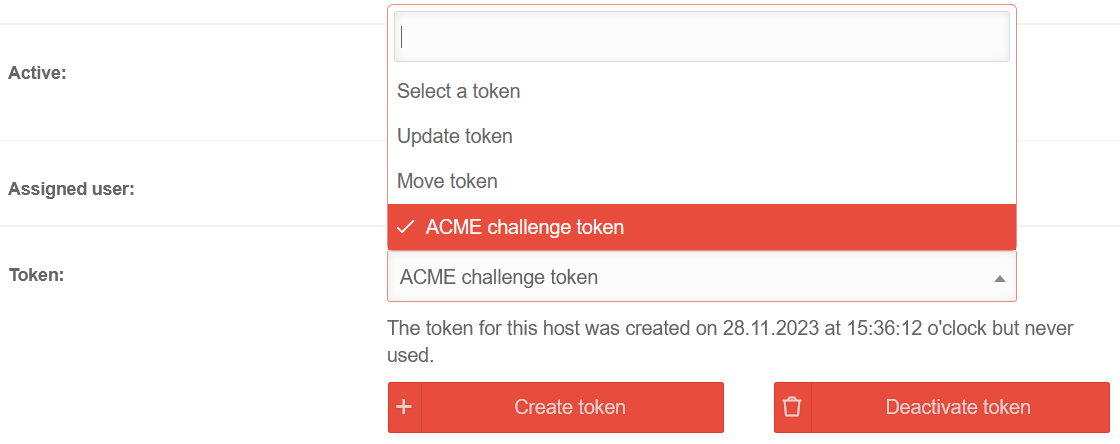
DynDNSDynDNS | |||
| Enabled: | Yes | Enables or disables (default) the DynDNS function | 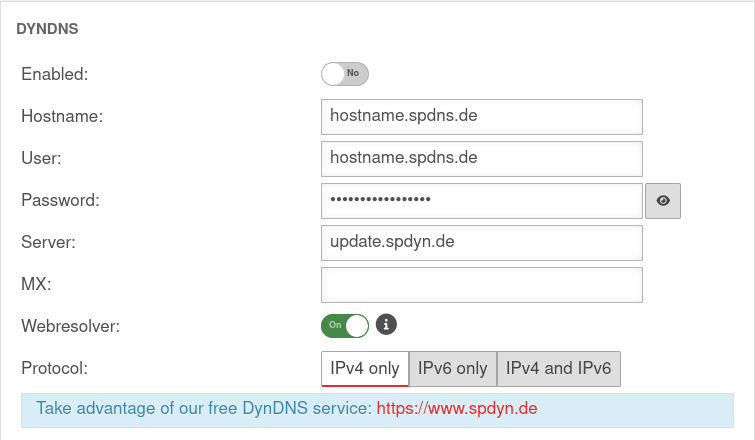 |
| Hostname: | hostname.spdns.de | Desired Hostname | |
| User: | hostname.spdns.de | The corresponding user name must be entered here
| |
| Password: | The password must be entered here
| ||
| Server: | update.spdyn.de | The securepoint update server | |
| MX: | |||
| Webresolver: | On | Must be activated if the NAT router is located before the DNS (i.e.: UTM → Fritzbox/Speedport → internet) | |
| Protocol: | The DNS service can be activated for IPv4 or IPv6 addresses only, or both IPv4 and IPv6. | ||
FallbackFallback | |||
| Fallback interface: | wan3 | Interface that stands in for the main interface in the case of a malfunction. The absence of malfunctions is verified by ping-checking an IP. Further notes on the configuration of a fallback can be found in a separate Wiki article. |
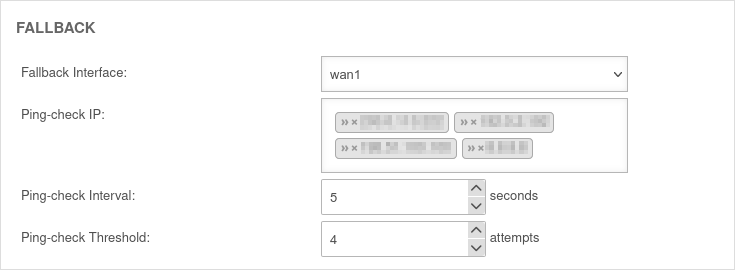 |
| Ping-check IP: | »203.0.2.203 »192.0.2.192 Example IPs must be replaced |
Host(s) to which the ping check is to be performed. This can also be a host in the internal network if necessary. This may also be a host in the internal network. If a ping check host does not respond, the subsequent IP address is tried immediately. If none of the ping check hosts responds, this is considered a failed attempt and checked again after the ping check interval. | |
| Ping-check Intervall: | 5▴▾ Seconds | Period between ping attempts | |
| Ping-check Threshold: | 4▴▾ Attempts | Number of failed ping attempts before switching to the fallback interface. | |
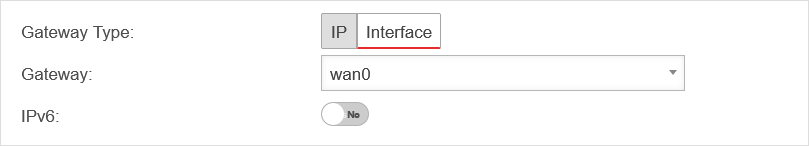
Create default route
Mobilfunkeinstellungen
Warnung: Der Anzeigetitel „Mobile Settings“ überschreibt den früheren Anzeigetitel „Ethernet Interfaces“.
Last adaptation to the version: 12.6.0
- Updated to Redesign of the webinterface
- 06.2025
- Incorrect 5G note removed
Vorbemerkung
Under Area Mobile a UMTS or LTE interface can be configured.
The mode used depends on the modem, the setup does not differ.
- The upgrade kit for the UMTS or LTE function can be obtained later for the Black Dwarf, the RC100 and the RC200.
- On request, it is also possible for the UMTS or LTE module to be installed before delivery.
- The devices or the upgrade kits are to be obtained exclusively from Securepoint or Wortmann AG.
Foreign products are not supported. - Detailed instructions for retrofitting can be found here. Installation Upgradekit
Available modules
| Name | Manufacturer | Function |
|---|---|---|
| MC7304 | Sierra Wireless Incorporated | LTE Modem |
| EM770W | Huawei | UMTS Modem |
| Qualcomm | LTE Modem |
Add mobile interface
| The Mobile interface is configured under Area Mobile button . The setup wizard for the Mobile interface opens. |
UTMuser@firewall.name.fqdnNetwork 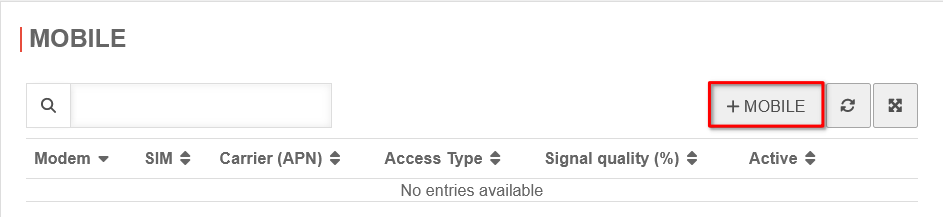 Add mobile interface Add mobile interface
|
Setup step 1 |
UTMuser@firewall.name.fqdnNetworkNetwork configuration 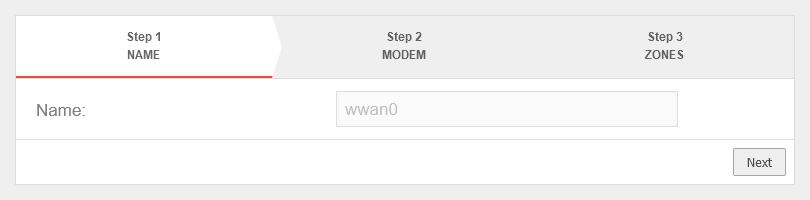
|
Setup step 2The module to be configured is selected. |
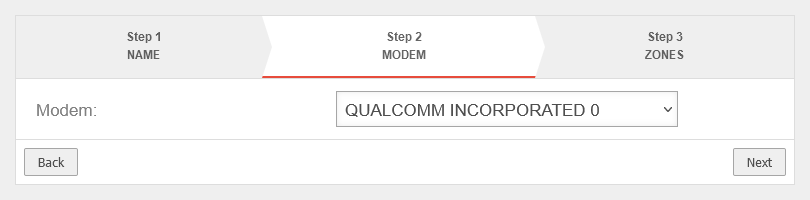 |
Setup step 3
|
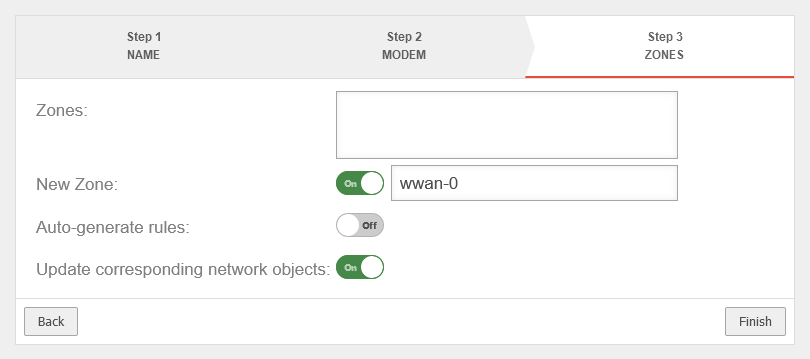 |
Manage SIM | |
Unlock SIMThe SIM card can be activated by clicking on the lock icon and entering the PIN. |
UTMuser@firewall.name.fqdnNetwork 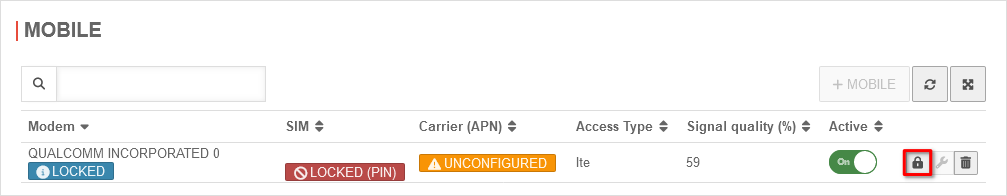 SIM cards unlocking SIM cards unlocking
|
Remove SIM PINThe PIN of a SIM can only be removed via SSH and with a root user.
| |
|
| |
Provider selectionAfter the SIM has been unlocked, the connection can be edited and the provider selected. The carriers differ by the respective APN. |
UTMuser@firewall.name.fqdnNetwork 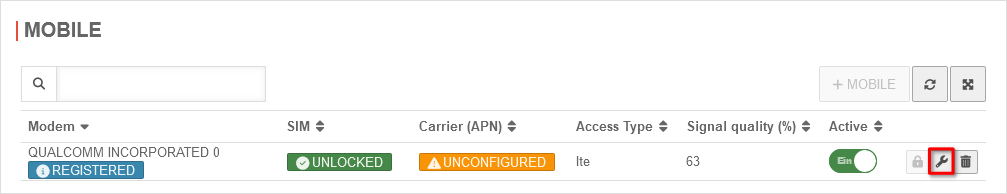
|
UTMuser@firewall.name.fqdnNetworkNetwork configuration 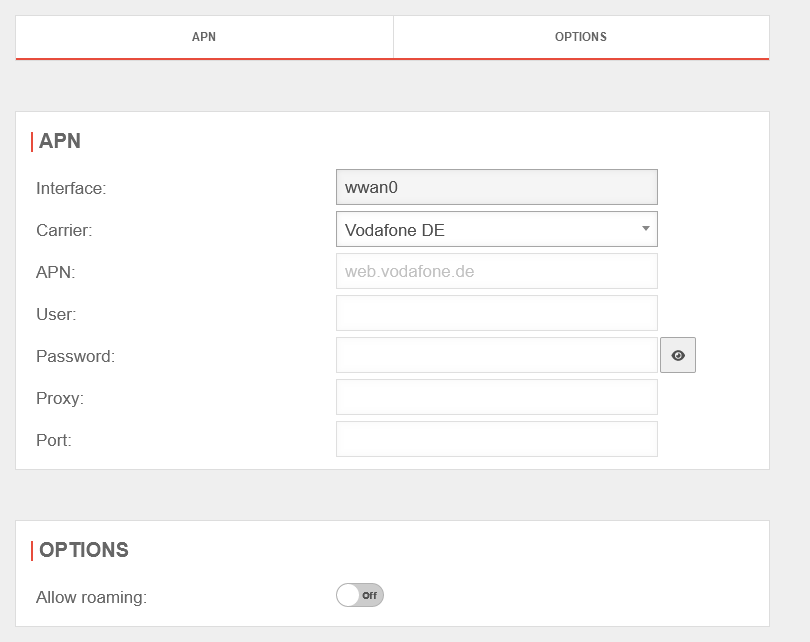
| |
Add routeA default route via the mobile interface (wwan0) is required so that a connection to the Internet can be established via the mobile interface. | |
|
| |
Signal qualityThe signal quality can be read out under Area Mobile. The signal quality is specified as a percentage. |
UTMuser@firewall.name.fqdnNetwork 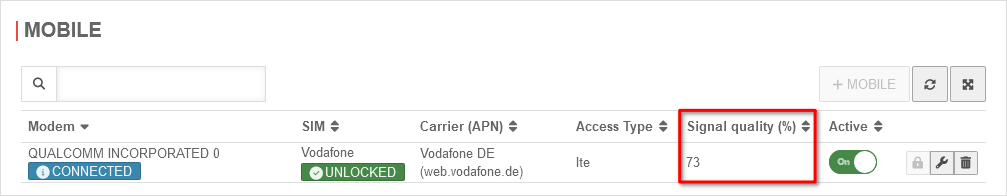 LTE signal with LTE modem LTE signal with LTE modem
|
UTMuser@firewall.name.fqdnNetwork 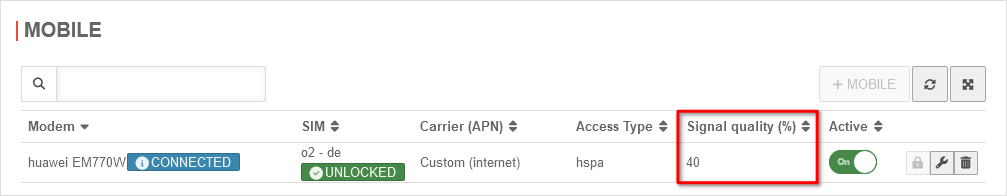 HSPA signal with UMTS modem HSPA signal with UMTS modem
| |
WLAN Konfiguration
Warnung: Der Anzeigetitel „Wifi function“ überschreibt den früheren Anzeigetitel „Mobile Settings“.
Last adaptation to the version: 12.6.0
- Updated to Redesign of the webinterface
- Note on maximum number of WLAN clients
WLAN functionality
- The Wi-Fi is available in the devices "Black Dwarf", "RC100" and "RC200" from the time of delivery or as a retrofit kit.
- The devices/retrofit kits can only be obtained from Securepoint GmbH or Wortmann AG.
- Detailed instructions for retrofitting can be found here.
As with any DMZ, rules and HideNATs may need to be created to allow access to the Internet/local network.
If a bridge is to be set up in which the Wi-Fi and the internal network are in the same IP network, the corresponding Instructions for Bridging must be used.
Call up the Wi-Fi configuration in the Area WLAN menu.
| Caption | Value | Description | UTMuser@firewall.name.fqdnNetworkNetwork configuration 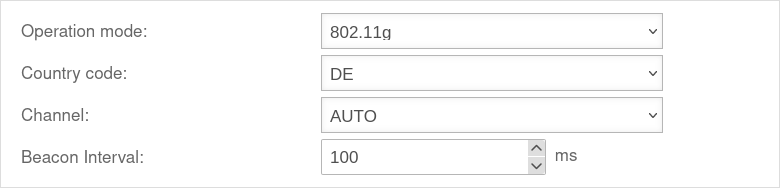
| ||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Operation mode: | Sets the speed and, if necessary, the frequency of the transmission. | ||||||||||||
| |||||||||||||
| Country code: | The country code is used to determine which frequencies and which signal strength may be used. The frequencies used and the transmission power can be found in a Wikipedia article. | ||||||||||||
| Channel: | The channel can be set individually or selected automatically, depending on the mode. | ||||||||||||
| Beacon-Interval: | 100▴▾(default) | Frequency in ms with which the base station transmits general information and management packets with identification data, to inform about its presence In fact, the value given is kμs (kilomicroseconds). One kμs corresponds to 1.024 milliseconds or 0.001024 seconds | |||||||||||
| Save and close | Saves the settings and closes the input dialogue. | ||||||||||||
Print WLAN QR codes |
Creates an html page with access codes in QR format for the WLANs and opens the print dialogue of the browser. |  | |||||||||||
WLAN Wizard |
Opens the Wi-Fi wizard Depending on the WLAN hardware available, up to 4 WLANs may be possible.
| ||||||||||||
Step 1 - IP address | |||||||||||||
| BSS: | wlan0 | Interface Name - is predefined and cannot be changed. (is part of the Basic service Set) | UTMuser@firewall.name.fqdnNetworkNetwork configuration 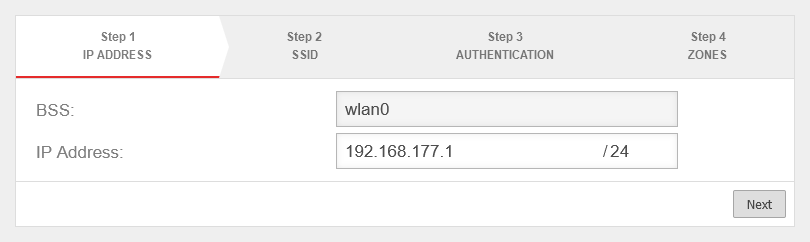 Step 1 - IP address Step 1 - IP address
| ||||||||||
| IP address: | IP address of the Wi-Fi interface. | ||||||||||||
Step 2 - SSID | |||||||||||||
| Network Name (SSID): | TTT-Point-WLAN | The name of the network that other devices must specify for a connection | 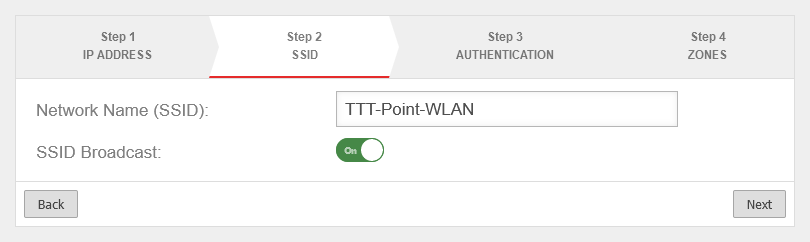 | ||||||||||
| SSID-Broadcast: | On | When activated, the WLAN is displayed for other devices. | |||||||||||
Step 3 - Authentication | |||||||||||||
| Security Mode: | 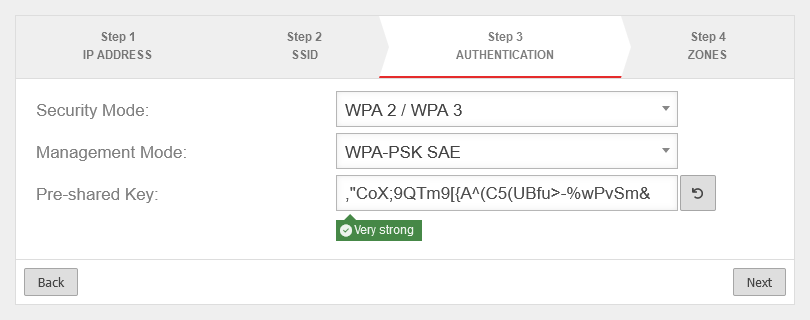 | ||||||||||||
| Standard with increased safety | |||||||||||||
| Standard with highest available safety. | |||||||||||||
| Management Mode: | Pre Shared Key. The base station and mobile device must have the same PSK (≙password). The security of the encryption depends directly on the length and complexity of the PSK! Short or easily guessed PSKs jeopardise network security. A secure PSK is automatically suggested, which can be regenerated with . | ||||||||||||
| Simultaneous Authentication of Equals: (Only with WPA3) . Also uses a PSK, but uses an improved method for key exchange. A unique but different Pairwise Master Key (PMK) is derived from the password for each client. Despite the use of a password that is the same for all clients, each client receives its own PMK. Pairwise Transient Keys (PTK) are derived from the PMK by means of a four-way handshake between the WiFi client and the authentication server. | |||||||||||||
| Extensible Authentication Protocol / WPA Enterprise: Authentication via a Radius Server. (This is set under ). | |||||||||||||
| Opportunistic Wireless Encryption: Encrypted connections without a password. Can be used for the Captive Portal, for example. | |||||||||||||
Step 4 - Zones | |||||||||||||
| New Zone: | On | Creates a new zone for the Wi-Fi. |
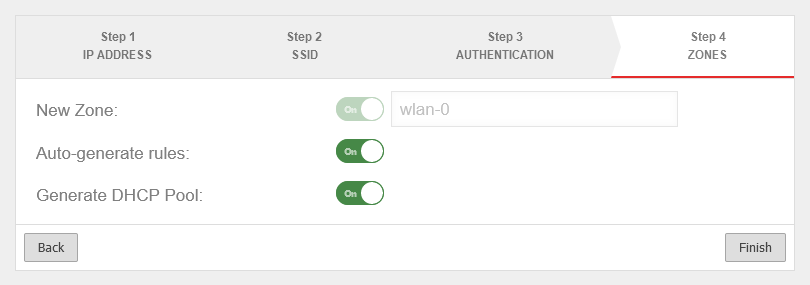 | ||||||||||
| Auto-generate rules: | On | Creates a port filter rule set for this interface with {spc any (Menu ) | |||||||||||
| Generate DHCP Pool: | On | Creates a DHCP pool with the selected network and the interface IP al router address. Edit in the DHCP Pools section. | |||||||||||
| Completing the wizard and saving the settings | |||||||||||||
Edit WLAN settingsEdit WLAN settings | |||||||||||||
| Area General | |||||||||||||
| BSS | Anyideas | Interface Name - is predefined and cannot be changed. (is part of the Basic service Set) | UTMuser@firewall.name.fqdn Network 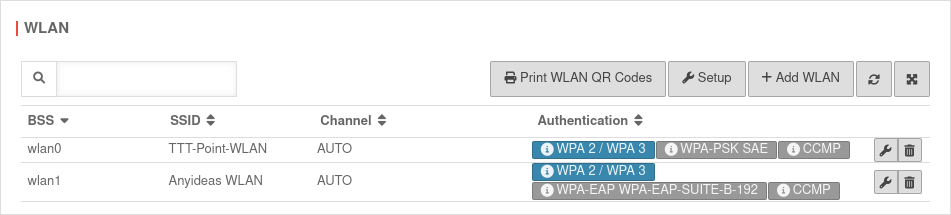 List of configured WLANs (max. 2) Depending on the WLAN hardware available, up to 4 WLANs may be possible. | ||||||||||
| Network Name (SSID) | TTT-Point-WLAN | The name of the network that other devices must specify for a connection | |||||||||||
| SSID-Broadcast | On | When activated, the WLAN is displayed for other devices. | |||||||||||
Area Authentication | |||||||||||||
| Settings as in wizard step 3 Additionally for WPA or WPA2: | |||||||||||||
| Encryption: | Encryption protocol based on the Advanced Encryption Standard (AES). A 128-bit key with a 48-bit initialisation vector is used. | ||||||||||||
| Uses simple encryption. Not available when using WPA3. | |||||||||||||
| Area Options | |||||||||||||
| AP Isolate: | On | End devices can only reach the firewall in the WLAN network. Clients in the same WLAN network cannot reach each other. | UTMuser@firewall.name.fqdn Network Network configuration 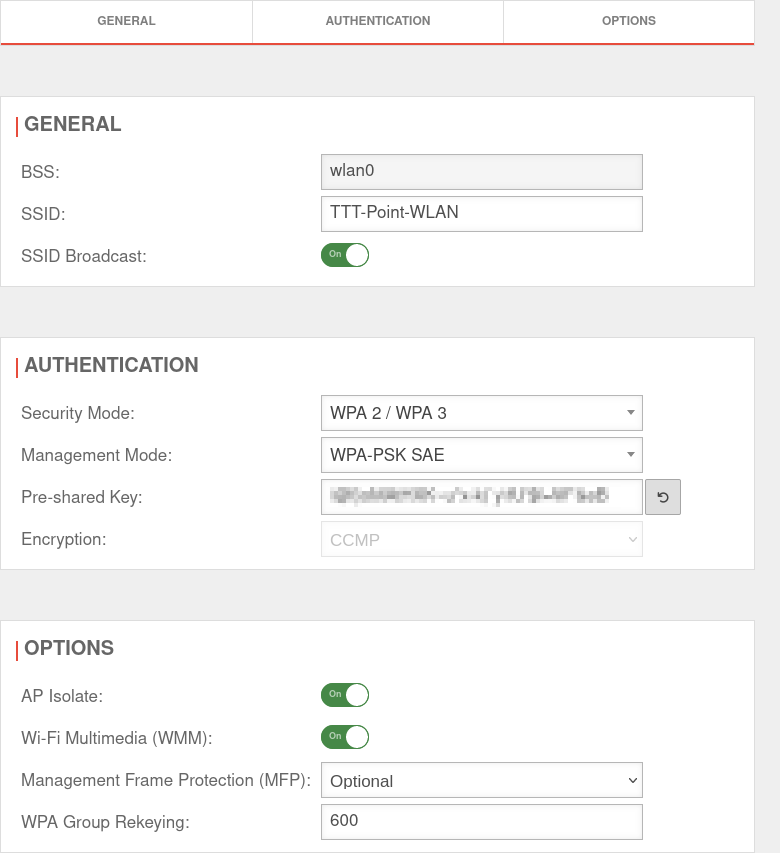 WLAN connection settings
| ||||||||||
| Wi-Fi Multimedia (WMM): | On | End devices can tag their frames, which affects the priority. | |||||||||||
| Management Frame Protection (MFP): | Enables encryption of the communication for the establishment and operation of the data connection according to IEEE 802.11w Increases network security and prevents e.g. Man in the Middle attacks. Requires WPA2 or WPA3 | ||||||||||||
| WPA Group Rekeying: | 600(default) | The entered value indicates the time interval in seconds by which the encryption is renegotiated. | |||||||||||
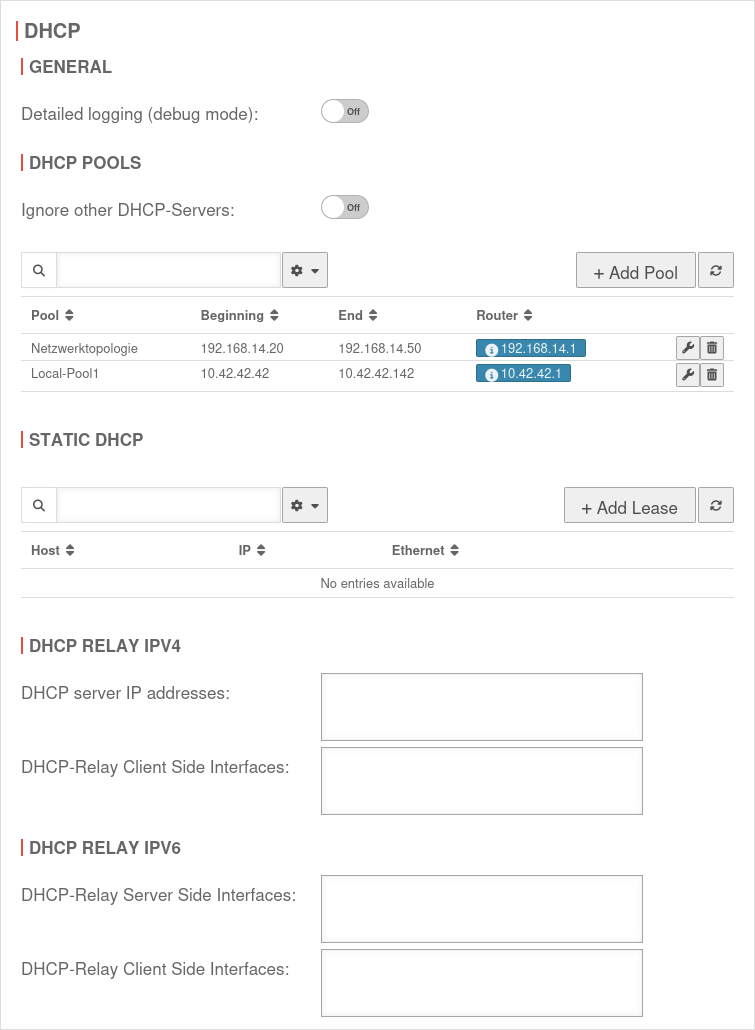
DHCP-Server IPv4
Warnung: Der Anzeigetitel „DHCP-Server IPv4“ überschreibt den früheren Anzeigetitel „Wifi function“.
Last adaptation to the version: 14.1.1
- Neuer Abschnitt Erweiterte Einstellungen bei Pool bearbeiten
- The dialog design has been revised
- 01.2026
- Hinweis zu dynamischen Leases
Prepare IP address ranges
UTMuser@firewall.name.fqdnNetwork 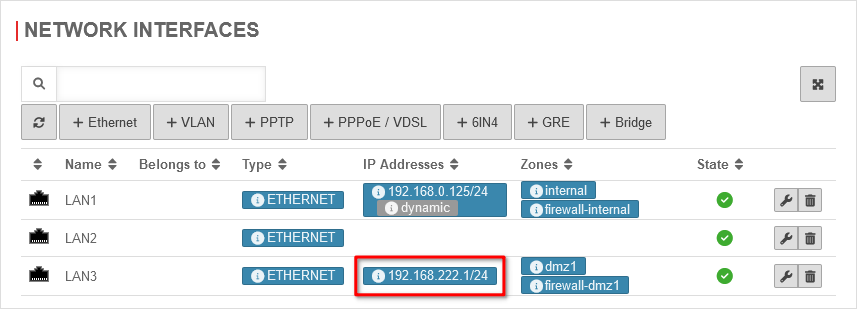 Network interfaces
Network interfaces
For the firewall to function as a DHCP server in a network, a fixed IP from the network range must be configured on the corresponding interface. In this example, IP addresses are assigned in network 192.168.222.0/24. To achieve this, an IP from this network is added to the interface. LAN3 → → IP addresses → In the selection box, enter or select the IP address from the desired network with the desired subnet mask, if applicable. Here 192.168.222.1/24
Set up DHCP server
General
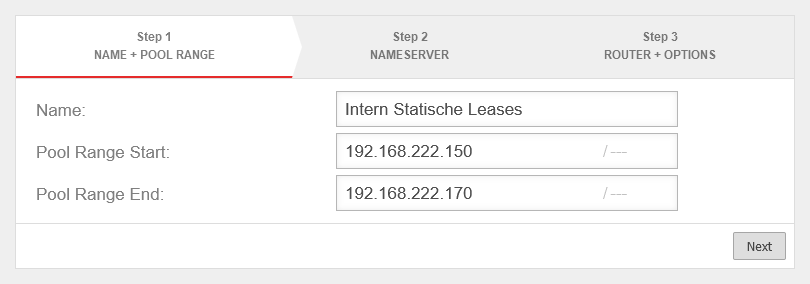
In the example, the following IP addresses are assigned
Pool start address:
Pool end address:
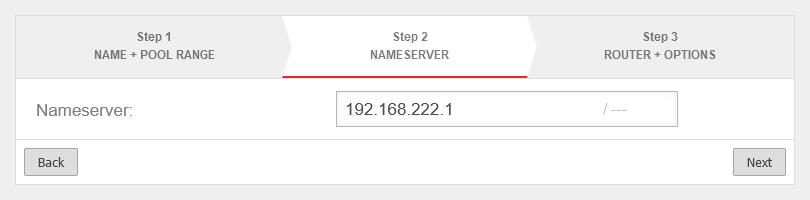
Either the IP of a public DNS server or the IP of the firewall itself can be entered here. In this example, the clients use the firewall itself as DNS.
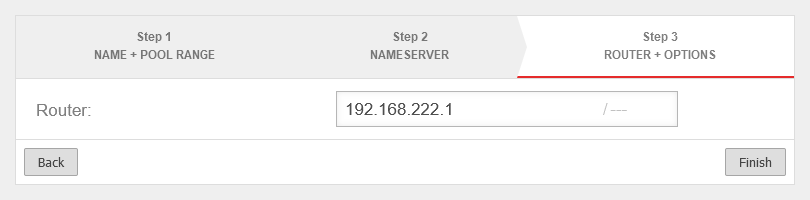
Edit pool
After the pool has been created correctly, the pool start and end address can be changed and other parameters of the DHCP pool can be set up to be passed to the DHCP client.
General
UTMuser@firewall.name.fqdnNetworkNetwork configuration 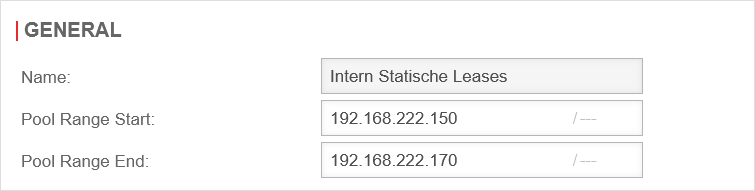 Edit pool general area
Edit pool general area
Changes to the pool range start and pool range end possible
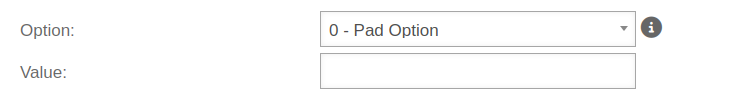
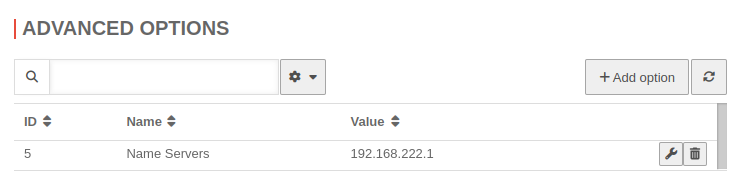
Options - DHCP Optionen
| Option | Option number | Value | Description | UTMuser@firewall.name.fqdnNetworkNetwork configuration 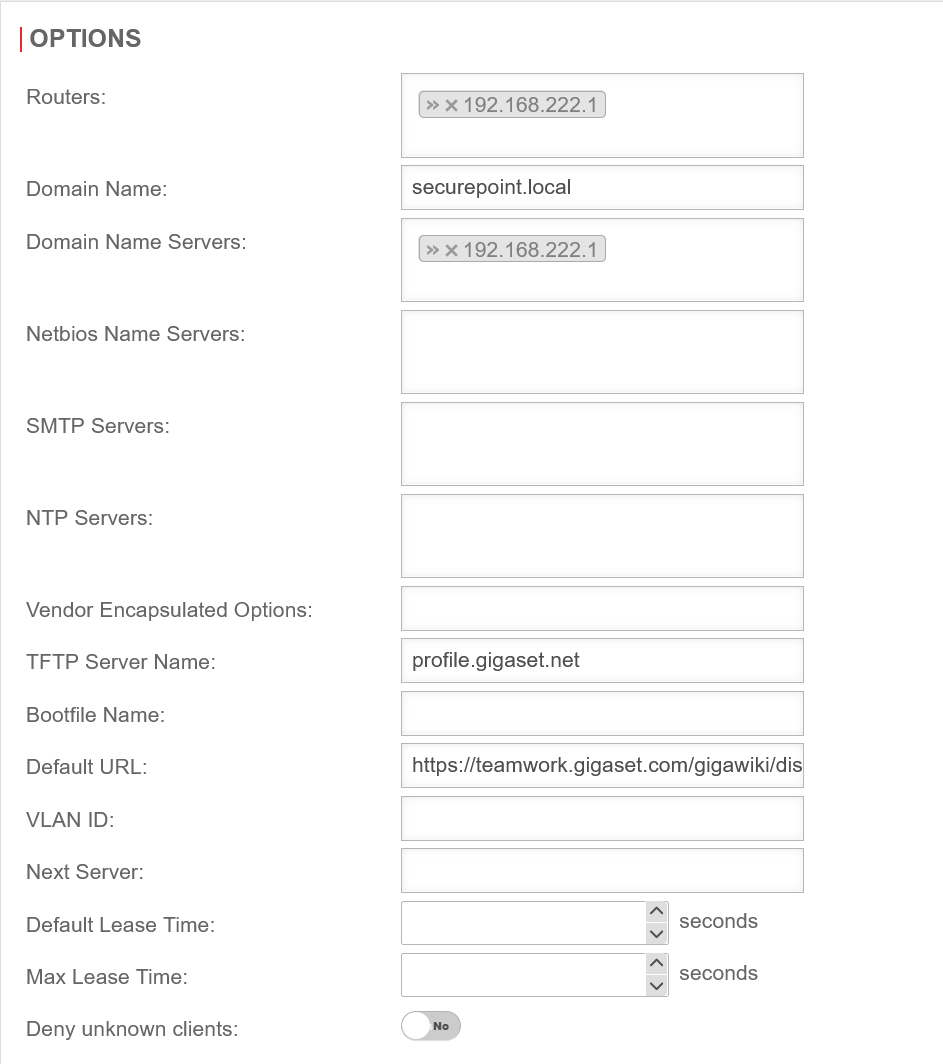 Edit pool general area Edit pool general area
|
|---|---|---|---|---|
| Router: | 3 | »192.168.222.1 | Router configured as in step 3 | |
| Domain name: | 15 | securepoint.local | Name of the domain in which the DHCP leases are assigned | |
| Domain name server: | 5 | »192.168.222.1 | Name server as configured in step 2 | |
| Netbios name server: | 44 | NetBIOS over TCP/IP Name Server Option | ||
| SMTP-Server: | 69 | Simple Mail Transport Protocol (SMTP) Server Option | ||
| NTP Server: | 41 | Servers should be listed in order of preference. | ||
| Vendor Encapsulated Options: | 43 | Values must be given coded. | ||
| TFTP Server Name: | 66 | profile.gigaset.net | The IPv4 address, or the hostname of the TFTP server option tftp-server-name text; | |
| Bootfile Name: | 67 | The name of the bootfile file option bootfile-name text; | ||
| Default URL: | 114 | https://teamwork.gigaset.com/gigawiki/display/GPPPO/DHCP+option+114 | Default URL option default-url string; | |
| VLAN ID: | 132 | The ID of the VLAN used option vlan-id code 132 = text; option vlan-id "128"; | ||
| Next Server: | The IPv4 address of the Next server | |||
| Default Lease Time: | 51 | 600 Seconds | Default validity period of the IP address if the client has not requested an explicit duration. | |
| Maximal Lease Time: | 7200 Seconds | Maximum validity period of the IP address in seconds that the client may receive when explicitly requested. | ||
| Reject unknown clients: | No | If activated Yes, an IP address is only assigned if there is a entry at Static DHCP tab for the MAC address of the client. notempty Changed standard behaviourab v12.7: The static lease entry for the DHCP must be in the same pool to be considered known. The static lease entry for the DHCP must be in the same pool to be considered known. | ||
Erweiterte Einstellungen
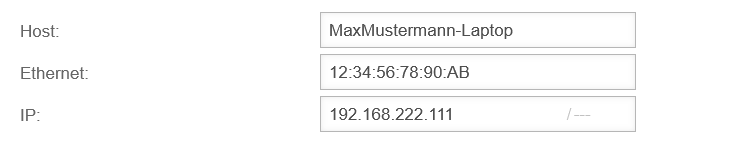
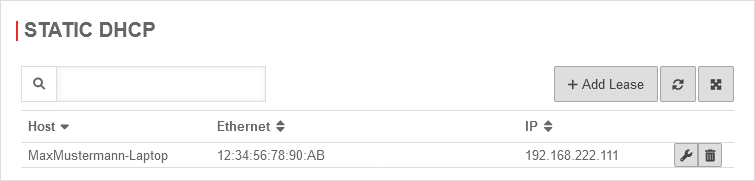
Static DHCP
If hosts are to be assigned predefined IP addresses ( fixed IPs bound to the MAC address, but assigned by the UTM), these IPs can be reserved with static leases:
Configuration under Area Static DHCP button
Static leases outside a pool
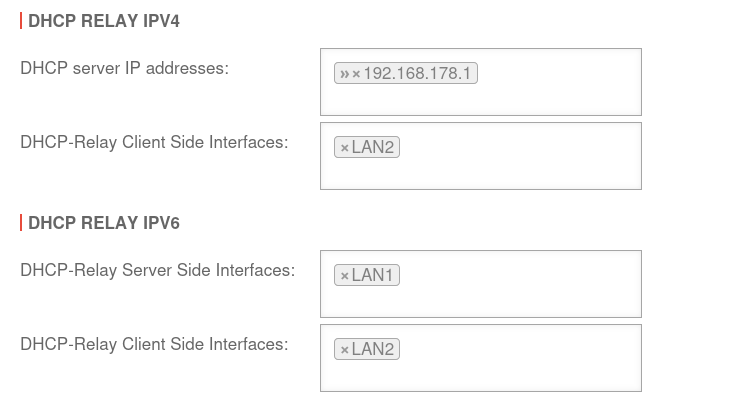
Configuration of DHCP-Relay
With the DHCP relay, devices can receive their network configuration dynamically via the network, even if the DHCP server is located in another subnet.
Widget
In the administrator interface of the UTM, there is a DHCP widget that provides an overview of the existing DHCP connections.
Further information can be found in the Wiki article UTM Widgets.
Zoneneinstellungen
Warnung: Der Anzeigetitel „Zone settings“ überschreibt den früheren Anzeigetitel „DHCP-Server IPv4“.
Last adaptation to the version: 12.6.0
- Updated to Redesign of the webinterface
Introduction
The zone concept defines through which interface an object (host or network) reaches the NextGen UTM.
To achieve this, it is bound to an interface in the network configuration, and in the rule set to a network object.
The zone concept
Create a new zone
UTMuser@firewall.name.fqdnNetworkZone Configuration 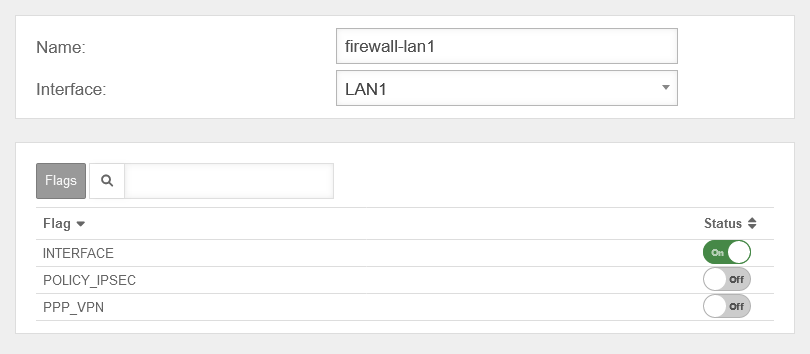 Add zone
Add zone
A new zone is created under by clicking the button.
A zone can be created only without, or with an already created interface.
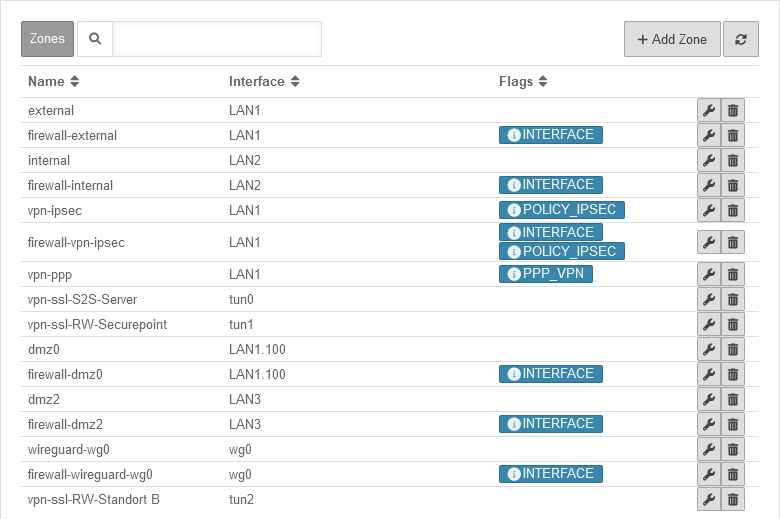
The zones
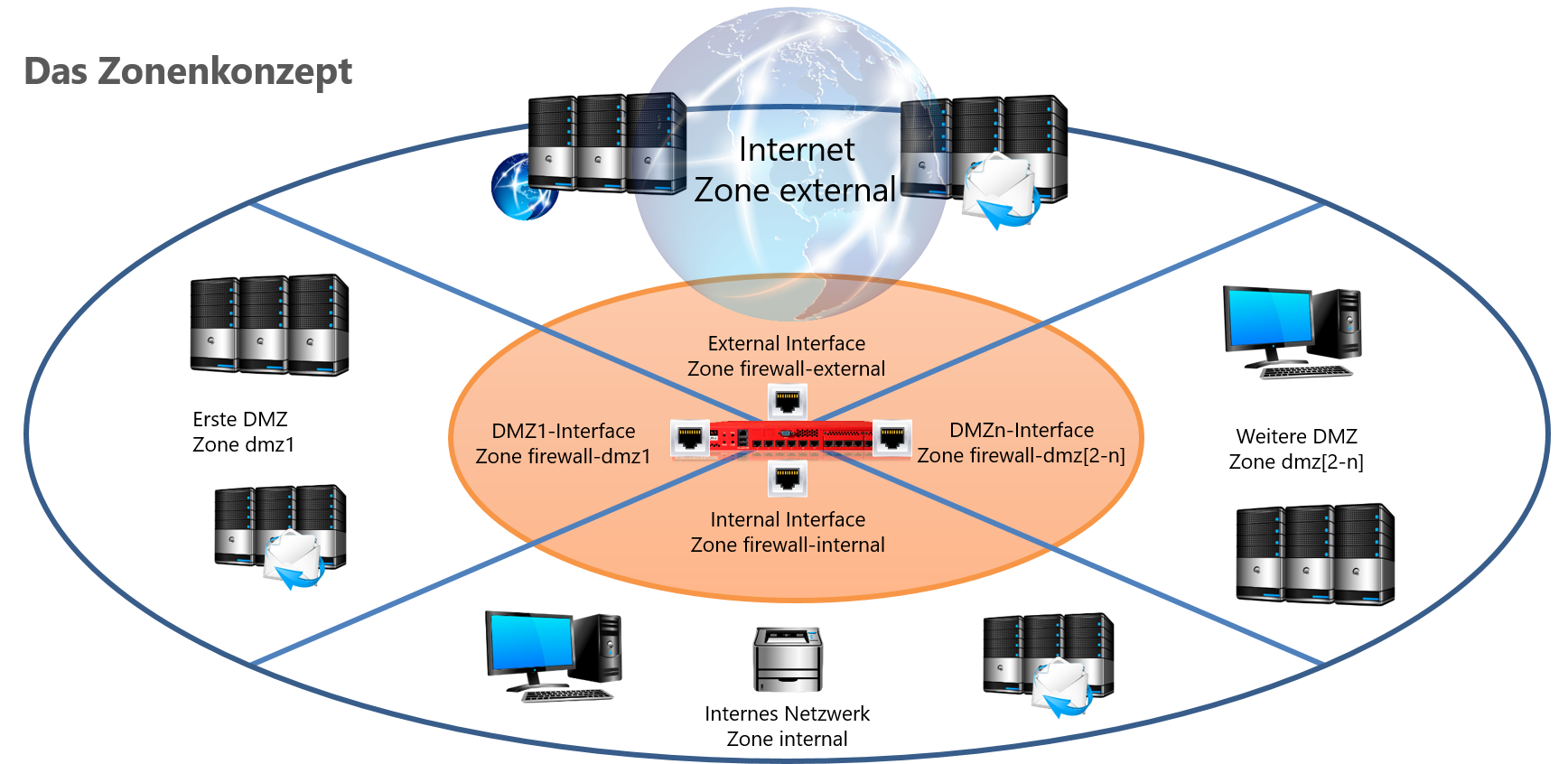
We distinguish between network, interface and VPN zones:
- Network zones distinguish the network segments, each of which is located behind an interface of the firewall.
- Interface zones distinguish the interfaces via which the different network zones are connected.
- VPN zones distinguish different networks that are connected via VPN connections.
The type of a zone is controlled by flags, which are defined when the zone is created.
The distinction for the user is simplified by naming conventions (interfaces: prefix "firewall-", VPN: prefix "vpn-").
By linking an object in the rule set to the interface via the zone, it is possible to ensure that a port filter rule only takes effect if not only the source, destination and service match the rule, but the connection is also made via the correct interfaces.
This prevents all attacks that involve IP spoofing. The assignment of an object to an interface is done by binding the zone to the interface on the one hand and the assignment of the network object to a zone on the other hand.
Examples:
Internal Network: internal
Internal Interface: firewall-internal
External Interface: firewall-external
Internet: external
Mailserver: internal
Webserver in the 1st DMZ: DMZ1
Remote IPSec subnet: vpn-ipsec
'Why is it necessary to distinguish between these different zones?"
Here is an example of a port filter rule:
If, for example, "www.ttt-point.de" is now entered into the browser, name resolution takes place before this connection is established.
Is the firewall DNS server is on the network, the workstation sends the DNS request to the firewall's internal interface.
This request must be allowed with a port filter rule:
Flags
IPv6
For new installations, IPv6 zones are no longer added. Existing zones also remain when upgrading firmware or importing a configuration.
Netzwerkwerkzeuge
Warnung: Der Anzeigetitel „Network tools“ überschreibt den früheren Anzeigetitel „Zone settings“.
Last adaptation to the version: 14.1.1
- Open and close now via the toolbar (bottom left)
- New function: Similarity detection
Introduction

To check the network connections, various functions are provided on the web interface of the UTM via the toolbar under Network tools.
To close the dialog, either click again or use the button as an alternative.
With a screen width of more than 1580 pixels, the dialog can also be displayed on the right-hand side of the screen.
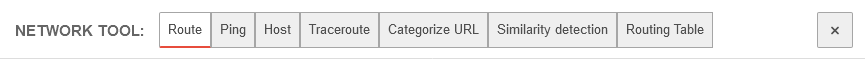
Route | |||
By pressing the button, the main routing table of the UTM is displayed. By default, the main routing table for IPv4 is displayed. |
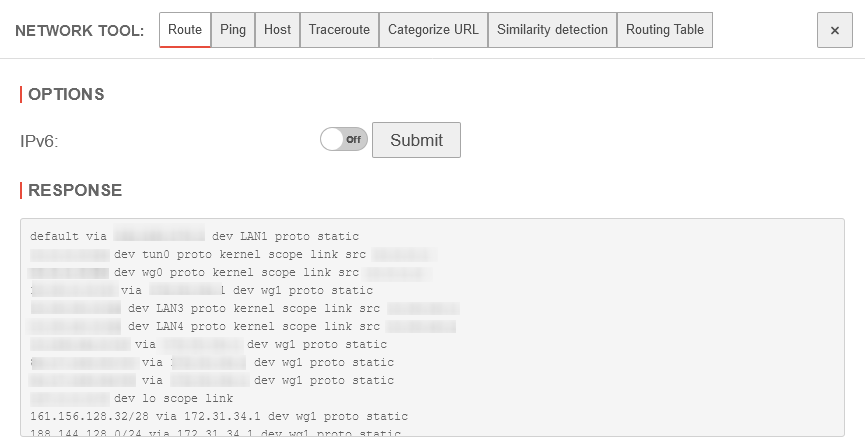 | ||
Ping | |||
| The Ping can be used to check whether a certain host can be reached in an internal or external network. No port filter rule is needed for this on the UTM from this point, but it is needed if pinging is to be done from a network device.
notempty
Not every destination allows icmp-echo-request! Ping for IPv4 |
 | ||
| Options | |||
| IPv6 | Off | Remains deactivated during an IPv4 ping | |
| Source | 192.168.175.1 | Selection of the IPv4 address to ping with | |
| Destination | k.root-servers.net | Destination name or IP address | |
| Starts the ping test | |||
| Response | The root server k.dns-zone.net of the Ripe NCC | ||
Ping for IPv6 | |||
| Options | |||
| Caption | Value | Description |  |
|---|---|---|---|
| IPv6 | On | Enable for IPv6 to be used at all |  |
| Source: | 2001:db08:aaaa:bbb00::1 | Selection of the IPv6 address to be pinged with | |
| Destination: | k.root-servers.net | Destination name or IP address | |
| Start Ping-Test | |||
| Response | The root server k.root-servers.net of the Ripe NCC should respond as shown in the picture | ||
Host | |||
| Options | |||
| Query type: | All listed types are queried | 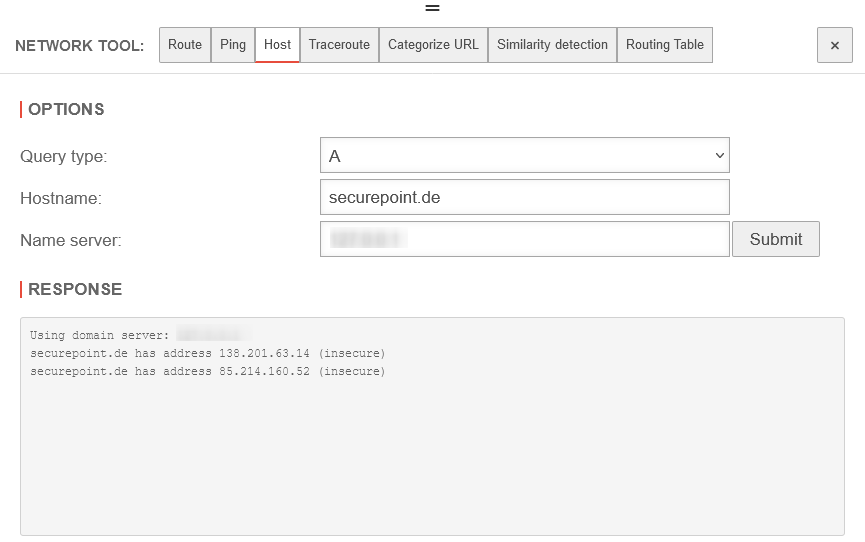 | |
| The A-record specifies the IPv4 address for the specified host | |||
| The AAAA-record specifies the IPv4 address for the specified host | |||
| Unlike forward DNS resolution (A and AAAA records), the PTR record is used to find domain names based on an IP address | |||
| The MX record specifies a mail exchange server for a DNS. The information is used by the Simple Mail Transfer Protocol (SMTP) to forward e-mails to the correct hosts. | |||
| The TXT record can contain any unformatted text strings. This is used by the Sender Policy Framcework (SPF) to prevent forged emails from being sent. | |||
| The SOA record specifies core information about a DNS zone, including the primary name server, the domain administrator's email, the domain serial number and several timers related to updating the zone | |||
| The NS record specifies an authoritative name server for a particular host | |||
| Hostname: | securepoint.de | Host that is to be requested | |
| Nameserver: | 127.0.0.1 | Name server to be used. Here it is the UTM itself. | |
| Response |
Using domain server: Name: 127.0.0.1 Address: 127.0.0.1#53 Aliases: securepoint.de has address 51.89.43.189 | ||
Traceroute | |||
| Options | |||
| With this tool, the hops of a connection to the host can be made visible.
If, for example, a destination is not reachable, the last reachable IP address on the way could be determined. |
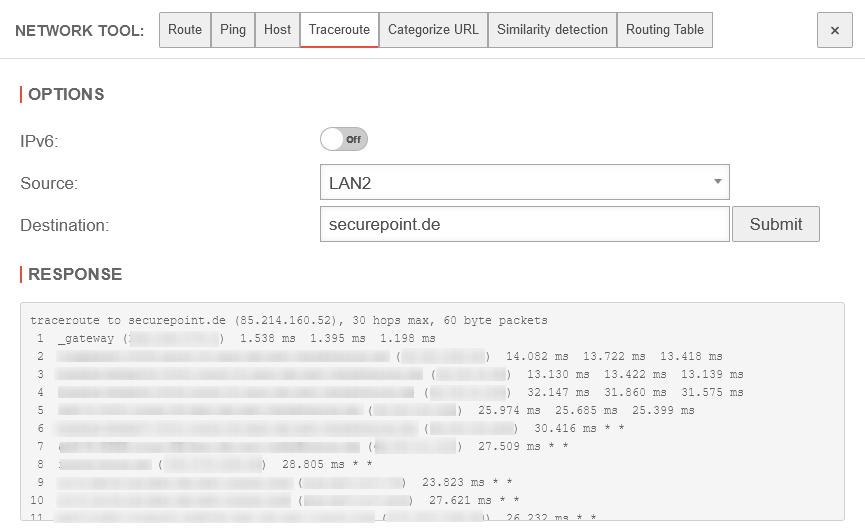 | ||
| IPv6: | Off | Set whether to use IPv6 | |
| Source: notempty New as of v14.0.0 |
LAN1 | Source from which the traceroute originates | |
| Destination: | k.root-servers.net | Specification of the destination to be tracked with Traceroute | |
| Response | Result of the Traceroute function | ||
Categorize URL | |||
| The URL filter categorises web pages and filters according to the specifications (content filter). Here you can check how certain pages are categorised. |
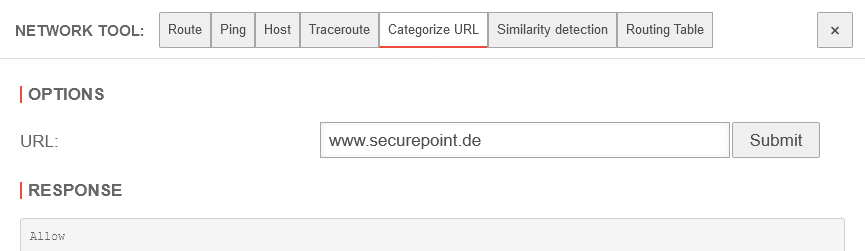 | ||
| Options | |||
| URL: | securepoint.de | Website whose categorisation is to be queried | |
| Response | Allow | Categorisation by the content filter of the UTM | |
Ähnlichkeitserkennung | |||
notempty New as of v14.1.1 Experimentell | |||
| Domains | »securepoint.de »google.de »hansestadt-lueneburg.de »goooogle.de »lueneburger-heide.de | Man kann mehrere Domains zugleich überprüfen lassen. Das Ergebnis hier: Nicht vertrauenswürdig: Vertrauensswürdige Domains: |
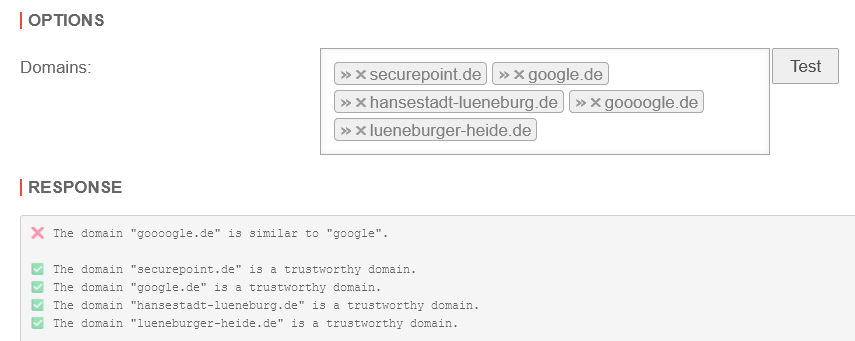 |
| Startet die Ähnlichkeitserkennung für Domain-Namen | |||
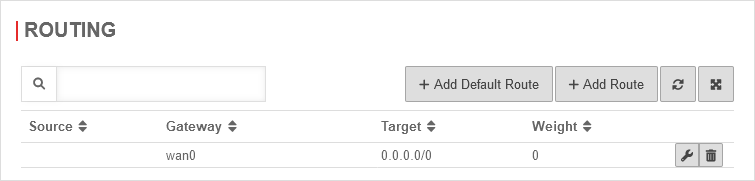
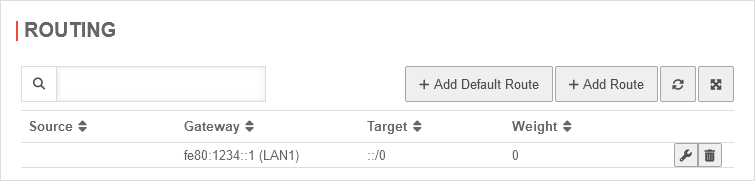
Routing table | |||
| Displays all routes stored on the UTM New since v12.2.2 | 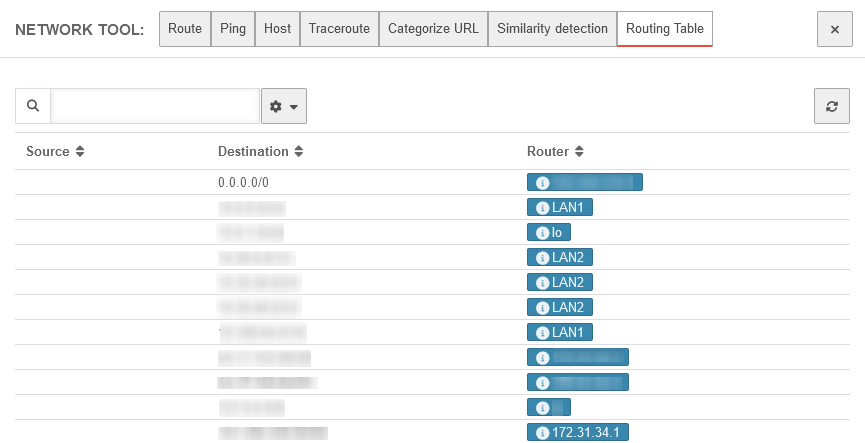 | ||
Paketfilter
Warnung: Der Anzeigetitel „Packetfilter“ überschreibt den früheren Anzeigetitel „Network tools“.
Last adaptation to the version: 14.1.0
- QoS configuration moved from Extras section to Generalunder button
- Log button for packet filter groups
- Cloud-managed Packet filter rules and Network objects
- Autogenerated rules can be edited
- Tabellen-Menü zur Layoutanpassung
- New attribute Log Alias (v14.0)
- Buttons for log access (v14.0)
- 04.2026
- Hinweis zum Verschieben von Regeln/Regelgrupppen eingefügt
The function and arrangement in the menu has remained identical.
For test purposes, iptables can be replaced by nftables.
system rule_engine set value "nftables"
or
system rule_engine set value "iptables"
Packet filter Description
UTMuser@firewall.name.fqdnFirewall 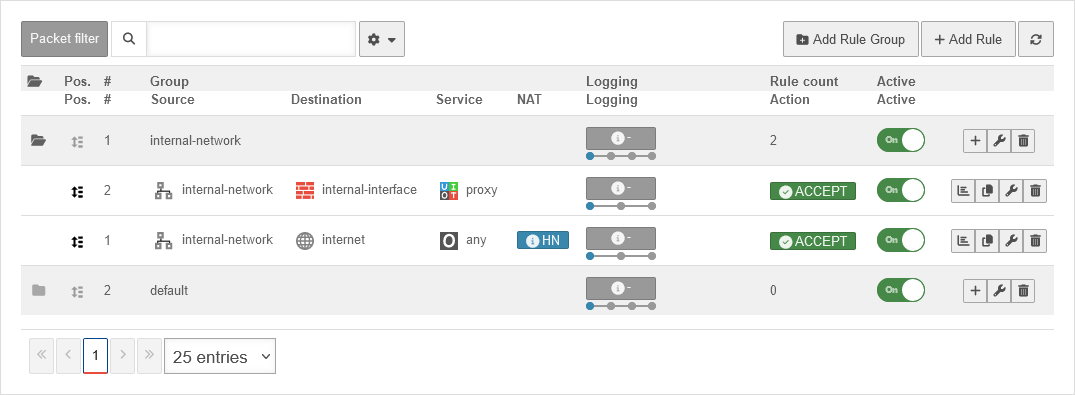 Menu Package Filter
The packet filter controls the data traffic that passes through the UTM.
Menu Package Filter
The packet filter controls the data traffic that passes through the UTM.
- All network packets that pass through the UTM are filtered and only forwarded based on packet filter rules.
- Thereby, it is irrelevant whether the destination address and source address of the packet are in the same network, in another, local network or in the Internet and a local network.
- Based on the source IP, destination IP and service used, the rules are checked from top to bottom.
The sequential number before a rule # indicates the order of rulecreation and is permanently retained. It does not indicate the order in which the rule is processed!
- If an exception is to be created for a rule, the (more specific) exception must first be defined and only then the more general rule.
If the exception rule applies to a package, the specified action is carried out and the packet filter is terminated.
If the exception rule does not apply, the more general rule is then checked.
If this rule then applies, the action specified there is executed.
A rule that has been created can be subsequently moved in the order by holding down the mouse button on the icon - Zum Verschieben einer einzelnen Regel sollten alle Regeln ausgeklappt sein Klick auf das oberste Ordner-Symbol →
- Zum Verschieben einer Regel-Gruppe sollten alle Regeln eingeklappt sein Klick auf das oberste Ordner-Symbol →
A packet filter rule contains several elements:
- Two Network Objects (source / destination).
- One Service
- if applicable, details of the NAT type (Network Address Translation)
- if applicable, Rule Routing
- If applicable, a QoS Profile that regulates the bandwidth made available for certain data packets.
- if applicable, a Time Profile at which the rule is to be applied
- an Action that is to be executed
- details of the Logging
- the assignment to a Rule Group
Packet filter rule
- The basic structure of a rule is :
Source → Target → Service → Action - With copy rulesrules can be copied. The Add Rule dialogue opens with a copy of the respective rule.
- Logging can be changed directly in the overview for individual rules or rule groups (see section Logging ) and notemptywith the button Packetfilter Log for the individual rules or with for all rules.New from v14.0:
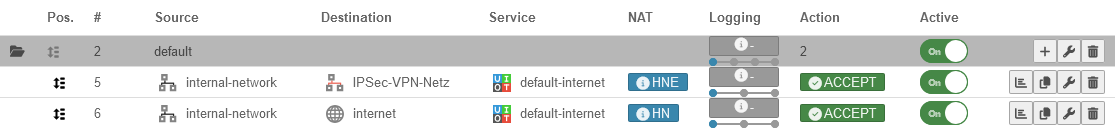
| Typical examples: | # | Source | Destination | Service | NAT | Logging | Action | Cloud | Active | ||
| The Internet should be accessible from the internal network | 7 | HN | Accept | On | |||||||
| The dmz1 network should be accessible for all services from the internal network. | 8 | Accept | On | ||||||||
| A server in the internal network is to be accessible from outside via ssh | 9 | DN ➞ | Accept | On | |||||||
| The Internet should be accessible from the internal network, but no ftp should be enabled! | 10 | Drop | On | ||||||||
| 7 | HN | Accept | On | ||||||||
| Wenn eine Regel über die VPN Konfiguration erstellt wurde, wird dies in der Spalte Cloud-verwaltet mit gezeigt. Diese Regeln können nicht kopiert, bearbeitet oder gelöscht werden. | ACCEPT | On | |||||||||
| ACCEPT | On | ||||||||||
Autogenerated rules
autogenerated
The UTM has autogenerated rules ex works.
These rules initially allow all data traffic into the existing networks and also release the proxy and DNS services of the respective interface for internal networks
Sie müssen unbedingt angepasst oder durch individualisierte Regeln ersetzt werden!
The visibility of the autogenerated rules can be controlled in the drop-down menu with this switch: On Show auto-generated rules Default
Packet filter Rule Settings
Only after that will the rules be applied!
/ →
notempty In dem Tabellen-Menü () lässt sich das Layout der Tabelle anpassen. Mehr Informationen sind hier zu finden.
New as of v14.0 | |||
GeneralGeneral
| |||
| Caption | Value | Description | UTMuser@firewall.name.fqdnFirewallPacket filter 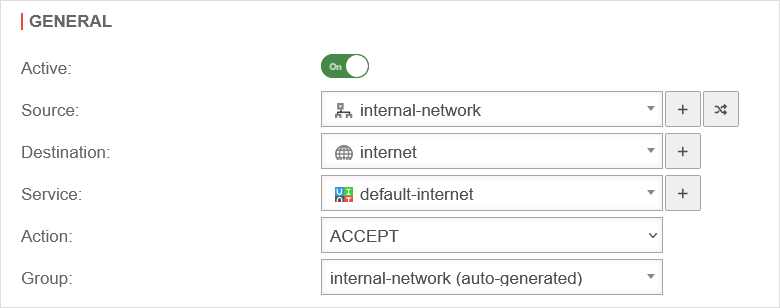 Packet filter rule settings General Packet filter rule settings General
|
|---|---|---|---|
| Active: | On | Only when activated is this rule checked | |
| Source: | Network object or user group that is permitted as the source of the data package. | ||
| Destination: | Network object or user group that is permitted as the destination of the data packet. | ||
| Service: | Desired service with stored port (see tab Services) | ||
| Netzwerkobjekt add / Dienst add | Adds a network object or service | ||
| Switch network object | Exchanges the network objects Source and Destination | ||
Action:Action |
ACCEPT Forwards the package | ||
| DROP The package is dropped | |||
| REJECT An ICMP packet is sent to the sender indicating that the port is not available. In the LAN, reject rules can prevent clients from having to wait for a timeout. | |||
| QOS Allows you to specify a Quality of Service profile that limits the bandwidth for data packets to which this rule applies. Configuration of the QoS profiles in the Area Profile menu. | |||
| STATELESS Allows connections regardless of status | |||
|
Allows you to specify a Quality of Service profile that limits the bandwidth for data packets to which this rule applies. Configuration of the QoS profiles in the Area Profile menu. | ||
| Group: | default | Packet filter rules must be assigned to a group. This makes it easier to keep track when adding to the set of rules. In addition, rule groups can be activated or deactivated with a switch notempty and the logging settings of all rules contained can be adjusted centrally via a button.
New as of v12.7.0 | |
LogLog
| |||
Logging:Logging |
Specifies how extensively the application of the rule is logged. notempty This setting is also available in the packet filter overview for individual filters as well as complete groups.
New as of v12.7.0 |
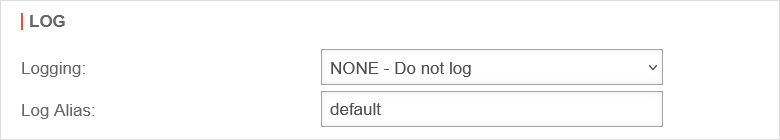 | |
| No logging (default) | |||
| Logs the first three entries per minute | |||
| Logs all entries | |||
Log Alias:Log Aliasnotempty New as of v14.0 |
default | Kurzer (maximal 10 Zeichen langer) Alias für die Paketfilterregel, der im Log statt der Id angezeigt wird. | |
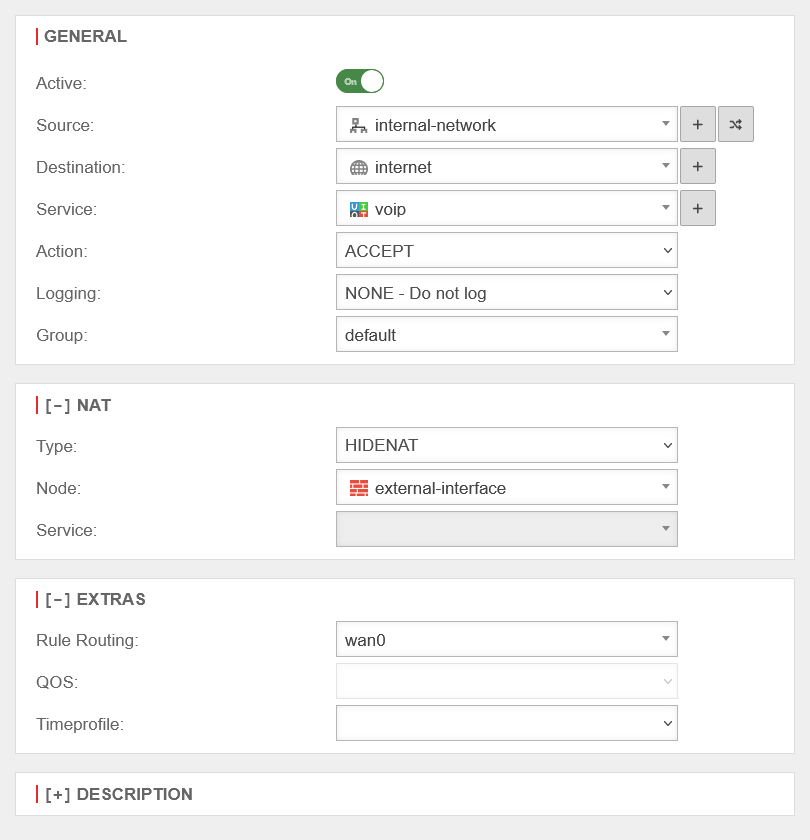
NAT[ - ] NAT
|
Network Address Translation is the conversion of IP addresses used in a network to another IP address from another network. Typically, all internally used private IP addresses are mapped to one or more public IP addresses. | ||
| Type: | No NAT is performed | ||
| With Full Cone NAT, the same port is set for the sender as for the recipient. However, IPs other than the originally addressed IP are also permitted as senders. This can be helpful with VOIP. |  | ||
| Also called Source NAT. Hides the original IP address behind the IP address of the interface used. The standard case is data traffic from an internal network with private IP addresses to the Internet. |
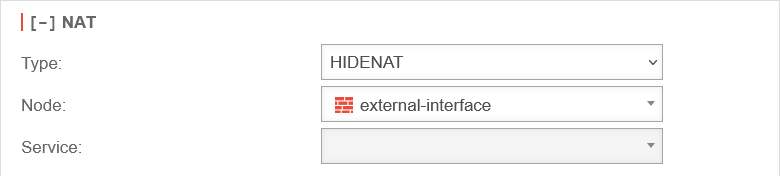 | ||
| HideNAT Exclude is usually used in connection with IPSec VPN connections. This ensures that data packets for the VPN remote terminal are routed through the VPN tunnel with the private IP address. Otherwise, these would be masked with the public WAN IP address like all other packets in the direction of the Internet and, since they are sent with a private destination address, would be discarded at the next Internet router. See also the Wiki article HideNAT Exclude. |
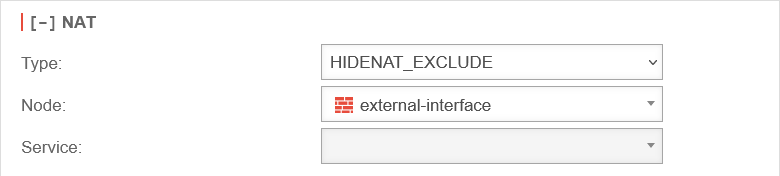  | ||
| Destination NAT is usually used to offer several services on different servers under one public IP address. For example, if you want to access the SSH service (port 22) of the server (198.51.100.1/32) from the Internet via the public IP address of the eth0 interface with port 10000, the rule would have to be created as shown opposite. The associated network objects and the service on port 10000 must be created for this. |
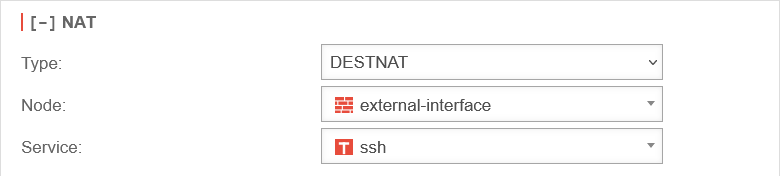 | ||
| NetMap is used to connect two identical subnets with each other. Using auxiliary networks (mapnet), which are not set up on either of the remote sites to be connected, these connections can be created collision-free without completely changing the subnet on either side. Instructions for connecting two networks can be found in a dedicated Wiki article NetMap |
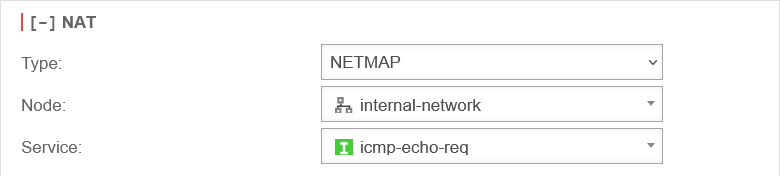 | ||
| Network object: | The IP address of this network object is then used as the sender IP of the data packets in the target network. As a rule, this should be the interface whose IP address is known to the target network so that reply packets can also be correctly delivered. | ||
| Service: | Uses the selected service in the local destination network. This value is often (but by no means always) identical with the service above it in the data source package for which the rule is checked. | ||
Extras[ - ] Extras
| |||
Rule RoutingRule Routing |
wan0 | In the [ - ] Extras section, the Rule Routing field is used to specify, based on rules, which route IP packets should take. In the example opposite, all VOIP packets are routed via the wan0 interface. If access to the Internet is via a router connected to an ethernet interface, this can be entered manually. |
 |
| Time profile | Restricts the validity of the rule to a previously defined time profile. See section Time Profiles. | ||
| Description | Show extended rule info On | Alternative text that can be displayed instead of the rule details. The alternative texts are displayed with the button |
UTMuser@firewall.name.fqdnFirewall 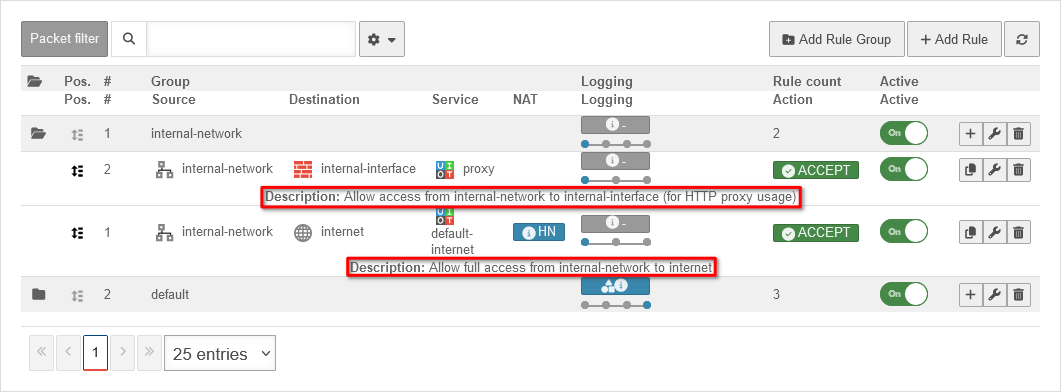 Rule description in plain text Rule description in plain text
|
notempty
After editing or adding a rule, the rulebook must be updated. Only after that will the rules be applied! / → | |||
Network objects
| button | Description | UTMuser@firewall.name.fqdnFirewall 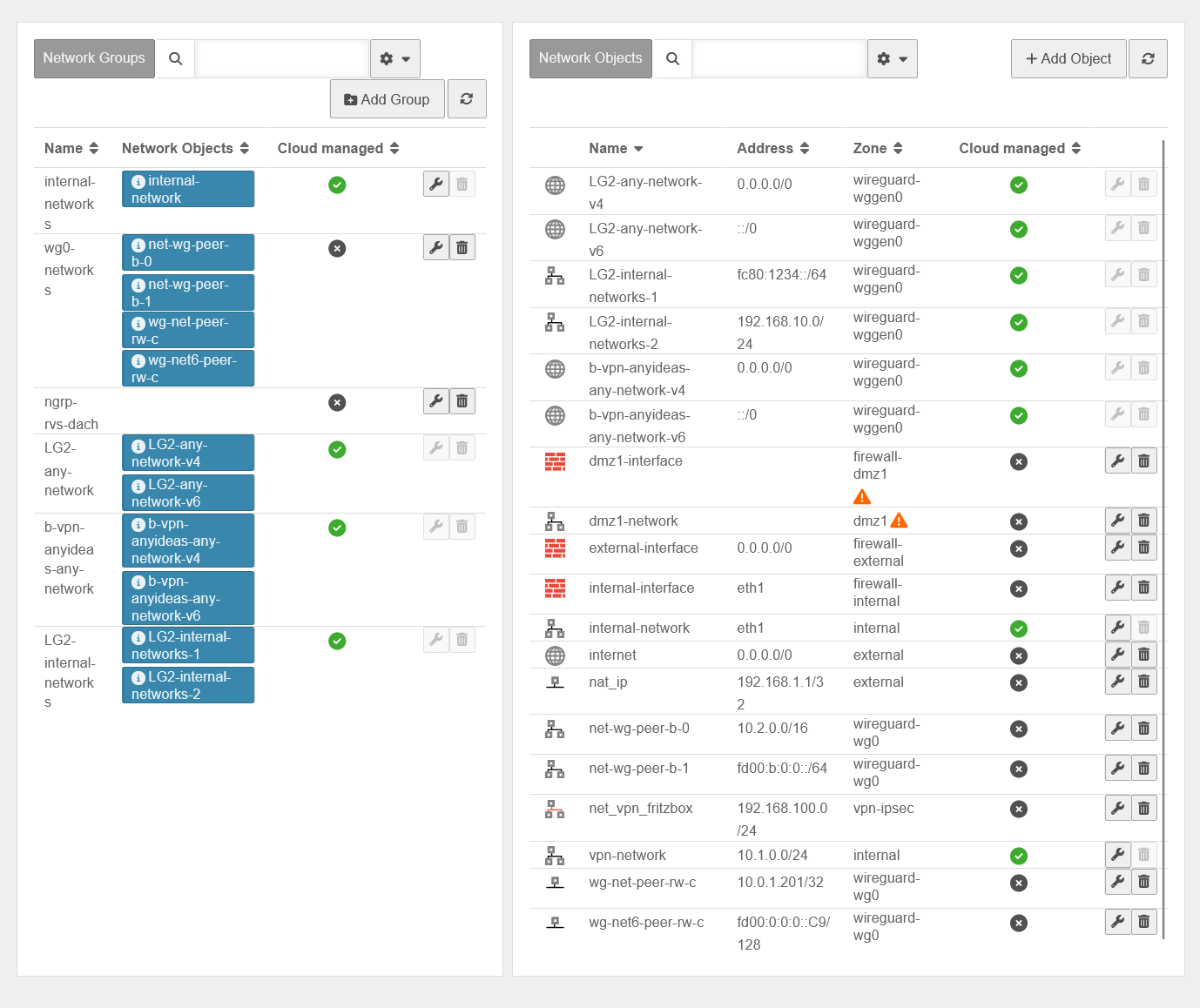 Tab Network Objects Tab Network Objects
|
|---|---|---|
| Edit | Opens the network group or network object for editing | |
| Delete | Deletes the network group or network object. The deletion must be confirmed once again | |
| Creates a new network group to which network objects can be added immediately | ||
| Show GeoIP objects On When disabled Off: Hides GeoIP objects to improve readability. | ||
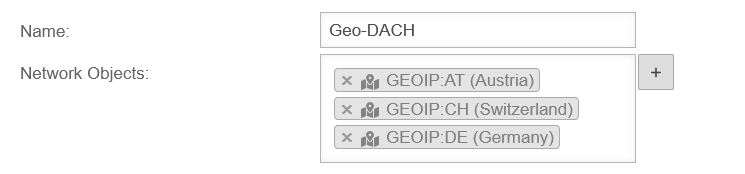
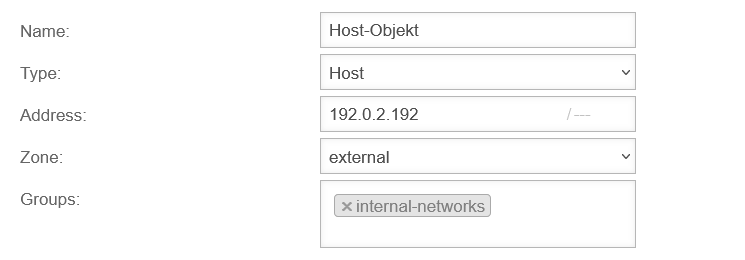
Network objects contain :
Network objects are mainly needed to create packet filter rules, but they are also used in the HTTP proxy. The members of a network group are displayed as labels. notempty If there are network objects that were created via the USC, the Cloud-managed column shows whether these are such objects or locally created objects . Cloud-managed objects must be edited in the Cloud under .
v14.0 | ||
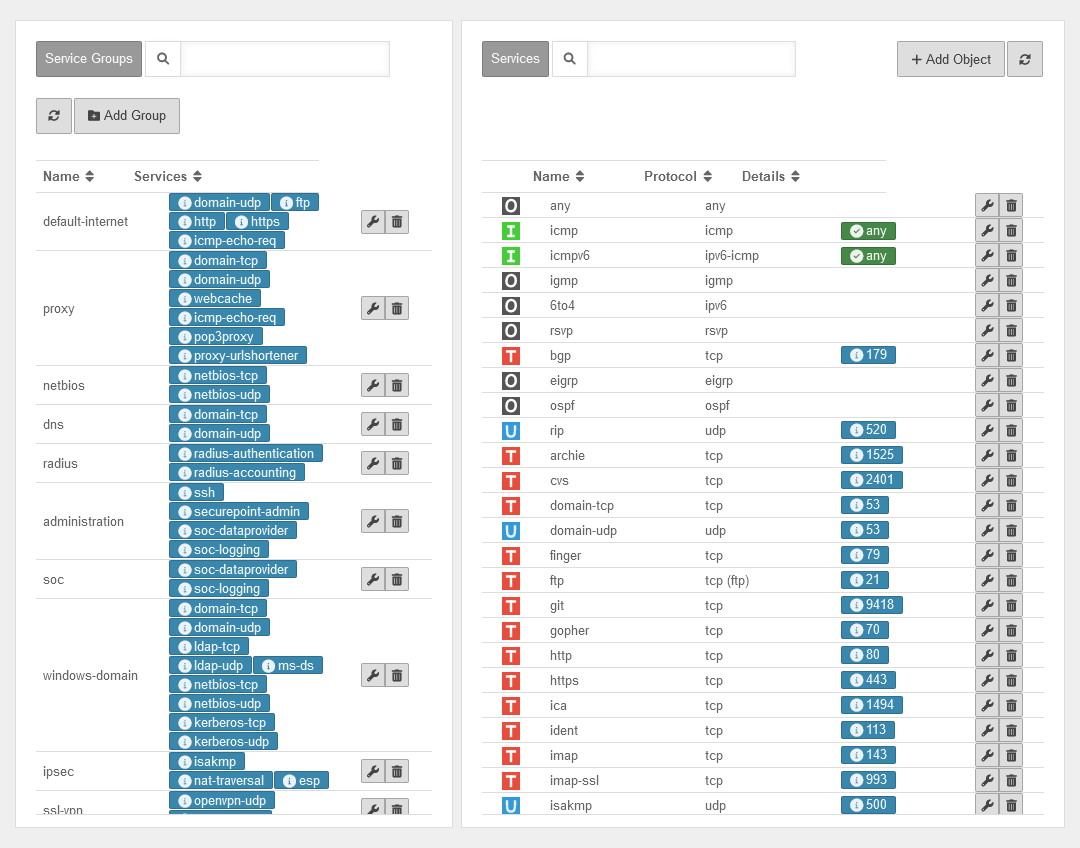
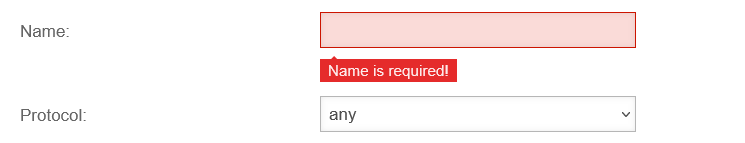
Services
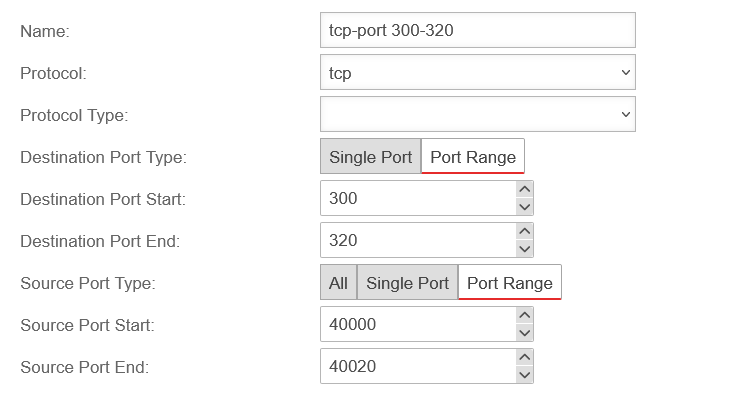
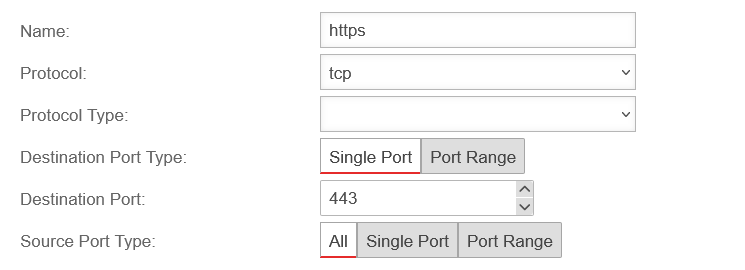
Add / edit services
If a service does not exist, it can be created with .
Depending on the protocol used, further settings can be made:
- Ports (TCP and UDP)
- Packet types (ICMP)
- Protocol type (gre)
Service groups
Services can be grouped together in service groups. Here, too, there are already predefined groups that can be added to and changed. Detailed display by clicking on the button .
Example: The group default-internet contains, for example, the services:
| Icon | Name | Protocol | UTMuser@firewall.name.fqdnFirewallServices 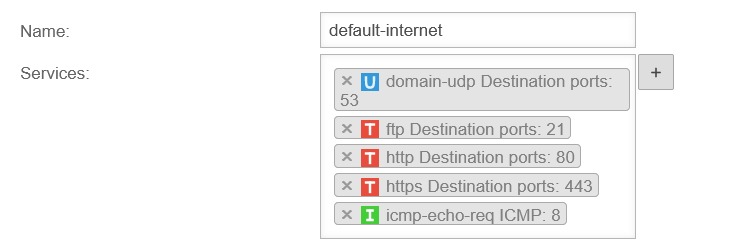
| |
|---|---|---|---|---|
| domain-udp | udp | Port 53 | ||
| ftp | tcp (ftp) | Port 21 | ||
| http | tcp | Port 80 | ||
| https | tcp | Port 443 | ||
| icmp-echo-req | icmp | Pakettyp 8 | ||
Add/remove service from a service group
- Clicking in the click box selects the desired service and thereby adds it.
- Clicking the button creates a new service and then adds it to the service group.
- A service is removed from the service group by clicking on ✕.
Time profiles
UTMuser@firewall.name.fqdnFirewall 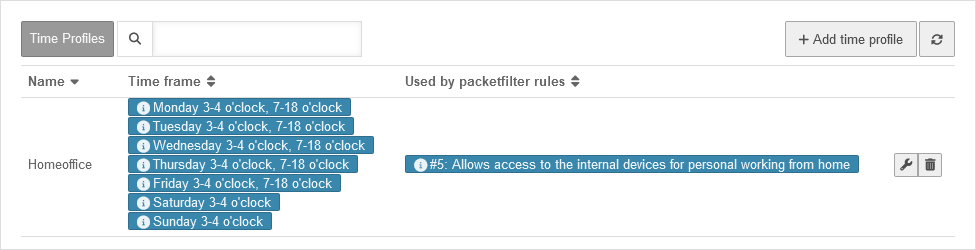 Time profiles overview
Time profiles are used to activate packet filter rules only at specified times. They can be configured under
Time profiles overview
Time profiles are used to activate packet filter rules only at specified times. They can be configured under
In the example shown, the profile applies daily between 3:00 am and 3:59:59 am and on weekdays from 7:00 am to 5:59:59 pm. This can be seen in the table under time window.
Under Used in packet filter rules, the IDs are listed together with the descriptions of the packet filters for which this time profile is set up. The packet filter can also be edited by clicking on the corresponding entry.
The Name column shows an assigned name that should describe the time profile.
Create time profiles
UTMuser@firewall.name.fqdnFirewallTime profiles 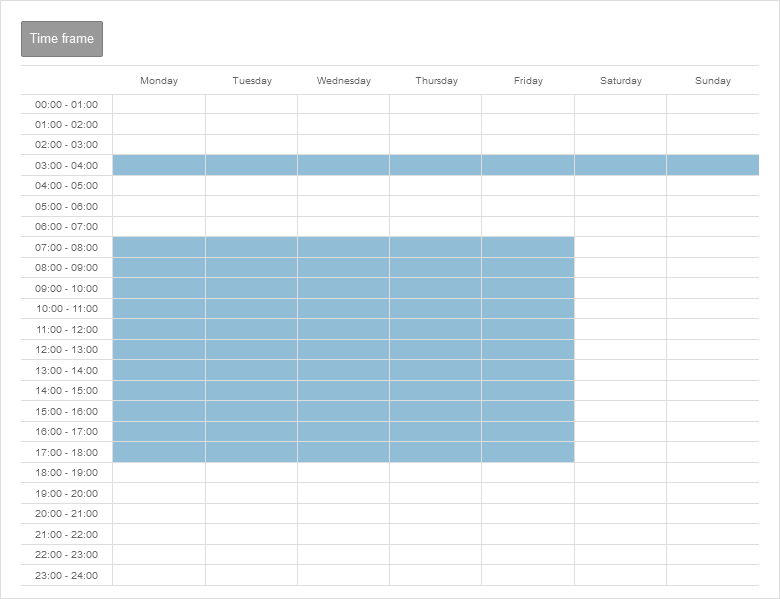 Add time profile
Add time profile
- Create a time profile under button .
- Select times
- Individual fields or time ranges can be selected by clicking the mouse
- Several fields and time ranges can be selected by holding down the mouse button
- Accept the time settings with the button Save and close
Use time profiles
Time profiles can be selected under the Extras section when creating or editing packet filter rules.
Implizite Regeln
Warnung: Der Anzeigetitel „Implied rules“ überschreibt den früheren Anzeigetitel „Packetfilter“.
Last adaptation to the version: 14.0.8.2
- Einstellungen für GeoIP Sperrungen verschoben zu IDS/IPS
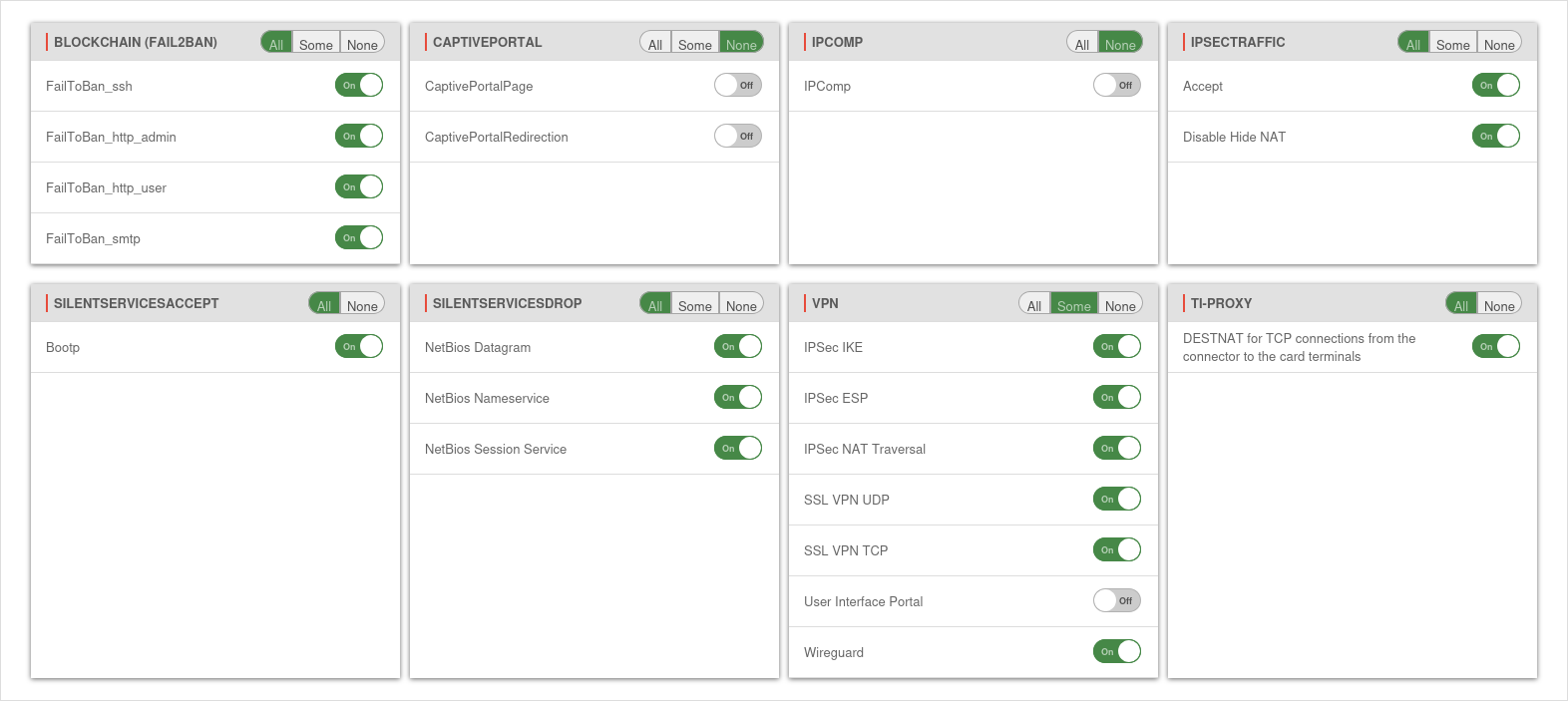
Implied rules
Settings in menu .
Implied rules have been added for certain use cases. These rules can be easily activated or deactivated by the user as needed. Some of these rules are already active by default.
| Group / Rule | Description | Protocol | Port | Active (Default) |
|---|---|---|---|---|
| BlockChain | Activates / deactivates the entire group | |||
| FailToBan_ssh | Access via ssh.Monitoring with Fail2Ban rules. Configuration at |
TCP | 22 | On |
| FailToBan_http_admin | Access via the Admin Interface. Monitoring with Fail2Ban rules. Configuration at Port changes possible at |
TCP | 11115* | On |
| FailToBan_http_user | Access via the User interface. Monitoring with Fail2Ban rules. Configuration at Port changes possible at |
TCP | 443* | On |
| FailToBan_smtp | Access via the Mailgateway. Monitoring with Fail2Ban rules. Configuration at Port changes possible at Area Smarthost |
TCP | 25* | On |
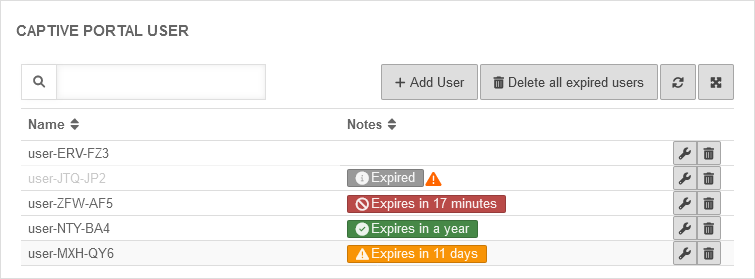
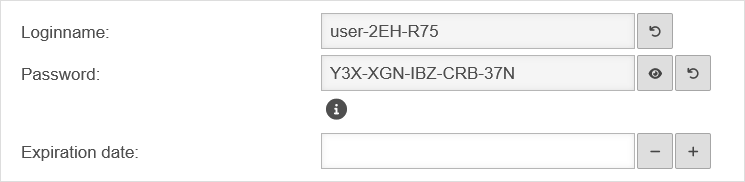
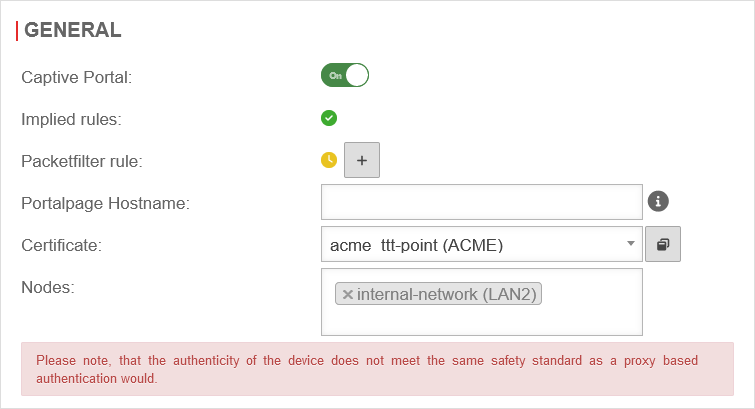
| CaptivePortal | Enable redirection of traffic to a landingpage | |||
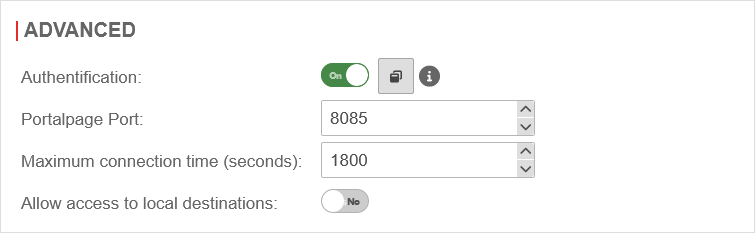
| CaptivePortalPage | Opens an incoming port on the corresponding interface of the firewall that is intended for the captive portal to display the landingpage. Port changes possible at Area Advanced |
TCP | 8085* | Off |
| CaptivePortalRedirection | Redirection of traffic to the above mentioned port. | Off | ||
| IPComp | ||||
| IPComp | Accepts connections with IPComp protocol (compression of data packets, IP protocol number 108) | IPComp | Off | |
| IpsecTraffic | Activates / deactivates the entire group | |||
| Accept | Accepts incoming and outgoing traffic of an IPSec connection. | On | ||
| No NAT for IPSec connections | Takes all IPSec connections from the NAT |
Off | ||
| Silent Services Accept | ||||
| Bootp | Accepts
|
UDP | 67 | On |
| 68 | ||||
| Silent Services Drop | ||||
| NetBios Datagram | Discards these packages without log message | UDP | 138 | On |
| NetBios Nameservice | Discards these packages without log message | UDP | 137 | On |
| NetBios Session Service | Discards these packages without log message | UDP | 139 | On |
| VPN | ||||
| IPSec IKE | Accepts connections on port 500/UDP | UDP | 500 | On |
| IPSec ESP | Accepts connections with the ESP protocol (50) | ESP | On | |
| IPSec NAT Traversal | Accepts connections on port 4500/UDP | UDP | 4500 | On |
| SSL VPN UDP | Accepts connections on ports for which an SSL VPN instance has been configured with the UDP protocol | UDP | 1194 | On |
| SSL VPN TCP | Accepts connections on ports for which an SSL VPN instance has been configured with the TCP protocol | TCP | 1194 | On |
| User Interface Portal | Accepts connections on port 443/TCP. Required for the user interface. | TCP | 443 | On |
| Wireguard | Enables connections with the Wireguard protocol. Port changes possible at button edit connection |
UDP | 51280* | On |
| TI-Proxy notempty New as of v14.0.7.2 |
||||
| DESTNAT for TCP connections from the connector to the card terminals | Erstellt und erlaubt eine Portweiterleitung von den IP-Adressen und Ports wie im TI-Proxy hinterlegt vom Konnektor per destnat zu den Kartenterminals (default: 60000→4742) | TCP | 60000 | On |
HTTP Proxy
Warnung: Der Anzeigetitel „HTTP Proxy“ überschreibt den früheren Anzeigetitel „Implied rules“.
Last adaptation to the version: 14.1.2
- Added note on current certificate requirements
- Renamed the Website-Allowlist and updated the description
- Creating additional configuration profiles is possible(14.1.1)
- FastDiff updates virus patterns in real time(14.1.0)
- SigQA submits new but unknown signatures to our AV-lab(14.1.0)
- 04.2026
- Corrected an error in the description of the sender's address
Introduction
The proxy serves as an intermediary between the internet and the network to be protected.
The clients send their request to the proxy and the proxy passes it on to the corresponding servers.
The actual address of the client remains hidden from the server.
In this way, it is possible to check the data traffic for viruses and unwanted content.
```markdown
- Support for certificates with a key length of 1024 bits or less will be removed starting with UTM version 14.2.
- Support for certificates with the SHA1 signing algorithm will also be removed starting with version 14.2.
- HTTP proxy or SSL VPN connections with such outdated certificates will no longer work as of v14.2!
- Insecure certificates should be replaced urgently!
The BSI recommends—as of January 2025—key lengths of 3000 bits or more and SHA256
BSI – Technical Guideline – Cryptographic Methods: Recommendations and Key Lengths BSI TR-02102-1 | Chapter 2.3: RSA encryptionThe default setting of the UTM for new certificates is RSA encryption with 3072 bits and SHA256 as the hash algorithm
- Affected applications:
- OpenVPN
- Server certificate when acting as a server (Roadwarrior or S2S)
- Client certificate for S2S
- If applicable, certificate specified as client certificate via user attribute (Authentication → Users → Edit User)
- Mailrelay
- Relaying "Certificate" (under TLS encryption as server)
- Reverse-Proxy
- Settings → SSL Certificate
- Webserver
- Network → Server Settings → Webserver → Certificate
- HTTP-Proxy
- SSL Interception → CA Certificate
- OpenVPN
Global Profile
General
| Caption | Value | Description | UTMuser@firewall.name.fqdnApplicationsHTTP-Proxy 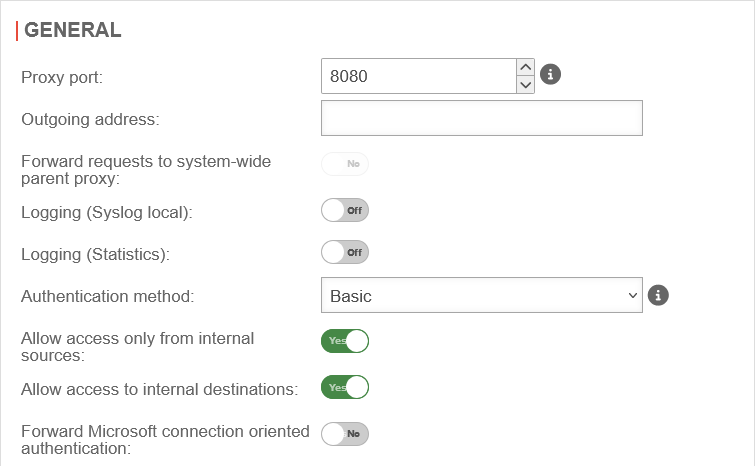 Area General Area General
|
|---|---|---|---|
| Proxy Port: | 8080▴▾ | Specifies on which port the proxy is to be addressed | |
| Outgoing Address: | The IP address of the interface that the HTTP proxy should use. The Outgoing Address is used for two scenarios:
In this example, the proxy is bound to the faster DSL line:
Connection to a web server in the VPN network:
| ||
| Forward requests to system-wide parent proxy: | No | If another proxy is used before the HTTP proxy, this function must be activated. The configuration takes place under | |
| Logging (Syslog lokal): | Off | Writes a general Syslog for the HTTP proxy (Open: Area Log | |
| Logging (Statistics): Only available if no anonymization for the HTTP proxy Settings at |
On | Writes a statistical Log call: Area HTTP proxy statistics | |
| Authentication method: | The proxy offers various possibilities for authentication. The possibilities are: | ||
| None | The HTTP proxy processes all requests without authentication | ||
| Basic | With basic authentication, the users are queried against the stored users under Area User on the firewall | ||
| NTLM / Kerberos | Here the firewall must be made known to the server. This can be set up in the web interface under | ||
| Radius | Here the firewall must be made known to the server. This can be set up in the web interface under | ||
| Allow access only from local sources: | Yes default |
Access to the HTTP proxy is now only possible from internal sources. These are:
| |
| Allow access to local destinations: | Yes default |
All internal networks can also be reached via the HTTP proxy (the packetfilter has already been passed through to reach the HTTP proxy). Disabling it prevents this and access to other internal networks must be explicitly allowed via the port filter without an HTTP proxy. | |
| Forward Microsoft connection-oriented authentication: | No | If it is enabled, login or authentication to websites is possible. For some websites this is not possible otherwise. With this option, NTLM, Negotiate and Kerberos authentications are forwarded notempty
If SSL-Interception is active, this parameter must be enabled for HTTPS-based authentications, otherwise no authentication/login is possible on these websites. | |
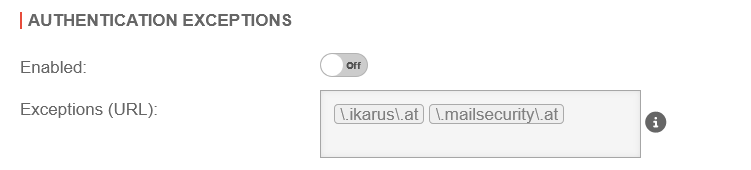
Authentication exceptions | |||
| Enabled | Off default |
Authentication exceptions are disabled by default.
If enabled: URLs listed here are accessed without prior authentication. |
 |
| Exception (URL): | \.ttt-point\.de | If authentication exceptions are enabled, custom exceptions can be defined here | |
Virusscan | |||
General | |||
|
Der Virenscanner im HTTP-Proxy kann Datenverkehr auf Viren prüfen. notempty Dabei werden mit FastDiff die Viruspattern in Echtzeit aktualisiert. New as of v14.1.0 Die Funktion lässt sich per CLI deaktivieren oder aktivieren. Per Default ist die Funktion aktiviert. FastDiff Deaktivieren: extc value set { application ikarus variable ENABLE_FASTDIFF value 0 } FastDiff Aktivieren: extc value set { application ikarus variable ENABLE_FASTDIFF value 1 } FastDiff Status abfragen:extc value get { application ikarus variable ENABLE_FASTDIFF } application|variable |value -----------+---------------+----- ikarus |ENABLE_FASTDIFF|1 notempty Zusätzlich werden mit der Funktion SigQA neue aber unbekannte Signaturen an unser AV-Labor übermittelt. New as of v14.1.0 Die Funktion lässt sich per CLI deaktivieren oder aktivieren. Per Default ist die Funktion aktiviert. SigQA Deaktivieren: extc value set { application ikarus variable ENABLE_SIGQA value 0 } SigQA Aktivieren: extc value set { application ikarus variable ENABLE_SIGQA value 1 } SigQA Status abfragen:extc value get { application ikarus variable ENABLE_SIGQA } application|variable |value -----------+------------+----- ikarus |ENABLE_SIGQA|1 | |||
| Virusscan: | On | The virus scanner is activated and the associated service is running (default setting) |
Datei:UTM v14.1.1 Anwendungen HTTP Proxy Virenscanner-en.png |
| On | The virus scanner service is deactivated. The HTTP proxy is not working correctly. The service can be started via the menu Virusscan | ||
| On | The virus scanner service is deactivated. The HTTP proxy is not working correctly. notempty On devices with less than 3GB RAM, the service for the virus scanner cannot start. Please change to current hardware or allocate more RAM! | ||
| Off | The virus scanner is deactivated. | ||
| Maximum scan size limit: | 2▴▾ Megabytes | Sets the size of the files to be scanned by the virus scanner | |
| Trickle Time: | 5▴▾ seconds | Interval at which data is transferred from the proxy to the browser so that the browser does not stop loading during the virus check | |
| Allowlist ICY-Protokoll: | Off | A web radio protocol that can be excluded from testing | |
| Cache Updates notempty New as of v12.7.2 |
Off | When activated On, the virus database updates are distributed to the connected clients with Securepoint Antivirus Pro after the initial download. In this way, traffic is reduced and the updates are rolled out smoothly. | |
| Mime type blocklist | application/x-shockwave-flash Example |
Mime types listed here are blocked in any case. The button opens a dialogue in which a mime type can be selected from a dop-down menu or an individual type can be entered. The MIME-Type detection is performed after the first few bytes of the file. Normally, this detection is accurate, and the blocklist is applied accordingly. Additionally, there is a rescan mechanism in place, which re-evaluates the MIME-Type specifically for Microsoft-Compound Storage Formate files. This rescan occurs once the full file is available or when the loaded portion of the file reaches the Virusscanner sizelimit.
| |
Allowlist | |||
| Enabled | On | The allowlist for MIME types and websites is enabled by default | |
| Mime-Type Allowlist | application/pkcs10 Example |
Mime types listed here are not scanned. Standard defaults:
| |
|
Exceptions
»^[^:]*://download\.windowsupdate\.com/ |
Here it is possible to create your own filters based on Regular Expressions (Regex). notempty Viruses from these pages are not detected! Some update servers that cause problems when using a virus scanner are already preconfigured. Hint: Further exceptions are necessary so that iTunes can communicate correctly with the internet. | ||
Bandwidth | |||
| Bandwidth limiting policy: | None | Default |  |
| Limit total bandwidth | In this case, the proxy only uses the specified maximum bandwidth and leaves the rest of the bandwidth untouched by your internet connection. (This bandwidth is shared by all hosts connected to the proxy.) | ||
| Per host bandwidth | Bandwidth for each host. The limited bandwidth for hosts cannot exceed the global bandwidth. | ||
| Global bandwidth: | 2.000.000▴▾ kbit/s | Default value, if activated | |
| Per host bandwidth: | 64.000▴▾ kbit/s | Default value, if activated | |
App Blocking | |||
| The general app blocking with fixed ports has been removed. Individual apps, or the ports they use, can be blocked flexibly via the packet filter. | |||
SSL-InterceptionWith the SSL interception feature, it is possible to recognise malicious code in SSL-encrypted data streams at the gateway. It interrupts the encrypted connections and makes the data packets visible to virus scanners and other filters. Data transmission to the client is then encrypted again. To do this, however, it is necessary to create a CA under and select this in the CA certificate field. | |||
| Caption | Value | Description | UTMuser@firewall.name.fqdnApplicationsHTTP-Proxy 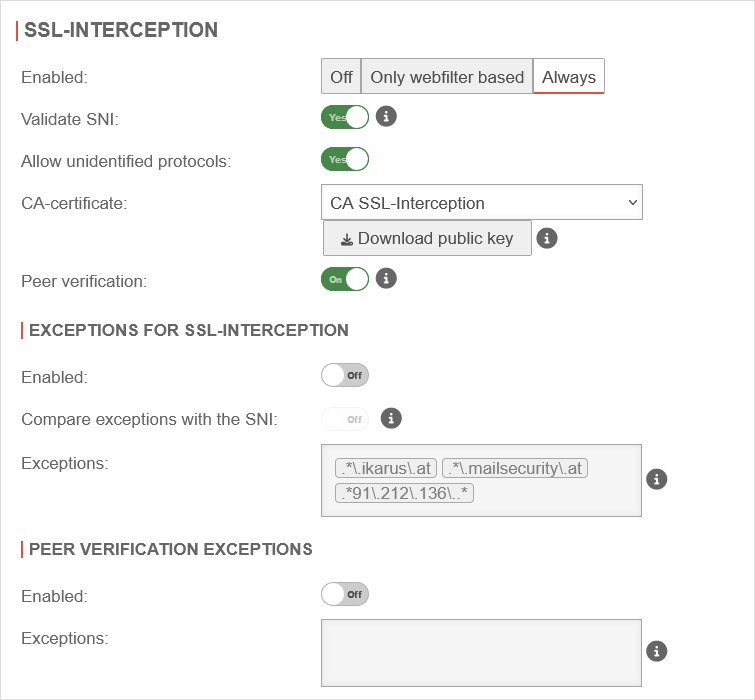 SSL Interception tab SSL Interception tab
|
| Enabled | The SSL-Interception is turned off | ||
| When enabled, only connections blocked by the web filter are intercepted. This avoids the problem that there are sites that do not tolerate an interruption of the encryption (e.g. banking software) without having to define an exception for it. | |||
| Activates the SSL interception | |||
| Validate SNI: |
Yes | When activated, any SNI in the ClientHello of the TLS handshake is checked. The host name contained is resolved and the addresses in the result are compared with the target address of the intercepted request. If they do not match, the connection is closed. Without Server Name Indication validation, clients can manipulate SNI arbitrarily to bypass the web filter. This setting should only be considered as a last resort when it seems impossible to standardize the DNS settings between the HTTP proxy and the UTM clients. If the client and UTM use different DNS servers, this can lead to false positives.
| |
| Allow non identified protocols: | Yes | If this switch is deactivated, unrecognized protocols are blocked. | |
| CA-Certificate: | CA-SSL-Interception | Here, a CA must be selected that can re-encrypt the connection after decryption (and scanning). The public key of the CA must be installed on all client computers that are to use SSL Interception. Download can be done here directly with . ```markdown
notempty
| |
| The public key should be installed on the clients that are going to use SSL interception to avoid certificate errors. | |||
| Peer verification: not for Only webfilter based |
On | This should definitely be enabled! With this, the HTTP proxy checks whether the certificate of the called page is trustworthy. Since the browser only sees the local certificate, a check by the browser is no longer possible. | |
Exceptions for SSL-Interception Exceptions for SSL-Interception not for Only webfilter based | |||
| Enabled | Off | It is possible to define exceptions in the format of Regular Expressions. However, since only https can arrive here, it is not filtered for protocols, unlike the virus scanner. New exceptions can be added directly in the input field. So an exception for www.securepoint.de would be:
.*\.securepoint\.de" | |
| Compare exceptions with the SNI: Only available if salidate SNI is active. |
Off | Applies Server Name Indication validation only to activated Exceptions of SSL-Interception . | |
| Exceptions: | .*\.ttt-point\.de Predefined in the Global Configuration Profile .*\.ikarus\.at.*\.mailsecurity\.at .*91\.212\.136\..* |
Define exceptions here for ttt-point.de | |
Peer verification exceptions Peer verification exceptions only if peer verification is active | |||
| Enabled | Off | Here exceptions for certificate verification in regex format can be added.
| |
Transparent Mode | |||
| Transparent Mode | On | Due to the transparent mode, the proxy is not visible to the clients, the client sees its internet connection (HTTP) as if no proxy was connected in front of it. Nevertheless, the entire HTTP stream goes through the proxy, which means that no settings have to be made on the client. However, there are the same possibilities to analyze / block / filter / manipulate the data stream as if a fixed proxy were used. Each network object or group of network objects that are to use the transparent proxy must be stored here. |
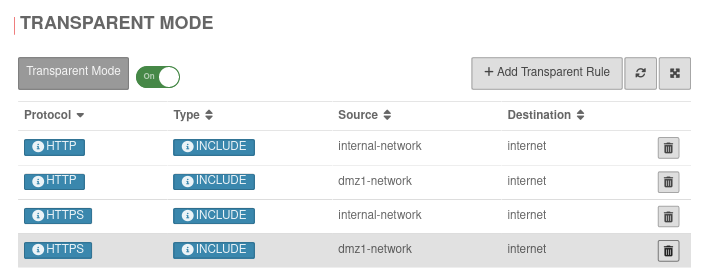 |
| Protocol: | HTTP or HTTPS |
Protocol that is used | UTMuser@firewall.name.fqdnApplicationsHTTP-ProxyGlobales Konfigurationsprofil bearbeiten 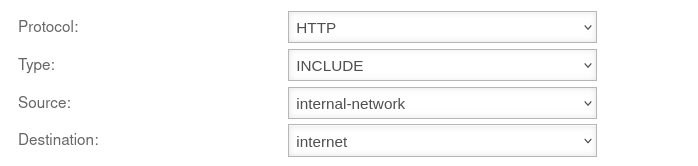 Adding a Transparent Rule Adding a Transparent Rule
|
| Type: | INCLUDE | The transparent mode is applied | |
| EXCLUDE | Transparent mode is not applied | ||
| Source: | internal-network | Source network object created under Area Network objects | |
| Destination: | internet | Destination network object | |
Add Configuration Profile
General
| Caption | Value | Description | UTMuser@firewall.name.fqdnApplicationsHTTP-Proxy 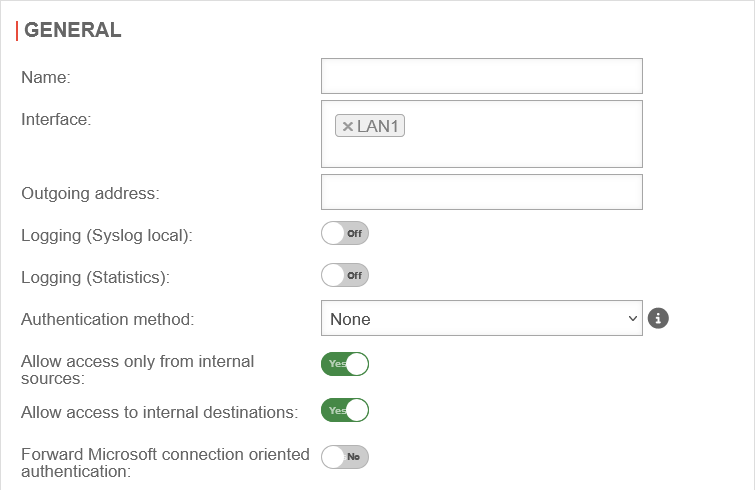 The General section in an additional configuration profile The General section in an additional configuration profile
|
|---|---|---|---|
| Name: | Configuration Profile 2 | Specify the name for the configuration profile | |
| Interface | LAN1 | Assign this configuration profile to an interface, e.g., LAN1 | |
| Outgoing Address: | The IP address of the interface that the HTTP proxy should use. The Outgoing Address is used for two scenarios:
In this example, the proxy is bound to the faster DSL line:
Connection to a web server in the VPN network:
| ||
| Forward requests to system-wide parent proxy : Is set in the global configuration profile |
No | ||
| Logging (Syslog lokal): | Off | Writes a general Syslog for the HTTP proxy (Open: Area Log | |
| Logging (Statistics): Only available if no anonymization for the HTTP proxy Settings at |
On | Writes a statistical Log call: Area HTTP proxy statistics | |
| Authentication method: | The proxy offers various possibilities for authentication. The possibilities are: | ||
| None | The HTTP proxy processes all requests without authentication | ||
| Basic | With basic authentication, the users are queried against the stored users under Area User on the firewall | ||
| NTLM / Kerberos | Here the firewall must be made known to the server. This can be set up in the web interface under | ||
| Radius | Here the firewall must be made known to the server. This can be set up in the web interface under | ||
| Allow access only from local sources: | Yes default |
Access to the HTTP proxy is now only possible from internal sources. These are:
| |
| Allow access to local destinations: | Yes default |
All internal networks can also be reached via the HTTP proxy (the packetfilter has already been passed through to reach the HTTP proxy). Disabling it prevents this and access to other internal networks must be explicitly allowed via the port filter without an HTTP proxy. | |
| Forward Microsoft connection-oriented authentication: | No | If it is enabled, login or authentication to websites is possible. For some websites this is not possible otherwise. With this option, NTLM, Negotiate and Kerberos authentications are forwarded notempty
If SSL-Interception is active, this parameter must be enabled for HTTPS-based authentications, otherwise no authentication/login is possible on these websites. | |
Authentication exceptions | |||
| Enabled | Off default |
Authentication exceptions are disabled by default.
If enabled: URLs listed here are accessed without prior authentication. |
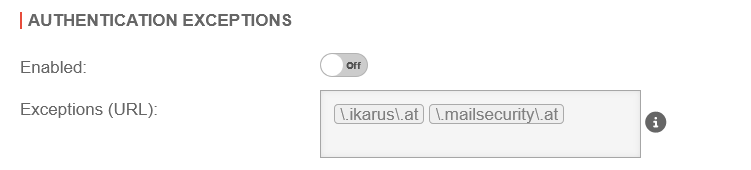 |
| Exception (URL): | \.ttt-point\.de | If authentication exceptions are enabled, custom exceptions can be defined here | |
Virusscan | |||
General | |||
|
Der Virenscanner im HTTP-Proxy kann Datenverkehr auf Viren prüfen. notempty Dabei werden mit FastDiff die Viruspattern in Echtzeit aktualisiert. New as of v14.1.0 Die Funktion lässt sich per CLI deaktivieren oder aktivieren. Per Default ist die Funktion aktiviert. FastDiff Deaktivieren: extc value set { application ikarus variable ENABLE_FASTDIFF value 0 } FastDiff Aktivieren: extc value set { application ikarus variable ENABLE_FASTDIFF value 1 } FastDiff Status abfragen:extc value get { application ikarus variable ENABLE_FASTDIFF } application|variable |value -----------+---------------+----- ikarus |ENABLE_FASTDIFF|1 notempty Zusätzlich werden mit der Funktion SigQA neue aber unbekannte Signaturen an unser AV-Labor übermittelt. New as of v14.1.0 Die Funktion lässt sich per CLI deaktivieren oder aktivieren. Per Default ist die Funktion aktiviert. SigQA Deaktivieren: extc value set { application ikarus variable ENABLE_SIGQA value 0 } SigQA Aktivieren: extc value set { application ikarus variable ENABLE_SIGQA value 1 } SigQA Status abfragen:extc value get { application ikarus variable ENABLE_SIGQA } application|variable |value -----------+------------+----- ikarus |ENABLE_SIGQA|1 | |||
| Virusscan: | Off | The virus scanner is deactivated, but the associated service is running (default setting) |
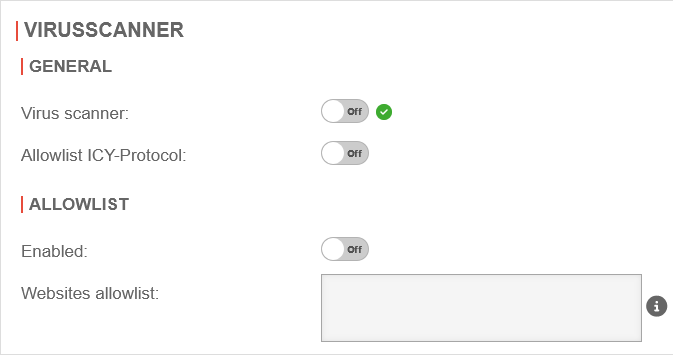 |
| On | The virus scanner is activated and the associated service is running | ||
| On | The virus scanner service is deactivated. The HTTP proxy is not working correctly. The service can be started via the menu Virusscan | ||
| On | The virus scanner service is deactivated. The HTTP proxy is not working correctly. notempty On devices with less than 3GB RAM, the service for the virus scanner cannot start. Please change to current hardware or allocate more RAM! | ||
| Off | The virus scanner is deactivated. | ||
| Maximum scan size limit: Is set in the global configuration profile |
2▴▾ Megabytes | ||
| Trickle Time: Is set in the global configuration profile |
5▴▾ seconds | ||
| Allowlist ICY-Protokoll: | Off | A web radio protocol that can be excluded from testing | |
Allowlist | |||
| Enabled | On | The allowlist for MIME types and websites is enabled by default | |
| Mime-Type Allowlist Is set in the global configuration profile |
application/pkcs10 Example |
||
|
Exceptions
»^[^:]*://download\.windowsupdate\.com/ |
Here it is possible to create your own filters based on Regular Expressions (Regex). notempty Viruses from these pages are not detected! Some update servers that cause problems when using a virus scanner are already preconfigured. Hint: Further exceptions are necessary so that iTunes can communicate correctly with the internet. | ||
| Cache Updates notempty New as of v12.7.2 Is set in the global configuration profile |
Off | ||
Bandwidth | |||
| Bandwidth limiting policy: | None | Default |  |
| Limit total bandwidth | In this case, the proxy only uses the specified maximum bandwidth and leaves the rest of the bandwidth untouched by your internet connection. (This bandwidth is shared by all hosts connected to the proxy.) | ||
| Per host bandwidth | Bandwidth for each host. The limited bandwidth for hosts cannot exceed the global bandwidth. | ||
| Global bandwidth: | 2.000.000▴▾ kbit/s | Default value, if activated | |
| Per host bandwidth: | 64.000▴▾ kbit/s | Default value, if activated | |
App Blocking | |||
| The general app blocking with fixed ports has been removed. Individual apps, or the ports they use, can be blocked flexibly via the packet filter. | |||
SSL-InterceptionWith the SSL interception feature, it is possible to recognise malicious code in SSL-encrypted data streams at the gateway. It interrupts the encrypted connections and makes the data packets visible to virus scanners and other filters. Data transmission to the client is then encrypted again. To do this, however, it is necessary to create a CA under and select this in the CA certificate field. | |||
| Caption | Value | Description | UTMuser@firewall.name.fqdnApplicationsHTTP-Proxy 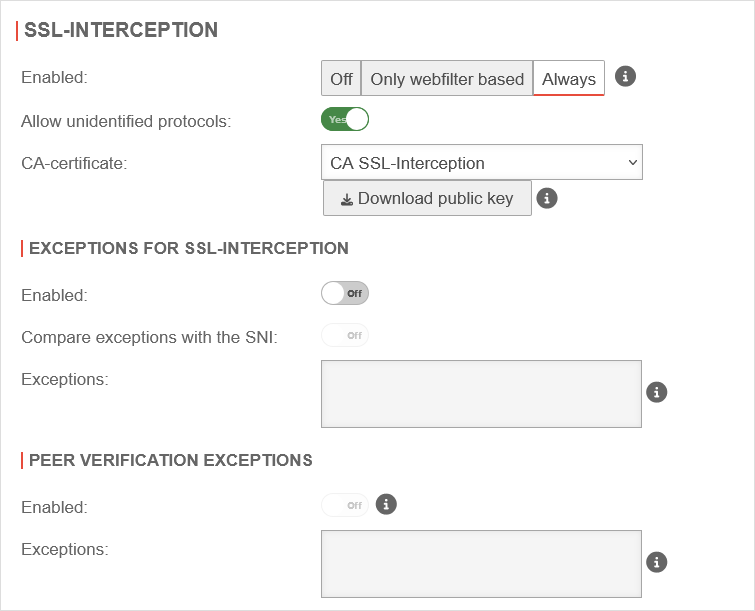 SSL Interception tab SSL Interception tab
|
| Enabled | The SSL-Interception is turned off | ||
| When enabled, only connections blocked by the web filter are intercepted. This avoids the problem that there are sites that do not tolerate an interruption of the encryption (e.g. banking software) without having to define an exception for it. | |||
| Activates the SSL interception | |||
| Validate SNI: Is set in the global configuration profile |
Yes | When activated, any SNI in the ClientHello of the TLS handshake is checked. The host name contained is resolved and the addresses in the result are compared with the target address of the intercepted request. If they do not match, the connection is closed. Without Server Name Indication validation, clients can manipulate SNI arbitrarily to bypass the web filter. This setting should only be considered as a last resort when it seems impossible to standardize the DNS settings between the HTTP proxy and the UTM clients. If the client and UTM use different DNS servers, this can lead to false positives.
| |
| Allow non identified protocols: | Yes | If this switch is deactivated, unrecognized protocols are blocked. | |
| CA-Certificate: | CA-SSL-Interception | Here, a CA must be selected that can re-encrypt the connection after decryption (and scanning). The public key of the CA must be installed on all client computers that are to use SSL Interception. Download can be done here directly with . ```markdown
notempty
| |
| The public key should be installed on the clients that are going to use SSL interception to avoid certificate errors. | |||
| Peer verification: not for Only webfilter based Is set in the global configuration profile |
On | This should definitely be enabled! With this, the HTTP proxy checks whether the certificate of the called page is trustworthy. Since the browser only sees the local certificate, a check by the browser is no longer possible. | |
Exceptions for SSL-Interception Exceptions for SSL-Interception not for Only webfilter based | |||
| Enabled | Off | It is possible to define exceptions in the format of Regular Expressions. However, since only https can arrive here, it is not filtered for protocols, unlike the virus scanner. New exceptions can be added directly in the input field. So an exception for www.securepoint.de would be:
.*\.securepoint\.de" | |
| Compare exceptions with the SNI: Only available if salidate SNI is active. |
Off | Applies Server Name Indication validation only to activated Exceptions of SSL-Interception . | |
| Exceptions: | .*\.ttt-point\.de Predefined in the Global Configuration Profile .*\.ikarus\.at.*\.mailsecurity\.at .*91\.212\.136\..* |
Define exceptions here for ttt-point.de | |
Peer verification exceptions Peer verification exceptions only if peer verification is active | |||
| Enabled | Off | Here exceptions for certificate verification in regex format can be added.
| |
Captive Portal
The Captive Portal is configured since v12.1 in its own menu under . There is a separate Wiki-article for this.
Warnung: Der Anzeigetitel „HTTP proxy transparent mode“ überschreibt den früheren Anzeigetitel „HTTP Proxy“.
Last adaptation to the version: 12.6.0
- Updated to Redesign of the webinterface
Functionality of the transparent proxy
The transparent proxy ensures that web page calls are routed through the HTTP proxy even without settings in the browser, so that the virus scanner and web filter can be used for these connections.
In order to be able to check SSL-encrypted connections for viruses and malware, the proxy must pretend to be a client to the web server on the Internet, so that the data can already be decrypted on the firewall.
These are to be passed on coded afterwards again to the actual Client in the internal network.
To achieve this, the feature SSL interception is used.
Configuration
Certificate
SSL-Interception
Configuration under Area SSL Interception
| Caption | Value | Description | UTMuser@firewall.name.fqdnApplicationsHTTP-Proxy 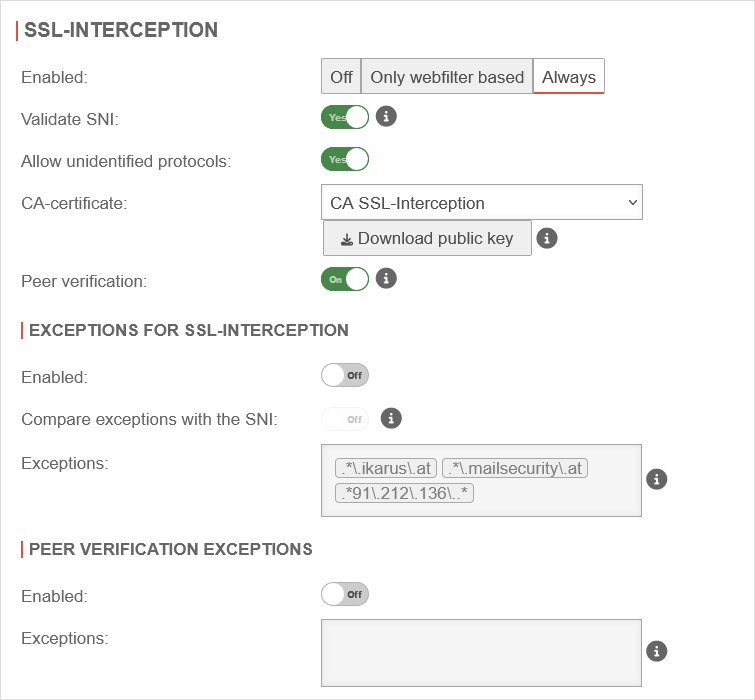 SSL Interception tab SSL Interception tab
|
|---|---|---|---|
| Enabled | The SSL-Interception is turned off | ||
| When enabled, only connections blocked by the web filter are intercepted. This avoids the problem that there are sites that do not tolerate an interruption of the encryption (e.g. banking software) without having to define an exception for it. | |||
| Activates the SSL interception | |||
| Validate SNI: Only in the global configuration profile Is inherited by additional configuration profiles |
Yes | When activated, any SNI in the ClientHello of the TLS handshake is checked. The host name contained is resolved and the addresses in the result are compared with the target address of the intercepted request. If they do not match, the connection is closed. Without Server Name Indication validation, clients can manipulate SNI arbitrarily to bypass the web filter. This setting should only be considered as a last resort when it seems impossible to standardize the DNS settings between the HTTP proxy and the UTM clients. If the client and UTM use different DNS servers, this can lead to false positives.
| |
| Allow non identified protocols: | Yes | If this switch is deactivated, unrecognized protocols are blocked. | |
| CA-Certificate: | CA-SSL-Interception | Here, a CA must be selected that can re-encrypt the connection after decryption (and scanning). The public key of the CA must be installed on all client computers that are to use SSL Interception. Download can be done here directly with . ```markdown
notempty
| |
| The public key should be installed on the clients that are going to use SSL interception to avoid certificate errors. | |||
| Peer verification: not for Only webfilter based Only in the global configuration profile Is inherited by additional configuration profiles |
On | This should definitely be enabled! With this, the HTTP proxy checks whether the certificate of the called page is trustworthy. Since the browser only sees the local certificate, a check by the browser is no longer possible. | |
Exceptions for SSL-Interception Exceptions for SSL-Interception not for Only webfilter based | |||
| Enabled | Off | It is possible to define exceptions in the format of Regular Expressions. However, since only https can arrive here, it is not filtered for protocols, unlike the virus scanner. New exceptions can be added directly in the input field. So an exception for www.securepoint.de would be:
.*\.securepoint\.de" | |
| Compare exceptions with the SNI: Only available if salidate SNI is active. |
Off | Applies Server Name Indication validation only to activated Exceptions of SSL-Interception . | |
| Exceptions: | .*\.ttt-point\.de Predefined in the Global Configuration Profile .*\.ikarus\.at.*\.mailsecurity\.at .*91\.212\.136\..* |
Define exceptions here for ttt-point.de | |
Peer verification exceptions Peer verification exceptions only if peer verification is active | |||
| Enabled | Off | Here exceptions for certificate verification in regex format can be added.
| |
Add certificate to the browser
To do this, the public part of the CA is downloaded via the button ![]() .
.
Either by logging in from each individual client on the UTM to store the CA on them or it is downloaded once and stored on a USB stick or network storage. The certificate is then added to the browser via this route.
Transparent mode
UTMuser@firewall.name.fqdnApplications 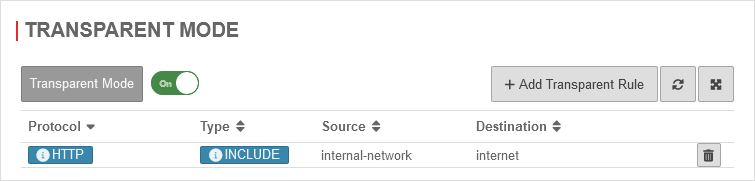 Transparent mode activated
Transparent mode activated
ACtivate under Area Transparent mode with Transparent mode On
Create HTTPS rule
In the default setting, transparent mode is already enabled for the HTTP protocol over port 80.
To set this up for the HTTPS protocol and port 443 as well, another rule is added by clicking the button.
Packet filter rules
Packet filter rule for access to DNS resolution
| # | Source | Destination | Service | NAT | Action | Active | |||
| 2 | Accept | On |
Examples of exceptions for Windows update server
For more examples on how to set up SSL interception, authentication exceptions, virus scanners, and web filters regarding Windows updates, see the knowledge base article Windows Updates with HTTP Proxy and Web Filter
Troubleshooting
Situation
- UTM with active transparent HTTP proxy for HTTP and HTTPS.
- SSL interception running in "Web Filter Based" mode.
Error message in the browser
ERROR_SSL_PROTOCOL_ERROR
or
ssl_error_rx_record_too_long
Log message in the UTM
Log message of Squid (menu ) in the UTM:
2021-09-15T16:50:20.003+02:00|squid|8933|1631717419.981 1 192.0.2.192 NONE/200 0 CONNECT 104.96.47.5:443 - HIER_NONE/- -
2021-09-15T16:50:20.007+02:00|squid|8933|1631717420.007 27 192.0.2.192 NONE_ABORTED/409 12387 CONNECT loadbalancing.ttt-point.de:443 - HIER_NONE/- text/html
2021-09-15T16:50:20.007+02:00|squid|8933|1631717420.007 27 192.0.2.192 NONE_ABORTED/409 12387 CONNECT loadbalancing.ttt-point.de:443 - HIER_NONE/- text/html
2021-09-15T16:50:22.652+02:00|squid|8933|SECURITY ALERT: Host header forgery detected on local=192.0.2.22:443 remote=192.168.175.10:28144 FD 9 flags=33 (local IP does not match any domain IP)
2021-09-15T16:50:22.654+02:00|squid|8933|SECURITY ALERT: on URL: loadbalancing.ttt-point.de:443
Meaning
- The client starts a TCP connection to an HTTPS server
- The connection is intercepted by the UTM → Transparent Proxy
- The HTTP proxy (Squid) checks the connection and analyzes the TLS handshake
- The information obtained, such as the SNI, is thereby resolved and compared with the original IP address
- In this case, the original IP and the resolved IP for the SNI (hostname) do not match and are therefore blocked by the HTTP proxy, resulting in the above mentioned error message
Cause
This behavior can be observed for hostnames with intensive load balancing.
If the provider gives different responses to DNS queries in a short period of time, the results in DNS resolution may differ between the client and the UTM.
This behavior can be caused by:
- Different DNS servers on client and UTM.
- Hostnames that are resolved differently by UTM and client with a very small TTL due to intensive load balancing.
- Use of DNS servers at different geographical locations.
In this case, a different IP address can be returned via the remote location for the called host names than at the local location of the UTM. (Geographic DNS Routing)
Solution
- Best Practice:
Auf dem Client wird die UTM als globaler Proxy-Server und ggf. für jede Anwendung als Proxy-Server eingetragen. - Workaround:
Auf Client und UTM werden die gleichen DNS-Server eingetragen.
In addition, it must be ensured that no DNS servers are used that are themselves already addressed via Geographic DNS Routing.
The Google servers, for example, differ despite identical IP address depending on the region from which they are called!
Captive Portal
Warnung: Der Anzeigetitel „Captive Portal“ überschreibt den früheren Anzeigetitel „HTTP proxy transparent mode“.
- No changes to the Server Settings are required any more
- ACME wildcard certificates can be used for the landing page
- 05.2024: Updated to Redesign of the webinterface
12.1.9 (externe & lokale Zertifikate) 11.8.7 (externe Zertifikate) 11.8.7 (lokale Zertifikate) 11.7.3 (externe Zertifikate) 11.7.3 (lokale Zertifikate) 11.7
Preliminary remark
The captive portal redirects an HTTP client in a network to a special web page (so-called landing page) before it can connect normally to the Internet. Thus, acceptance of the condition of use must take place and additional authentication can be configured.
It is recommended to use either an ACME certificate or a purchased certificate from an official CA (or an already existing wildcard certificate) for the captive portal to prevent later irritations due to warning messages of the browser.
Planning
The following aspects should be considered before configuration:
- For which networks should the captive portal be configured?
Will all potential users be reached exclusively? - How and by whom will the terms of use be written?
- Should authentication take place?
- Which internal web servers are not allowed to be reached from the network behind the captive portal?
Jus a few preparations must be made to use the captive portal:
- A certificate must be available for the landing page
- Implicit and port filter rules must allow access
The host name of the portal page is configured under Area General.
Provide certificate
Create an ACME certificate
To use ACME certificates (Let's Encrypt) the following steps are required:
- Activate ACME service
- Generate ACME Challenge Token on spDyn
- Create certificate
- Add SAN with spDyn hostname and token
- Create certificate
Area ACME
| Caption | Value | Description | UTMuser@firewall.name.fqdnAuthentifizierung 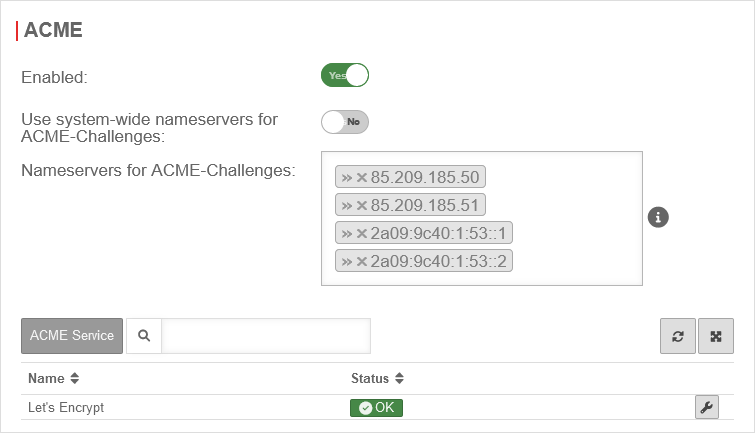
|
|---|---|---|---|
| Activated: | Yes | Enables the use of ACME certificates. For more information see below Activate ACME service. | |
| Use system-wide nameservers for ACME challenges: | Yes | If the addresses for the servers for the extension of the ACME challenges cannot be resolved via the system-wide nameserver (e.g. due to configured relay or foreward zones), alternative nameservers can be entered by deactivating No. | |
| Nameserver for ACME challenges: Can be used for ACME challenges when system-wide nameserver is disabled |
»85.209.185.50»85.209.185.51»2a09:9c40:1:53::1»2a09:9c40:1:53::2 | Here you can enter the nameservers for the ACME-Challenges. | |
Activate ACME service
To be able to use ACME certificates, this must be activated under Area ACME Enabled: Yes.
- As soon as the service has been activated and this has been saved with , the link to the terms of use is loaded and the settings can be called up.
- With the button Activate Yes and the storage of an Email address for notifications by the ACME service provider (here: Let's Encrypt), the information can be saved with
- A dialog will appear with a link to the Terms of Use, which must be accepted Yes.
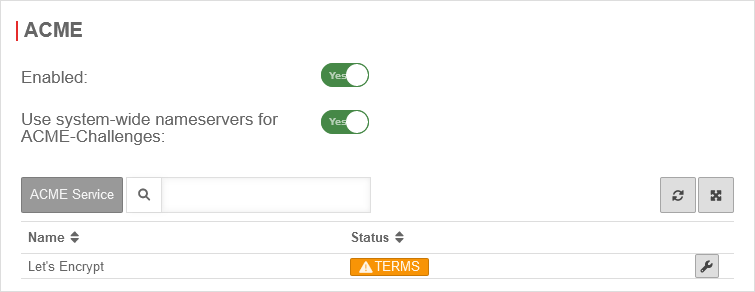
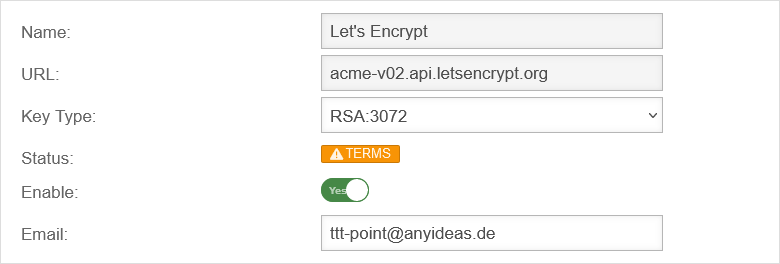
Generate token
spDYN To generate the certificates, the ACME token must first be generated in the spDYN portal.
Within the spDYN portal, the corresponding host must be opened.
- Call up spDyn Host
- Select the ACME Challenge Token from the Token drop-down menu.
- Generate token
notemptyThe token is displayed once during generation and cannot be displayed again.
The token should be noted and stored safely.
Renewal of ACME certificates
The renewal of the ACME/Let's Encrypt certificates takes place via the nameservers used, which are configured under Area ACME (see above)
ACME Certificates
After completing the previous steps, the actual certificate can now be generated. A click on in the Certificates tab opens the corresponding dialog.
Purchased certificate
Alternatively, a purchased certificate can also be imported
Grundsätzlich bestehen hier zwei Optionen:
- A Certificate for a FQDN
- in this case the common name of the certificate would be portal.anyideas.de
- A wildcard certificate
- in which case the common name of the certificate would be *.anyideas.de
In the first step, the CA provided together with the certificate must be imported into the UTM.
Menu Area CA buttonIn the first step, the CA provided together with the certificate must be imported into the UTM.
Menu Area CA button
Import format
Certificates and CAs to be imported into a UTM must be in the format .pem or .p12 (pkcs12).
Certificates can be converted with the tool openssl - available for all common platforms (part of Linux, call via console) - and the following commands:
| Certificate | Command |
|---|---|
| X509 to PEM | openssl x509 -in certificatename.cer -outform PEM -out certificatename.pem |
| DER to PEM | openssl x509 -inform der -in certificate.cer -out certificate.pem |
| P7B to PEM | openssl pkcs7 -print_certs -in certificate.p7b -out certificate.pem |
Error message during import
During import, the error message "The certificate format is not supported..." may appear.
Password protected certificates in pkcs12 format (.p12 , .pfx , .pkcs12) in conjunction with older ciphers can trigger this error.
Import is usually possible if in the tab General the option Support legacy cryptographic algorithms On is enabled.
Options for importing certificates:
- Convert certificate to *.pem
Certificates can be converted with the tool openssl - available for all common platforms (part of Linux, call via console) - and the following commands:
openssl pkcs12 -in Zertifikat.pfx -out Zertifikat.pem -nodes
Alternatively with the help of an online service
- CLI commands to allow certificate import with obsolete ciphers in the UTM
extc global set variable GLOB_ENABLE_SSL_LEGACY value 1
appmgmt config application "securepoint_firewall"
appmgmt config application "fwserver"
system reboot
cli> extc global get variable GLOB_ENABLE_SSL_LEGACY variable |value ----------------------+----- GLOB_ENABLE_SSL_LEGACY|0 cli> extc global set variable GLOB_ENABLE_SSL_LEGACY value 1 OK cli> extc global get variable GLOB_ENABLE_SSL_LEGACY variable |value ----------------------+----- GLOB_ENABLE_SSL_LEGACY|1 cli> appmgmt config application "securepoint_firewall" cli> appmgmt config application "fwserver"
Local certificate
The UTM can also provide its own certificate
- At Area CA a CA must be created
- At Area Certificates a Server- certificate must be created. A separate certificate should be created for the captive portal so that it can be revoked if necessary without affecting other connections or applications.
How to create a certificate on the UTM can be read here.
The user receives a warning message in which the trustworthiness must be confirmed once.
Captive Portal User
Add user
Captive Portal users can be managed by:
- Administrators
- Users who are members of a group with the permission Userinterface Administrator .
They reach the user administration via the user interface.
Implied rules
UTMuser@firewall.name.fqdnFirewall 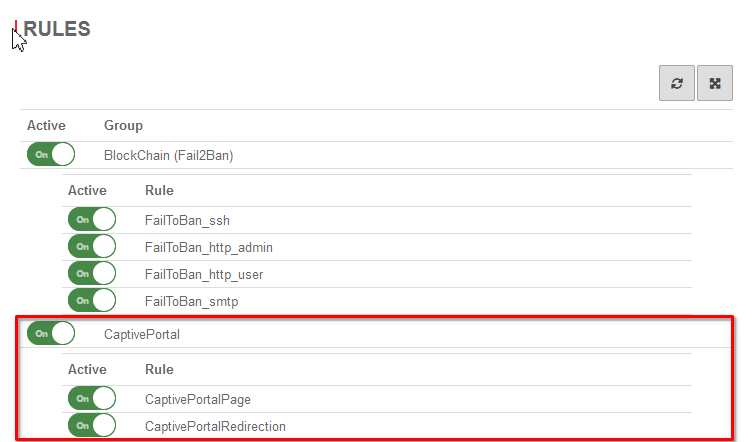 Firewall - Implied rules
Menu Group Ein Captive Portal
Firewall - Implied rules
Menu Group Ein Captive Portal
At the item Captive Portal in the menu Implied Rules you have to make sure that both rules are activated.
The switch CaptivePortalPage opens an incoming port on the corresponding interface of the firewall, which is intended for the Captive Portal to be able to display the landing page.
The switch CaptivePortalRedirection is, as the name suggests, responsible for the corresponding redirection of the traffic to the port mentioned above.
Packetfilter
UTMuser@firewall.name.fqdnFirewallPacketfilter  Firewall - Portfilter IP
A rule is required in the port filter to allow Captive Portal users to access the Internet.
Firewall - Portfilter IP
A rule is required in the port filter to allow Captive Portal users to access the Internet.
Alternatively, an autogenerated any rule can also be created in the Captive Portal settings using the button in the General tab.
| Source: | |
| Destination: | |
| Service: | |
| [–] NAT | |
| Type: | |
| Network object: |
SaveSave and close
Then use the button to
Settings in the Captive Portal
Menu
General
Nameserver
Menu Area Zones
If the firewall name cannot be changed to a FQDN, for example because the UTM is used as outgoing mail relay, the name server of the firewall must also be used: In this example, it is assumed that the firewall for the network of the captive portal is the responsible DHCP server and is set up as primary DNS server.
Add Forward Zone
Button
The zone name to be assigned corresponds to the landing page of the captive portal.
In the example portal.anyideas.de.
localhost is used as the host name of the name server.
The IP address field can be left empty.
Edit Forward Zone
UTMuser@firewall.name.fqdnApplicationsNameserver 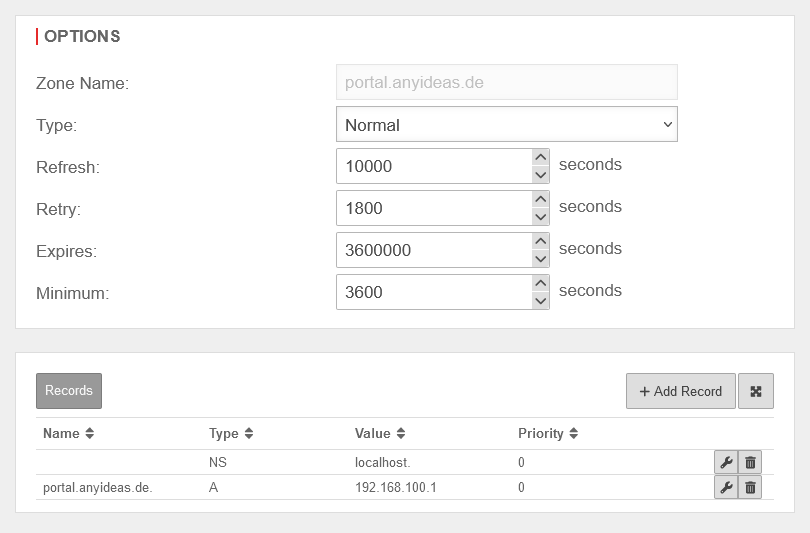 Nameserver - A-Record with IP address
The following entry is added to the zone just created → Button :
Nameserver - A-Record with IP address
The following entry is added to the zone just created → Button :
| Caption | Value | Description |
|---|---|---|
| Name: | portal.anyideas.de. | FQDN of the firewall |
| Type: | A-Record | |
| Value: | 192.168.100.1 | IP of the interface via which the captive portal is to be reached (here wlan0 ) |
Transparent mode
UTMuser@firewall.name.fqdnAnwendungen 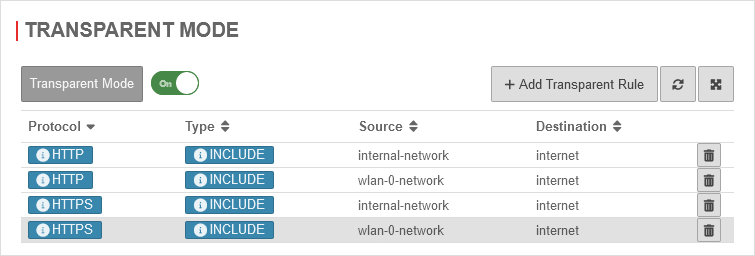 HTTP Proxy - Transparent Proxy
Menu Area Transparent mode
HTTP Proxy - Transparent Proxy
Menu Area Transparent mode
To access the Internet via the required HTTP proxy, at least one rule is necessary (HTTP), better two (additionally HTTPS)
Button
| Caption | Value |
|---|---|
| Protocol | |
| Type | |
| Source | |
| Destination |
To access https pages, in the tab SSL Interception SSL Interception On must be activated. (Requires a CA certificate of the UTM)
| Caption | Value |
|---|---|
| Protocol | |
| Type | |
| Source | |
| Destination |
Webfilter
Finally, the web filter should be configured, since surfing through the proxy is possible without rules in the port filter access to e.g. internal web servers:
with authentication
- Area Network objects button
Create a group (e.g. grp_CP_webfilter) that contains the wlan-0-network network object - Button
- Network or user group: Select the newly created group
- Edit newly generated rule record
- webserver.anyideas.de URL of the (internal) server to which access via the captive portal should be blocked
- Leave action on block
without authentication
- Button
- Select the user group
- Edit newly generated rule record
- webserver.anyideas.de URL of the (internal) server to which access via the captive portal should be blocked
- Leave action on block